- 生成tomcat服务端的证书
如系统中没有配置jdk环境变量,需要在\jdk\bin的目录下执行CMD
如在系统中配置了jdk环境变量,直接运行CMD
运行以下语句
keytool -genkey -v -alias tomcat -keyalg RSA -keystore D:\https\key\tomcat.keystore -validity 36500
“-alias tomcat ”为证书别名
“D:\https\key\tomcat.keystore”为生成证书的地址与证书名
“-validity 36500”有效期36000天
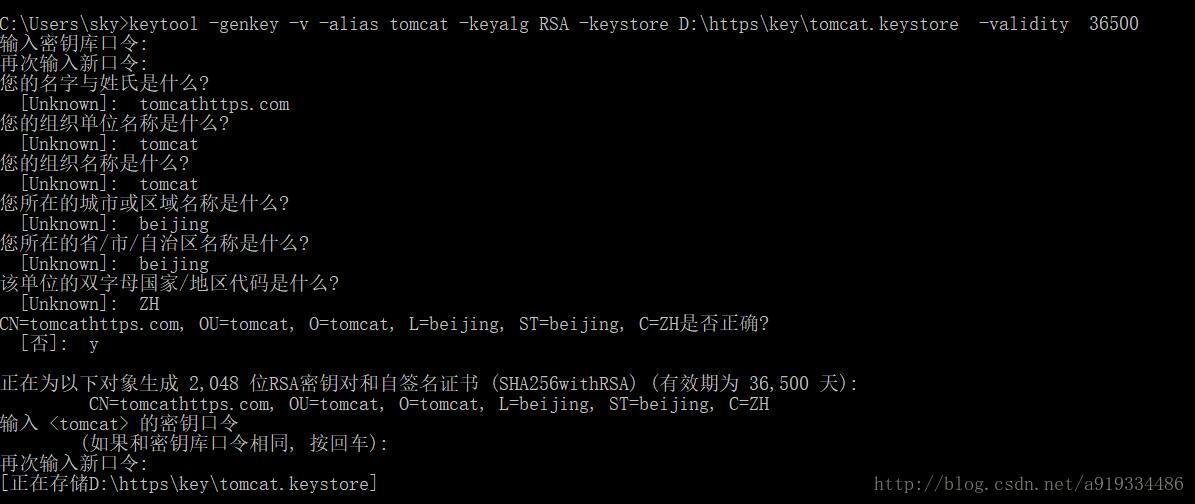
其中“您的名字与姓氏是什么”这个是tomcat部署的主机或域名,如本机测试可填写localhost。
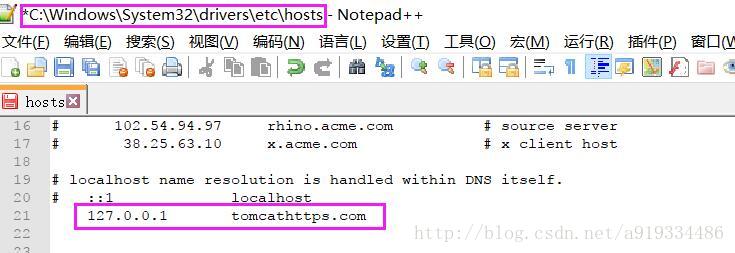
如为上图中所写需修改host文件
2. 为客户端生成证书
运行以下语句
keytool -genkey -v -alias client -keyalg RSA -storetype PKCS12 -keystore D:\https\key\client.p12 -validity 36500
“-alias client”为客户端别名
“D:\https\key\client.p12”生成的存储地址
“-validity 36500”证书有效期36500天

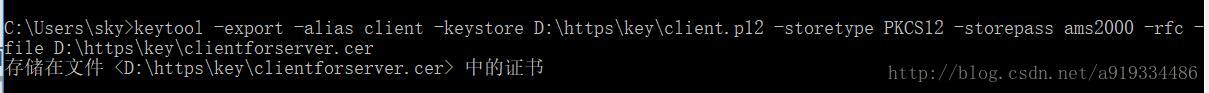
3. 服务端信任证书
首先生成CER客户证书
keytool -export -alias client -keystore D:\https\key\client.p12 -storetype PKCS12 -storepass ams2000 -rfc -file D:\https\key\clientforserver.cer
“D:\https\key\client.p12”为上文中生成的client.p12地址
“-storepass ams2000”客户端密码
“-file D:\https\key\clientforserver.cer”生成CER文件的路径
运行以下语句
keytool -import -v -file D:\https\key\clientforserver.cer -keystore D:\https\key\tomcat.keystore
输入密码,输入“y”
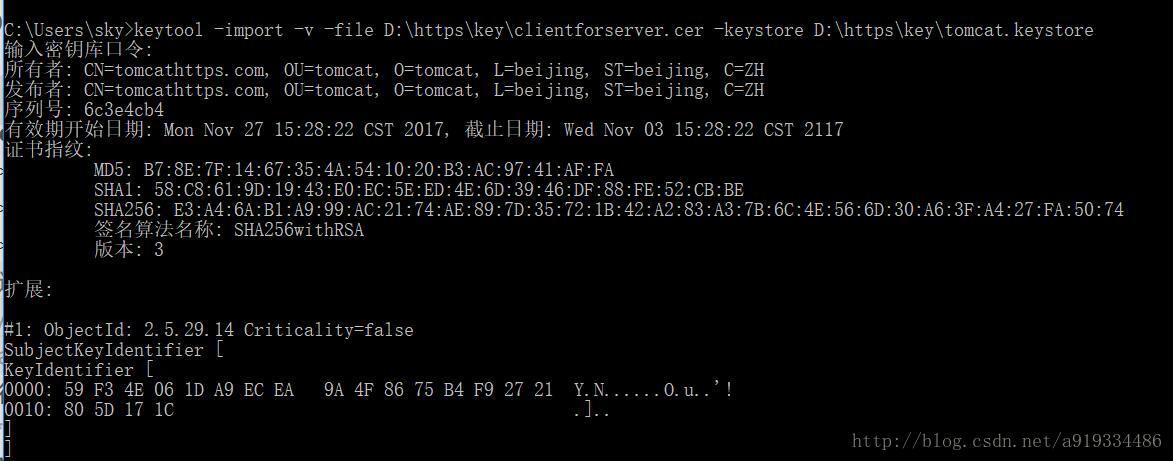
检查信任结果
keytool -list -keystore D:\https\key\tomcat.keystore
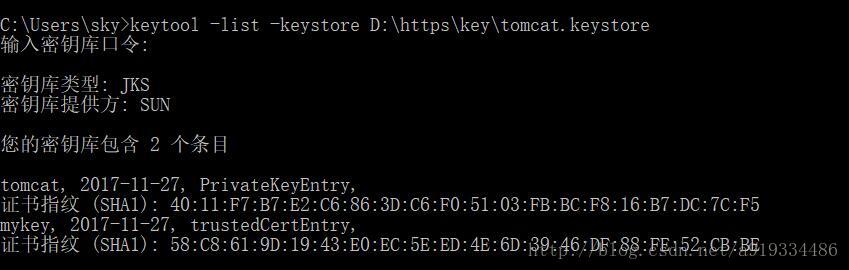
信任成功
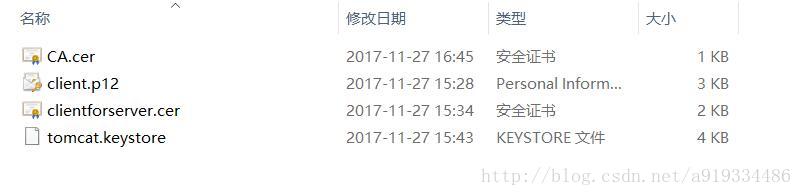
4. 列表内容生成可用的客户端证书
keytool -keystore D:\https\key\tomcat.keystore -export -alias tomcat -file D:\https\key\CA.cer
5. 安装证书
现得到如下四个证书文件
双击运行**client.p12**
一直点击下一步,直到显示
查看证书说明导入成功
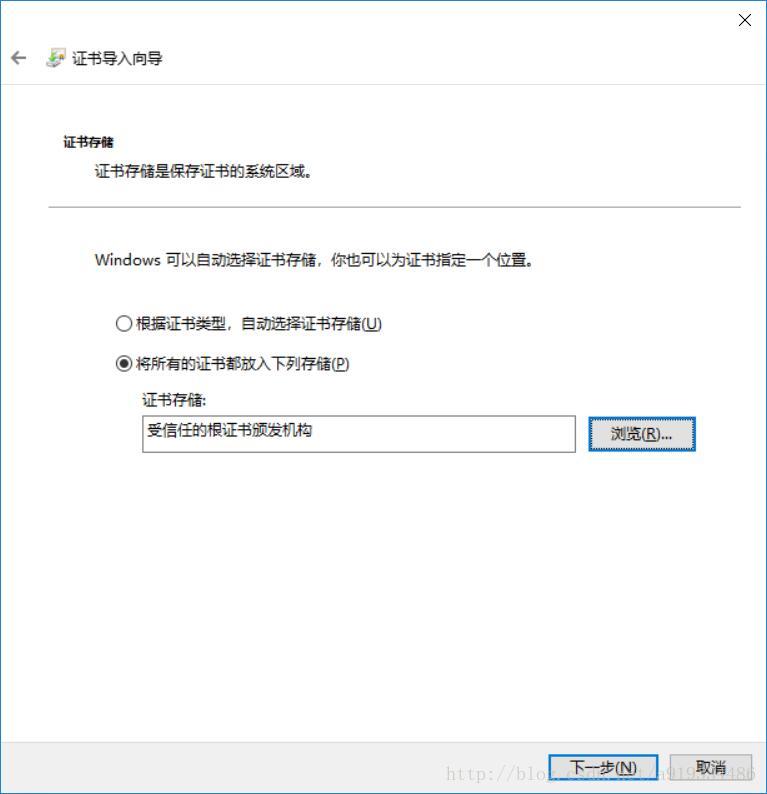
双击运行**CA.cer**
一直下一步 到如下步骤时修改,直至安装成功
6.修改tomcat参数发布服务
在tomcat/bin/server.xml中修改
<Connector port="8443" protocol="org.apache.coyote.http11.Http11Protocol" SSLEnabled="true"
maxThreads="150" scheme="https" secure="true"
clientAuth="true" sslProtocol="TLS"
keystoreFile="D:\https\key\tomcat.keystore"
keystorePass="ams2000"
truststoreFile="D:\https\key\tomcat.keystore"
truststorePass="ams2000"
/>运行tomcat,本例子需要修改host文件

访问如下地址
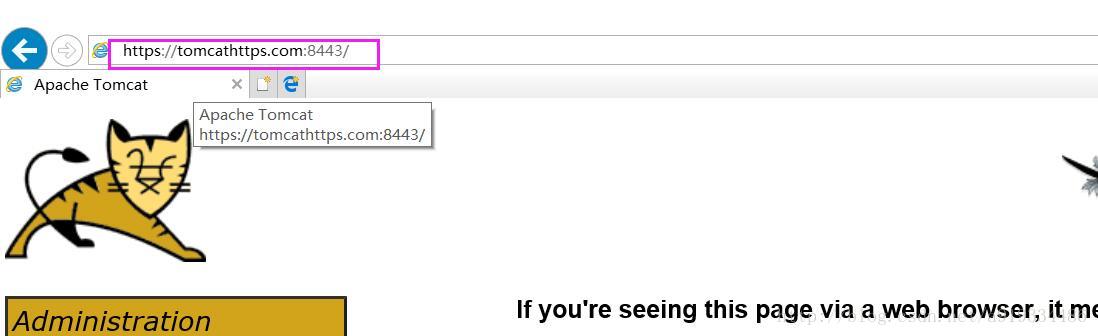
配置成功
6. 以下为待有证书的访问实例
import org.apache.commons.io.IOUtils;
import org.apache.http.HttpEntity;
import org.apache.http.client.methods.CloseableHttpResponse;
import org.apache.http.client.methods.HttpGet;
import org.apache.http.conn.ssl.SSLConnectionSocketFactory;
import org.apache.http.conn.ssl.TrustSelfSignedStrategy;
import org.apache.http.conn.ssl.TrustStrategy;
import org.apache.http.impl.client.CloseableHttpClient;
import org.apache.http.impl.client.HttpClients;
import org.apache.http.ssl.SSLContexts;
import org.apache.http.util.EntityUtils;
import javax.net.ssl.SSLContext;
import java.io.File;
import java.io.FileInputStream;
import java.security.KeyStore;
import java.security.cert.CertificateException;
import java.security.cert.X509Certificate;
/*
* Created with Intellij IDEA
* USER: 焦一平
* Date: 2016/5/8
* Time: 1:10
* To change this template use File | Settings | File Template
*/
public class SSLDemo {
public static void main(String[] args) throws Exception {
KeyStore keyStore = KeyStore.getInstance("PKCS12");
keyStore.load(new FileInputStream(new File("C:\\Users\\Administrator\\Desktop\\jiaoyiping.p12")), "123456".toCharArray());
SSLContext sslcontext = SSLContexts.custom()
//忽略掉对服务器端证书的校验
.loadTrustMaterial(new TrustStrategy() {
@Override
public boolean isTrusted(X509Certificate[] chain, String authType) throws CertificateException {
return true;
}
})
//加载服务端提供的truststore(如果服务器提供truststore的话就不用忽略对服务器端证书的校验了)
//.loadTrustMaterial(new File("D:\\truststore.jks"), "123456".toCharArray(),
// new TrustSelfSignedStrategy())
.loadKeyMaterial(keyStore, "cmcc".toCharArray())
.build();
SSLConnectionSocketFactory sslConnectionSocketFactory = new SSLConnectionSocketFactory(
sslcontext,
new String[]{"TLSv1"},
null,
SSLConnectionSocketFactory.getDefaultHostnameVerifier());
CloseableHttpClient httpclient = HttpClients.custom()
.setSSLSocketFactory(sslConnectionSocketFactory)
.build();
try {
HttpGet httpget = new HttpGet("https://10.2.5.116/PnsReceiver/ReceiveMessage");
System.out.println("Executing request " + httpget.getRequestLine());
CloseableHttpResponse response = httpclient.execute(httpget);
try {
HttpEntity entity = response.getEntity();
System.out.println(response.getStatusLine());
System.out.println(IOUtils.toString(entity.getContent()));
EntityUtils.consume(entity);
} finally {
response.close();
}
} finally {
httpclient.close();
}
}
}






















 324
324

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








