1.什么是单点登录
单点登录SSO(Single Sign On)实际上就是用户在一个系统登录之后,在单点登录的其他客户端(应用)不用重复的登陆,登陆校验交给中央认证服务器去校验。单点登录的应用场景通常为一个大型的系统下有很多小系统,并且这些系统使用的是同一套认证体系。
常用的单点登录框架为cas,cas分为cas-server,cas-client.
2.使用jeesite实现单点登录的配置
看过jeesite的应该知道,jeesite使用的是shiro整合spring的方式,并且自定义实现了多种SessionManager和多种cacheManager,。由于单点登录的特殊性,需要我们自定义realm,realm可以看做是一个安全数据源,用来收集用户的认证信息和授权信息。
2.1单点登录的配置文件
2.1.1 loginUrl配置的为单点登录认证服务器的地址和service回调地址
2.1.2 需要单独配置logoutFilter,用于到认证服务器进行单点退出。
2.1.3 配置casFilter用于接收认证服务器验证之后的信息。并进行认证授权的处理
2.1.4自定义relam,在SystemAuthorizingRealm基础上进行改造。
2.1.5单点登录的配置文件:
<?xml version="1.0" encoding="UTF-8"?>
<beans xmlns="http://www.springframework.org/schema/beans"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xmlns:context="http://www.springframework.org/schema/context"
xsi:schemaLocation="
http://www.springframework.org/schema/beans http://www.springframework.org/schema/beans/spring-beans-4.0.xsd
http://www.springframework.org/schema/context http://www.springframework.org/schema/context/spring-context-4.0.xsd"
default-lazy-init="true">
<description>Shiro Configuration</description>
<!-- 加载配置属性文件 -->
<context:property-placeholder
ignore-unresolvable="true" location="classpath:app.properties" />
<!-- Shiro权限过滤过滤器定义 -->
<bean name="shiroFilterChainDefinitions" class="java.lang.String">
<constructor-arg>
<value>
/static/** = anon
/userfiles/** = anon
${adminPath}/cas = cas
<!-- ${adminPath}/login = authc -->
${adminPath}/logout = logout
${adminPath}/** = user
/act/rest/service/editor/** = perms[act:model:edit]
/act/rest/service/model/** = perms[act:model:edit]
/act/rest/service/** = user
/ReportServer/** = user
</value>
</constructor-arg>
</bean>
<!-- 安全认证过滤器 -->
<bean id="shiroFilter" class="org.apache.shiro.spring.web.ShiroFilterFactoryBean">
<property name="securityManager" ref="securityManager" />
<property name="loginUrl" value="${cas.server.url}/login?service=${cas.project.url}${adminPath}/cas"
/>
<!-- <property name="loginUrl" value="${adminPath}/login" /> -->
<property name="successUrl" value="${adminPath}/index?login" />
<property name="filters">
<map>
<entry key="cas" value-ref="casFilter" />
<entry key="logout">
<bean class="org.apache.shiro.web.filter.authc.LogoutFilter">
<property name="redirectUrl" value="${cas.server.url}/logout?service=${cas.project.url}${frontPath}"></property>
</bean>
</entry>
<!-- <entry key="authc" value-ref="formAuthenticationFilter" /> -->
</map>
</property>
<property name="filterChainDefinitions">
<ref bean="shiroFilterChainDefinitions" />
</property>
</bean>
<!-- CAS认证过滤器 -->
<bean id="casFilter" class="org.apache.shiro.cas.CasFilter">
<property name="failureUrl" value="${frontPath}/login" />
</bean>
<!-- 定义Shiro安全管理配置 -->
<bean id="securityManager" class="org.apache.shiro.web.mgt.DefaultWebSecurityManager">
<property name="realm" ref="casAuthorizingRealm" />
<property name="sessionManager" ref="sessionManager" />
<property name="cacheManager" ref="shiroCacheManager" />
</bean>
<bean id="casAuthorizingRealm" class="com.aligns.administrator.sys.security.CasAuthorizingRealm">
<property name="casServerUrlPrefix" value="${cas.server.url}" />
<property name="casService" value="${cas.project.url}${adminPath}/cas" />
</bean>
<!-- 自定义会话管理配置 -->
<bean id="sessionManager"
class="com.aligns.plat.core.security.shiro.session.SessionManager">
<property name="sessionDAO" ref="sessionDAO" />
<!-- 会话超时时间,单位:毫秒 -->
<property name="globalSessionTimeout" value="${session.sessionTimeout}" />
<!-- 定时清理失效会话, 清理用户直接关闭浏览器造成的孤立会话 -->
<property name="sessionValidationInterval" value="${session.sessionTimeoutClean}" />
<!-- <property name="sessionValidationSchedulerEnabled" value="false"/> -->
<property name="sessionValidationSchedulerEnabled" value="true" />
<property name="sessionIdCookie" ref="sessionIdCookie" />
<property name="sessionIdCookieEnabled" value="true" />
</bean>
<!-- 指定本系统SESSIONID, 默认为: JSESSIONID 问题: 与SERVLET容器名冲突, 如JETTY, TOMCAT 等默认JSESSIONID,
当跳出SHIRO SERVLET时如ERROR-PAGE容器会为JSESSIONID重新分配值导致登录会话丢失! -->
<bean id="sessionIdCookie" class="org.apache.shiro.web.servlet.SimpleCookie">
<constructor-arg name="name" value="jeesite.session.id" />
</bean>
<!-- 自定义Session存储容器 -->
<!-- <bean id="sessionDAO" class="com.thinkgem.jeesite.common.security.shiro.session.JedisSessionDAO">
<property name="sessionIdGenerator" ref="idGen" />
<property name="sessionKeyPrefix" value="${redis.keyPrefix}_session_" />
</bean> -->
<bean id="sessionDAO"
class="com.aligns.plat.core.security.shiro.session.CacheSessionDAO">
<property name="sessionIdGenerator" ref="idGen" />
<property name="activeSessionsCacheName" value="activeSessionsCache" />
<property name="cacheManager" ref="jedisCacheManager" />
</bean>
<!--
<bean id="jedisUtils" class="com.aligns.plat.utils.JedisUtils"></bean>
-->
<!-- 如果需要集群配置,则将SessionDao设置为jedis -->
<!-- <bean id="sessionDAO"
class="com.aligns.plat.core.security.shiro.session.JedisSessionDAO" >
<property name="sessionIdGenerator" ref="idGen" />
<property name="activeSessionsCacheName" value="activeSessionsCache" />
<property name="cacheManager" ref="jedisCacheManager" />
</bean> -->
<!-- 定义授权缓存管理器 -->
<!-- <bean id="shiroCacheManager" class="com.aligns.plat.core.common.security.shiro.cache.SessionCacheManager"
/> -->
<bean id="shiroCacheManager" class="org.apache.shiro.cache.ehcache.EhCacheManager">
<property name="cacheManager" ref="cacheManager" />
</bean>
<bean id="jedisCacheManager" class="com.aligns.plat.core.security.shiro.cache.JedisCacheManager">
</bean>
<!-- 保证实现了Shiro内部lifecycle函数的bean执行 -->
<bean id="lifecycleBeanPostProcessor" class="org.apache.shiro.spring.LifecycleBeanPostProcessor" />
<!-- AOP式方法级权限检查 -->
<bean
class="org.springframework.aop.framework.autoproxy.DefaultAdvisorAutoProxyCreator"
depends-on="lifecycleBeanPostProcessor">
<property name="proxyTargetClass" value="true" />
</bean>
<bean
class="org.apache.shiro.spring.security.interceptor.AuthorizationAttributeSourceAdvisor">
<property name="securityManager" ref="securityManager" />
</bean>
</beans>2.1.6单点登录的自定义relam(CasAuthorizingRealm)
/**
*
*/
package com.aligns.administrator.sys.security;
import java.util.ArrayList;
import java.util.Iterator;
import java.util.List;
import java.util.Map;
import org.apache.shiro.authc.AuthenticationException;
import org.apache.shiro.authc.AuthenticationInfo;
import org.apache.shiro.authc.AuthenticationToken;
import org.apache.shiro.authc.SimpleAuthenticationInfo;
import org.apache.shiro.authz.AuthorizationInfo;
import org.apache.shiro.authz.SimpleAuthorizationInfo;
import org.apache.shiro.cas.CasAuthenticationException;
import org.apache.shiro.cas.CasRealm;
import org.apache.shiro.cas.CasToken;
import org.apache.shiro.subject.PrincipalCollection;
import org.apache.shiro.subject.SimplePrincipalCollection;
import org.apache.shiro.util.CollectionUtils;
import org.apache.shiro.util.StringUtils;
import org.jasig.cas.client.authentication.AttributePrincipal;
import org.jasig.cas.client.validation.Assertion;
import org.jasig.cas.client.validation.TicketValidationException;
import org.jasig.cas.client.validation.TicketValidator;
import com.aligns.administrator.sys.entity.Menu;
import com.aligns.administrator.sys.entity.Role;
import com.aligns.administrator.sys.entity.User;
import com.aligns.administrator.sys.security.SystemAuthorizingRealm.Principal;
import com.aligns.administrator.sys.service.SystemService;
import com.aligns.administrator.sys.utils.LogUtils;
import com.aligns.administrator.sys.utils.UserUtils;
import com.aligns.plat.core.Servlets;
import com.aligns.plat.utils.SpringContextHolder;
/**
* 系统安全认证单点登录实现类
*
* @author kefan
* @version 2014-7-5
*/
//@Service
// @DependsOn({"userDao","roleDao","menuDao"})
public class CasAuthorizingRealm extends CasRealm {
private SystemService systemService;
public CasAuthorizingRealm() {
super();
}
/**
* 认证
* */
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken token) throws AuthenticationException {
CasToken casToken = (CasToken) token;
if (token == null)
return null;
String ticket = (String) casToken.getCredentials();
if (!StringUtils.hasText(ticket))
return null;
TicketValidator ticketValidator = ensureTicketValidator();
try {
Assertion casAssertion = ticketValidator.validate(ticket, getCasService());
//casPrincipal 认证后的用户信息
AttributePrincipal casPrincipal = casAssertion.getPrincipal();
String userId = casPrincipal.getName();
//获取用户
User user = getSystemService().getUserByLoginName(userId);
Map<String,Object> attributes = casPrincipal.getAttributes();
casToken.setUserId(userId);
String rememberMeAttributeName = getRememberMeAttributeName();
String rememberMeStringValue = (String) attributes.get(rememberMeAttributeName);
boolean isRemembered = rememberMeStringValue != null && Boolean.parseBoolean(rememberMeStringValue);
if (isRemembered)
casToken.setRememberMe(true);
// 这里可以拿到Cas的登录账号信息,加载到对应权限体系信息放到缓存中...
return new SimpleAuthenticationInfo(new Principal(user, false), ticket,getName());
} catch (TicketValidationException e) {
throw new CasAuthenticationException((new StringBuilder()).append("Unable to validate ticket [")
.append(ticket).append("]").toString(), e);
}
}
/**
* 授权
* */
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principals) {
Principal principal = (Principal) getAvailablePrincipal(principals);
User user = getSystemService().getUserByLoginName(principal.getLoginName());
if (user != null) {
SimpleAuthorizationInfo info = new SimpleAuthorizationInfo();
List<Menu> list = UserUtils.getMenuList();
for (Menu menu : list){
if (org.apache.commons.lang3.StringUtils.isNotBlank(menu.getPermission())){
// 添加基于Permission的权限信息
for (String permission : org.apache.commons.lang3.StringUtils.split(menu.getPermission(),",")){
info.addStringPermission(permission);
}
}
}
// 添加用户权限
info.addStringPermission("user");
// 添加用户角色信息
for (Role role : user.getRoleList()){
info.addRole(role.getEnname());
}
// 更新登录IP和时间
getSystemService().updateUserLoginInfo(user);
// 记录登录日志
LogUtils.saveLog(Servlets.getRequest(), "系统登录");
return info;
} else {
return null;
}
}
protected List<String> split(String s) {
List<String> list = new ArrayList<String>();
String elements[] = StringUtils.split(s, ',');
if (elements != null && elements.length > 0) {
String arr$[] = elements;
int len$ = arr$.length;
for (int i$ = 0; i$ < len$; i$++) {
String element = arr$[i$];
if (StringUtils.hasText(element))
list.add(element.trim());
}
}
return list;
}
protected void addRoles(SimpleAuthorizationInfo simpleAuthorizationInfo, List<String> roles) {
String role;
for (Iterator<String> i$ = roles.iterator(); i$.hasNext(); simpleAuthorizationInfo.addRole(role))
role = (String) i$.next();
}
protected void addPermissions(SimpleAuthorizationInfo simpleAuthorizationInfo, List<String> permissions) {
String permission;
for (Iterator<String> i$ = permissions.iterator(); i$.hasNext(); simpleAuthorizationInfo
.addStringPermission(permission))
permission = (String) i$.next();
}
public SystemService getSystemService() {
if (systemService == null){
systemService = SpringContextHolder.getBean(SystemService.class);
}
return systemService;
}
}
3.需要注意的事项:
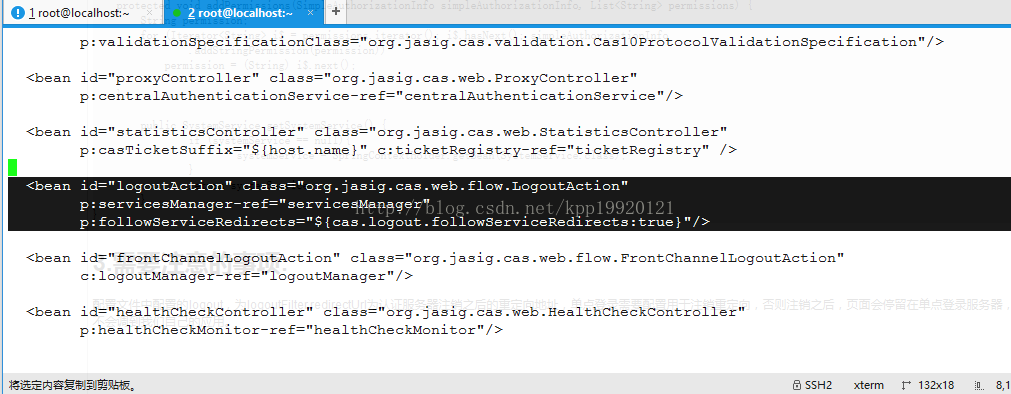
配置文件中配置的logout,为logoutFilter,redirectUrl为认证服务器注销之后的重定向地址,单点登录需要配置用于注销重定向,否则注销之后,页面会停留在单点登录服务器,不会调到我们自己的应用。修改认证服务器的cas-servlet,路径为WEB-INF/cas-servet.xml,把false改为true






















 1758
1758

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








