0x01 前言(Register)
webhacking.kr
最近发现了一个好玩的Web练习题库,先是注册我就没找到button(后来发现是Firebug自动把注释去掉了尼玛),看一下源码,会找到注册的按钮的
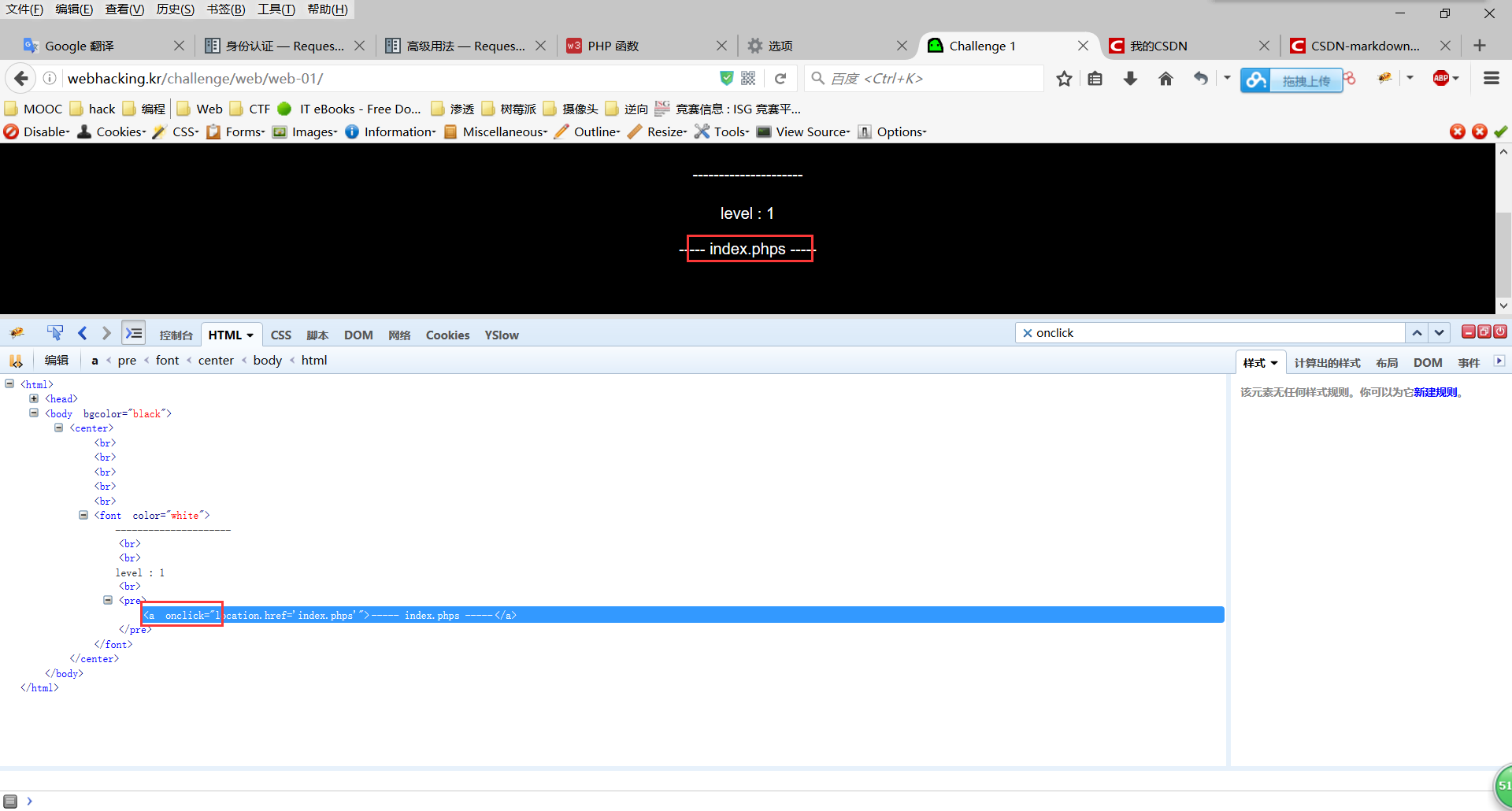
0x02 Challenge 1
查看源码,发现一个onclick
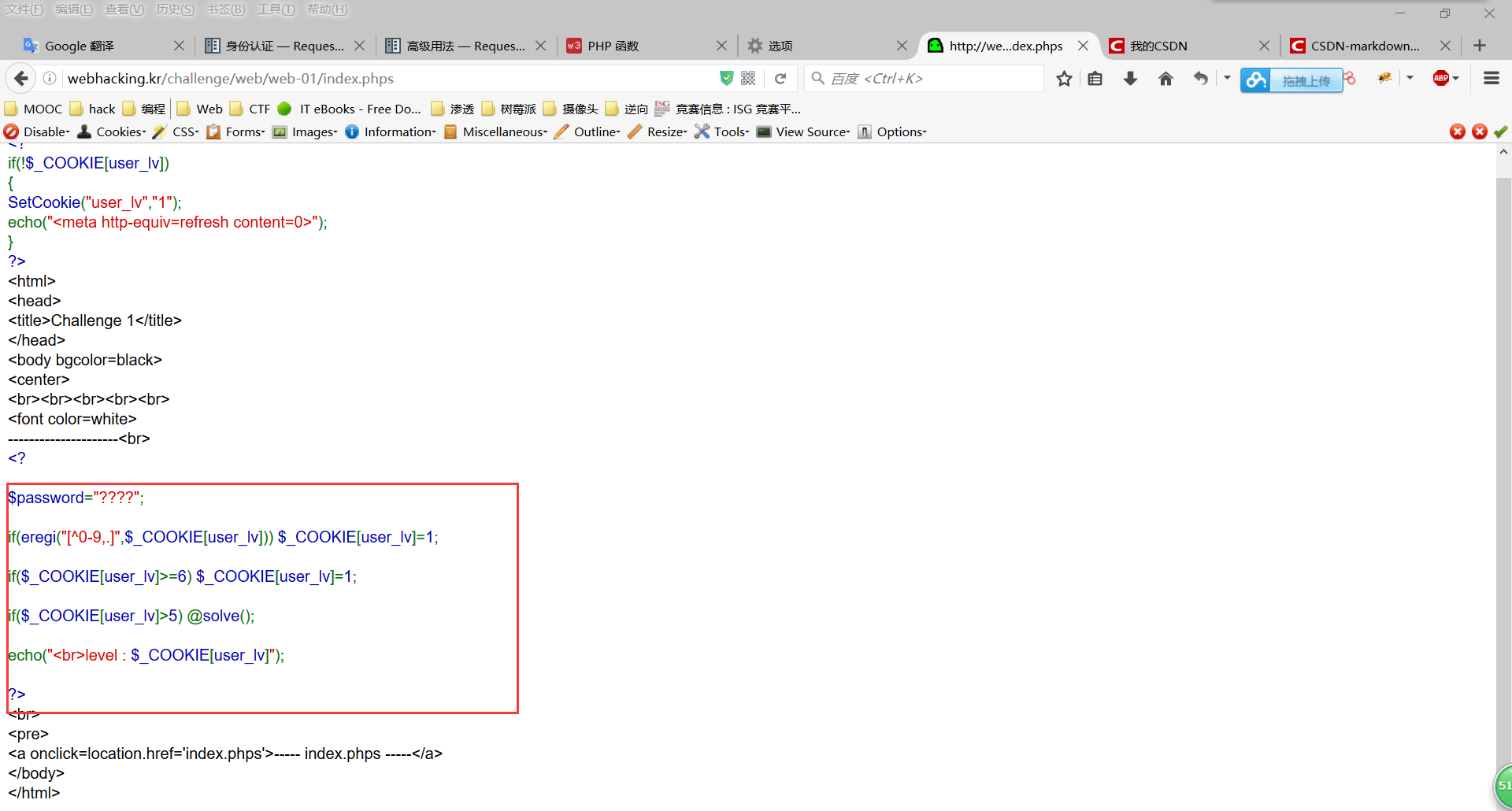
这里发现一个正则
正则的意思是,如果user_lv不是数字,那么user_lv=1,如果user_lv大于6,那么user_lv=1,如果user_lv大于5,那么问题解决;
所以我们抓包,吧user_lv改为5.1即可
0x02 Challenge 2
(棒子的网站看到韩文好不习惯。。)
做题蒙蔽的时候发现原来还有人和我一起蒙蔽,这题参考了他的wp
并且他的Py脚本对我这个弱鸡很有参考价值。。
bengdawang的Blog
具体的参考他写的就好了,在其中的注入环节我尝试了sqlmap的POST注入和cookie注入,均无果,下面整理一下我参阅的文章。
Cookie
坚持的蜗牛
Temper
Temper的使用方法与部分脚本的功能
SQLMAP过WAF
POST
POST注入实例
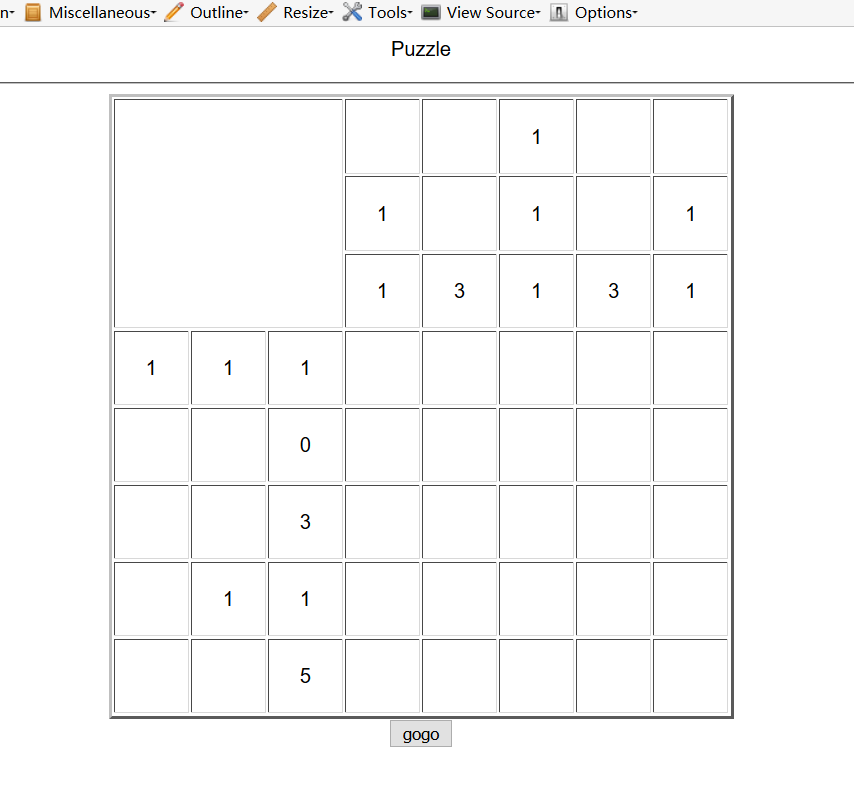
0x03 Challenge 3
上来一脸蒙蔽。。
猜测数字是每行每列黑色块的分布,区别于连续与不连续,于是尝试描绘形状即可。
剩下的一个answer的sql注入我不会了,但是通过这次题掌握了很多的sqlmap的用法。
0x04 Challenge4
先是base64,再是sha1,在是md5。
PS:sha1和md5有什么区别?貌似在某些情况下得到的摘要是一样的?
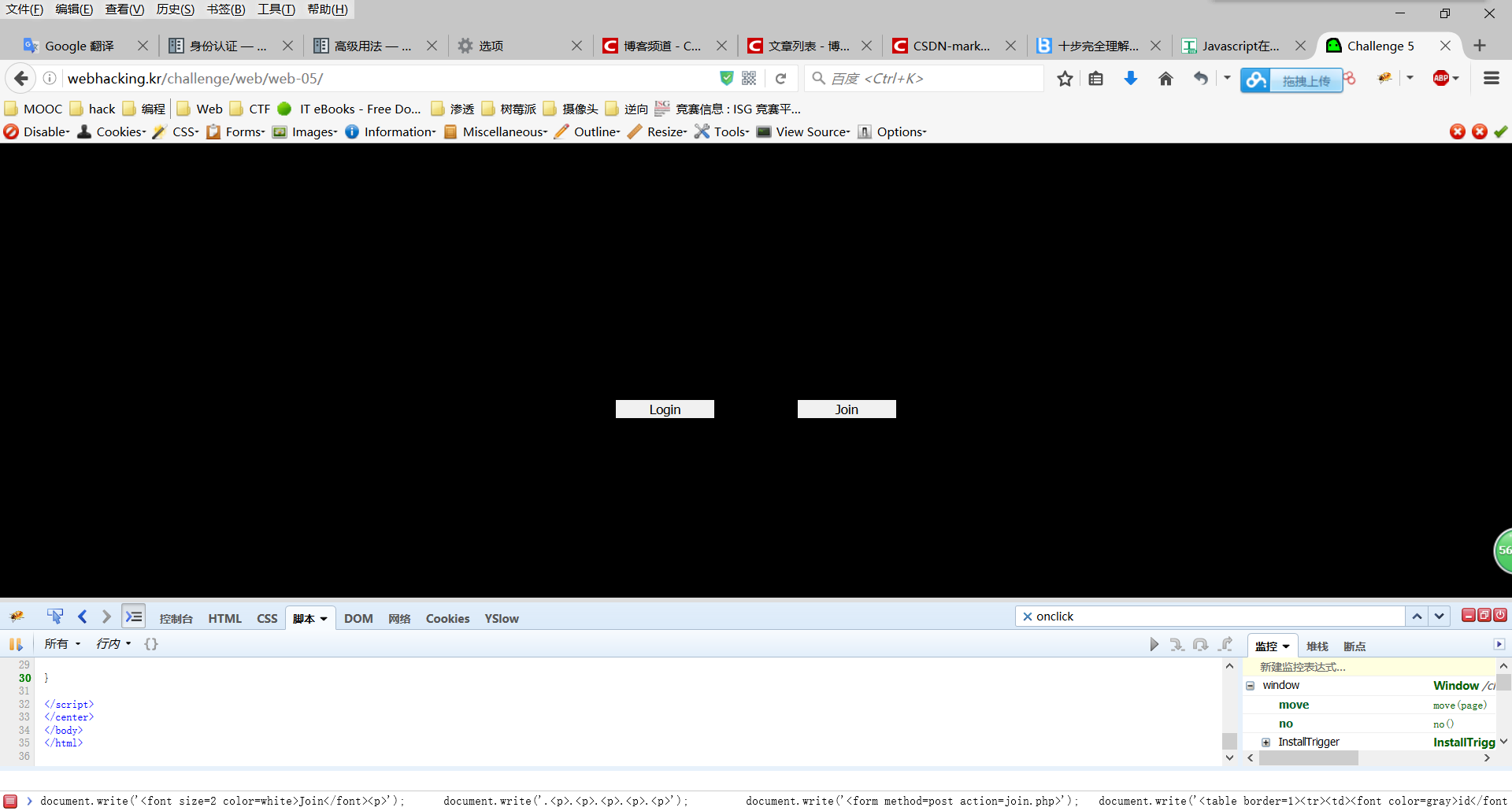
0x05 Challenge5
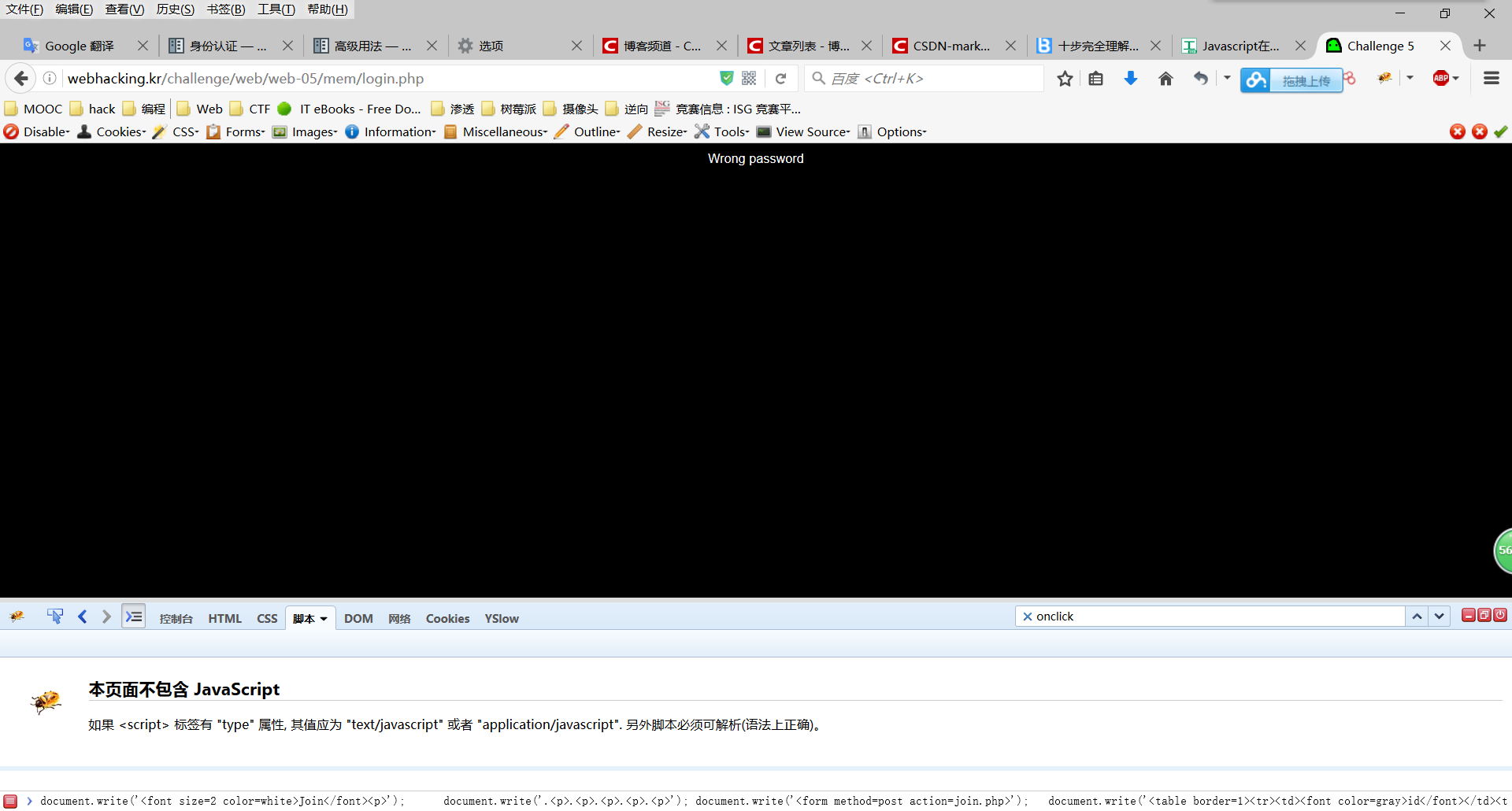
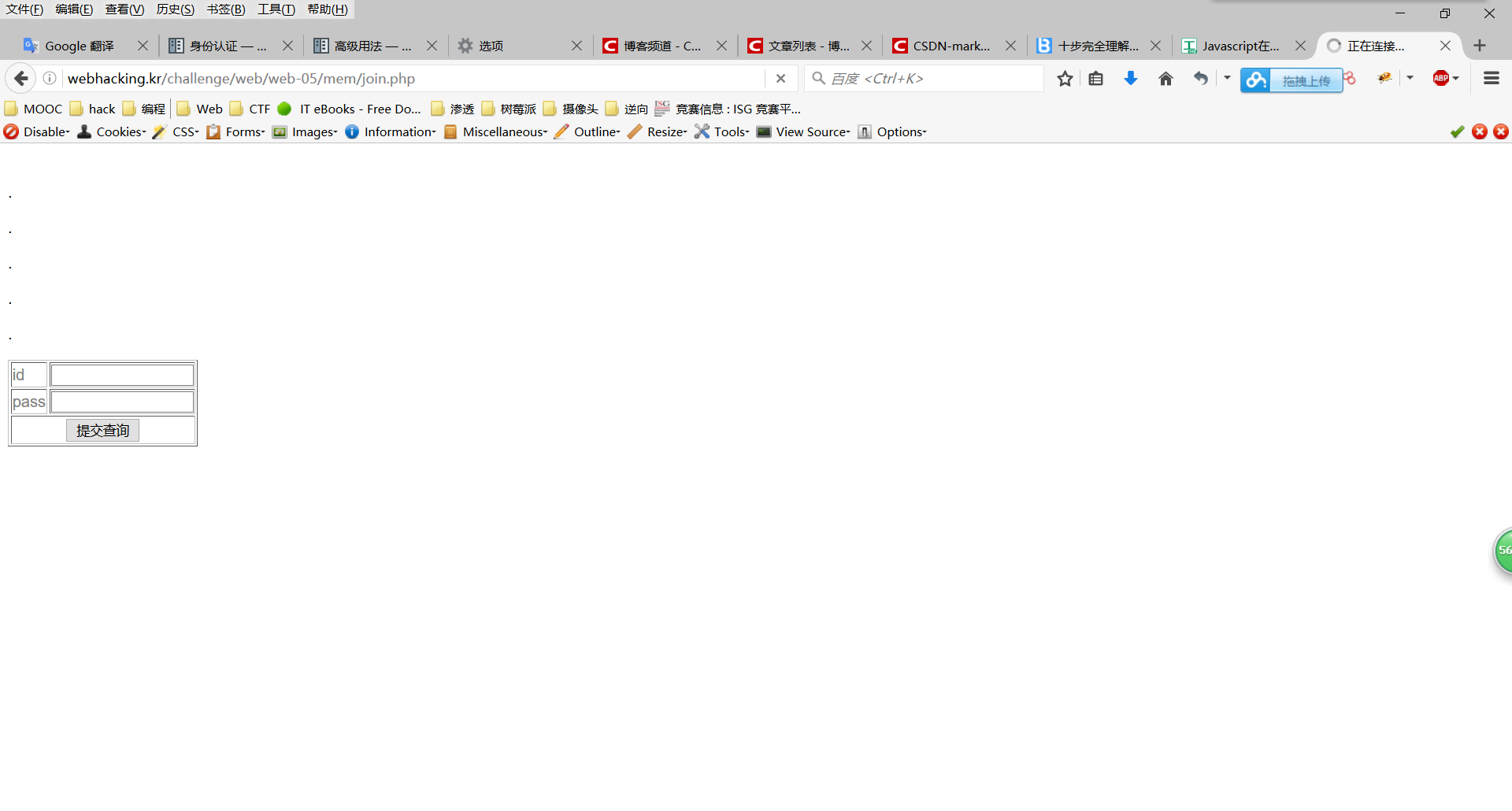
首先是login与join
login点开后发现是admin才能登陆
随便试了几个密码发现不对,而且这里貌似没什么注入(貌似这种地方都没什么注入)
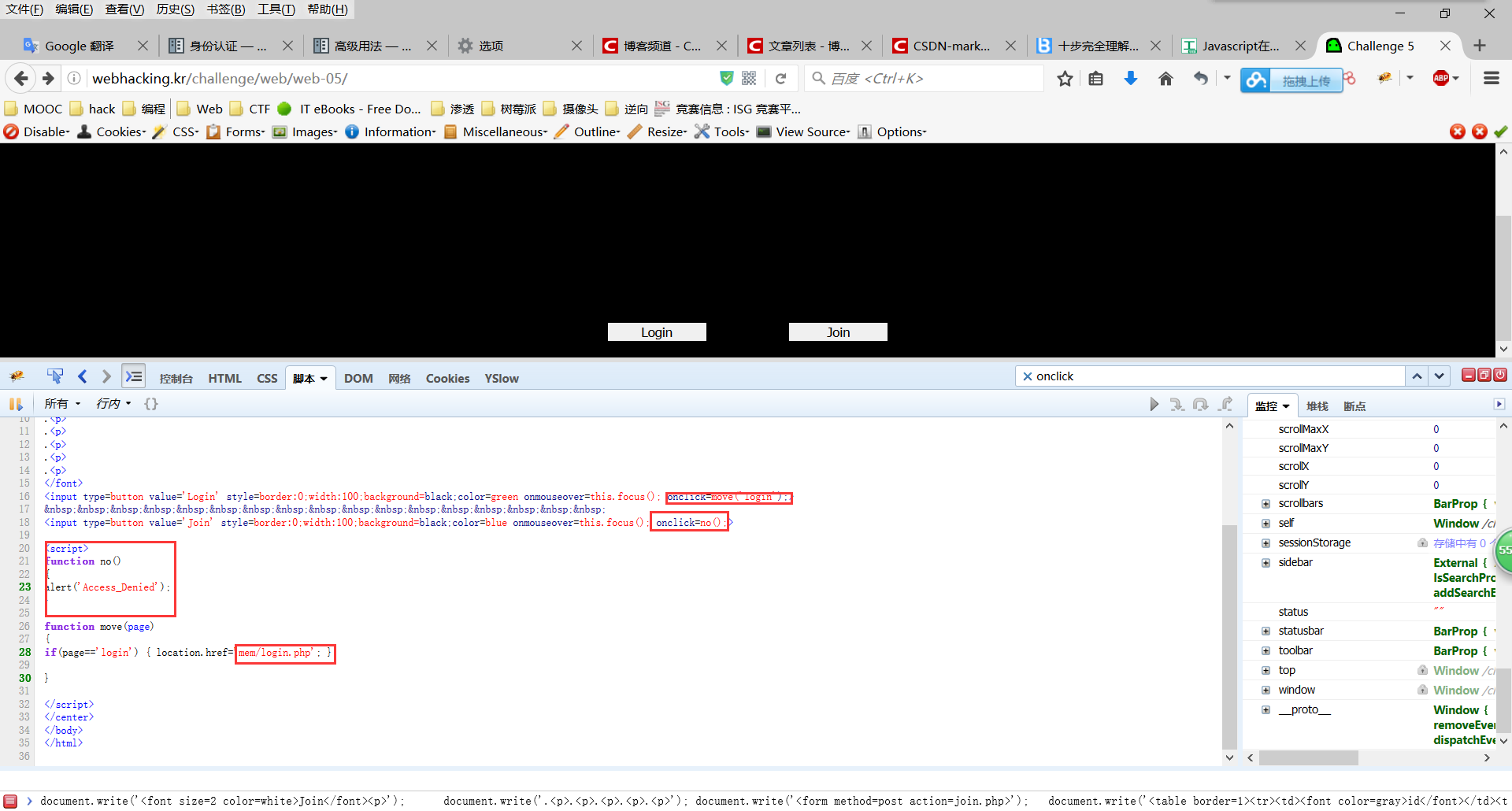
F12看一下,login是跳到/mem/login.php,join是本地的no函数
于是猜测存在/mem/join.php,果然
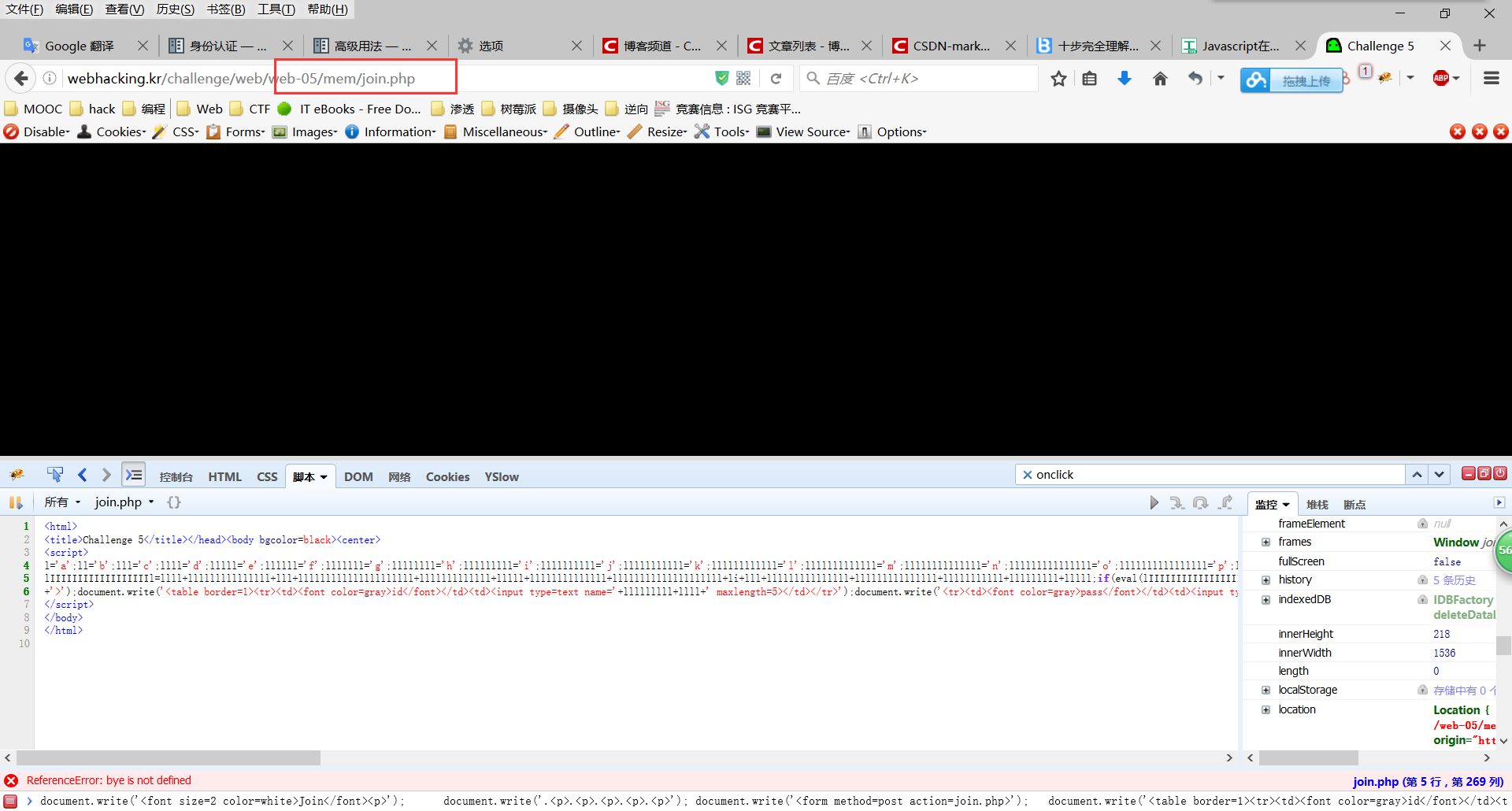
查看源码,发现js,整理并手动翻译了一下(py的print)。。
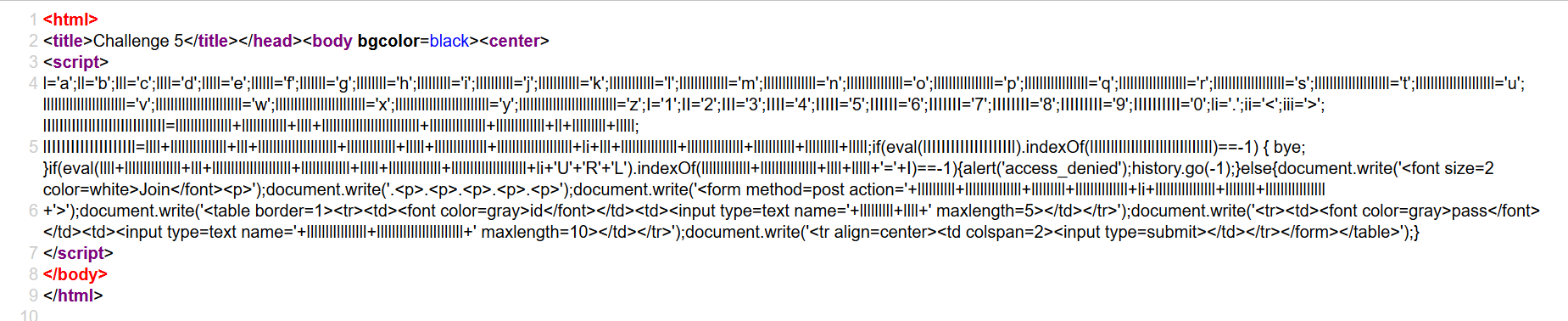
l = 'a';
ll = 'b';
lll = 'c';
llll = 'd';
lllll = 'e';
llllll = 'f';
lllllll = 'g';
llllllll = 'h';
lllllllll = 'i';
llllllllll = 'j';
lllllllllll = 'k';
llllllllllll = 'l';
lllllllllllll = 'm';
llllllllllllll = 'n';
lllllllllllllll = 'o';
llllllllllllllll = 'p';
lllllllllllllllll = 'q';
llllllllllllllllll = 'r';
lllllllllllllllllll = 's';
llllllllllllllllllll = 't';
lllllllllllllllllllll = 'u';
llllllllllllllllllllll = 'v';
lllllllllllllllllllllll = 'w';
llllllllllllllllllllllll = 'x';
lllllllllllllllllllllllll = 'y';
llllllllllllllllllllllllll = 'z';
I = '1';
II = '2';
III = '3';
IIII = '4';
IIIII = '5';
IIIIII = '6';
IIIIIII = '7';
IIIIIIII = '8';
IIIIIIIII = '9';
IIIIIIIIII = '0';
li = '.';
ii = '<';
iii = '>';
lIllIllIllIllIllIllIllIllIllIl = lllllllllllllll + llllllllllll + llll + llllllllllllllllllllllllll + lllllllllllllll + lllllllllllll + ll + lllllllll + lllll;
lIIIIIIIIIIIIIIIIIIl = llll + lllllllllllllll + lll + lllllllllllllllllllll + lllllllllllll + lllll + llllllllllllll + llllllllllllllllllll + li + lll + lllllllllllllll + lllllllllllllll + lllllllllll + lllllllll + lllll;
if (eval(oldzombie).indexOf(document.cookie) == -1) {
bye
}
if (eval(document.URL).indexOf(mode=1) == -1) {
alert('access_denied');
history.go(-1)
} else {
document.write('<font size=2 color=white>Join</font><p>');
document.write('.<p>.<p>.<p>.<p>.<p>');
document.write('<form method=post action=join.php>');
document.write('<table border=1><tr><td><font color=gray>id</font></td><td><input type=text name=id maxlength=5></td></tr>');
document.write('<tr><td><font color=gray>pass</font></td><td><input type=text name=pw maxlength=10></td></tr>');
document.write('<tr align=center><td colspan=2><input type=submit></td></tr></form></table>')
}其中有用的是下面一部分
document.write('<font size=2 color=white>Join</font><p>');
document.write('.<p>.<p>.<p>.<p>.<p>');
document.write('<form method=post action=join.php>');
document.write('<table border=1><tr><td><font color=gray>id</font></td><td><input type=text name=id maxlength=5></td></tr>');
document.write('<tr><td><font color=gray>pass</font></td><td><input type=text name=pw maxlength=10></td></tr>');
document.write('<tr align=center><td colspan=2><input type=submit></td></tr></form></table>')把这段代码放到浏览器里运行
尝试,发现好像是添加账号,于是添加admin,发现失败
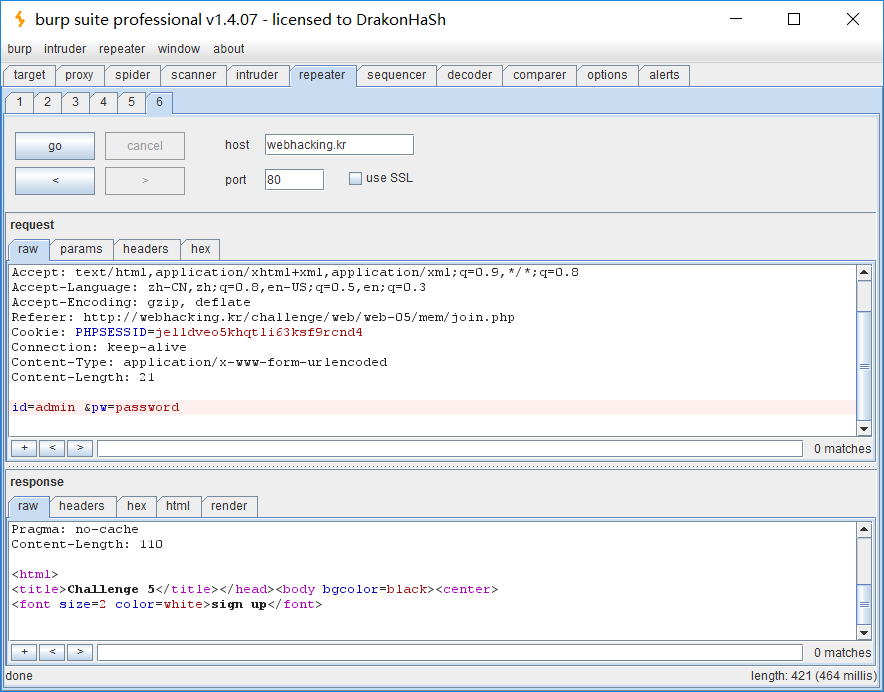
于是蒙逼了,看了下别人的解法,说是在admin后面加上空格,于是抓包,加上空格,提示sign up
于是我们再回到login.php,输入admin password,成功
(PS:在admin后面加上空格是什么注入原理?)





















 4443
4443











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








