前言
在当今信息安全领域,特别是恶意软件分析中,经常需要利用到 虚拟机技术,以提高病毒分析过程的安全性以及硬件资源的节约性,因此它在恶意软件领域中是应用越来越来广泛。这里我们所谓的 虚拟机(Virtual Machine)是指通过软件模拟的具有完整硬件系统功能的、运行在一个完全隔离环境中的完整计算机系统。通过 虚拟机软件(比如VMware,Virtual PC ,VirtualBox),你可以在一台物理计算机上模拟出一台或多台 虚拟的计算机,这些 虚拟机完全就像真正的计算机那样进行工作,例如你可以安装操作系统、安装应用程序、访问网络资源等等。攻击者为了提高恶意程序的隐蔽性以及破坏真实主机的成功率,他们都在恶意程序中加入检测 虚拟机的代码,以判断程序所处的运行环境。当发现程序处于 虚拟机(特别是蜜罐系统)中时,它就会改变操作行为或者中断执行,以此提高反病毒人员分析恶意软件行为的难度。本文主要针对基于Intel CPU的 虚拟环境VMware中的Windows XP SP3系统进行检测分析,并列举出当前常见的几种 虚拟机检测方法。方法一:通过执行特权指令来检测虚拟机
bool IsInsideVMWare()
{
bool rc = true;
__try
{
__asm
{
push edx
push ecx
push ebx
mov eax, 'VMXh'
mov ebx, 0 // 将ebx设置为非幻数’VMXH’的其它值
mov ecx, 10 // 指定功能号,用于获取VMWare版本,当它为0x14时用于获取VMware内存大小
mov edx, 'VX' // 端口号
in eax, dx // 从端口dx读取VMware版本到eax
//若上面指定功能号为0x14时,可通过判断eax中的值是否大于0,若是则说明处于虚拟机中
cmp ebx, 'VMXh' // 判断ebx中是否包含VMware版本’VMXh’,若是则在虚拟机中
setz [rc] // 设置返回值
pop ebx
pop ecx
pop edx
}
}
__except(EXCEPTION_EXECUTE_HANDLER) //如果未处于VMware中,则触发此异常
{
rc = false;
}
return rc;
}
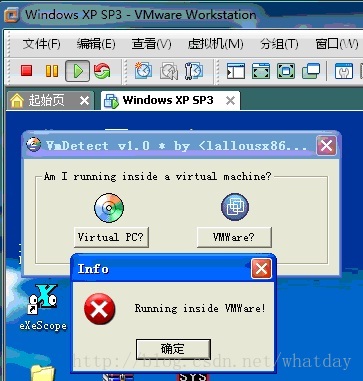
图1
如图1所示,VMDetect成功检测出VMWare的存在。
方法二:利用IDT基址检测虚拟机
利用IDT基址检测 虚拟机的方法是一种通用方式,对VMware和Virtual PC均适用。中断描述符表IDT(Interrupt Descriptor Table)用于查找处理中断时所用的软件函数,它是一个由256项组成的数据,其中每一中断对应一项函数。为了读取IDT基址,我们需要通过SIDT指令来读取IDTR(中断描述符表寄存器,用于IDT在内存中的基址),SIDT指令是以如下格式来存储IDTR的内容:typedef struct
{
WORD IDTLimit; // IDT的大小
WORD LowIDTbase; // IDT的低位地址
WORD HiIDTbase; // IDT的高位地址
} IDTINFO;
#include <stdio.h>
int main () {
unsigned char m[2+4], rpill[] = "\x0f\x01\x0d\x00\x00\x00\x00\xc3"; //相当于SIDT[adrr],其中addr用于保存IDT地址
*((unsigned*)&rpill[3]) = (unsigned)m; //将sidt[addr]中的addr设为m的地址
((void(*)())&rpill)(); //执行SIDT指令,并将读取后IDT地址保存在数组m中
printf ("idt base: %#x\n", *((unsigned*)&m[2])); //由于前2字节为IDT大小,因此从m[2]开始即为IDT地址
if (m[5]>0xd0) printf ("Inside Matrix!\n", m[5]); //当IDT基址大于0xd0xxxxxx时则说明程序处于VMware中
else printf ("Not in Matrix.\n");
return 0;
}
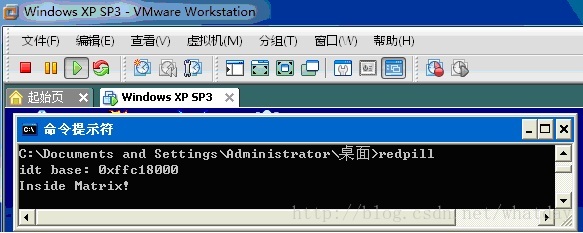
图2
利用此IDT检测的方法存在一个缺陷,由于IDT的值只针对处于正在运行的处理器而言,在单CPU中它是个常量,但当它处于多CPU时就可能会受到影响了,因为每个CPU都有其自己的IDT,这样问题就自然而然的产生了。针对此问题,Offensive Computing组织成员提出了两种应对方法,其中一种方法就是利用Redpill反复地在系统上循环执行任务,以此构造出一张当前系统的IDT值变化统计图,但这会增加CPU负担;另一种方法就是windows API函数SetThreadAffinityMask()将线程限制在单处理器上执行,当执行此测试时只能准确地将线程执行环境限制在本地处理器,而对于将线程限制在VM处理器上就可能行不通了,因为VM是计划在各处理器上运行的,VM线程在不同的处理器上执行时,IDT值将会发生变化,因此此方法也是很少被使用的。为此,有人提出了使用LDT的检测方法,它在具有多个CPU的环境下检测 虚拟机明显优于IDT检测方法,该方法具体内容参见下节内容。
方法三:利用LDT和GDT的检测方法
在 《Intel® 64 and IA-32 Architecture Software Developer’s Manual Volume 3A: System Programming Guide》第二章的Vol.3 2-5 一页(我的Intel开发手册是2008版的)中对于LDT和GDT的描述如下(以下内容为个人翻译):在保护模式下,所有的内存访问都要通过全局描述符表(GDT)或者本地描述符表(LDT)才能进行。这些表包含有段描述符的调用入口。各个段描述符都包含有各段的基址,访问权限,类型和使用信息,而且每个段描述符都拥有一个与之相匹配的段选择子,各个段选择子都为软件程序提供一个GDT或LDT索引(与之相关联的段描述符偏移量),一个全局/本地标志(决定段选择子是指向GDT还是LDT),以及访问权限信息。
若想访问段中的某一字节,必须同时提供一个段选择子和一个偏移量。段选择子为段提供可访问的段描述符地址(在GDT 或者LDT 中)。通过段描述符,处理器从中获取段在线性地址空间里的基址,而偏移量用于确定字节地址相对基址的位置。假定处理器在当前权限级别(CPL)可访问这个段,那么通过这种机制就可以访问在GDT 或LDT 中的各种有效代码、数据或者堆栈段,这里的CPL是指当前可执行代码段的保护级别。
……
GDT的线性基址被保存在GDT寄存器(GDTR)中,而LDT的线性基址被保存在LDT寄存器(LDTR)中。
由于 虚拟机与真实主机中的GDT和LDT并不能相同,这与使用IDT的检测方法一样,因此 虚拟机必须为它们提供一个“复制体”。关于GDT和LDT的基址可通过SGDT和SLDT指令获取。 虚拟机检测工具Scoopy suite的作者Tobias Klein经测试发现,当LDT基址位于0x0000(只有两字节)时为真实主机,否则为 虚拟机,而当GDT基址位于0xFFXXXXXX时说明处于 虚拟机中,否则为真实主机。具体实现代码如下:
#include <stdio.h>
void LDTDetect(void)
{
unsigned short ldt_addr = 0;
unsigned char ldtr[2];
_asm sldt ldtr
ldt_addr = *((unsigned short *)&ldtr);
printf("LDT BaseAddr: 0x%x\n", ldt_addr);
if(ldt_addr == 0x0000)
{
printf("Native OS\n");
}
else
printf("Inside VMware\n");
}
void GDTDetect(void)
{
unsigned int gdt_addr = 0;
unsigned char gdtr[4];
_asm sgdt gdtr
gdt_addr = *((unsigned int *)&gdtr[2]);
printf("GDT BaseAddr:0x%x\n", gdt_addr);
if((gdt_addr >> 24) == 0xff)
{
printf("Inside VMware\n");
}
else
printf("Native OS\n");
}
int main(void)
{
LDTDetect();
GDTDetect();
return 0;
}
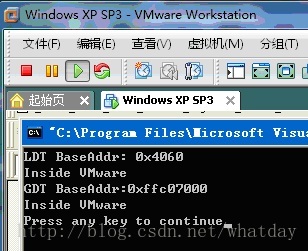
图3
方法四:基于STR的检测方法
在保护模式下运行的所有程序在切换任务时,对于当前任务中指向TSS的段选择器将会被存储在任务寄存器中,TSS中包含有当前任务的可执行环境状态,包括通用寄存器状态,段寄存器状态,标志寄存器状态,EIP寄存器状态等等,当此项任务再次被执行时,处理器就会其原先保存的任务状态。每项任务均有其自己的TSS,而我们可以通过STR指令来获取指向当前任务中TSS的段选择器。这里STR(Store task register)指令是用于将任务寄存器 (TR) 中的段选择器存储到目标操作数,目标操作数可以是通用寄存器或内存位置,使用此指令存储的段选择器指向当前正在运行的任务的任务状态段 (TSS)。在 虚拟机和真实主机之中,通过STR读取的地址是不同的,当地址等于0x0040xxxx时,说明处于 虚拟机中,否则为真实主机。实现代码如下:#include <stdio.h>
int main(void)
{
unsigned char mem[4] = {0};
int i;
__asm str mem;
printf (" STR base: 0x");
for (i=0; i<4; i++)
{
printf("%02x",mem[i]);
}
if ( (mem[0]==0x00) && (mem[1]==0x40))
printf("\n INSIDE MATRIX!!\n");
else
printf("\n Native OS!!\n");
return 0;
}
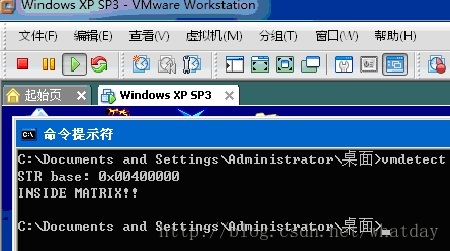
图4
方法五:基于注册表检测虚拟机
在windows 虚拟机中常常安装有VMware Tools以及其它的 虚拟硬件(如网络适配器、 虚拟打印机,USB集线器……),它们都会创建任何程序都可以读取的windows注册表项,因此我们可以通过检测注册表中的一些关键字符来判断程序是否处于 虚拟机之中。关于这些注册表的位置我们可以通过在注册表中搜索关键词“vmware”来获取,下面是我在VMware下的WinXP中找到的一些注册表项:项名:HKEY_CLASSES_ROOT\Applications\VMwareHostOpen.exe
项名:HKEY_CLASSES_ROOT\Installer\Products\C2A6F2EFE6910124C940B2B12CF170FE\ProductName
键值“VMware Tools”
项名:HKEY_CLASSES_ROOT\Installer\Products\C2A6F2EFE6910124C940B2B12CF170FE\SourceList\PackageName
键值:VMware Tools.msi
项名:HKEY_CURRENT_USER\Printers\DeviceOld
键值:_#VMwareVirtualPrinter,winspool,TPVM:
项名:HKEY_LOCAL_MACHINE\HARDWARE\DEVICEMAP\Scsi\Scsi Port 0\Scsi Bus 0\Target Id 0\Logical Unit Id 0\Identifier
键值:VMware Virtual IDE Hard Drive
项名:HKEY_LOCAL_MACHINE\HARDWARE\DEVICEMAP\Scsi\Scsi Port 1\Scsi Bus 0\Target Id 0\Logical Unit Id 0\Identifier
键值:NECVMWar VMware IDE CDR10
项名:HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Installer\Products\C2A6F2EFE6910124C940B2B12CF170FE\ProductName
键值:VMware Tools
项名:HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\C2A6F2EFE6910124C940B2B12CF170FE\InstallProperties\DisplayName
键值:VMware Tools
项名:HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Reinstall\0002\DeviceDesc
键值:VMware SVGA II
项名:HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\NetworkCards\2\Description
键值:VMware Accelerated AMD PCNet Adapter
项名:HKEY_LOCAL_MACHINE\SOFTWARE\VMware, Inc.\VMware Tools
项名:HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class\{4D36E968-E325-11CE-BFC1-08002BE10318}\0000\DriverDesc
键值:VMware SVGA II
项名:HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class\{4D36E968-E325-11CE-BFC1-
08002BE10318}\0000\ProviderName
键值:VMware, Inc.
项名:HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class\{4D36E972-E325-11CE-BFC1-08002bE10318}\0001\DriverDesc
键值:VMware Accelerated AMD PCNet Adapter
项名:HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class\{4D36E97B-E325-11CE-BFC1-08002BE10318}\0000\DriverDesc
键值:VMware SCSI Controller
项名:HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Print\Monitors\ThinPrint Print Port Monitor for VMWare
补充另外一处 具体代码如下:
BOOL DetectVM() {
HKEY hKey;
char szBuffer[64];
unsigned long hSize= sizeof(szBuffer) - 1;
if( RegOpenKeyEx( HKEY_LOCAL_MACHINE, "HARDWARE\\DESCRIPTION\\System\\BIOS\\", 0, KEY_READ, &hKey )==ERROR_SUCCESS ) {
RegQueryValueEx( hKey, "SystemManufacturer", NULL, NULL, (unsigned char *)szBuffer, &hSize );
if( strstr( szBuffer, "VMWARE" )) {
RegCloseKey( hKey );
return TRUE;
}
RegCloseKey( hKey );
}
return FALSE;
}.386 .model flat, stdcall option casemap:none include windows.inc include user32.inc include kernel32.inc include advapi32.inc includelib user32.lib includelib kernel32.lib includelib advapi32.lib .data szCaption db "VMware Detector ",0 szInside db "Inside VMware!",0 szOutside db "Native OS!",0 szSubKey db "software\VMWare, Inc.\VMware tools",0 hKey dd ? .code start: invoke RegOpenKeyEx, HKEY_LOCAL_MACHINE, addr szSubKey, 0,\ KEY_WRITE or KEY_READ, addr hKey .if eax == ERROR_SUCCESS invoke MessageBox, NULL,addr szInside, addr szCaption, MB_OK .else invoke MessageBox, NULL,addr szOutside, addr szCaption, MB_OK .endif invoke RegCloseKey,hKey invoke ExitProcess,NULL end start
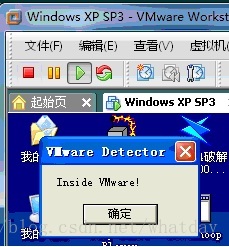
图5
方法六:基于时间差的检测方式
本方法通过运行一段特定代码,然后比较这段代码在 虚拟机和真实主机之中的相对运行时间,以此来判断是否处于 虚拟机之中。这段代码我们可以通过RDTSC指令来实现,RDTSC指令是用于将计算机启动以来的CPU运行周期数存放到EDX:EAX里面,其中EDX是高位,而EAX是低位。下面我们以xchg ecx, eax 一句指令的运行时间为例,这段指令在我的真实主机windows 7系统上的运行时间为0000001E,如图6所示: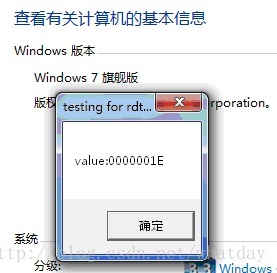
图6
而该指令在 虚拟机WinXP下的运行时间为00000442,如图7所示:
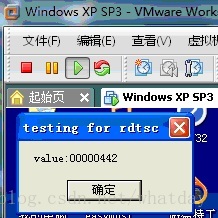
图7
两者之间的运行时间明显差别很多,在 虚拟机中的运行速度远不如真实主机的,一般情况下,当它的运行时间大于0xFF时,就可以确定它处于 虚拟机之中了,因此不难写出检测程序,具体实现代码如下:
.586p .model flat, stdcall option casemap:none include windows.inc include kernel32.inc include user32.inc includelib kernel32.lib includelib user32.lib .data szTitle db "VMDetect With RDTSC", 0h szInsideVM db "Inside VMware!", 0h szOutsideVM db "Native OS!", 0h .code start: RDTSC xchg ecx, eax RDTSC sub eax, ecx cmp eax, 0FFh jg Detected invoke MessageBox, 0, offset szOutsideVM, offset szTitle, 0 ret Detected: invoke MessageBox, 0, offset szInsideVM, offset szTitle, 0 ret end start
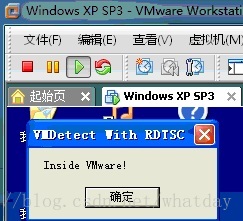
图8
方法七:利用虚拟硬件指纹检测虚拟机
利用 虚拟硬件指纹也可用于检测 虚拟机的存在,比如VMware默认的网卡MAC地址前缀为“00-05-69,00-0C-29或者00-50-56”,这前3节是由VMware分配的唯一标识符OUI,以供它的 虚拟化适配器使用。在我的VMWare WinXP下的MAC地址为00-0C-29-5B-D7-67,如图9所示: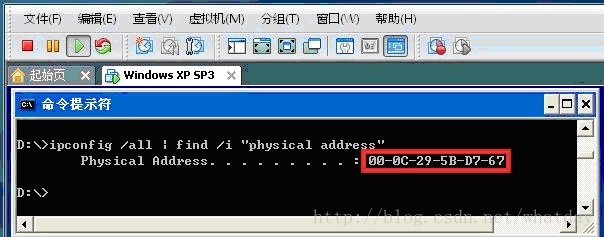
图9
但由于这些可经过修改配置文件来绕过检测。另外,还可通过检测特定的硬件控制器,BIOS,USB控制器,显卡,网卡等特征字符串进行检测,这些在前面使用注册表检测方法中已有所涉及。
另外之前在看雪论坛上也有朋友提到通过检测硬盘Model Number是否含有“vmware”或“virtual”等字样来实现检测虚拟机的功能,具体转载如下:
小试 anti vmware
今天偶然看到一款绿色版的硬盘专业工具,突然发现可以利用其中的一项功能来实现anti vmware。
今日事今日毕,那就在今晚12:00之前把这个想法实现吧,let's go!
我的想法就是检测硬盘的modelnumber,具体什么是modelnumber自己网上搜吧,反正不是硬盘序列号。难点就是在多种操作系统下都要能起到anti vmware的效果。程序在xp、2k、2003下都可以检测到vmware的运行。
直接贴代码了,如果看不懂也没关系,我也是逆了人家的代码写出来的。Delphi也可以当汇编语言开发工具用,难道不是吗?
unit Unit1;
interface
uses
Windows, Messages, SysUtils, Variants, Classes, Graphics, Controls, Forms,
Dialogs, StdCtrls, Buttons;
type
TForm1 = class(TForm)
BitBtn1: TBitBtn;
procedure BitBtn1Click(Sender: TObject);
procedure FormClose(Sender: TObject; var Action: TCloseAction);
private
{ Private declarations }
public
{ Public declarations }
end;
var
Form1: TForm1;
hDeviceHandle:Thandle;
implementation
{$R *.dfm}
procedure TForm1.BitBtn1Click(Sender: TObject);
var
InBuffer: array[0..$8f] of byte;
cb:Cardinal;
tmp:Pchar;
begin
hDeviceHandle:=CreateFile('\\.\PHYSICALDRIVE0',$C0000000,$3,nil,OPEN_EXISTING,$8000000,0);
ZeroMemory(@InBuffer,sizeof(InBuffer));
asm
pushad
lea ebx,InBuffer
xor ecx,ecx
mov al,$2c
MOV [ebx],al
MOV EAX,$200c0000
MOV [ebx+4], eax
mov al,$01
MOV [ebx+8],al
mov al,$40
MOV [ebx+$c],al
MOV EAX,$0001a5E0
MOV [ebx+$10], eax
mov al,$30
MOV [ebx+$18],al
mov al,$12
MOV [ebx+$1c],al
mov al,$40
MOV [ebx+$20],al
add ecx,ebx
add ecx,$50
MOV [ebx+$14], ecx
popad
end;
if DeviceIoControl(hDeviceHandle,$4D014,@InBuffer,$50,@InBuffer,$50,cb,nil) then
begin
asm
pushad
lea ebx,InBuffer
add ebx,$58
mov tmp,ebx
popad
end; //asm
if ((pos('vmware',LowerCase(tmp))>0) or (pos('virtual',LowerCase(tmp))>0)) then
showmessage('检测到 VMware Workstation!!!')
else
showmessage('请在VMware中测试!');
end;
end;
procedure TForm1.FormClose(Sender: TObject; var Action: TCloseAction);
begin
closehandle(hDeviceHandle);
end;
end.
代码很短,但是效果不错。截图几张,留作纪念!C++代码实现如下:
通过IOCTL_STORAGE_QUERY_PROPERTY
typedef enum _STORAGE_QUERY_TYPE {PropertyStandardQuery = 0,PropertyExistsQuery,PropertyMaskQuery,PropertyQueryMaxDefined} STORAGE_QUERY_TYPE, *PSTORAGE_QUERY_TYPE;
typedef enum _STORAGE_PROPERTY_ID {StorageDeviceProperty = 0,StorageAdapterProperty} STORAGE_PROPERTY_ID, *PSTORAGE_PROPERTY_ID;
typedef struct _STORAGE_PROPERTY_QUERY {
STORAGE_PROPERTY_ID PropertyId;
STORAGE_QUERY_TYPE QueryType;
UCHAR AdditionalParameters[1];
} STORAGE_PROPERTY_QUERY, *PSTORAGE_PROPERTY_QUERY;
typedef struct _STORAGE_DEVICE_DESCRIPTOR {
ULONG Version;
ULONG Size;
UCHAR DeviceType;
UCHAR DeviceTypeModifier;
BOOLEAN RemovableMedia;
BOOLEAN CommandQueueing;
ULONG VendorIdOffset;
ULONG ProductIdOffset;
} STORAGE_DEVICE_DESCRIPTOR, *PSTORAGE_DEVICE_DESCRIPTOR;
#define IOCTL_STORAGE_QUERY_PROPERTY CTL_CODE(IOCTL_STORAGE_BASE, 0x0500, METHOD_BUFFERED, FILE_ANY_ACCESS)
bool IsSandboxed()
{
HANDLE hPhysicalDriveIOCTL = 0;
int j = 0,k = 0;
char szModel[128],szBuffer[128];
char *szDrives[] = {
"qemu",
"virtual",
"vmware",
NULL
};
hPhysicalDriveIOCTL = CreateFile ("\\\\.\\PhysicalDrive0", 0,FILE_SHARE_READ | FILE_SHARE_WRITE, NULL,OPEN_EXISTING, 0, NULL);
if (hPhysicalDriveIOCTL != INVALID_HANDLE_VALUE)
{
STORAGE_PROPERTY_QUERY query;
DWORD cbBytesReturned = 0;
memset ((void *) & query, 0, sizeof (query));
query.PropertyId = StorageDeviceProperty;
memset (szBuffer, 0, sizeof (szBuffer));
memset (szModel, 0, sizeof (szModel));
if (DeviceIoControl(hPhysicalDriveIOCTL, IOCTL_STORAGE_QUERY_PROPERTY,& query,sizeof (query),& szBuffer,sizeof (szBuffer),& cbBytesReturned, NULL)){
STORAGE_DEVICE_DESCRIPTOR *descrip = (STORAGE_DEVICE_DESCRIPTOR*)&szBuffer;
int pos = descrip->ProductIdOffset;
int m = 0;
for(int g = pos;szBuffer[g] != '\0';g++){
szModel[m++] = szBuffer[g];
}
CharLowerBuff(szModel,strlen(szModel));
for (int i = 0; i < (sizeof(szDrives)/sizeof(LPSTR)) - 1; i++ ) {
if (szDrives[i][0] != 0) {
if(strstr(szModel,szDrives[i]))
return TRUE;
}
}
}
CloseHandle (hPhysicalDriveIOCTL);
}
return FALSE;
}总结
国外SANS安全组织的研究人员总结出当前各种 虚拟机检测手段不外乎以下四类:
● 搜索 虚拟环境中的进程,文件系统,注册表;
● 搜索 虚拟环境中的内存
● 搜索 虚拟环境中的特定 虚拟硬件
● 搜索 虚拟环境中的特定处理器指令和功能
因为现代计算系统大多是由文件系统,内存,处理器及各种硬件组件构成的,上面提到的四种检测手段均包含了这些因素。纵观前面各种检测方法,也均在此四类当中。除此之外,也有人提出通过网络来检测虚拟机,比如搜索ICMP和TCP数据通讯的时间差异,IP ID数据包差异以及数据包中的异常头信息等等。随着技术研究的深入,相信会有更多的检测手段出现,与此同时,虚拟机厂商也会不断进化它们的产品,以增加anti-vmware的难度,这不也正是一场永无休止的无烟战争!
================================================================================
anti VM的解决方法
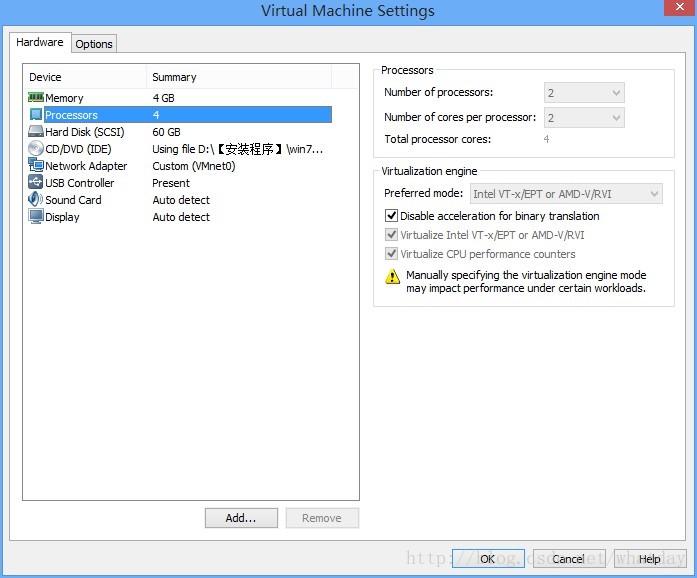
对于上边 方法一二三四六的解决方案是 :
1.在本机BIOS的CPU设置中开启VT(虚拟化)选项。 注意要先做这一步以后 才能安装VM 顺序错了只能把VM完全卸载重新安装。
2.新建虚拟机 在CPU设置如下图设置:
主要目的是为了 关闭二进制优化 开启虚拟机的VT虚拟化。
3.关闭一些虚拟机的设置 用记事本打开 VMX 文件 这个文件是VM的配置文件 如类似地址"C:\VM Machines\Windows 7 (32位)\Windows 7 (32位).vmx",在文本末尾加入
isolation.tools.getPtrLocation.disable = "TRUE"
isolation.tools.setPtrLocation.disable = "TRUE"
isolation.tools.setVersion.disable = "TRUE"
isolation.tools.getVersion.disable = "TRUE"
monitor_control.disable_directexec = "TRUE"
monitor_control.disable_chksimd = "TRUE"
monitor_control.disable_ntreloc = "TRUE"
monitor_control.disable_selfmod = "TRUE"
monitor_control.disable_reloc = "TRUE"
monitor_control.disable_btinout = "TRUE"
monitor_control.disable_btmemspace = "TRUE"
monitor_control.disable_btpriv = "TRUE"
monitor_control.disable_btseg = "TRUE"
monitor_control.restrict_backdoor = "TRUE"方法七的解决方案就是修改硬件信息,这里的VM特征硬件信息有很多,这里只说网卡的,直接下载一个mac地址修改器,修改mac这样一来mac地址就不是VM特有的了,从而达到过方法七的效果。
方法五,很多商业软件都是用这个方法来验证,原因很简单不管是在驱动还是在应用层都可以很方便的读取注册表,只要保护开发人员自己安装一个VM就能提取里边特征注册码,这个解决方案就是 搜索注册表的“VMware” "virtual" 等字段,把能修改的都修改了,然后导出注册表,以便重启系统后导入,因为重启VM后有些注册表信息会还原。
实例如下:
环境:VM虚拟机 WIN7 32位,光盘镜像名称 XBL_GHOST_WIN7_SP1_07ZJB.iso
原理:修改注册表中的 “VMware” 修改为了 “test123”
注册表:
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SystemInformation]
"BIOSVersion"="6.00"
"BIOSReleaseDate"="07/02/2012"
"SystemManufacturer"="test123, Inc."
"SystemProductName"="test123 test123 Platform"
"InformationSource"=dword:00000001
[HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS]
"BiosMajorRelease"=dword:00000004
"BiosMinorRelease"=dword:00000006
"ECFirmwareMajorRelease"=dword:00000000
"ECFirmwareMinorRelease"=dword:00000000
"BaseBoardManufacturer"="Intel Corporation"
"BaseBoardProduct"="440BX Desktop Reference Platform"
"BaseBoardVersion"="None"
"BIOSReleaseDate"="07/02/2012"
"BIOSVendor"="Phoenix Technologies LTD"
"BIOSVersion"="6.00"
"SystemFamily"=""
"SystemManufacturer"="test123, Inc."
"SystemProductName"="test123 test123 Platform"
"SystemSKU"=""
"SystemVersion"="None"
[HKEY_LOCAL_MACHINE\HARDWARE\DEVICEMAP\Scsi\Scsi Port 2\Scsi Bus 0\Target Id 0\Logical Unit Id 0]
"InquiryData"=hex:00,00,02,02,1f,00,00,73,56,4d,77,61,72,65,2c,20,56,4d,77,61,\
72,65,20,56,69,72,74,75,61,6c,20,53,31,2e,30,20
"Identifier"="test123, test123 Virtual S1.0 "
"DeviceType"="DiskPeripheral"
[HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class\{4D36E968-E325-11CE-BFC1-08002BE10318}\0000]
"CoInstallers32"=hex(7):76,00,6d,00,78,00,5f,00,6d,00,6f,00,64,00,65,00,2e,00,\
64,00,6c,00,6c,00,2c,00,20,00,56,00,4d,00,58,00,5f,00,4d,00,6f,00,64,00,65,\
00,43,00,68,00,61,00,6e,00,67,00,65,00,00,00,00,00
"InfPath"="oem2.inf"
"InfSection"="vmx_svga_vista"
"ProviderName"="test123, Inc."
"DriverDateData"=hex:00,80,de,95,e5,e0,ca,01
"DriverDate"="4-21-2010"
"DriverVersion"="11.6.0.35"
"MatchingDeviceId"="pci\\ven_15ad&dev_0405&subsys_040515ad&rev_00"
"DriverDesc"="test123 SVGA II"
"FeatureScore"=dword:000000fc
[HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class\{4D36E968-E325-11CE-BFC1-08002BE10318}\0000\Settings]
"InstalledDisplayDrivers"=hex(7):76,00,6d,00,78,00,5f,00,66,00,62,00,00,00,00,\
00
"VgaCompatible"=dword:00000000
"DefaultSettings.XResolution"=dword:00000280
"DefaultSettings.YResolution"=dword:000001e0
"DefaultSettings.BitsPerPel"=dword:00000020
"Device Description"="test123 SVGA II"
[HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SystemInformation]
"BIOSVersion"="6.00"
"BIOSReleaseDate"="07/02/2012"
"SystemManufacturer"="test123, Inc."
"SystemProductName"="test123 test123 Platform"
"InformationSource"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Video\{AB246128-79BD-44A8-95C3-DC6CB912ED85}\0000]
"InstalledDisplayDrivers"=hex(7):76,00,6d,00,78,00,5f,00,66,00,62,00,00,00,00,\
00
"VgaCompatible"=dword:00000000
"DefaultSettings.XResolution"=dword:00000280
"DefaultSettings.YResolution"=dword:000001e0
"DefaultSettings.BitsPerPel"=dword:00000020
"Device Description"="test123 SVGA II"
"Resolution.0"=hex:33,32,30,78,32,34,30,00
"Resolution.1"=hex:34,30,30,78,33,30,30,00
"Resolution.2"=hex:35,31,32,78,33,38,34,00
"Resolution.3"=hex:36,34,30,78,34,38,30,00
"Resolution.4"=hex:38,30,30,78,36,30,30,00
"Resolution.5"=hex:31,30,32,34,78,37,36,38,00
"Resolution.6"=hex:31,31,35,32,78,38,36,34,00
"Resolution.7"=hex:31,32,38,30,78,39,36,30,00
"Resolution.8"=hex:31,34,30,30,78,31,30,35,30,00
"Resolution.9"=hex:31,36,30,30,78,31,32,30,30,00
"Resolution.10"=hex:31,39,32,30,78,31,34,34,30,00
"Resolution.11"=hex:32,30,34,38,78,31,35,33,36,00
"Resolution.12"=hex:32,35,36,30,78,31,39,32,30,00
"Resolution.13"=hex:38,35,34,78,34,38,30,00
"Resolution.14"=hex:31,32,38,30,78,37,32,30,00
"Resolution.15"=hex:31,33,36,36,78,37,36,38,00
"Resolution.16"=hex:31,39,32,30,78,31,30,38,30,00
"Resolution.17"=hex:31,32,38,30,78,38,30,30,00
"Resolution.18"=hex:31,34,34,30,78,39,30,30,00
"Resolution.19"=hex:31,36,38,30,78,31,30,35,30,00
"Resolution.20"=hex:31,39,32,30,78,31,32,30,30,00
"Resolution.21"=hex:32,35,36,30,78,31,36,30,30,00
"Resolution.22"=hex:37,32,30,78,34,38,30,00
"Resolution.23"=hex:37,32,30,78,35,37,36,00
"Resolution.24"=hex:33,32,30,78,32,30,30,00
"Resolution.25"=hex:36,34,30,78,34,30,30,00
"Resolution.26"=hex:38,30,30,78,34,38,30,00
"Resolution.27"=hex:31,32,38,30,78,37,36,38,00
"Resolution.28"=hex:31,32,38,30,78,31,30,32,34,00
"HardwareInformation.ChipType"=hex:56,00,4d,00,77,00,61,00,72,00,65,00,20,00,\
53,00,56,00,47,00,41,00,20,00,49,00,49,00,00,00
"HardwareInformation.DacType"=hex:56,00,4d,00,77,00,61,00,72,00,65,00,20,00,53,\
00,56,00,47,00,41,00,20,00,49,00,49,00,00,00
"HardwareInformation.MemorySize"=hex:00,00,00,08
"HardwareInformation.AdapterString"=hex:56,00,4d,00,77,00,61,00,72,00,65,00,20,\
00,53,00,56,00,47,00,41,00,20,00,49,00,49,00,00,00
"HardwareInformation.BiosString"=hex:56,00,4d,00,77,00,61,00,72,00,65,00,20,00,\
53,00,56,00,47,00,41,00,20,00,49,00,49,00,00,00
[HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Video\{AB246128-79BD-44A8-95C3-DC6CB912ED85}\0000\VolatileSettings]
"{5b45201d-f2f2-4f3b-85bb-30ff1f953599}"=hex:5c,00,3f,00,3f,00,5c,00,50,00,43,\
00,49,00,23,00,56,00,45,00,4e,00,5f,00,31,00,35,00,41,00,44,00,26,00,44,00,\
45,00,56,00,5f,00,30,00,34,00,30,00,35,00,26,00,53,00,55,00,42,00,53,00,59,\
00,53,00,5f,00,30,00,34,00,30,00,35,00,31,00,35,00,41,00,44,00,26,00,52,00,\
45,00,56,00,5f,00,30,00,30,00,23,00,33,00,26,00,32,00,61,00,63,00,66,00,31,\
00,65,00,39,00,26,00,30,00,26,00,37,00,38,00,23,00,7b,00,35,00,62,00,34,00,\
35,00,32,00,30,00,31,00,64,00,2d,00,66,00,32,00,66,00,32,00,2d,00,34,00,66,\
00,33,00,62,00,2d,00,38,00,35,00,62,00,62,00,2d,00,33,00,30,00,66,00,66,00,\
31,00,66,00,39,00,35,00,33,00,35,00,39,00,39,00,7d,00
[HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Video\{AB246128-79BD-44A8-95C3-DC6CB912ED85}\0001]
"InstalledDisplayDrivers"=hex(7):76,00,6d,00,78,00,5f,00,66,00,62,00,00,00,00,\
00
"VgaCompatible"=dword:00000000
"DefaultSettings.XResolution"=dword:00000280
"DefaultSettings.YResolution"=dword:000001e0
"DefaultSettings.BitsPerPel"=dword:00000020
"Device Description"="test123 SVGA II"
[HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Video\{AB246128-79BD-44A8-95C3-DC6CB912ED85}\0001\VolatileSettings]
"{5b45201d-f2f2-4f3b-85bb-30ff1f953599}"=hex:5c,00,3f,00,3f,00,5c,00,50,00,43,\
00,49,00,23,00,56,00,45,00,4e,00,5f,00,31,00,35,00,41,00,44,00,26,00,44,00,\
45,00,56,00,5f,00,30,00,34,00,30,00,35,00,26,00,53,00,55,00,42,00,53,00,59,\
00,53,00,5f,00,30,00,34,00,30,00,35,00,31,00,35,00,41,00,44,00,26,00,52,00,\
45,00,56,00,5f,00,30,00,30,00,23,00,33,00,26,00,32,00,61,00,63,00,66,00,31,\
00,65,00,39,00,26,00,30,00,26,00,37,00,38,00,23,00,7b,00,35,00,62,00,34,00,\
35,00,32,00,30,00,31,00,64,00,2d,00,66,00,32,00,66,00,32,00,2d,00,34,00,66,\
00,33,00,62,00,2d,00,38,00,35,00,62,00,62,00,2d,00,33,00,30,00,66,00,66,00,\
31,00,66,00,39,00,35,00,33,00,35,00,39,00,39,00,7d,00
[HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\vmx_svga\Device0]
"InstalledDisplayDrivers"=hex(7):76,00,6d,00,78,00,5f,00,66,00,62,00,00,00,00,\
00
"VgaCompatible"=dword:00000000
"DefaultSettings.XResolution"=dword:00000280
"DefaultSettings.YResolution"=dword:000001e0
"DefaultSettings.BitsPerPel"=dword:00000020
"Device Description"="test123 SVGA II"
[HKEY_LOCAL_MACHINE\SYSTEM\ControlSet002\Control\Class\{4D36E968-E325-11CE-BFC1-08002BE10318}\0000]
"CoInstallers32"=hex(7):76,00,6d,00,78,00,5f,00,6d,00,6f,00,64,00,65,00,2e,00,\
64,00,6c,00,6c,00,2c,00,20,00,56,00,4d,00,58,00,5f,00,4d,00,6f,00,64,00,65,\
00,43,00,68,00,61,00,6e,00,67,00,65,00,00,00,00,00
"InfPath"="oem2.inf"
"InfSection"="vmx_svga_vista"
"ProviderName"="test123, Inc."
"DriverDateData"=hex:00,80,de,95,e5,e0,ca,01
"DriverDate"="4-21-2010"
"DriverVersion"="11.6.0.35"
"MatchingDeviceId"="pci\\ven_15ad&dev_0405&subsys_040515ad&rev_00"
"DriverDesc"="test123 SVGA II"
"FeatureScore"=dword:000000fc
[HKEY_LOCAL_MACHINE\SYSTEM\ControlSet002\Control\Class\{4D36E968-E325-11CE-BFC1-08002BE10318}\0000\Settings]
"InstalledDisplayDrivers"=hex(7):76,00,6d,00,78,00,5f,00,66,00,62,00,00,00,00,\
00
"VgaCompatible"=dword:00000000
"DefaultSettings.XResolution"=dword:00000280
"DefaultSettings.YResolution"=dword:000001e0
"DefaultSettings.BitsPerPel"=dword:00000020
"Device Description"="test123 SVGA II"
[HKEY_LOCAL_MACHINE\SYSTEM\ControlSet002\Control\Video\{AB246128-79BD-44A8-95C3-DC6CB912ED85}\0000]
"InstalledDisplayDrivers"=hex(7):76,00,6d,00,78,00,5f,00,66,00,62,00,00,00,00,\
00
"VgaCompatible"=dword:00000000
"DefaultSettings.XResolution"=dword:00000280
"DefaultSettings.YResolution"=dword:000001e0
"DefaultSettings.BitsPerPel"=dword:00000020
"Device Description"="test123 SVGA II"
"Resolution.0"=hex:33,32,30,78,32,34,30,00
"Resolution.1"=hex:34,30,30,78,33,30,30,00
"Resolution.2"=hex:35,31,32,78,33,38,34,00
"Resolution.3"=hex:36,34,30,78,34,38,30,00
"Resolution.4"=hex:38,30,30,78,36,30,30,00
"Resolution.5"=hex:31,30,32,34,78,37,36,38,00
"Resolution.6"=hex:31,31,35,32,78,38,36,34,00
"Resolution.7"=hex:31,32,38,30,78,39,36,30,00
"Resolution.8"=hex:31,34,30,30,78,31,30,35,30,00
"Resolution.9"=hex:31,36,30,30,78,31,32,30,30,00
"Resolution.10"=hex:31,39,32,30,78,31,34,34,30,00
"Resolution.11"=hex:32,30,34,38,78,31,35,33,36,00
"Resolution.12"=hex:32,35,36,30,78,31,39,32,30,00
"Resolution.13"=hex:38,35,34,78,34,38,30,00
"Resolution.14"=hex:31,32,38,30,78,37,32,30,00
"Resolution.15"=hex:31,33,36,36,78,37,36,38,00
"Resolution.16"=hex:31,39,32,30,78,31,30,38,30,00
"Resolution.17"=hex:31,32,38,30,78,38,30,30,00
"Resolution.18"=hex:31,34,34,30,78,39,30,30,00
"Resolution.19"=hex:31,36,38,30,78,31,30,35,30,00
"Resolution.20"=hex:31,39,32,30,78,31,32,30,30,00
"Resolution.21"=hex:32,35,36,30,78,31,36,30,30,00
"Resolution.22"=hex:37,32,30,78,34,38,30,00
"Resolution.23"=hex:37,32,30,78,35,37,36,00
"Resolution.24"=hex:33,32,30,78,32,30,30,00
"Resolution.25"=hex:36,34,30,78,34,30,30,00
"Resolution.26"=hex:38,30,30,78,34,38,30,00
"Resolution.27"=hex:31,32,38,30,78,37,36,38,00
"Resolution.28"=hex:31,32,38,30,78,31,30,32,34,00
"HardwareInformation.ChipType"=hex:56,00,4d,00,77,00,61,00,72,00,65,00,20,00,\
53,00,56,00,47,00,41,00,20,00,49,00,49,00,00,00
"HardwareInformation.DacType"=hex:56,00,4d,00,77,00,61,00,72,00,65,00,20,00,53,\
00,56,00,47,00,41,00,20,00,49,00,49,00,00,00
"HardwareInformation.MemorySize"=hex:00,00,00,08
"HardwareInformation.AdapterString"=hex:56,00,4d,00,77,00,61,00,72,00,65,00,20,\
00,53,00,56,00,47,00,41,00,20,00,49,00,49,00,00,00
"HardwareInformation.BiosString"=hex:56,00,4d,00,77,00,61,00,72,00,65,00,20,00,\
53,00,56,00,47,00,41,00,20,00,49,00,49,00,00,00
[HKEY_LOCAL_MACHINE\SYSTEM\ControlSet002\Control\Video\{AB246128-79BD-44A8-95C3-DC6CB912ED85}\0001]
"InstalledDisplayDrivers"=hex(7):76,00,6d,00,78,00,5f,00,66,00,62,00,00,00,00,\
00
"VgaCompatible"=dword:00000000
"DefaultSettings.XResolution"=dword:00000280
"DefaultSettings.YResolution"=dword:000001e0
"DefaultSettings.BitsPerPel"=dword:00000020
"Device Description"="test123 SVGA II"
[HKEY_LOCAL_MACHINE\SYSTEM\ControlSet002\services\vmx_svga\Device0]
"InstalledDisplayDrivers"=hex(7):76,00,6d,00,78,00,5f,00,66,00,62,00,00,00,00,\
00
"VgaCompatible"=dword:00000000
"DefaultSettings.XResolution"=dword:00000280
"DefaultSettings.YResolution"=dword:000001e0
"DefaultSettings.BitsPerPel"=dword:00000020
"Device Description"="test123 SVGA II"
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Class\{4D36E968-E325-11CE-BFC1-08002BE10318}\0000]
"CoInstallers32"=hex(7):76,00,6d,00,78,00,5f,00,6d,00,6f,00,64,00,65,00,2e,00,\
64,00,6c,00,6c,00,2c,00,20,00,56,00,4d,00,58,00,5f,00,4d,00,6f,00,64,00,65,\
00,43,00,68,00,61,00,6e,00,67,00,65,00,00,00,00,00
"InfPath"="oem2.inf"
"InfSection"="vmx_svga_vista"
"ProviderName"="test123, Inc."
"DriverDateData"=hex:00,80,de,95,e5,e0,ca,01
"DriverDate"="4-21-2010"
"DriverVersion"="11.6.0.35"
"MatchingDeviceId"="pci\\ven_15ad&dev_0405&subsys_040515ad&rev_00"
"DriverDesc"="test123 SVGA II"
"FeatureScore"=dword:000000fc
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Class\{4D36E968-E325-11CE-BFC1-08002BE10318}\0000\Settings]
"InstalledDisplayDrivers"=hex(7):76,00,6d,00,78,00,5f,00,66,00,62,00,00,00,00,\
00
"VgaCompatible"=dword:00000000
"DefaultSettings.XResolution"=dword:00000280
"DefaultSettings.YResolution"=dword:000001e0
"DefaultSettings.BitsPerPel"=dword:00000020
"Device Description"="test123 SVGA II"
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SystemInformation]
"BIOSVersion"="6.00"
"BIOSReleaseDate"="07/02/2012"
"SystemManufacturer"="test123, Inc."
"SystemProductName"="test123 test123 Platform"
"InformationSource"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Video\{AB246128-79BD-44A8-95C3-DC6CB912ED85}\0000]
"InstalledDisplayDrivers"=hex(7):76,00,6d,00,78,00,5f,00,66,00,62,00,00,00,00,\
00
"VgaCompatible"=dword:00000000
"DefaultSettings.XResolution"=dword:00000280
"DefaultSettings.YResolution"=dword:000001e0
"DefaultSettings.BitsPerPel"=dword:00000020
"Device Description"="test123 SVGA II"
"Resolution.0"=hex:33,32,30,78,32,34,30,00
"Resolution.1"=hex:34,30,30,78,33,30,30,00
"Resolution.2"=hex:35,31,32,78,33,38,34,00
"Resolution.3"=hex:36,34,30,78,34,38,30,00
"Resolution.4"=hex:38,30,30,78,36,30,30,00
"Resolution.5"=hex:31,30,32,34,78,37,36,38,00
"Resolution.6"=hex:31,31,35,32,78,38,36,34,00
"Resolution.7"=hex:31,32,38,30,78,39,36,30,00
"Resolution.8"=hex:31,34,30,30,78,31,30,35,30,00
"Resolution.9"=hex:31,36,30,30,78,31,32,30,30,00
"Resolution.10"=hex:31,39,32,30,78,31,34,34,30,00
"Resolution.11"=hex:32,30,34,38,78,31,35,33,36,00
"Resolution.12"=hex:32,35,36,30,78,31,39,32,30,00
"Resolution.13"=hex:38,35,34,78,34,38,30,00
"Resolution.14"=hex:31,32,38,30,78,37,32,30,00
"Resolution.15"=hex:31,33,36,36,78,37,36,38,00
"Resolution.16"=hex:31,39,32,30,78,31,30,38,30,00
"Resolution.17"=hex:31,32,38,30,78,38,30,30,00
"Resolution.18"=hex:31,34,34,30,78,39,30,30,00
"Resolution.19"=hex:31,36,38,30,78,31,30,35,30,00
"Resolution.20"=hex:31,39,32,30,78,31,32,30,30,00
"Resolution.21"=hex:32,35,36,30,78,31,36,30,30,00
"Resolution.22"=hex:37,32,30,78,34,38,30,00
"Resolution.23"=hex:37,32,30,78,35,37,36,00
"Resolution.24"=hex:33,32,30,78,32,30,30,00
"Resolution.25"=hex:36,34,30,78,34,30,30,00
"Resolution.26"=hex:38,30,30,78,34,38,30,00
"Resolution.27"=hex:31,32,38,30,78,37,36,38,00
"Resolution.28"=hex:31,32,38,30,78,31,30,32,34,00
"HardwareInformation.ChipType"=hex:56,00,4d,00,77,00,61,00,72,00,65,00,20,00,\
53,00,56,00,47,00,41,00,20,00,49,00,49,00,00,00
"HardwareInformation.DacType"=hex:56,00,4d,00,77,00,61,00,72,00,65,00,20,00,53,\
00,56,00,47,00,41,00,20,00,49,00,49,00,00,00
"HardwareInformation.MemorySize"=hex:00,00,00,08
"HardwareInformation.AdapterString"=hex:56,00,4d,00,77,00,61,00,72,00,65,00,20,\
00,53,00,56,00,47,00,41,00,20,00,49,00,49,00,00,00
"HardwareInformation.BiosString"=hex:56,00,4d,00,77,00,61,00,72,00,65,00,20,00,\
53,00,56,00,47,00,41,00,20,00,49,00,49,00,00,00
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Video\{AB246128-79BD-44A8-95C3-DC6CB912ED85}\0000\VolatileSettings]
"{5b45201d-f2f2-4f3b-85bb-30ff1f953599}"=hex:5c,00,3f,00,3f,00,5c,00,50,00,43,\
00,49,00,23,00,56,00,45,00,4e,00,5f,00,31,00,35,00,41,00,44,00,26,00,44,00,\
45,00,56,00,5f,00,30,00,34,00,30,00,35,00,26,00,53,00,55,00,42,00,53,00,59,\
00,53,00,5f,00,30,00,34,00,30,00,35,00,31,00,35,00,41,00,44,00,26,00,52,00,\
45,00,56,00,5f,00,30,00,30,00,23,00,33,00,26,00,32,00,61,00,63,00,66,00,31,\
00,65,00,39,00,26,00,30,00,26,00,37,00,38,00,23,00,7b,00,35,00,62,00,34,00,\
35,00,32,00,30,00,31,00,64,00,2d,00,66,00,32,00,66,00,32,00,2d,00,34,00,66,\
00,33,00,62,00,2d,00,38,00,35,00,62,00,62,00,2d,00,33,00,30,00,66,00,66,00,\
31,00,66,00,39,00,35,00,33,00,35,00,39,00,39,00,7d,00
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Video\{AB246128-79BD-44A8-95C3-DC6CB912ED85}\0001]
"InstalledDisplayDrivers"=hex(7):76,00,6d,00,78,00,5f,00,66,00,62,00,00,00,00,\
00
"VgaCompatible"=dword:00000000
"DefaultSettings.XResolution"=dword:00000280
"DefaultSettings.YResolution"=dword:000001e0
"DefaultSettings.BitsPerPel"=dword:00000020
"Device Description"="test123 SVGA II"
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Video\{AB246128-79BD-44A8-95C3-DC6CB912ED85}\0001\VolatileSettings]
"{5b45201d-f2f2-4f3b-85bb-30ff1f953599}"=hex:5c,00,3f,00,3f,00,5c,00,50,00,43,\
00,49,00,23,00,56,00,45,00,4e,00,5f,00,31,00,35,00,41,00,44,00,26,00,44,00,\
45,00,56,00,5f,00,30,00,34,00,30,00,35,00,26,00,53,00,55,00,42,00,53,00,59,\
00,53,00,5f,00,30,00,34,00,30,00,35,00,31,00,35,00,41,00,44,00,26,00,52,00,\
45,00,56,00,5f,00,30,00,30,00,23,00,33,00,26,00,32,00,61,00,63,00,66,00,31,\
00,65,00,39,00,26,00,30,00,26,00,37,00,38,00,23,00,7b,00,35,00,62,00,34,00,\
35,00,32,00,30,00,31,00,64,00,2d,00,66,00,32,00,66,00,32,00,2d,00,34,00,66,\
00,33,00,62,00,2d,00,38,00,35,00,62,00,62,00,2d,00,33,00,30,00,66,00,66,00,\
31,00,66,00,39,00,35,00,33,00,35,00,39,00,39,00,7d,00
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\vmx_svga\Device0]
"InstalledDisplayDrivers"=hex(7):76,00,6d,00,78,00,5f,00,66,00,62,00,00,00,00,\
00
"VgaCompatible"=dword:00000000
"DefaultSettings.XResolution"=dword:00000280
"DefaultSettings.YResolution"=dword:000001e0
"DefaultSettings.BitsPerPel"=dword:00000020
"Device Description"="test123 SVGA II"







 本文介绍在恶意软件分析中,如何利用虚拟机技术提高安全性及资源节约性。文章详细阐述了基于Intel CPU的虚拟环境中,针对Windows XP SP3系统的虚拟机检测方法,包括执行特权指令、利用IDT基址、LDT/GDT检测、STR检测、注册表检测、时间差检测以及硬件指纹检测等。
本文介绍在恶意软件分析中,如何利用虚拟机技术提高安全性及资源节约性。文章详细阐述了基于Intel CPU的虚拟环境中,针对Windows XP SP3系统的虚拟机检测方法,包括执行特权指令、利用IDT基址、LDT/GDT检测、STR检测、注册表检测、时间差检测以及硬件指纹检测等。
















 1万+
1万+

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








