Summary of the first chapter of《Computer Network — A Top Down Approach》
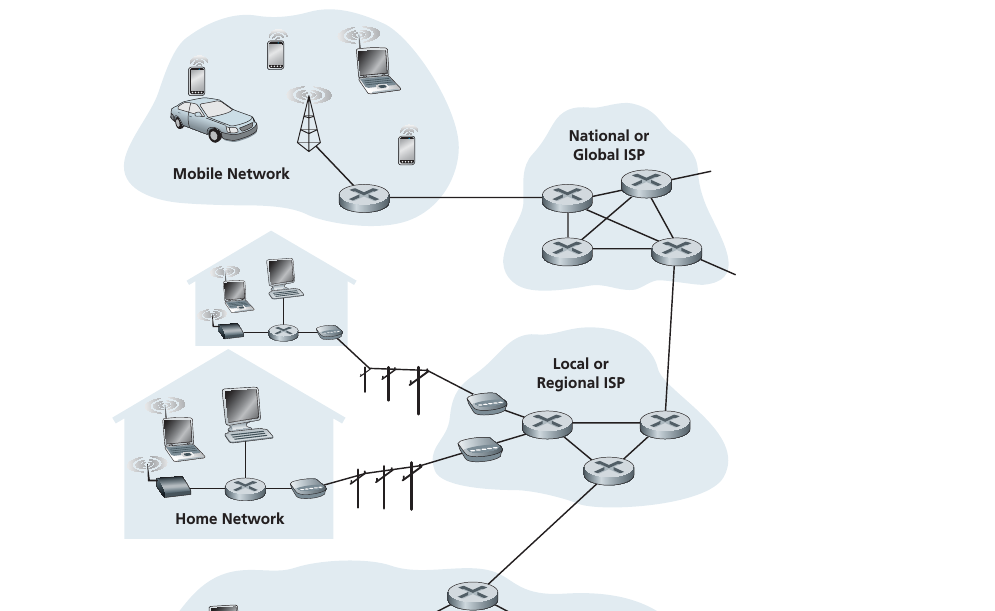
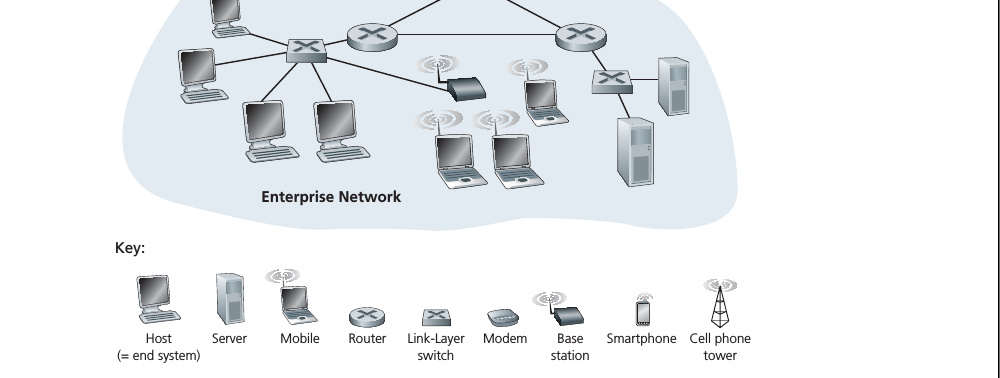
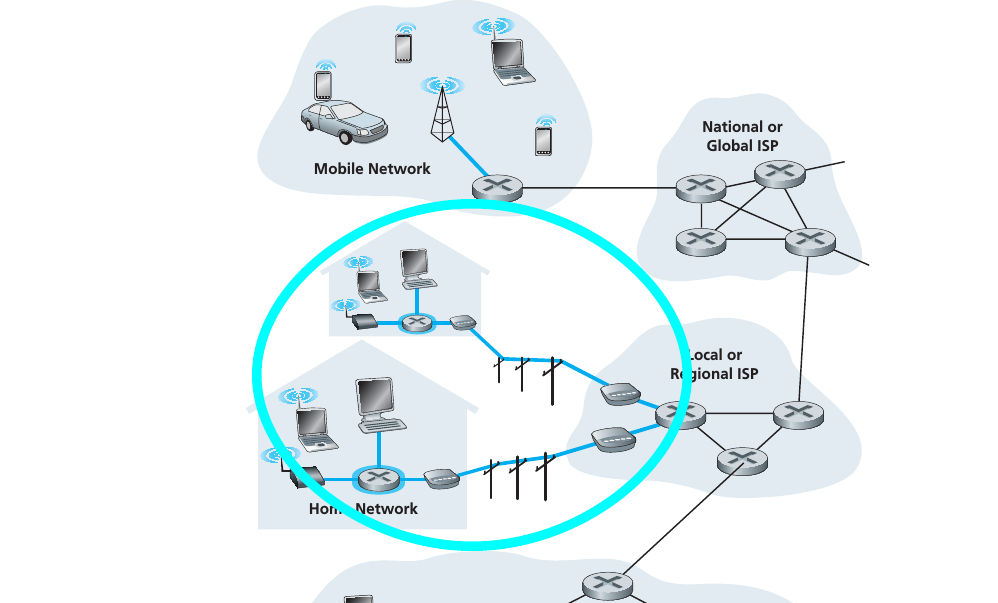
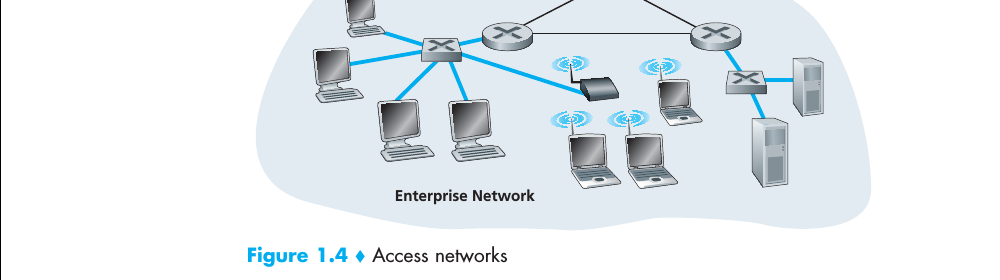
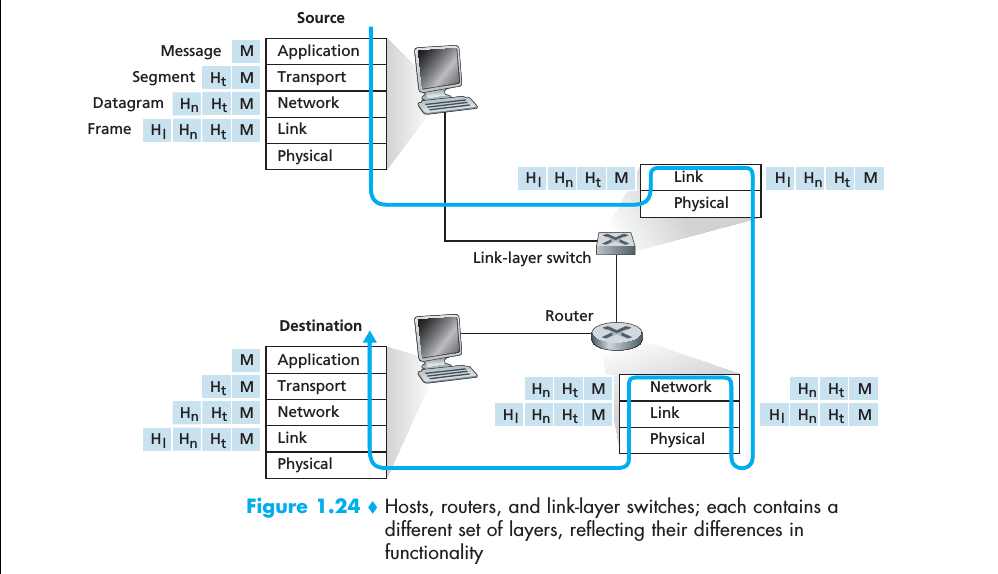
- Link layer switches are typically used in access networks, while routers are typically used in the network core.
- The IP protocol specifies the format of the packets that are sent and received among routers and end systems.
- Application layer: Message; Transport layer: Segment; Network layer: datagram; Link layer: frame.
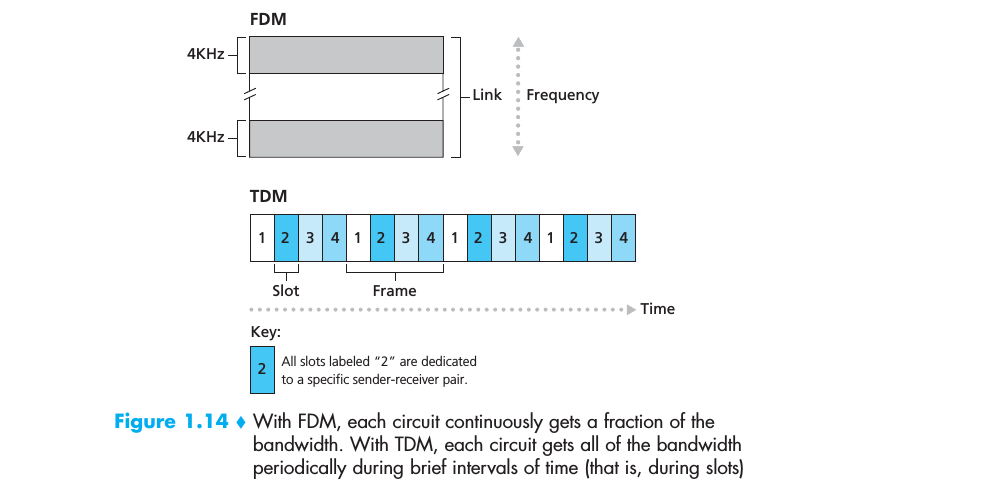
- packet exchange and circuit exchange
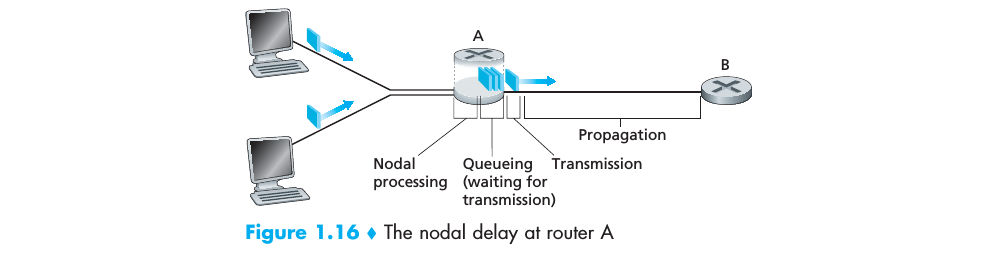
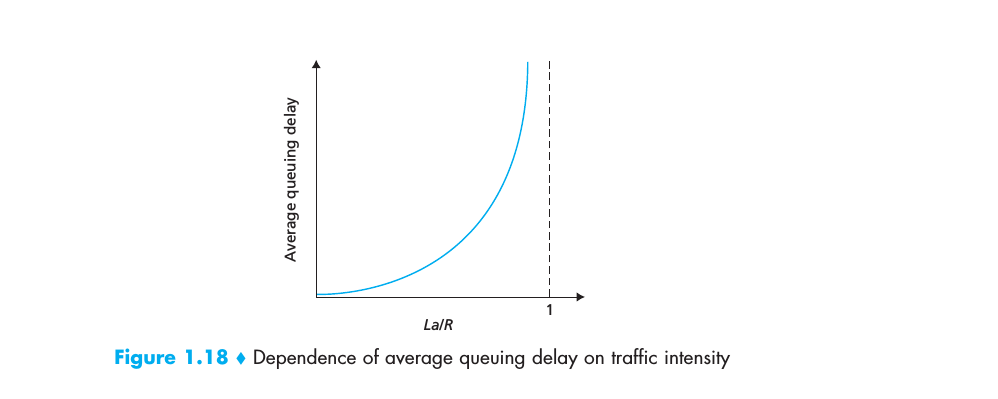
- traffic intensity; throughput
- Virus are malware that require some form of user interaction to infect the users device.
- Worms are malware that can enter a device without any explicit user interaction.
- Vulnerability attack; Bandwidth flooding; Connection flooding. DoS;DDoS. IP spoofing; packet sniffer.
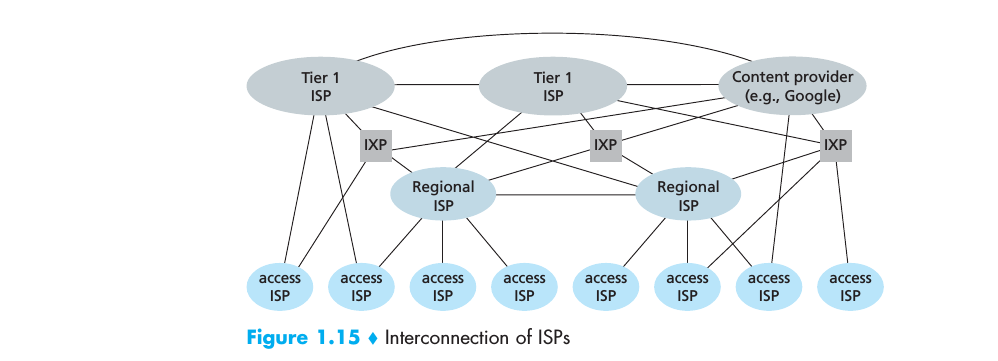
- Internet is a network of network.






















 310
310











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








