术语解释:
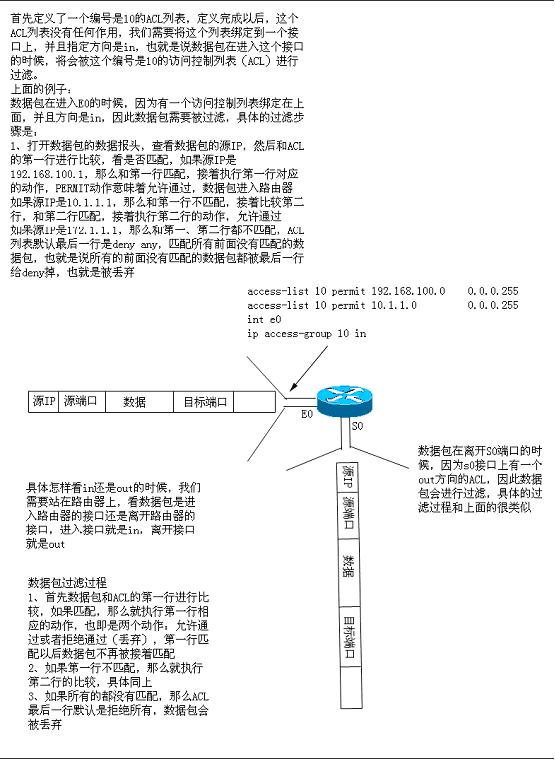
Advanced Encryption Standard (AES):高级加密标准,使用128,192,256位长的KEY来加密128,192,256位长的数据块,可以作出9种组合
Authentication Header (AH): 验证头部,一种安全协议,只是用来验证头部和防重发.不对实际用户数据部分加密.可配合ESP使用.
Authentication:IPsec框架种的一个功能,用来验证数据完整性,并确保数据在传输过程中没有被篡改,同时也可用来验证数据来源的合法性(验证数据来源).
Certification Authority (CA): 权威认证.第三方受信机构.提供CA证书或发布不信任认证.
Certificate:一个包含标志身份和公钥的加密签名对象
Certificate Revocation List (CRL): 不信任列表,由CA颁布的.
Crypto map: 加密映像,CISCO IOS的一个配置功能语句,提供3个主要功能:一,选择需要加密的数据流(通过调用ACL),二,定义策略(通过调用转换集),三,设置对等体
Data integrity数据完整性机制,通过密钥或公钥确保数据传输过程中没有被篡改.:
Data confidentiality: 数据机密性,通过加密或者只让伙伴知道KEY值的方法来保证数据不被其它人读取.
Data origin authentication: 数据源验证,一种安全服务,确保数据是来自正确的发送方,服务要求数据完整性+KEY分发机制(一个密钥只能是发送和接受方知道)
Data Encryption Standard (DES): 数据加密标注,使用密钥加密分组,CISCO-IPSEC使用56位长密钥加密分组
Diffie-Hellman:一种确保共享KEY安全穿越不安全网络的方法,它是OAKLEY的一个组成部分.
Encapsulating Security Payload (ESP): 封装安全有效负载,一种提供数据加密的协议,同时支持验证和防重发功能,它完整封装用户数据,可独自使用或与AH配合使用.
Hash: 哈西,散列算法,将变长分组转化成定长摘要.CISCO在IPSEC中使用SHA (Secure Hash Algorithm )和MD5(Message Digest 5)两种方法.
HMAC:使用SHA,MD5进行消息验证的一种机制.
Internet Key Exchange (IKE): internet key交换.,一种在Internet Security Association and Key Management Protocol (ISAKMP) 框架中使用Oakley和SKEME协议组的混合协议.IKE通常用来确定一个共享的安全策略和对需要KEY 的KEY服务的验证,在IPSEC流量能通过之前,先要对router/firewall/host 这些对等体进行身份验证.可以在双边手工输入预共享(pre-share)ke'y或者通过CA获得KEY,通过双边协商双边获得统一IKE的SA,建立 初步的安全通道,为接下来的IPSEC作准备.
Internet Security Association and Key Management Protocol (ISAKMP):一种协议框架,定义一种KEY交换和安全策略协商的
Message Digest 5 (MD5):MD5消息摘要,和SHA一样从MD4发展而来的,产生一个128位长的摘要,SHA比MD5更安全,但更耗资源.
Oakley: 一种KEY交换协议,它的一个基本机制就是Diffie-Hellman KEY交换算法
Perfect Forward Secrecy (PFS): PFS ensures that a given IPSec SA key was not derived from any other secret (like some other keys). In other words, if someone breaks a key, PFS ensures that the attacker is not able to derive any other key. If PFS is not enabled, someone can potentially break the IKE SA secret key, copy all the IPSec protected data, and then use knowledge of the IKE SA secret in order to compromise the IPSec SAs setup by this IKE SA. With PFS, breaking IKE does not give an attacker immediate access to IPSec. The attacker needs to break each IPSec SA individually. The Cisco IOS IPSec implementation uses PFS group 1 (D-H 768 bit) by default.
Replay-detection: A security service where the receiver can reject old or duplicate packets in order to defeat replay attacks (replay attacks rely on the attacker sending out older or duplicate packets to the receiver and the receiver thinking that the bogus traffic is legitimate). Replay-detection is done by using sequence numbers combined with authentication, and is a standard feature of IPSec.
RSA: A public key cryptographic algorithm (named after its inventors, Rivest, Shamir and Adleman) with a variable key length. RSA's main weakness is that it is significantly slow to compute compared to popular secret-key algorithms, such as DES. Cisco's IKE implementation uses a Diffie-Hellman exchange to get the secret keys. This exchange can be authenticated with RSA (or pre-shared keys). With the Diffie-Hellman exchange, the DES key never crosses the network (not even in encrypted form), which is not the case with the RSA encrypt and sign technique. RSA is not a public domain, and must be licensed from RSA Data Security.
Security Association (SA): An instance of security policy and keying material applied to a data flow. Both IKE and IPSec use SAs, although SAs are independent of one another. IPSec SAs are unidirectional and they are unique in each security protocol. A set of SAs are needed for a protected data pipe, one per direction per protocol. For example, if you have a pipe that supports ESP between peers, one ESP SA is required for each direction. SAs are uniquely identified by destination (IPSec endpoint) address, security protocol (AH or ESP), and security parameter index (SPI).
IKE negotiates and establishes SAs on behalf of IPSec. A user can also establish IPSec SAs manually.
An IKE SA is used by IKE only. Unlike the IPSec SA, it is bi-directional.
Secure Hash Algorithm (SHA): A one way hash put forth by NIST. SHA is closely modeled after MD4 and produces a 160-bit digest. Because SHA produces a 160-bit digest, it is more resistant to brute-force attacks than 128-bit hashes (such as MD5), but it is slower.
Transform: A transform describes a security protocol (AH or ESP) with its corresponding algorithms. For example, ESP with the DES cipher algorithm and HMAC-SHA for authentication.
Transport Mode: An encapsulation mode for AH/ESP. Transport Mode encapsulates the upper layer payload (such as Transmission Control Protocol (TCP) or User Datagram Protocol (UDP)) of the original IP datagram. This mode can only be used when the peers are the endpoints of the communication. The contrast of Transport Mode is Tunnel Mode.
Tunnel Mode: Encapsulation of the complete IP Datagram for IPSec. Tunnel Mode is used on order to protect datagrams sourced from or destined to non-IPSec systems (such as in a Virtual Private Network (VPN) scenario).
配置IPSec-VPN流程图:
IKE的存在主要是为了IPSEC协商SA,它为IPSEC进行了铺路.两边对等体要就IKE的安全策略进行协商,我们可以定义多个IKE策略在每 一边,最终对等体协商一个双方都相同的策略.IKE第一阶段协商成功IKE SA(主交换模式),然后进行IPSEC SA的协商(快速交换模式),2阶段协商成功后,可以进行正常的IPSEC数据通信了.
IKE的策略配置主要包含:
1.加密算法 encryption 默认:DES
2.散列算法 hash 默认:SHA 如果路由器不够强大,建议使用 MD5
3.密钥交换 group 默认 1
4.验证方法 authentication 默认 rsa-sig 如果使用RSA-SG则要用CA建立KEY,如果使用pre-share则在路由器中配置key
5.IKE SA生命周期 lefttime 默认 86400秒 一天.
CISCO(config)#
crypto isakmp policy 1进入IKE 策略编辑模式,后面的数字序号可以区别各个策略,且数字越小被能被优先使用
CISCO(config-isakmp)#
encryption des默认的加密方式
CISCO(config-isakmp)#group 2Diffie-Hellman 密钥交换方法,Group 1 is 768 bits long, and group 2 is 1024 bits long.路由器不够强大建议使用group 1,默认也是1
CISCO(config-isakmp)#hash md5散列算法,默认SHA,路由器不够强大就使用MD5
CISCO(config-isakmp)#lifetime 500IKE SA生命周期,默认86400秒,也就是一天,路由器不够强大则不建议太短.
CISCO(config-isakmp)#authentication pre-share验证方法,默认RSA-SG,使用RSA-SG需要配合CA.使用pre-share就需要使用crypto isakmp key **** address peer-address来指定key
CISCO(config-isakmp)#group 2Diffie-Hellman 密钥交换方法,Group 1 is 768 bits long, and group 2 is 1024 bits long.路由器不够强大建议使用group 1,默认也是1
CISCO(config-isakmp)#hash md5散列算法,默认SHA,路由器不够强大就使用MD5
CISCO(config-isakmp)#lifetime 500IKE SA生命周期,默认86400秒,也就是一天,路由器不够强大则不建议太短.
CISCO(config-isakmp)#authentication pre-share验证方法,默认RSA-SG,使用RSA-SG需要配合CA.使用pre-share就需要使用crypto isakmp key **** address peer-address来指定key
CISCO(config-isakmp)#exit
CISCO(config)#crypto isakmp key Slurpee-Machine address 192.168.0.8
这里的KEY要和对等体的配置一样.
You are now done with IKE configuration. These lines are the IKE configuration of the peer (the complete configurations for both routers are in the
Sample Configurations section of this document):
crypto isakmp policy 1
hash md5
group 2
authentication pre-share
crypto isakmp key Slurpee-Machine address 192.168.0.6
接下来
Configure IPSec
:
创建extended ACL:
CISCO(config)# access-list 101 permit ip 192.168.3.0 0.0.0.255 10.3.2.0 0.0.0.255
CISCO(config)# access-list 101 permit ip 192.168.3.0 0.0.0.255 10.3.2.0 0.0.0.255
创建IPSec transform(s):
CISCO(config)# crypto ipsec transform-set MamaBear ah-md5-hmac esp-des
CISCO(config)# crypto ipsec transform-set MamaBear ah-md5-hmac esp-des
创建crypto map:
CISCO(config)# crypto map armadillo 10 ipsec-isakmp
CISCO(config-crypto-map)# set peer 192.168.0.8
CISCO(config)# crypto map armadillo 10 ipsec-isakmp
CISCO(config-crypto-map)# set peer 192.168.0.8
CISCO(config-crypto-map)#set session-key lifetime seconds 4000
CISCO(config-crypto-map)#set transform-set MamaBear 这里还可以继续写多个转换集名
CISCO(config-crypto-map)#match address 101
CISCO(config-crypto-map)#set transform-set MamaBear 这里还可以继续写多个转换集名
CISCO(config-crypto-map)#match address 101
Apply crypto map tothe interface:
CISCO(config)# interface e0
CISCO(config-if)# crypto map armadillo
CISCO(config)# interface e0
CISCO(config-if)# crypto map armadillo





















 2932
2932











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








