图胜千言:


TCP/IP Protocol Stack With SSL :
| TCP/IP Layer | Protocol |
| Application Layer | HTTP, IMAP, NNTP, Telnet, FTP, etc. |
| Secure Sockets Layer | SSL |
| Transport Layer | TCP |
| Internet Layer | IP |
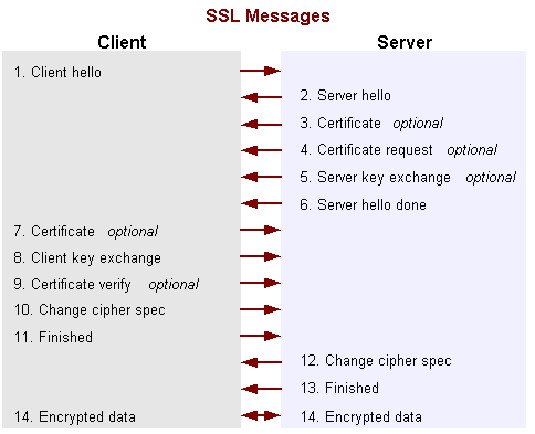
How SSL Works: the Handshake in Detail:
- Client hello - The client sends the server information including the highest version of SSL it supports and a list of the cipher suites it supports.
- Server hello - The server chooses the highest version of SSL and the best cipher suite that both the client and server support and sends this information to the client.
- Certificate - If server authentication is required then the server sends the client a certificate or a certificate chain.
- Certificate request - If the server needs to authenticate the client, it sends the client a certificate request.
- Server key exchange - The server sends the client a server key exchange message when the public key information sent in 3) above is not sufficient for key exchange.
- Server hello done - The server tells the client it is finished with its initial negotiation messages.
- Certificate - If the server requests a certificate from the client in Message 4, the client sends its certificate chain, like the server did in Message 3.
- Client key exchange - The client generates information used to create a key to use for symmetric encryption. For RSA, the client then encrypts this key information with the server's public key and sends it to the server.
- Certificate verify – If the server is authenticating the client, the client sends a random number that it digitally signs. When the server decrypts number with the client's public key, the server authenticates the client.
- Change cipher spec - The client tells the server to change to encrypted mode.
- Finished - The client sends the server a hash of the handshake messages.
- Change cipher spec - The server tells the client to change to encrypted mode.
- Finished - The server sends the client a hash of the handshake messages.
Encrypted data - The client and the server communicate using the symmetric encryption algorithm and the cryptographic hash function negotiated in Messages 1 and 2, using the secret key that the client sent to the server in Message 8.






















 3383
3383

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








