Nginx is a robust, fast, reliable and dynamic open-source web server popular for serving high traffic sites. In addition, it is well renowned for its ease of configuration, high scalability, and support for a myriad of protocols.
Among the protocols supported by Nginx is the new HTTP/2 protocol whose main advantage over its predecessor HTTP 1.1 is the high transfer speed required for content-rich websites.
Nginx是一种健壮,快速,可靠和动态的开源Web服务器,常用于为高流量站点提供服务。 此外,它以易于配置,高度可扩展性以及对多种协议的支持而闻名。
Nginx支持的协议中包括新的HTTP / 2协议,它比其前身的HTTP 1.1的主要优势是内容丰富的网站所需的高传输速度。
In this guide, we will delve in the installation and setup of a secure Nginx server with HTTP/2 Support:
在本指南中,我们将深入研究具有HTTP / 2支持的安全Nginx服务器的安装和设置:
先决条件 (Prerequisites)
To start let’s go through the flight check and see whether we have the following
首先,让我们通过飞行检查,看看是否有以下内容
- A server instance of Ubuntu 18.04 LTS Ubuntu 18.04 LTS的服务器实例
- Nginx version 1.9.5 or higher (To verify the version of Nginx, run
nginx -v), read Install Nginx on Ubuntu 18.04. Nginx版本1.9.5或更高版本(要验证Nginx的版本,请运行nginx -v),请阅读在Ubuntu 18.04上安装Nginx 。 - OpenSSL version 1.0.2 or higher (Check the version using openssl version) OpenSSL版本1.0.2或更高版本(使用openssl版本检查版本)
- A regular, non-root user with sudo privileges 具有sudo特权的普通非root用户
- A Fully Qualified Domain Name (FQDN) In this case, we are going to use
crazytechgeek.infopurchased from GoDaddy.The domain name’s A record should point to the IP address of the server. crazytechgeek.info has been pointed to 216.200.116.207.
crazytechgeek.info。域名的A记录应指向服务器的IP地址。 crazytechgeek.info已指向216.200.116.207。
- An SSL certificate (Either a self-signed certificate or a one from Let’s encrypt SSL. Similarly, you can purchase one form a different provider. SSL证书(自签名证书或“让我们加密SSL”的证书。类似地,您可以从其他提供商处购买一个证书。
步骤1 –启用HTTP /2.0支持 (Step 1 – Enabling HTTP /2.0 Support)
To start off, it is assumed that you have configured Nginx server block at
首先,假设您已经在以下位置配置了Nginx服务器块:
/etc/nginx/sites-available/your_domainIn our case, the server block is /etc/nginx/sites-available/crazytechgeek.info.
在我们的例子中,服务器块是/etc/nginx/sites-available/crazytechgeek.info 。
Using your favorite text editor, open the server block file and locate the listen directive as shown
使用您喜欢的文本编辑器,打开服务器阻止文件并找到listen指令,如图所示
The first directive indicates IPv6 connections while the second one is for IPv4 connections
第一个指令指示IPv6连接,而第二个指令则用于IPv4连接
Now, we are going to modify each directive to include a http2 flag as shown
现在,我们将修改每个指令以包括一个http2标志,如下所示
This is going to instruct Nginx to use HTTP/2 on supported browsers
这将指示Nginx在支持的浏览器上使用HTTP / 2
Save the configuration file and exit your editor.
保存配置文件并退出编辑器。
Next, open /etc/nginx/sites-available/default file and make the same changes
接下来,打开/etc/nginx/sites-available/default文件并进行相同的更改
Save and exit the text editor.
保存并退出文本编辑器。
Just to make sure that there are no syntax errors in any of the Nginx files, run the command below
为了确保所有Nginx文件中没有语法错误,请运行以下命令
$ sudo nginx -tOutput
输出量
步骤2 –清除旧的和不安全的密码 (Step 2 – Purging Old and insecure Ciphers)
For HTTP/2 to work as expected, we must avoid using old and insecure ciphers which have been on the HTTP/2 blacklist. Cipher suites are cryptographic algorithms which dictate how traffic is to be encrypted.
为了使HTTP / 2正常工作,我们必须避免使用HTTP / 2黑名单中的旧密码和不安全密码。 密码套件是规定如何加密流量的加密算法。
If certbot was used to obtain the certificates, then the ciphers in the path /etc/letsencrypt/options-ssl-nginx.conf are not secure enough for HTTP/2. However, modification of this file will only cause errors and prevent certbot from applying updates. This means we must specify our list of ciphers and instruct Nginx to ignore the file
如果使用certbot获得证书,则/etc/letsencrypt/options-ssl-nginx.conf路径中的密码对于HTTP / 2而言不够安全。 但是,对该文件的修改只会导致错误并阻止certbot应用更新。 这意味着我们必须指定密码列表并指示Nginx忽略该文件
Open the configuration file for your Nginx’s domain server block
打开您的Nginx的域服务器块的配置文件
$ vim /etc/nginx/sites-available/crazytechgeek.infoComment this line
评论这行
# include /etc/letsencrypt/options-ssl-nginx.conf;Below that line, append the line below to define the allowed ciphers
在该行下方,追加以下行以定义允许的密码
ssl_ciphers EECDH+CHACHA20:EECDH+AES128:RSA+AES128:EECDH+AES256:RSA+AES256:EECDH+3DES:RSA+3DES:!MD5;Save the file and exit the text editor
保存文件并退出文本编辑器
If a self-assigned certificate was used, or a third party certificate, then open the file
如果使用了自定义证书或第三方证书,请打开文件
/etc/nginx/snippets/ssl-params.conf$ sudo vim /etc/nginx/snippets/ssl-params.confLocate the line as shown below
找到如下所示的行
...
ssl_ciphers ECDHE-RSA-AES256-GCM-SHA512:DHE-RSA-AES256-GCM-SHA512:ECDHE-RSA-AES256-GCM-SHA384:DHE-RSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-SHA384;
...Modify the file accordingly as shown below
相应地修改文件,如下所示
...
ssl_ciphers EECDH+CHACHA20:EECDH+AES128:RSA+AES128:EECDH+AES256:RSA+AES256:EECDH+3DES:RSA+3DES:!MD5;The finally save and exit the configuration file
最后保存并退出配置文件
Once again check for any Nginx configuration errors
再次检查是否有任何Nginx配置错误
$ sudo nginx -tIf all went well, you should see the output below as shown earlier
如果一切顺利,您应该看到下面的输出,如之前所示
Restart Nginx
重新启动Nginx
$ sudo systemctl reload nginxIn the next step, we are going to test whether our server can server HTTP/2 pages
下一步,我们将测试服务器是否可以处理HTTP / 2页
步骤3 –测试是否启用了HTTP / 2 (Step 3 – Testing If HTTP/2 is enabled)
Now let’s test whether HTTP is running and enabled on our Nginx web server
In your terminal, execute the command below
现在让我们测试Nginx Web服务器上是否正在运行并启用HTTP
在您的终端中,执行以下命令
curl -I -L https://your_domainIn our case, it shall be
在我们的情况下,
curl -I -L https://crazytechgeek.infoOutput
输出量
Alternatively, you can verify HTTP/2 by opening Google developer tools by hitting
或者,您可以通过点击来打开Google开发人员工具来验证HTTP / 2
Ctrl + Shift + INext, click on Network Tab.
接下来,单击“ Network选项卡。
In the Protocol column, be sure to find the label h2
在“ Protocol列中,确保找到标签h2
步骤4 –部署HTTP严格传输安全性 (Step 4 – Deploying HTTP Strict Transport Security)
Lastly, even though we know very clearly that our server can redirect HTTP requests to HTTPS, we want to enable HSTS HTTP Strict Transport Security to eliminate such redirects. Should a browser chance upon an HSTS header, it will not try connecting to the server again for a certain duration of time. IT will only exchange data via secure and encrypted HTTPS protocol.
最后,即使我们非常清楚地知道我们的服务器可以将HTTP请求重定向到HTTPS,我们仍希望启用HSTS HTTP Strict Transport Security来消除此类重定向。 如果浏览器碰巧遇到了HSTS标头,它将在一段时间内不尝试再次连接到服务器。 IT仅通过安全和加密的HTTPS协议交换数据。
To achieve this, Open the Nginx config file
为此,请打开Nginx配置文件
$ vim /etc/nginx/nginx.confAppend the line below
追加以下行
add_header Strict-Transport-Security "max-age=15768000" always;max-age is set in seconds
max-age以秒为单位
If your site has subdomains, and you desire to apply HSTS to all of them, append the includeSubDomains flag at the end of the line
如果您的站点有子域,并且您希望对所有子域都应用HSTS,请在该行的末尾附加includeSubDomains标志
add_header Strict-Transport-Security "max-age=15768000; includeSubDomains" always;Save and exit from the config file.
保存并退出配置文件。
As always, check whether there are any errors
和往常一样,检查是否有任何错误
$ sudo nginx -t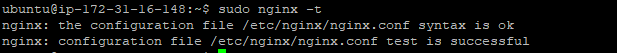
Finally, restart Nginx
最后,重启Nginx
$ sudo systemctl restart nginx结论 (Conclusion)
At this point, your Nginx server is now serving HTTP/2 pages.
You can also visit https://tools.keycdn.com/http2-test to test your site’s HTTP/2 status as shown
此时,您的Nginx服务器现在正在提供HTTP / 2页面。
您还可以访问https://tools.keycdn.com/http2-test来测试站点的HTTP / 2状态,如下所示
Alternatively, you can also visit this site
另外,您也可以访问此网站
https://http2.pro/For more detailed results use
有关更详细的结果,请使用
https://www.ssllabs.com/ssltest/翻译自: https://www.journaldev.com/27916/nginx-http-2-support-ubuntu





















 1783
1783

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








