转自:http://blog.rootcon.org/2012/03/introducing-35-pentesting-tools-used.html
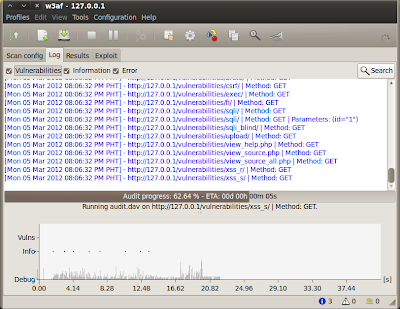
1. w3af
w3af or Web Application Attack and Audit Framework is an open source penetration testing tool for finding web vulnerabilities and an exploit tool that comes with cool plugins like sqlmap, xssBeef, and davShell. w3af automatically updates itself every time you launch the tool making it a very reliable tool for website hacking. For more information just check out their website hosted at
SourceForge.
2. Acunetix Web Vulnerability Scanner
Acunetix WVS or Web Vulnerability Scanner is a pentesting tool for Windows users so that they may be able to check for SQL Injection, Cross Site Scripting (XSS), CRLF injection, Code execution, Directory Traversal, File inclusion, checks for vulnerabilities in File Upload forms and other serious web vulnerabilities. You can download this tool here.
3. SQLninja
SQLninja is a an sql injection tool for web applications that use Microsoft SQL Server as its back-end though it runs only in Linux, Mac and BSD. It requires perl modules; NetPacket, Net-Pcap, Net-DNS, Net-RawIP, and IO-Socket-SSL. You can download this tool here.
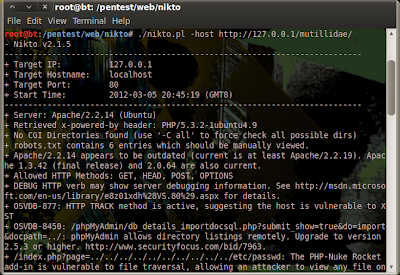
4. Nikto
Nikto is an open source web server scanner “ which performs comprehensive tests against web servers for multiple items, including over 6400 potentially dangerous files or CGIs, checks for outdated versions of over 1200 servers, and version specific problems on over 270 servers." The good thing about Nikto is that it easy to use and and performs scanning faster. Nikto is coded in Perl and written by Chris Sullo and David Lodge. Although not all checks are really a big security problem but most are like XSS (Cross Site Scripting) Vulnerabilities, phpmyadmin logins, etc. Nikto alerts and gives you security tips in order to prevent your website from various attacks.
5. SQLmap
SQLmap is an open source automatic SQL injection and database takeover tool that fully supports MySQL, Oracle, PostgreSQL and Microsoft SQL Server. It partially supports Microsoft Access, DB2, Informix, Sybase and Interbase. Download sqlmap here.
6. Pangolin 3.2.3
Pangolin is another sql injection scanner for web applications using Access,DB2,Informix,Microsoft SQL Server 2000,Microsoft SQL Server 2005,Microsoft SQL Server 2008, MySQL, Oracle, PostgreSQL, Sqlite3, and Sybase. Its features include keyword auto analysis, supports HTTPS, has bypass firewall setting, injection digger, data dumper, etc. You can download its zip file here.
7. Havij v1.15 Advanced SQL Injection
Havij is another famous automatic sql injection tool that has a free and premium version. The free version only supports a few injection methods like MsSQL 2000/2005 with error, MsSQL 2000/2005 no error union based, MySQL union based, MySQL Blind, MySQL error based, MySQL time based, Oracle union based, MsAccess union based, and Sybase (ASE). It also includes an admin finder and an md5 cracker.
8. SQL Power Injector
SQL Power Injector is a web pentesting application created in .Net 1.1 that helps the penetration tester and hackers find and exploit SQL injections on a web application that uses SQL Server, Oracle, MySQL, Sybase/Adaptive Server and DB2 compliant, but it is possible to use it with any existing Database Management System when using the inline injection or normal mode. You can download the latest version of this tool which includes a Firefox plugin here.
9. VulnDetector
VulnDetector is a project coded in python which scans a website and detects various web based security vulnerabilities in the website. It was developed by Brad Cable who is into coding open source tools. You can download the script here.
10. SQLIer 0.8.2b
SQLIer is another project of Brad Cable and is a shell script that determines all the necessary information to build and exploit an SQL Injection vulnerability to a URL by itself without user interaction unless it can't guess the table or field names for the database correctly. SQLIer can build a UNION SELECT query designed to brute force passwords out of the database. This script also does not use quotes in the exploit to operate, meaning it will work for a wider range of sites. Download the shell script here.
11. bsqlbf-v2
bsqlbf-v2 or Blind Sql Injection Brute Forcer version 2 is a perl script that allows extraction of data from Blind SQL Injections. It accepts custom SQL queries as a command line parameter and it works for both integer and string based injections. It supports MySQL, Oracle, PostgreSQL and Microsoft SQL Server databases. You can download the perl script on a Google hosted project.
12. Marathon Tool
Marathon Tool is an alpha release SQL Injection tool or project that extracts information from web applications using Microsoft SQL Server, Microsoft Access, MySQL or Oracle Databases by using Time-Based Blind SQL Injection attack. The alpa release can be found here.
13. XSSer
XSSer or Cross Site "Scripter" is an automatic -framework- to detect, exploit and report XSS vulnerabilities in web-based applications. It also includes a GUI interface by using the command : ./xxser --gtk. You can download xxser's beta version here.
14. ASP Auditor v2.2
ASP Auditor v2.2 is a an auditing tool for ASP that sends initial probe request, path discovery request, ASP.NET validate discovery request, ASP.NET Apr/07 XSS Check, application trace request, and null remoter service request. By using the opt command -bf, it allows you to brute force ASP.NET version using JS Validate directories.
15.Absinthe
"Absinthe is a GUI-based tool that automates the process of downloading the schema and contents of a database that is vulnerable to Blind SQL Injection. This tool does not aid in the discovery of SQL Injection holes but speeds up the process of data recovery." It supports Microsoft SQL Server, MSDE, Oracle, and Postgres and the tool runs on Linux, Windows and Mac OSX. Download here.
16. SQID
SQID or SQL injection digger is a command line tool written in ruby by Metaeye Security Group that looks for SQL injections and common errors in web sites. It performs a Google search when finding for SQL injections and common errors in web site URLs and crawls a webpage. You can download this tool by checking out its project SVN:
svn checkout svn://rubyforge.org/var/svn/sqid
17.DarkMySQLi
DarkMySQLi is a multi purpose MySQL Injection tool coded in python which is also available for BackTrack 5 as one of its packed tools.
18. fimap
fimap is an automatic LFI/RFI scanner and exploiter coded in python by Iman Karim. It allows a pentester to scan a single URL for File inclusion errors, scan a list of URLS for File Inclusion errors, scan Google search results for FiIe inclusion errors, and harvest all links of a webpage with recurse level of 3 and write the URLs to a file directory.
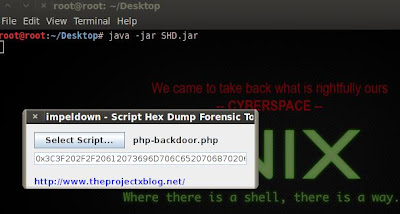
19.Script Hex Dump – Forensic Tool
Script Hex Dump - Forensic Tool is a java application that helps you in parsing your scripts like PHP and automatically converts it as a hex value, some penetration testers use this to test for possible sql injection vulnerability in a website. SQL Injection attack has been a chronic threat especially for those websites running PHP and MySQL as the backend of their database server, one of its capability if the server is not properly configure is the command for writing arbitrary files. You can download this tool here.
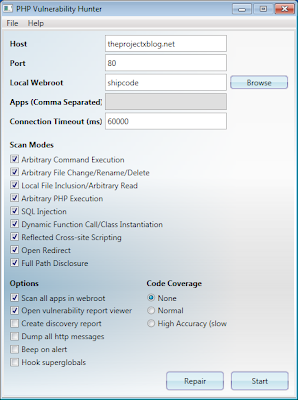
20. PHP Vulnerability Hunter
PHP Vulnerability Hunter is a PHP web application fuzzer that scans for common vulnerabilities like local file inclusion, SQL Injection, full path disclosure, arbitrary command execution and many more. A good tool for analyzing your own web server. You can grab the new version of this tool here which is 1.1.4.6.
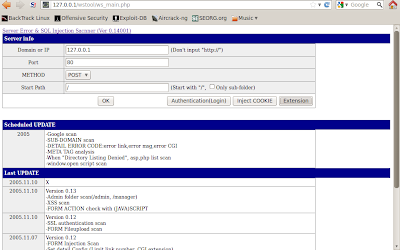
21. WSTOOL : Web vulnerable scan tool
WATOOL is a server error and SQL Injection, XSS or Cross Site Scripting scanner which uses PHP Check up collate with HTML FORM and LINK. You can download this tool here.
22. ProjectX WHMCS Pentesting Tool v.1
Projectx WHMCS Pentesting Tool v.1 is a vulnerability scanner coded in VB.NET that uses a black box approach. It echos the db_username and the db_password of a website that is vulnerable to WHMCS Local File Disclosure. This kind of vulnerability is only applicable to versions 3.x.x and some 4.x.x which was a viral exploit last year that some website administrators took for granted. You can download the tool here.
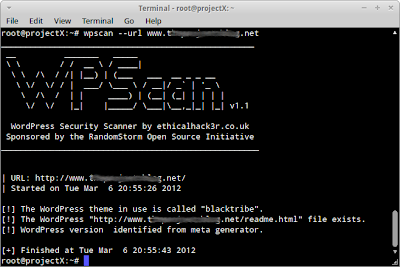
23. Wpscan
WPscan or Wordpress Security Scanner is a pentesting tool written in ruby for Wordpress installations. The tools is coed by Ryan Dewhurst which uses a black box approach in finding security holes for Wordpress like timthumb, easy to guess passwords, plugin holes, etc. You can download wpscan here.
24. Skipfish
Skipfish is an active web application security reconnaissance tool written by Michal Zalewski. Skipfish spiders a URL using the wordlists, a very powerful web scanning tool with a simple implementation. It also scans for vulnerabilities like php injection, XSS, format string vulnerabilities, overflow vulnerabilities, file inclusions , etc. You can download this tool here.
25. WhatWeb
WhatWeb is a web scanner coded by Andrew Horton aka urbanadventurer from Security-Assessment.com. It is used for information gathering because it identifies content management systems (CMS), blogging platforms, stats/analytics packages, javascript libraries, servers, etc. You can download this tool here.
26. OWASP ZAP
Zed Attack Proxy (ZAP) is a project of OWASP which is a GUI penetration testing tool for finding website vulnerabilities and flaws. This open source tool includes features like intercepting proxy, active scanner, passive scanner, brute force scanner, spider, fuzzer, port scanner, dynamic SSL certificates, API, and Beanshell integration. For more information about this tool, check out their website.
27. Webshag
Webshag is a multi-threaded, multi-platform web server auditing tool coded in python. It is used for crawling a URL, port scanning, file fuzzing and audits your website. You can download this security auditing tool here.
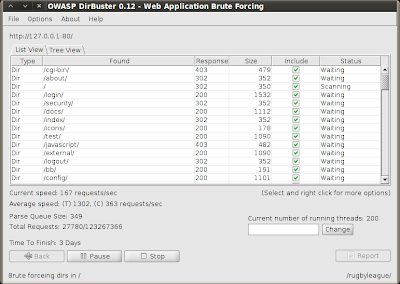
28. OWASP DirBuster
DirBuster is another project of OWASP that a multi threaded java application designed to brute force directories and files names on web/application servers that uses a black box approach for application testing by trying to find hidden content. You can download this tool here.
29. Grendel-Scan
Grendel-Scan is free and open source web application pentesting tool that has an automatic scanning feature which detects common web application vulnerabilities, and features geared at aiding manual penetration tests. Get this tool now.
30. Mopest
Mopest is a PERL Local PHP Vulnerability Scanner for exploits PhpBB 2.0.20 Disable Administrator, PhpBB 2.0.19 Denial of Service - Infinitely topic, phpBB 2.0.15 Database Authentication Details, Invision Power Board 2.0.2 Multipl Users DoS, Invision Power Board 2.1.5 Code Execution, MyBB 1.0 RC4 Sql injection, MyBB 1.1.3 Create An Admin, MyBB Sql Injection, and WordPress 1.5.11 Sql Injection. It also has tools like Fake Mailer, Email Bomber, and MD5 Cracker. You can check out this project here.
31. SecuBat
SecuBat is another web vulnerability scanner which automatically analyzes web sites with the aim of finding exploitable SQL injection and XSS vulnerabilities. You can check this tool here.
32. Arachni
Arachni is an open source web application security scanner framework coded in ruby that helps website administrators and penetration testers evaluate the security of a web application. Arachni asks you for the URL of the target and it automatically performs a simple scan and presents you with its findings which could be a very risky flaw or loophole. You can download this tool here.
33. WebSlayer
WebSlayer is another OWASP project that slays your web application by brute forcing the GET and POST parameters, checking the directories, brute forcing the login forms, fuzzing, brute forcing sessions, Ntml brute forcing, and many more. For more information of this project just check this site.
34. Burp Suite
Burp Suite is penetration testing tool and integrated platform for website security. Burp Suite has cool features like an intercepting proxy, application spider for crawling, detects numerous web application vulnerabilities, repeater tool, allows you to write your own plugins, and many more. The free edition is available for download here.
35. ProxMon
ProxMon is not a Digimon but a Python based open source framework that automates web application tests. Its key features include:
- automatic value tracing of set cookies, sent cookies, query strings and post parameters across sites,
- proxy agnostic
- included library of vulnerability checks
- active testing mode
- cross platform
- easy to program extensible python framework
You can download this tool here.
About the Contributor:
Shipcode is a prolific blogger of ROOTCON and at the same time an InfoSec enthusiast from Cebu. He was inspired to join ROOTCON as part of the core team to share his knowledge in information security. He encourages other like minded individuals to come forward and share their knowledge through blogging right here at ROOTCON Blog section.
ROOTCON is managed by like minded InfoSec professionals across the Philippines. All rights reserved. Designated trademarks, brands and articles are the property of their respective owners.




































 3062
3062











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








