Android Malware Sandbox
This project aim to provide a simple configurable and modulable sandbox for quickly sandbox known or unknown families of Android Malware.
Demo

Installation
First you'll need to install Android-Studio or something that can launch AVD.
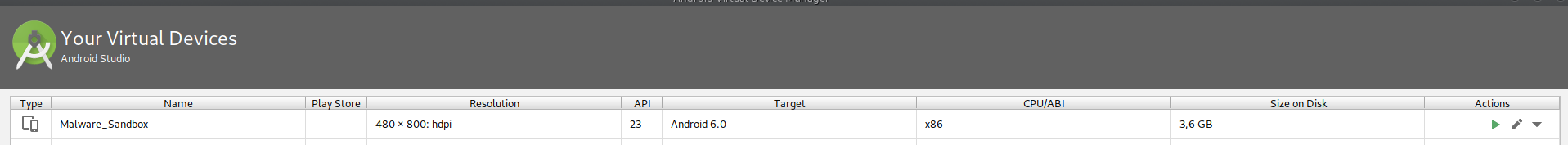
Then you will need to create the AVD you want to run the samples, example :
The you'll need to install dependencies :
python3 -m venv env # python >= 3.6
source env/bin/activate
apt install -y liblzma-dev
pip install -r requirements.txt
pip installfrida-push
npm install
npm install -g frida-compile
They you will need to configure config.ini, change adb_path and emulator_path with the path of your binaries
Next you'll need to config the emulator in config.ini :
# Example
[EMULATOR]
vm_name = Nexus_5X_API_28 # emulator -list-avds
snapshot_name =
use_snapshot = no # to use the snapshot defined under
show_window = yes # to show the emulator
wipe_data = yes # to wipe data at launch
Change the output database file
They are many more options in the config file feel free to change them
All is set up, you can now launch your analysis by using :
python main.py
To customize run, change settings in config.ini.
Reporting
Once an analysis finished, a report is generated in an html file.
The reporting needs improvement, you'll be able to see more in the debug logs and the sqlite database.
Anti anti-emulation
This sandbox has been designed to bypass many anti-emulation technics by using hooks.
Altought new anti-emulation can be added, feel free to contribute.
Hooking
This sample highly rely on Frida hooks, you can add new hooks by adding a plugin in the plugin folder.
To add a plugin, your python source code must contain at least the functions :
def onload() # called when loaded
def onunload() # called when unloaded
def parse(module,message) # Will parse the callbacks text from Frida
def get_frida_script() # To define the frida hook
Test
This sandbox has been tested on the following malware families :
apk.adultswine
apk.ahmyth
apk.anubis
apk.anubisspy
apk.bahamut
apk.brata
apk.cerberus
apk.charger
apk.clientor
apk.comet_bot
apk.connic
apk.cpuminer
apk.filecoder
apk.flexnet
apk.glancelove
apk.irrat
apk.joker
apk.kevdroid
apk.koler
apk.monokle
apk.omnirat
apk.redalert2
apk.riltok
apk.roaming_mantis
apk.sauron_locker
apk.spybanker
apk.telerat
apk.triada
apk.unidentified_001
apk.unidentified_002
apk.unidentified_003
apk.viper_rat
apk.zoopark
apk.ztorg
Thanks
This project uses https://github.com/google/android-emulator-container-scripts to create dockers when the device type is docker
TODO
Improve reports
Add new hooks
Improve dockerisation




















 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








