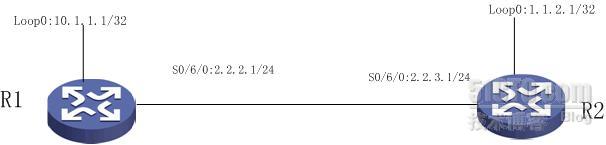
一、组网和实验环境
本文实验采用的交换机是H3C模拟器,下载地址如下:http://forum.h3c.com/forum.php?mod=viewthread&tid=109740&highlight=H3C%E6%A8%A1%E6%8B%9F%E5%99%A8
二、实验过程
配置完成后见如下信息:
1、debu ipsec packet
思路,在R2上发ping包,R1上看debug信息
<R2>ping -a 10.1.2.1 10.1.1.1
PING 10.1.1.1: 56 data bytes, press CTRL_C to break
Reply from 10.1.1.1: bytes=56 Sequence=2 ttl=255 time=5 ms
Reply from 10.1.1.1: bytes=56 Sequence=3 ttl=255 time=4 ms
Reply from 10.1.1.1: bytes=56 Sequence=5 ttl=255 time=4 ms
<R1> debu ipsec packet
*Feb 17 11:37:26:718 2013 R1 IPSEC/7/DBG:--- Receive IPSec(ESP) packet ---收包
*Feb 17 11:37:26:718 2013 R1 IPSEC/7/DBG:Src:2.2.3.1 Dst:2.2.2.1 SPI:54321(0x0000d431)源和目的IP SPI
*Feb 17 11:37:26:718 2013 R1 IPSEC/7/DBG:New ESP(RFC2406) Enc Alg:DES Auth Alg:HMAC-SHA1-96 对比后发现安全协议的算法
*Feb 17 11:37:26:718 2013 R1 IPSEC/7/DBG:ESP new input: Authentication succeed! 验证成功
*Feb 17 11:37:26:718 2013 R1 IPSEC/7/DBG:IPSEC Task: Decryption succeed! 解密成功
*Feb 17 11:37:26:718 2013 R1 IPSEC/7/DBG:Tunnel mode. Org Src:10.1.2.1 Org Dst:10.1.1.1 解开后发现包的内部源和目的
*Feb 17 11:37:26:718 2013 R1 IPSEC/7/DBG:Now send it to IP input process... 现在开始进入发包进程
*Feb 17 11:37:26:718 2013 R1 IPSEC/7/DBG:--- Send IPSec packet ---发包
*Feb 17 11:37:26:718 2013 R1 IPSEC/7/DBG:Tunnel mode. Adding outer IP header succeed! 加IP包
*Feb 17 11:37:26:718 2013 R1 IPSEC/7/DBG:Src:2.2.2.1 Dst:2.2.3.1 SPI:12345(0x00003039) 外部头的源和目的
*Feb 17 11:37:26:718 2013 R1 IPSEC/7/DBG:New ESP(RFC2406) Enc Alg:DES Auth Alg:HMAC-SHA1-96 算法
*Feb 17 11:37:26:718 2013 R1 IPSEC/7/DBG:Encryption finished! New ESP(RFC2406) SN:1 加密完成
*Feb 17 11:37:26:718 2013 R1 IPSEC/7/DBG:Now send it to IP output process... 进入发包进程
以上是一个收发包过程
2、我们来看R1上ipsec的相关显示信息
<R1>dis ipsec ?
policy Display IPSec security policy information
policy-template Display IPSec security policy template information
profile Display IPsec Profile info
proposal Display configured IPSec proposal
sa Display IPSec security association information
session Display IPsec session information
statistics Display statistics information of security packets
tunnel Display IPSec tunnel information
<R1> dis ipsec poli
<R1> dis ipsec policy
===========================================
IPsec Policy Group: "map1"
Using interface: {Serial0/6/0}
===========================================
-----------------------------
IPsec policy name: "map1"
sequence number: 10
mode: manual
-----------------------------
security data flow : 3101
tunnel local address: 2.2.2.1
tunnel remote address: 2.2.3.1
proposal name:tran1
inbound AH setting:
AH spi:
AH string-key:
AH authentication hex key:
inbound ESP setting:
ESP spi: 54321 (0xd431)
ESP string-key: gfedcba
ESP encryption hex key:
ESP authentication hex key:
outbound AH setting:
AH spi:
AH string-key:
AH authentication hex key:
outbound ESP setting:
ESP spi: 12345 (0x3039)
ESP string-key: abcdefg
ESP encryption hex key:
ESP authentication hex key:
<R1> dis ipsec proposal
IPsec proposal name: tran1
encapsulation mode: tunnel
transform: esp-new
ESP protocol: authentication sha1-hmac-96, encryption des
<R1>
<R1> dis ipsec sa 注:手工配置的Ipsec sa配置完成就存在
===============================
Interface: Serial0/6/0
path MTU: 1500
===============================
-----------------------------
IPsec policy name: "map1" 名字是本地有效
sequence number: 10
mode: manual
-----------------------------
encapsulation mode: tunnel
perfect forward secrecy: None
tunnel:
local address: 2.2.2.1
remote address: 2.2.3.1
Flow :
as defined in acl 3101
[inbound ESP SAs]
spi: 54321 (0xd431)
proposal: ESP-ENCRYPT-DES ESP-AUTH-SHA1
No duration limit for this sa
[outbound ESP SAs]
spi: 12345 (0x3039)
proposal: ESP-ENCRYPT-DES ESP-AUTH-SHA1
No duration limit for this sa
<R1> dis ipsec se
<R1> dis ipsec session
<R1> dis ipsec session 当前会话
------------------------------------------------------------
total sessions : 1
------------------------------------------------------------
tunnel-id : 2
session idle time/total duration (sec) : 3/300
session flow : (4 times matched)
Sour Addr : 10.1.1.1 Sour Port: 0 Protocol : 1
Dest Addr : 10.1.2.1 Dest Port: 0 Protocol : 1
<R1> dis ipsec tu
<R1> dis ipsec tunnel 隧道
total tunnel : 1
------------------------------------------------
Connection ID : 2
Perfect forward secrecy: None
SA's SPI :
Inbound : 54321 (0xd431) [ESP]
Outbound : 12345 (0x3039) [ESP]
Tunnel :
Local Address: 2.2.2.1 Remote Address : 2.2.3.1
Flow :
As defined in acl 3101
Current Encrypt-card : None
<R1> dis ipsec ?
policy Display IPSec security policy information
policy-template Display IPSec security policy template information
profile Display IPsec Profile info
proposal Display configured IPSec proposal
sa Display IPSec security association information
session Display IPsec session information
statistics Display statistics information of security packets
tunnel Display IPSec tunnel information
<R1> dis ipsec st
<R1> dis ipsec statistics
the security packet statistics:
input/output security packets: 35/35
input/output security bytes: 2940/2940
input/output dropped security packets: 0/0
dropped security packet detail:
not enough memory: 0
can't find SA: 0
queue is full: 0
authentication has failed: 0
wrong length: 0
replay packet: 0
packet too long: 0
wrong SA: 0
<R1> dis ipsec statistics
the security packet statistics:
input/output security packets: 40/40
input/output security bytes: 3360/3360
input/output dropped security packets: 0/0
dropped security packet detail:
not enough memory: 0
can't find SA: 0
queue is full: 0
authentication has failed: 0
wrong length: 0
replay packet: 0
packet too long: 0
wrong SA: 0
<R1>
三、配置文本
R1:
<R1>DIS CU
#
version 5.20, Alpha 1011
#
sysname R1
#
password-control login-attempt 3 exceed lock-time 120
#
undo voice vlan mac-address 00e0-bb00-0000
#
ipsec cpu-backup enable
#
undo cryptoengine enable
#
domain default enable system
#
vlan 1
#
domain system
access-limit disable
state active
idle-cut disable
self-service-url disable
#
ipsec proposal tran1
esp authentication-algorithm sha1
#
ipsec policy map1 10 manual
security acl 3101
proposal tran1
tunnel local 2.2.2.1
tunnel remote 2.2.3.1
sa spi inbound esp 54321
sa string-key inbound esp gfedcba
sa spi outbound esp 12345
sa string-key outbound esp abcdefg
#
acl number 3101
rule 0 permit ip source 10.1.1.1 0 destination 10.1.2.1 0
#
interface Serial0/6/0
link-protocol ppp
ip address 2.2.2.1 255.255.255.0
ipsec policy map1
#
interface Serial0/6/1
link-protocol ppp
#
interface Serial0/6/2
link-protocol ppp
#
interface Serial0/6/3
link-protocol ppp
#
interface NULL0
#
interface LoopBack0
ip address 10.1.1.1 255.255.255.255
#
interface Ethernet0/4/0
port link-mode bridge
#
interface Ethernet0/4/1
port link-mode bridge
#
interface Ethernet0/4/2
port link-mode bridge
#
interface Ethernet0/4/3
port link-mode bridge
#
interface Ethernet0/4/4
port link-mode bridge
#
interface Ethernet0/4/5
port link-mode bridge
#
interface Ethernet0/4/6
port link-mode bridge
#
interface Ethernet0/4/7
port link-mode bridge
#
ip route-static 0.0.0.0 0.0.0.0 Serial0/6/0
#
load xml-configuration
#
user-interface con 0
user-interface vty 0 4
#
return
转载于:https://blog.51cto.com/hciewd/1134395





















 2562
2562











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








