保存和备份iptables规则
service iptables save //会把规则保存到/etc/sysconfig/iptables
把iptables规则备份到my.ipt文件中:
iptables-save > my.ipt 恢复刚才备份的规则:
iptables-restore < my.ipt
1.保存规则
[root@yong-02 ~]# service iptables save
iptables: Saving firewall rules to /etc/sysconfig/iptables:[ 确定 ]它会保存到配置文件/etc/sysconfig/iptables中
[root@yong-02 ~]# cat /etc/sysconfig/iptables
# Generated by iptables-save v1.4.21 on Thu May 10 21:26:10 2018
*filter
:INPUT ACCEPT [0:0]
:FORWARD ACCEPT [0:0]
:OUTPUT ACCEPT [288:23091]
-A INPUT -m state --state RELATED,ESTABLISHED -j ACCEPT
-A INPUT -p icmp -j ACCEPT
-A INPUT -i lo -j ACCEPT
-A INPUT -p tcp -m state --state NEW -m tcp --dport 22 -j ACCEPT
-A INPUT -j REJECT --reject-with icmp-host-prohibited
-A FORWARD -j REJECT --reject-with icmp-host-prohibited
COMMIT
# Completed on Thu May 10 21:26:10 20182.备份规则 另外一个位置
[root@yong-02 ~]# iptables-save > /tmp/ipt.txt查看规则
[root@yong-02 ~]# cat /tmp/ipt.txt
# Generated by iptables-save v1.4.21 on Thu May 10 21:28:08 2018
*filter
:INPUT ACCEPT [0:0]
:FORWARD ACCEPT [0:0]
:OUTPUT ACCEPT [356:29367]
-A INPUT -m state --state RELATED,ESTABLISHED -j ACCEPT
-A INPUT -p icmp -j ACCEPT
-A INPUT -i lo -j ACCEPT
-A INPUT -p tcp -m state --state NEW -m tcp --dport 22 -j ACCEPT
-A INPUT -j REJECT --reject-with icmp-host-prohibited
-A FORWARD -j REJECT --reject-with icmp-host-prohibited
COMMIT
# Completed on Thu May 10 21:28:08 20183.恢复规则
[root@yong-02 ~]# iptables-restore < /tmp/ipt.txt恢复规则一般使用备份规则中,注意:服务器或者重启iptables,它会自动加载配置文件中的规则
Linux防火墙
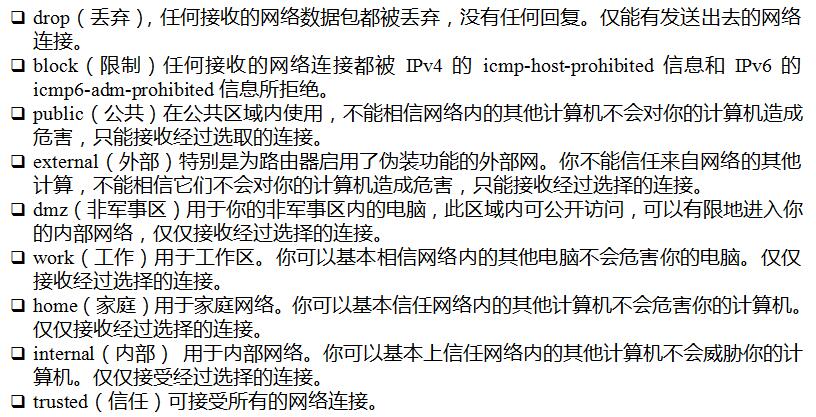
firewalld的9个zone
• 打开firewalld
• systemctl disable iptables 禁用iptables
• systemctl stop iptables
• systemctl enable firewalld
• systemctl start firewalld
• firewalld默认有9个zone
• 默认zone为public
• firewall-cmd --get-zones //查看所有zone
• firewall-cmd --get-default-zone//查看默认zone
- 关闭开机自动启动netfilter
[root@yong-02 ~]# systemctl disable iptables
Removed symlink /etc/systemd/system/basic.target.wants/iptables.service.- 关闭暂停netfilter
[root@yong-02 ~]# systemctl stop iptables
- 设置开机启动firewalld
[root@yong-02 ~]# systemctl enable firewalld
Created symlink from /etc/systemd/system/dbus-org.fedoraproject.FirewallD1.service to /usr/lib/systemd/system/firewalld.service.
Created symlink from /etc/systemd/system/multi-user.target.wants/firewalld.service to /usr/lib/systemd/system/firewalld.service.- 启动firewalld
[root@yong-02 ~]# systemctl start firewalld- 查看firewalld的默认规则
[root@yong-02 ~]# iptables -t nat -nvL
Chain PREROUTING (policy ACCEPT 1 packets, 92 bytes)
pkts bytes target prot opt in out source destination
1 92 PREROUTING_direct all -- * * 0.0.0.0/0 0.0.0.0/0
1 92 PREROUTING_ZONES_SOURCE all -- * * 0.0.0.0/0 0.0.0.0/0
1 92 PREROUTING_ZONES all -- * * 0.0.0.0/0 0.0.0.0/0
Chain INPUT (policy ACCEPT 1 packets, 92 bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
0 0 OUTPUT_direct all -- * * 0.0.0.0/0 0.0.0.0/0
Chain POSTROUTING (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
0 0 POSTROUTING_direct all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 POSTROUTING_ZONES_SOURCE all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 POSTROUTING_ZONES all -- * * 0.0.0.0/0 0.0.0.0/0
Chain OUTPUT_direct (1 references)
pkts bytes target prot opt in out source destination
Chain POSTROUTING_ZONES (1 references)
pkts bytes target prot opt in out source destination
0 0 POST_public all -- * ens33 0.0.0.0/0 0.0.0.0/0 [goto]
0 0 POST_public all -- * + 0.0.0.0/0 0.0.0.0/0 [goto]
Chain POSTROUTING_ZONES_SOURCE (1 references)
pkts bytes target prot opt in out source destination
Chain POSTROUTING_direct (1 references)
pkts bytes target prot opt in out source destination
Chain POST_public (2 references)
pkts bytes target prot opt in out source destination
0 0 POST_public_log all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 POST_public_deny all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 POST_public_allow all -- * * 0.0.0.0/0 0.0.0.0/0
Chain POST_public_allow (1 references)
pkts bytes target prot opt in out source destination
Chain POST_public_deny (1 references)
pkts bytes target prot opt in out source destination
Chain POST_public_log (1 references)
pkts bytes target prot opt in out source destination
Chain PREROUTING_ZONES (1 references)
pkts bytes target prot opt in out source destination
1 92 PRE_public all -- ens33 * 0.0.0.0/0 0.0.0.0/0 [goto]
0 0 PRE_public all -- + * 0.0.0.0/0 0.0.0.0/0 [goto]
Chain PREROUTING_ZONES_SOURCE (1 references)
pkts bytes target prot opt in out source destination
Chain PREROUTING_direct (1 references)
pkts bytes target prot opt in out source destination
Chain PRE_public (2 references)
pkts bytes target prot opt in out source destination
1 92 PRE_public_log all -- * * 0.0.0.0/0 0.0.0.0/0
1 92 PRE_public_deny all -- * * 0.0.0.0/0 0.0.0.0/0
1 92 PRE_public_allow all -- * * 0.0.0.0/0 0.0.0.0/0
Chain PRE_public_allow (1 references)
pkts bytes target prot opt in out source destination
Chain PRE_public_deny (1 references)
pkts bytes target prot opt in out source destination
Chain PRE_public_log (1 references)
pkts bytes target prot opt in out source destination
-
firewalld有9个zone;zone是firewalld的一个单位,centos7默认是public.
-
查看所有的zone
[root@yong-02 ~]# firewall-cmd --get-zones
block dmz drop external home internal public trusted work- 查看系统默认的zone
[root@yong-02 ~]# firewall-cmd --get-default-zone
public9个zone的介绍
firewalld关于zone的操作
• firewall-cmd --set-default-zone=work //设定默认zone
• firewall-cmd --get-zone-of-interface=ens33 //查指定网卡
• firewall-cmd --zone=public --add-interface=lo //给指定网卡设置zone
• firewall-cmd --zone=dmz --change-interface=lo //针对网卡更改zone
• firewall-cmd --zone=dmz --remove-interface=lo //针对网卡删除zone
• firewall-cmd --get-active-zones //查看系统所有网卡所在的zone
- 修改默认的zone值
[root@yong-02 ~]# firewall-cmd --get-default-zone //查看系统默认的zone
public
[root@yong-02 ~]# firewall-cmd --set-default-zone=work //修改默认的zone值
success
[root@yong-02 ~]# firewall-cmd --get-default-zone //查看系统默认的zone
work
- 查看指定网卡所在zone
[root@yong-02 ~]# firewall-cmd --get-zone-of-interface=ens33
work- 给指定的网卡设置zone
[root@yong-02 ~]# firewall-cmd --zone=home --add-interface=lo //指定网卡lo为zone
success
[root@yong-02 ~]# firewall-cmd --get-zone-of-interface=lo //查看网卡lo的zone
home
- 针对网卡更改zone
[root@yong-02 ~]# firewall-cmd --zone=dmz --change-interface=lo //将网卡lo的zone修改成dmz
success
[root@yong-02 ~]# firewall-cmd --get-zone-of-interface=lo //查看网卡lo的zone
dmz
- 针对网卡删除zone
[root@linux-128 ~]# firewall-cmd --zone=dmz --remove-interface=lo
success
[root@linux-128 ~]# firewall-cmd --get-zone-of-interface=lo
no zone
- 查看系统所有网卡所在的zone
[root@yong-02 ~]# firewall-cmd --get-active-zones
dmz
interfaces: lo
work
interfaces: ens33firewalld关于service的操作
• firewall-cmd --get-services 查看所有的servies
• firewall-cmd --list-services //查看当前zone下有哪些services
• firewall-cmd --zone=public --add-service=http //把http增加到public zone下面
• firewall-cmd --zone=public --remove-service=http //移除
• ls /usr/lib/firewalld/zones/ //zone的配置文件模板
• firewall-cmd --zone=public --add-service=http --permanent //更改配置文件,之后会在/etc/firewalld/zones目录下面生成配置文件
• 需求:ftp服务自定义端口1121,需要在work zone下面放行ftp
• cp /usr/lib/firewalld/services/ftp.xml /etc/firewalld/services
• vi /etc/firewalld/services/ftp.xml //把21改为1121
• cp /usr/lib/firewalld/zones/work.xml /etc/firewalld/zones/
• vi /etc/firewalld/zones/work.xml //增加一行
• <service name="ftp"/>
• firewall-cmd --reload //重新加载
• firewall-cmd --zone=work --list-services
- 查看所有的services
[root@yong-02 ~]# firewall-cmd --get-services
RH-Satellite-6 amanda-client amanda-k5-client bacula bacula-client bitcoin bitcoin-rpc bitcoin-testnet bitcoin-testnet-rpc ceph ceph-mon cfengine condor-collector ctdb dhcp dhcpv6 dhcpv6-client dns docker-registry dropbox-lansync elasticsearch freeipa-ldap freeipa-ldaps freeipa-replication freeipa-trust ftp ganglia-client ganglia-master high-availability http https imap imaps ipp ipp-client ipsec iscsi-target kadmin kerberos kibana klogin kpasswd kshell ldap ldaps libvirt libvirt-tls managesieve mdns mosh mountd ms-wbt mssql mysql nfs nrpe ntp openvpn ovirt-imageio ovirt-storageconsole ovirt-vmconsole pmcd pmproxy pmwebapi pmwebapis pop3 pop3s postgresql privoxy proxy-dhcp ptp pulseaudio puppetmaster quassel radius rpc-bind rsh rsyncd samba samba-client sane sip sips smtp smtp-submission smtps snmp snmptrap spideroak-lansync squid ssh synergy syslog syslog-tls telnet tftp tftp-client tinc tor-socks transmission-client vdsm vnc-server wbem-https xmpp-bosh xmpp-client xmpp-local xmpp-server- 查看当前zone下有哪些services
[root@yong-02 ~]# firewall-cmd --get-default-zone //查看当前系统默认的zone
work
[root@yong-02 ~]# firewall-cmd --list-services //查看当前系统默认的zone下有那些service
ssh dhcpv6-client
- 查看指定zone下有那些service
[root@yong-02 ~]# firewall-cmd --zone=public --list-services
ssh dhcpv6-client
-
添加一个service到指定的zone下
[root@yong-02 ~]# firewall-cmd --zone=public --add-service=ftp //将服务ftp添加到public下
success
[root@yong-02 ~]# firewall-cmd --zone=public --list-services //查看public下的services
ssh dhcpv6-client ftp
-
删除指定zone下的service
[root@yong-02 ~]# firewall-cmd --zone=public --remove-service=http //删除public下的服务http
success
[root@yong-02 ~]# firewall-cmd --zone=public --list-services //查看是否删除成功
ssh dhcpv6-client ftp-
zone的配置文件模板
[root@yong-02 ~]# ls /usr/lib/firewalld/zones
block.xml drop.xml home.xml public.xml work.xml
dmz.xml external.xml internal.xml trusted.xml-
更改zone的配置文件
[root@yong-02 ~]# firewall-cmd --zone=public --add-service=http --permanent
success
[root@yong-02 ~]# cat /etc/firewalld/zones/public.xml
<?xml version="1.0" encoding="utf-8"?>
<zone>
<short>Public</short>
<description>For use in public areas. You do not trust the other computers on networks to not harm your computer. Only selected incoming connections are accepted.</description>
<service name="ssh"/>
<service name="dhcpv6-client"/>
<service name="http"/> //已经添加
</zone>在添加一个service ftp
[root@yong-02 ~]# firewall-cmd --zone=public --add-service=ftp --permanent
success
[root@yong-02 ~]# cat /etc/firewalld/zones/public.xml
<?xml version="1.0" encoding="utf-8"?>
<zone>
<short>Public</short>
<description>For use in public areas. You do not trust the other computers on networks to not harm your computer. Only selected incoming connections are accepted.</description>
<service name="ssh"/>
<service name="dhcpv6-client"/>
<service name="http"/>
<service name="ftp"/>
</zone>案例:需求:ftp服务自定义端口1121,需要在work zone下面放行ftp
拷贝配置文件ftp.xml
[root@yong-02 ~]# cp /usr/lib/firewalld/services/ftp.xml /etc/firewalld/services/
[root@yong-02 ~]# vi /etc/firewalld/services/ftp.xml
配置文件如下:
<?xml version="1.0" encoding="utf-8"?>
<service>
<short>FTP</short>
<description>FTP is a protocol used for remote file transfer. If you plan to make your FTP server publicly available, enable this option. You need the vsftpd package installed for this option to be useful.</description>
<port protocol="tcp" port="1121"/>
<module name="nf_conntrack_ftp"/>
</service>
拷贝配置文件work.xml
[root@yong-02 ~]# cp /usr/lib/firewalld/zones/work.xml /etc/firewalld/zones/
[root@yong-02 ~]# vi /etc/firewalld/zones/work.xml
配置文件如下:
<?xml version="1.0" encoding="utf-8"?>
<zone>
<short>Work</short>
<description>For use in work areas. You mostly trust the other computers on networks to not harm your computer. Only selected incoming connections are accepted.</description>
<service name="ssh"/>
<service name="dhcpv6-client"/>
<service name="ftp"/>
</zone>
重新加载 firewall-cmd --reload
[root@yong-02 ~]# firewall-cmd --reload
success查看work下面的service
[root@yong-02 ~]# firewall-cmd --zone=work --list-services
ssh dhcpv6-client ftp























 2275
2275

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








