配制一个SSL站点
1、自建CA签证服务器IP:192.168.1.5 电脑名称:jacktest (Linux5.4-32b)
2、http服务器IP:192.168.1.3 电脑名称:test (Linux5.4-32b)
3、测试服务器IP: 192.168.1.19 电脑名称:test2 (winXP)
4、站点名称与证书站点名称一定要一致,否则有警告;
5、一个IP地址只能建立一个SSL虚拟主机;
一、安装SSL环境
[root@test conf.d]# yum install mod_ssl
Installed:
mod_ssl.i386 1:2.2.3-31.el5
Dependency Installed:
distcache.i386 0:1.4.5-14.1
[root@test conf.d]# rpm -ql mod_ssl
/etc/httpd/conf.d/ssl.conf #ssl配制文件
/usr/lib/httpd/modules/mod_ssl.so #ssl模块
/var/cache/mod_ssl #ssl缓存目录
/var/cache/mod_ssl/scache.dir
/var/cache/mod_ssl/scache.pag
/var/cache/mod_ssl/scache.sem
二、设置CA服务器
[root@jacktest ~]# cd /etc/pki/CA #CA服务器192.168.1.5
[root@jacktest CA]# (umask 077; openssl genrsa -out private/cakey.pem 2048)
Generating RSA private key, 2048 bit long modulus
......+++
........................................................................................+++
e is 65537 (0x10001)
[root@jacktest CA]# ll private/
total 4
-rw------- 1 root root 1679 Dec 28 08:56 cakey.pem
[root@jacktest CA]# vi ../tls/openssl.cnf
[ CA_default ]
dir = /etc/pki/CA # Where everything is kept
certs = $dir/certs # Where the issued certs are kept签发的证书位置
crl_dir = $dir/crl # Where the issued crl are kept吊销的证书位置
database = $dir/index.txt # database index file颁发过的证书索引文件
#unique_subject = no # Set to 'no' to allow creation of
# several ctificates with same subject.
new_certs_dir = $dir/newcerts # default place for new certs.
certificate = $dir/cacert.pem # The CA certificate指明CA的自签证书
serial = $dir/serial # The current serial number 指明当前证书序列号,第一次要指定
...
[ req_distinguished_name ]
countryName = Country Name (2 letter code)
countryName_default = CN
countryName_min = 2
countryName_max = 2
stateOrProvinceName = State or Province Name (full name)
stateOrProvinceName_default = Jiansu
localityName = Locality Name (eg, city)
localityName_default = Suzhou
0.organizationName = Organization Name (eg, company)
0.organizationName_default = jacktest
# we can do this but it is not needed normally :-)
#1.organizationName = Second Organization Name (eg, company)
#1.organizationName_default = World Wide Web Pty Ltd
organizationalUnitName = Organizational Unit Name (eg, section)
#organizationalUnitName_default =
organizationalUnitName_default = Tech
[root@jacktest CA]# openssl req -new -x509 -key private/cakey.pem -out cacert.pem -days 3655
You are about to be asked to enter information that will be incorporated #生成自签证书
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [CN]:
State or Province Name (full name) [Jiansu]:
Locality Name (eg, city) [Suzhou]:
Organization Name (eg, company) [jacktest]:
Organizational Unit Name (eg, section) [Tech]:
Common Name (eg, your name or your server's hostname) []:ca.jacktest.com
Email Address []:admin@jacktest.com
-----BEGIN CERTIFICATE-----
MIIEmDCCA4CgAwIBAgIJANeTZklDKv8MMA0GCSqGSIb3DQEBBQUAMIGOMQswCQYD
...
-----END CERTIFICATE-----
[root@jacktest CA]# mkdir certs crl newcerts
[root@jacktest CA]# touch index.txt
[root@jacktest CA]# echo 01 > serial
[root@jacktest CA]# ls
certs crl index.txt newcerts private serial
三、设置服务器申请证书
[root@test ssl]# (umask 077; openssl genrsa 1024 > httpd.key)
Generating RSA private key, 1024 bit long modulus
.....................................................++++++
....................................++++++
e is 65537 (0x10001)
[root@test ssl]# ll
total 8
-rw------- 1 root root 887 Dec 28 09:40 httpd.key
[root@test ssl]# openssl req -new -key httpd.key -out http.csr
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [CN]:
State or Province Name (full name) [Jiangsu]:
Locality Name (eg, city) [Kunshan]:
Organization Name (eg, company) [Fox]:jacktest #此项要与服务方一致,否则签证不成功
Organizational Unit Name (eg, section) [Tech]:
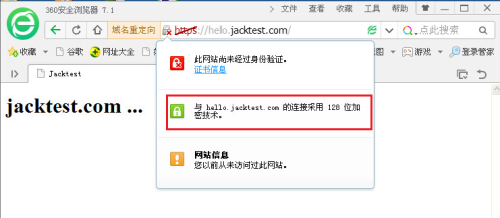
Common Name (eg, your name or your server's hostname) []:hello.jacktest.com
Email Address []:hello@jacktest.com
#hello.jacktest.com站点名称与证书站点名称一定要一致,否则有警告
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:
[root@test ssl]# ll
total 12
-rw-r--r-- 1 root root 704 Dec 28 09:45 http.csr
-rw------- 1 root root 887 Dec 28 09:40 httpd.key
[root@test ssl]# scp http.csr 192.168.1.5:/tmp
http.csr 100% 704 0.7KB/s 00:00
[root@test ssl]#
四、CA服务器收到后签署申请的证书
[root@jacktest CA]# ll /tmp/http.csr
-rw-r--r-- 1 root root 708 Dec 28 10:05 /tmp/http.csr
[root@jacktest CA]# openssl ca -in /tmp/http.csr -out /tmp/http.crt -days 3650
Using configuration from /etc/pki/tls/openssl.cnf
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number: 1 (0x1)
Validity
Not Before: Dec 28 02:08:24 2016 GMT
Not After : Dec 26 02:08:24 2026 GMT
Subject:
countryName = CN
stateOrProvinceName = Jiansu
organizationName = jacktest
organizationalUnitName = Tech
commonName = hello.jacktest.com
emailAddress = hello@jacktest.com
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Comment:
OpenSSL Generated Certificate
X509v3 Subject Key Identifier:
83:4B:E1:D1:C5:0D:A0:F0:44:54:1B:D7:D3:12:C1:05:E6:61:9D:F8
X509v3 Authority Key Identifier:
keyid:38:24:D5:41:1D:98:0D:69:90:0C:95:41:69:72:67:BB:62:4D:4B:A2
Certificate is to be certified until Dec 26 02:08:24 2026 GMT (3650 days)
Sign the certificate? [y/n]:y
1 out of 1 certificate requests certified, commit? [y/n]y
Write out database with 1 new entries
Data Base Updated
[root@jacktest CA]# cd /etc/pki/CA/
[root@jacktest CA]# ls
cacert.pem certs crl index.txt index.txt.attr index.txt.old newcerts private serial serial.old
[root@jacktest CA]# cat index.txt
V 261226020824Z 01 unknown /C=CN/ST=Jiansu/O=jacktest/OU=Tech/CN=hello.jacktest.com/emailAddress=hello@jacktest.com
[root@jacktest CA]# cat serial #下一个签证序号
02
[root@jacktest tmp]# scp http.crt 192.168.1.3:/etc/httpd/ssl/
root@192.168.1.3's password:
http.crt 100% 3885 3.8KB/s 00:00
[root@jacktest tmp]# rm -f http.*
[root@test ssl]# ll #服务器192.168.1.3
total 16
-rw-r--r-- 1 root root 708 Dec 28 09:59 http.csr
-rw-r--r-- 1 root root 3885 Dec 28 10:25 http.crt
-rw------- 1 root root 887 Dec 28 09:57 httpd.key
五、CA服务器收到后签署申请的证书
[root@test conf.d]# vi ssl.conf
<VirtualHost 192.168.1.3:443>
# General setup for the virtual host, inherited from global configuration
#DocumentRoot "/var/www/html"
ServerName www.jacktest.com:443
DocumentRoot "/www/jacktest.com"
# Use separate log files for the SSL virtual host; note that LogLevel
# is not inherited from httpd.conf.
ErrorLog logs/ssl_error_log
TransferLog logs/ssl_access_log
LogLevel warn
# SSL Engine Switch:
# Enable/Disable SSL for this virtual host.
SSLEngine on
# SSL Protocol support:
# List the enable protocol levels with which clients will be able to
# connect. Disable SSLv2 access by default:
SSLProtocol all -SSLv2 #除V2以外
# Server Certificate:
# Point SSLCertificateFile at a PEM encoded certificate. If
# the certificate is encrypted, then you will be prompted for a
# pass phrase. Note that a kill -HUP will prompt again. A new
# certificate can be generated using the genkey(1) command.
SSLCertificateFile /etc/httpd/ssl/httpd.crt
# Server Private Key:
# If the key is not combined with the certificate, use this
# directive to point at the key file. Keep in mind that if
# you've both a RSA and a DSA private key you can configure
# both in parallel (to also allow the use of DSA ciphers, etc.)
SSLCertificateKeyFile /etc/httpd/ssl/httpd.key
[root@test conf.d]# ll /etc/httpd/ssl/http.crt
-rw-r--r-- 1 root root 3885 Dec 28 11:31 /etc/httpd/ssl/http.crt
[root@test conf.d]# httpd -t
Syntax OK
[root@test conf.d]# service httpd restart
Stopping httpd: [FAILED]
Starting httpd: [ OK ]
[root@test conf.d]# netstat -tnlp |grep :443
tcp 0 0 0.0.0.0:443 0.0.0.0:* LISTEN 14998/httpd
[root@test conf.d]# service httpd restart
Stopping httpd: [ OK ]
Starting httpd: [ OK ]
---END---
转载于:https://blog.51cto.com/wangfx/1886872




















 12万+
12万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








