12.13 Nginx防盗链
防盗链,可以和不记录访问日志、过期时间的配置段一起设置:
[root@nginx ~]# vim /usr/local/nginx/conf/vhost/test.com.conf
server
{
listen 80;
server_name test.com test1.com test2.com;
server
{
listen 80;
server_name test.com test1.com test2.com;
index index.html index.php;
root /data/wwwroot/test.com;
# location /
# {
# auth_basic "Auth";
# auth_basic_user_file /usr/local/nginx/conf/htpasswd;
# }
location ~* ^(.+)\.(gif|jpg|jpeg|png|bmp|swf)$ //匹配url
{
expires 7d;
access_log off;
valid_referers none blocked server_names *.test.com; //设定referers白名单
if ($invalid_referer) //如果不是白名单referer
{
return 403; //就返回403拒绝访问
}
}
[root@nginx ~]# /usr/local/nginx/sbin/nginx -t
nginx: the configuration file /usr/local/nginx/conf/nginx.conf syntax is ok
nginx: configuration file /usr/local/nginx/conf/nginx.conf test is successful
[root@nginx ~]# /usr/local/nginx/sbin/nginx -s reload
验证测试防盗链:
[root@nginx ~]# curl -e "http://www.baidu.com" -x127.0.0.1:80 test.com/1.txt
echo "this is test page!"
[root@nginx ~]# curl -e "http://www.baidu.com" -x127.0.0.1:80 test.com/1.gif
<html>
<head><title>403 Forbidden</title></head>
<body bgcolor="white">
<center><h1>403 Forbidden</h1></center>
<hr><center>nginx/1.14.0</center>
</body>
</html>
[root@nginx ~]# curl -e "http://test.com" -x127.0.0.1:80 test.com/1.gif
"this is a gif file"
12.14 Nginx访问控制
对网站目录进行访问控制,限制来源ip:
[root@nginx ~]# vim /usr/local/nginx/conf/vhost/test.com.conf
server
{
listen 80;
server_name test.com test1.com test2.com;
index index.html index.php;
root /data/wwwroot/test.com;
# location /
# {
# auth_basic "Auth";
# auth_basic_user_file /usr/local/nginx/conf/htpasswd;
# }
location /admin/
{
allow 127.0.0.1; //允许本机访问
allow 192.168.87.150; // nginx不像Apache,没有order顺序的概念,如果匹配了ip就执行,后面则不再匹配相同的ip。
deny all; //禁止其他所有ip
}
验证测试对目录admin的访问:
[root@nginx ~]# curl -x127.0.0.1:80 test.com/admin/1.txt -I
HTTP/1.1 200 OK
Server: nginx/1.14.0
Date: Mon, 11 Jun 2018 09:07:54 GMT
Content-Type: text/plain
Content-Length: 0
Last-Modified: Mon, 11 Jun 2018 09:07:06 GMT
Connection: keep-alive
ETag: "5b1e3bba-0"
Accept-Ranges: bytes
[root@nginx ~]# curl -x192.168.87.128:80 test.com/admin/1.txt -I //192.168.87.128不被允许,所以403
HTTP/1.1 403 Forbidden
Server: nginx/1.14.0
Date: Mon, 11 Jun 2018 09:15:21 GMT
Content-Type: text/html
Content-Length: 169
Connection: keep-alive
还可以对文件,或者url进行访问控制:使用正则匹配
server
{
server_name test.com test1.com test2.com;
index index.html index.php;
root /data/wwwroot/test.com;
location ~ .*(abc|image)/.*\.php$ //禁止访问abc或者image目录下的php文件
{
deny all;
}
}
验证测试对url的访问控制:
[root@nginx ~]# curl -x127.0.0.1:80 test.com/abc/2.php -I //访问abc下的php文件403
HTTP/1.1 403 Forbidden
Server: nginx/1.14.0
Date: Mon, 11 Jun 2018 09:28:28 GMT
Content-Type: text/html
Content-Length: 169
Connection: keep-alive
[root@nginx ~]# curl -x127.0.0.1:80 test.com/abc/1.txt -I //访问abc下的txt 200
HTTP/1.1 200 OK
Server: nginx/1.14.0
Date: Mon, 11 Jun 2018 09:28:37 GMT
Content-Type: text/plain
Content-Length: 18
Last-Modified: Mon, 11 Jun 2018 09:28:13 GMT
Connection: keep-alive
ETag: "5b1e40ad-12"
Accept-Ranges: bytes
对user_agent进行访问控制:
[root@nginx ~]# vim /usr/local/nginx/conf/vhost/test.com.conf
server
{
listen 80;
server_name test.com test1.com test2.com;
index index.html index.php;
root /data/wwwroot/test.com;
location /admin/
{
allow 127.0.0.1;
allow 192.168.87.128;
deny all;
}
location ~ .*(abc|image)/.*\.php$
{
deny all;
}
if ($http_user_agent ~* 'spider/3.0|YoudaoBot|Tomato') //匹配user_agent,为黑名单,禁止访问
{
return 403;
}
[root@nginx ~]# curl -A "tomato" -x127.0.0.1:80 test.com/1.txt -I //tomato的403
HTTP/1.1 403 Forbidden
Server: nginx/1.14.0
Date: Mon, 11 Jun 2018 09:34:22 GMT
Content-Type: text/html
Content-Length: 169
Connection: keep-alive
[root@nginx ~]# curl -A "IE" -x127.0.0.1:80 test.com/1.txt -I //IE的200
HTTP/1.1 200 OK
Server: nginx/1.14.0
Date: Mon, 11 Jun 2018 09:35:14 GMT
Content-Type: text/plain
Content-Length: 26
Last-Modified: Sun, 10 Jun 2018 06:15:24 GMT
Connection: keep-alive
ETag: "5b1cc1fc-1a"
Accept-Ranges: bytes
12.15 Nginx解析php相关配置
要增加一段配置才能够解析php:
[root@nginx ~]# vim /usr/local/nginx/conf/vhost/test.com.conf
server
{
listen 80;
server_name test.com test1.com test2.com;
index index.html index.php;
root /data/wwwroot/test.com;
location ~\.php$
{
include fastcgi_params; //
//php的监听sock, 如果php-fpm配置文件里是监听的127.0.0.1:9000,那么这里改为fastcgi_pass 127.0.0.1:9000
//如果写错了sock路径,会报502
fastcgi_pass unix:/tmp/php-fcgi.sock;
fastcgi_index index.php; //主页
fastcgi_param SCRIPT_FILENAME /data/wwwroot/test.com$fastcgi_script_name; //
}
//php-fpm配置文件
[root@nginx test.com]# vim /usr/local/php-fpm/etc/php-fpm.conf
[global]
pid = /usr/local/php-fpm/var/run/php-fpm.pid
error_log = /usr/local/php-fpm/var/log/php-fpm.log
[www]
listen = /tmp/php-fcgi.sock
listen.mode = 666 //上面监听的是sock,这里必须加权限为666,否则502。因为Nginx进程的运行用户是nobody,没有权限读取sock的话,就报错。
user = php-fpm
group = php-fpm
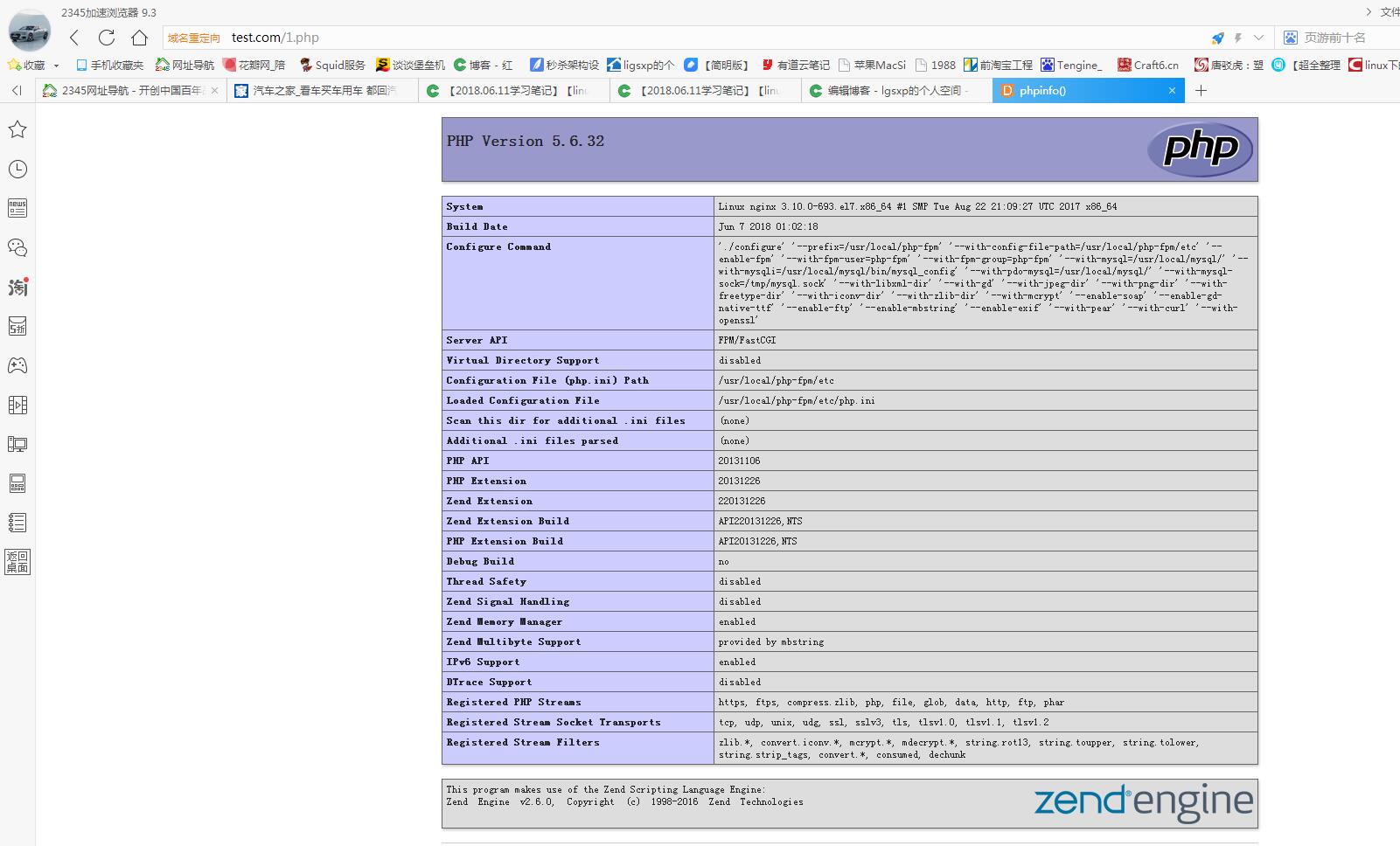
验证测试php页面:
[root@nginx test.com]# vim 1.php
<?php
phpinfo(); //显示php信息函数
[root@nginx test.com]# curl -x127.0.0.1:80 test.com/1.php -I
HTTP/1.1 200 OK
Server: nginx/1.14.0
Date: Mon, 11 Jun 2018 10:14:27 GMT
Content-Type: text/html; charset=UTF-8
Connection: keep-alive
X-Powered-By: PHP/5.6.32
[root@nginx test.com]# curl -x127.0.0.1:80 test.com/1.php
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml"><head>
<style type="text/css">
body {background-color: #fff; color: #222; font-family: sans-serif;}
pre {margin: 0; font-family: monospace;}
a:link {color: #009; text-decoration: none; background-color: #fff;}
a:hover {text-decoration: underline;}
table {border-collapse: collapse; border: 0; width: 934px; box-shadow: 1px 2px 3px #ccc;}
.center {text-align: center;}
.center table {margin: 1em auto; text-align: left;}
.center th {text-align: center !important;}
td, th {border: 1px solid #666; font-size: 75%; vertical-align: baseline; padding: 4px 5px;}
h1 {font-size: 150%;}
h2 {font-size: 125%;}
.p {text-align: left;}
.e {background-color: #ccf; width: 300px; font-weight: bold;}
.h {background-color: #99c; font-weight: bold;}
.v {background-color: #ddd; max-width: 300px; overflow-x: auto;}
.v i {color: #999;}
img {float: right; border: 0;}
浏览器访问php验证:打开服务器的80端口,确保telnet80成功
[root@nginx test.com]# iptables -I INPUT -p tcp --dport 80 -j ACCEPT
[root@nginx test.com]# service iptables save
iptables: Saving firewall rules to /etc/sysconfig/iptables:[ 确定 ]
[root@nginx test.com]# iptables -nvL
Chain INPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
4 172 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:80
12.16 Nginx代理
当用户访问一个网站的时候,那个网站是在私有网内的,外网用户无法访问,可以通过一个能够访问私有网络的代理服务器来间接访问网站。
通过代理服务器,也能够提高网站的访问速度。如大陆用户通过香港的代理服务器访问美国的网站,能够提高访问速度。
在代理服务器上安装Nginx,并进行配置:vhost下新建一个 proxy.conf
[root@nginx vhost]# vim proxy.conf
server
{
listen 80; //监听80端口
server_name ask.apelearn.com; //访问的域名
location /
{
proxy_pass http://223.94.95.10; //代理的web服务器的ip
proxy_set_header Host $Host; //主机名
proxy_set_header X-Real-IP $remote_addr; //客户端ip
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; // 代理服务器ip
}
}
测试验证代理apelearn.com网站
[root@nginx vhost]# curl -x127.0.0.1:80 ask.apelearn.com/robots.txt //通过本机代理 读取了apelearn的蜘蛛机器人文本的内容。
#
# robots.txt for MiWen
#
User-agent: *
Disallow: /?/admin/
Disallow: /?/people/
Disallow: /?/question/
Disallow: /account/
Disallow: /app/
Disallow: /cache/
Disallow: /install/
Disallow: /models/
Disallow: /crond/run/
Disallow: /search/
Disallow: /static/
Disallow: /setting/
Disallow: /system/
Disallow: /tmp/
Disallow: /themes/
Disallow: /uploads/
Disallow: /url-*
Disallow: /views/
Disallow: /*/ajax/[root@nginx vhost]#























 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








