Ipsec实现***
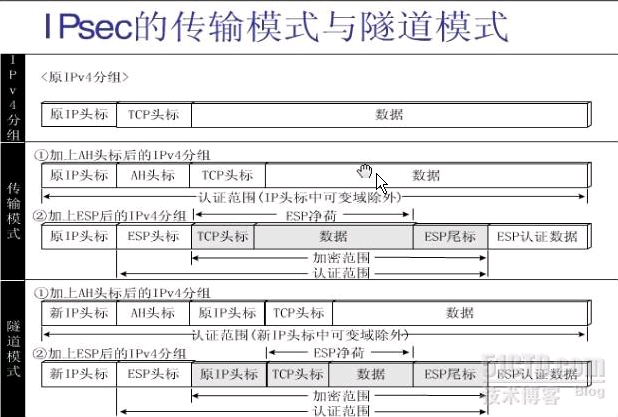
IPSec简介:IPSec 是一系列网络安全协议的总称,它是由IETF(Internet 工程任务组)开发的,可为通讯双方提供访问控制、无连接的完整性、数据来源认证、反重放、加密以及对数据流分类加密等服务。它是网络层的安全机制,通过对网络层包信息的保护,上层应用程序即使没有实现安全性,也能够自动从网络层提供的安全性中获益。这打消了人们对×××安全性的顾虑,使得××× 得以广泛应用。IPSec的工作方式有两种;传输方式;隧道方式。
IPSec对报文的处理过程分析:
为了实现数据包在IP层的安全,IPSec通过加密和数据验证等方式来保证数据报在网络上传输时的保密性、完整性、真实性、抗重播。为了实现上面的4个目标,
IPSec通过两种安全协议:AH(认证头)和ESP(封装安全载荷)。
下面通过一张图来对比分析一下这两种协议:
【AH】
传输方式下:
当原始数据包在网络层传输时,在原始IP头部和TCP头部之间加入AH协议头, 原始的IP头部没有变化。
隧道方式下:
当原始数据包在网络层传输时, 原始的IP头被新的IP头部所替换掉,又在新的IP头和TCP头部之间加入了AH协议头部。
【ESP】
传输方式下:
当原始数据包在网络层传输时,在原始IP头部和TCP头部之间加入ESP协议头, 原始的IP头部没有变化。
隧道方式下:
当原始数据包在网络层传输时, 原始的IP头被新的IP头部所替换掉,又在新的IP头和TCP头部之间加入了ESP协议头部。
【总结】
从安全性来讲,隧道模式优于传输模式。它可以完全地对原始ip数据报进行验证和加密;此外,可以使用IPSec对等体的IP地址来隐藏客户机的ip地址。从性能来讲,隧道模式比传输模式占用更多的带宽,因为它有一个额外的ip头部。
安全联盟【SA】:安全联盟是IPSec的基础,也是IPSec的本质。SA是单向的、在两个对等体之间的双向通信,最少需要两个安全联盟来分别对两个方向的数据流进行安全保护。有两种方式来建立安全联盟:一种是Manual(手工方式);另一种是IKE(自动协商)。
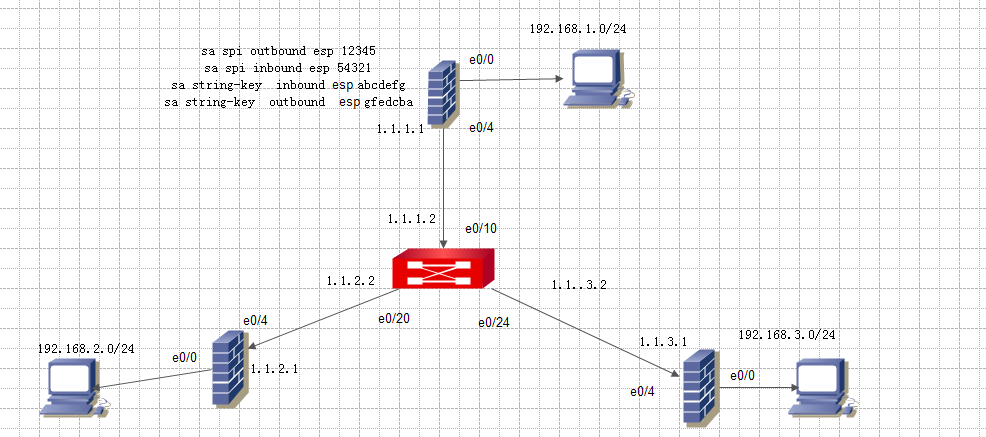
下面来通过一个实验来介绍一下。
【实验拓扑图】
配置步骤:
Step1:定义被保护的数据流(acl)
Step2:定义安全提议
①IPSec工作方式选择:transport(传输方式)/tunnel(隧道方式)【默认】
②选择安全协议类型:AH(认证头)/ESP(封装安全载荷)
③在选择的协议类型下选择相应的加密算法和认证算法。
AH----> authentication-algorithm MD5/SHA1
ESP---->authentication-algorithm MD5/SHA1
----->encryption-algorithm DES/3DES/AES
Step3:定义安全策略(安全策略组) ------>实现acl和安全提议的绑定
Step4: 接口应用安全策略 ----->在接口上应用策略
配置参考:
FW-1配置
[fw1]dis cu
#
sysname fw1
#
firewall packet-filter enable
firewall packet-filter default permit
#
insulate
#
firewall statistic system enable
#
radius scheme system
server-type extended
#
domain system
#
local-user admin
password cipher .]@USE=B,53Q=^Q`MAF4<1!!
service-type telnet terminal
level 3
service-type ftp
#
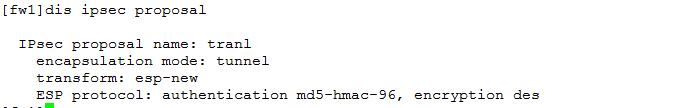
ipsec proposal tranl
#
ipsec policy policy1 10 manual
security acl 3000
proposal tranl
tunnel local 1.1.1.1
tunnel remote 1.1.2.1
sa spi inbound esp 54321
sa string-key inbound esp abcdefg
sa spi outbound esp 12345
sa string-key outbound esp gfedcba
#
acl number 3000 match-order auto
rule 10 permit ip source 192.168.1.0 0.0.0.255 destination 192.168.2.0 0.0.0.255
#
interface Aux0
async mode flow
#
interface Ethernet0/0
loopback
ip address 192.168.1.1 255.255.255.0
#
interface Ethernet0/1
#
interface Ethernet0/2
#
interface Ethernet0/3
#
interface Ethernet0/4
ip address 1.1.1.1 255.255.255.0
ipsec policy policy1
#
interface Encrypt1/0
#
interface NULL0
#
firewall zone local
set priority 100
#
firewall zone trust
add interface Ethernet0/0
add interface Ethernet0/4
set priority 85
#
firewall zone untrust
set priority 5
#
firewall zone DMZ
set priority 50
#
firewall interzone local trust
#
firewall interzone local untrust
#
firewall interzone local DMZ
#
firewall interzone trust untrust
#
firewall interzone trust DMZ
#
firewall interzone DMZ untrust
#
FTP server enable
#
ip route-static 0.0.0.0 0.0.0.0 1.1.1.2 preference 60
#
user-interface con 0
user-interface aux 0
user-interface vty 0 4
authentication-mode scheme
#
return
[fw1]dis ipsec policy
===========================================
IPsec Policy Group: "policy1"
Using interface: {Ethernet0/4}
===========================================
-----------------------------
IPsec policy name: "policy1"
sequence number: 10
mode: manual
-----------------------------
security data flow : 3000
selector mode: standard
tunnel local address: 1.1.1.1
tunnel remote address: 1.1.2.1
proposal name:tranl
inbound AH setting:
AH spi:
AH string-key:
AH authentication hex key:
inbound ESP setting:
ESP spi: 54321 (0xd431)
ESP string-key: abcdefg
ESP encryption hex key:
ESP authentication hex key:
outbound AH setting:
AH spi:
AH string-key:
AH authentication hex key:
outbound ESP setting:
ESP spi: 12345 (0x3039)
ESP string-key: gfedcba
ESP encryption hex key:
ESP authentication hex key:
FW-2配置
[fw2]dis cu
#
sysname fw2
#
firewall packet-filter enable
firewall packet-filter default permit
#
insulate
#
firewall statistic system enable
#
radius scheme system
server-type extended
#
domain system
#
local-user admin
password cipher .]@USE=B,53Q=^Q`MAF4<1!!
service-type telnet terminal
level 3
service-type ftp
#
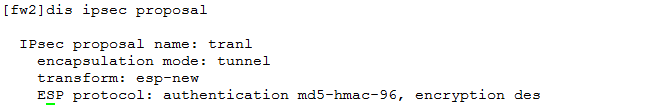
ipsec proposal tranl
#
ipsec policy policy1 10 manual
security acl 3000
proposal tranl
tunnel local 1.1.2.1
tunnel remote 1.1.1.1
sa spi inbound esp 12345
sa string-key inbound esp gfedcba
sa spi outbound esp 54321
sa string-key outbound esp abcdefg
#
acl number 3000 match-order auto
rule 10 permit ip source 192.168.2.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
rule 20 deny ip
#
interface Aux0
async mode flow
#
interface Ethernet0/0
loopback
ip address 192.168.2.1 255.255.255.0
#
interface Ethernet0/1
#
interface Ethernet0/2
#
interface Ethernet0/3
#
interface Ethernet0/4
ip address 1.1.2.1 255.255.255.0
ipsec policy policy1
#
interface Encrypt1/0
#
interface NULL0
#
firewall zone local
set priority 100
#
firewall zone trust
add interface Ethernet0/0
add interface Ethernet0/4
set priority 85
#
firewall zone untrust
set priority 5
#
firewall zone DMZ
set priority 50
#
firewall interzone local trust
#
firewall interzone local untrust
#
firewall interzone local DMZ
#
firewall interzone trust untrust
#
firewall interzone trust DMZ
#
firewall interzone DMZ untrust
#
FTP server enable
#
ip route-static 0.0.0.0 0.0.0.0 1.1.2.2 preference 60
#
user-interface con 0
user-interface aux 0
user-interface vty 0 4
authentication-mode scheme
#
return
[fw2]dis ipsec policy
===========================================
IPsec Policy Group: "policy1"
Using interface: {Ethernet0/4}
===========================================
-----------------------------
IPsec policy name: "policy1"
sequence number: 10
mode: manual
-----------------------------
security data flow : 3000
selector mode: standard
tunnel local address: 1.1.2.1
tunnel remote address: 1.1.1.1
proposal name:tranl
inbound AH setting:
AH spi:
AH string-key:
AH authentication hex key:
inbound ESP setting:
ESP spi: 12345 (0x3039)
ESP string-key: gfedcba
ESP encryption hex key:
ESP authentication hex key:
outbound AH setting:
AH spi:
AH string-key:
AH authentication hex key:
outbound ESP setting:
ESP spi: 54321 (0xd431)
ESP string-key: abcdefg
ESP encryption hex key:
ESP authentication hex key:
交换机配置
<Quidway>dis cu
#
sysname Quidway
#
radius scheme system
server-type huawei
primary authentication 127.0.0.1 1645
primary accounting 127.0.0.1 1646
user-name-format without-domain
domain system
radius-scheme system
access-limit disable
state active
vlan-assignment-mode integer
idle-cut disable
self-service-url disable
messenger time disable
domain default enable system
#
local-server nas-ip 127.0.0.1 key huawei
#
vlan 1
#
vlan 10
#
vlan 20
#
vlan 24
#
interface Vlan-interface1
#
interface Vlan-interface10
ip address 1.1.1.2 255.255.255.0
#
interface Vlan-interface20
ip address 1.1.2.2 255.255.255.0
#
interface Vlan-interface24
ip address 1.1.3.2 255.255.255.0
#
interface Aux0/0
#
interface Ethernet0/1
#
interface Ethernet0/2
#
interface Ethernet0/3
#
interface Ethernet0/4
#
interface Ethernet0/5
#
interface Ethernet0/6
#
interface Ethernet0/7
#
interface Ethernet0/8
#
interface Ethernet0/9
#
interface Ethernet0/10
port access vlan 10
#
interface Ethernet0/11
#
interface Ethernet0/12
#
interface Ethernet0/13
#
interface Ethernet0/14
#
interface Ethernet0/15
#
interface Ethernet0/16
#
interface Ethernet0/17
#
interface Ethernet0/18
#
interface Ethernet0/19
#
interface Ethernet0/20
port access vlan 20
#
interface Ethernet0/21
#
interface Ethernet0/22
#
interface Ethernet0/23
#
interface Ethernet0/24
port access vlan 24
#
interface NULL0
#
user-interface aux 0
user-interface vty 0 4
#
return
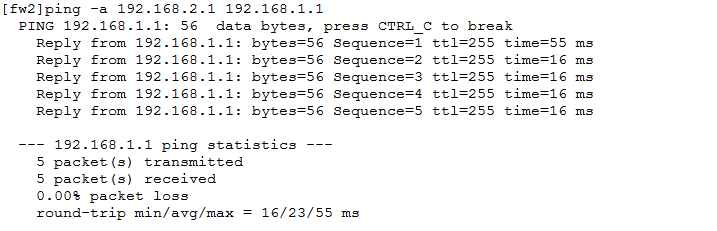
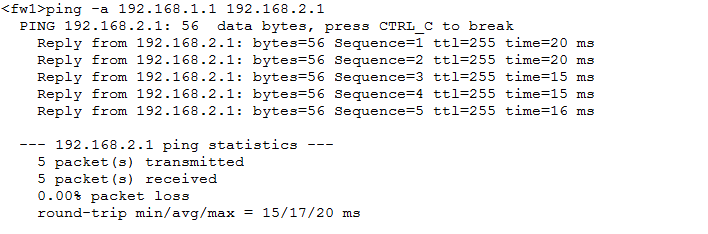
测试结果:
Ping:
转载于:https://blog.51cto.com/muxiaohao/1275539





















 9033
9033











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








