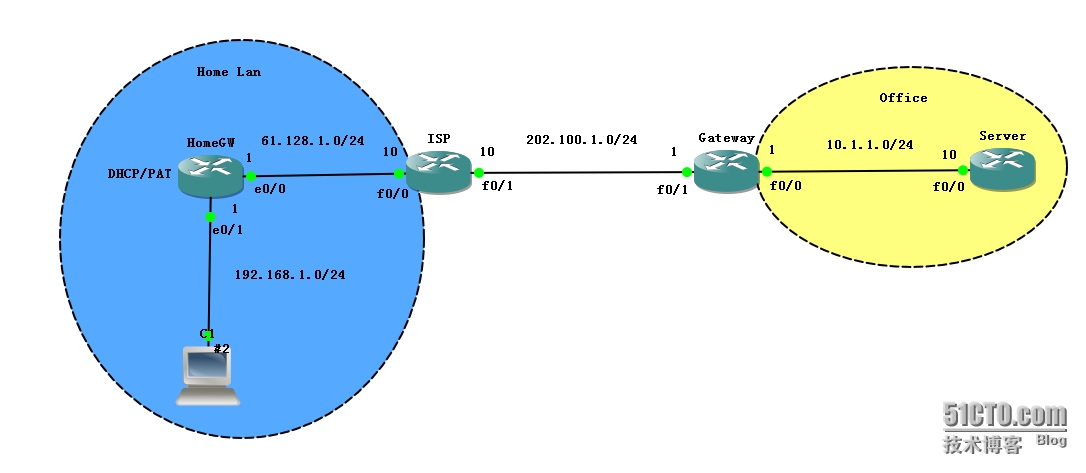
拓扑如下:
要求:C1使用L2TP ×××加密访问Server
配置:
Gateway:
hostname Gateway
interface FastEthernet0/0
ip address 10.1.1.1 255.255.255.0
ip nat inside
interface FastEthernet0/1
ip address 202.100.1.1 255.255.255.0
ip nat outside
ip access-list extended PAT
permit ip 10.1.1.0 0.0.0.255 any
ip nat inside source list PAT interface FastEthernet0/1 overload
ip route 0.0.0.0 0.0.0.0 202.100.1.10
vpdn enable //启用VPDN(Virtual Private Dial-up Networks)功能
vpdn-group 1
Default L2TP VPDN group
accept-dialin //服务器为接受拨入
protocol l2tp
virtual-template 1 //关联到虚拟模板用于克隆产生Virtual-Access接口
l2tp security crypto-profile L2TP-CRY-PROFILE
no l2tp tunnel authentication //禁用L2TP的L2L认证
username cisco password 0 cisco123
ip local pool L2TP-Pool 123.1.1.100 123.1.1.200
interface Virtual-Template1
ip unnumbered FastEthernet0/0 //unnumbered任意一个有IP地址的接口,也可以任意配置IP地址
peer default ip address pool L2TP-Pool
ppp authentication ms-chap-v2 //Windows默认算法
crypto isakmp policy 10 //策略只能如下,因为Windows默认会使用如下的策略
encr 3des
authentication pre-share
group 2
crypto isakmp key cisco@123 address 0.0.0.0 0.0.0.0
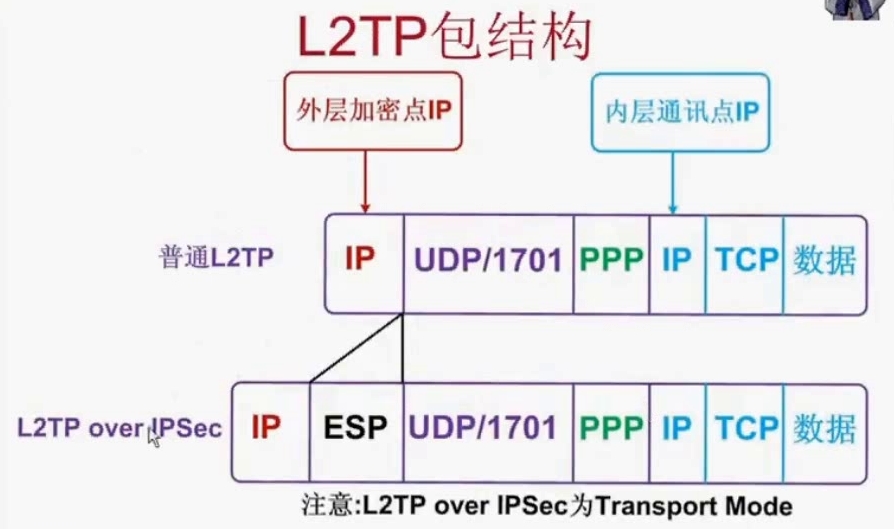
crypto ipsec transform-set myset esp-3des esp-sha-hmac //策略只能如下,因为Windows默认会使用如下的策略
mode transport
crypto map mymap 10 ipsec-isakmp profile L2TP-CRY-PROFILE
set transform-set myset
interface FastEthernet0/1
crypto map mymapServer:
hostname Server
no ip domain lookup
interface FastEthernet0/0
ip address 10.1.1.10 255.255.255.0
no ip routing
ip default-gateway 10.1.1.1
ip http server
line vty 0 4
no login
enable password ciscoISP:
hostname ISP
interface FastEthernet0/0
ip address 61.128.1.10 255.255.255.0
duplex auto
speed auto
!
interface FastEthernet0/1
ip address 202.100.1.10 255.255.255.0
duplex auto
speed autoHomeGW:
hostname HomeGW
interface Ethernet0/0
ip address 61.128.1.1 255.255.255.0
ip nat outside
ip virtual-reassembly
full-duplex
interface Ethernet0/1
ip address 192.168.1.1 255.255.255.0
ip nat inside
ip virtual-reassembly
half-duplex
ip dhcp pool 192
network 192.168.1.0 255.255.255.0
default-router 192.168.1.1
ip dhcp excluded-address 192.168.1.1
ip route 0.0.0.0 0.0.0.0 Ethernet0/0
ip access-list standard PAT
permit any
ip nat inside source list PAT interface Ethernet0/0 overload验证:
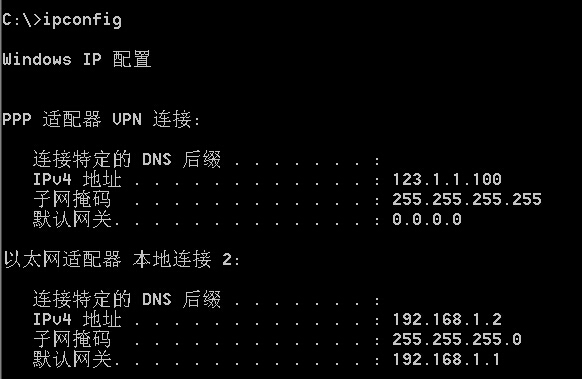
拨号成功后在客户机上查看接口信息:
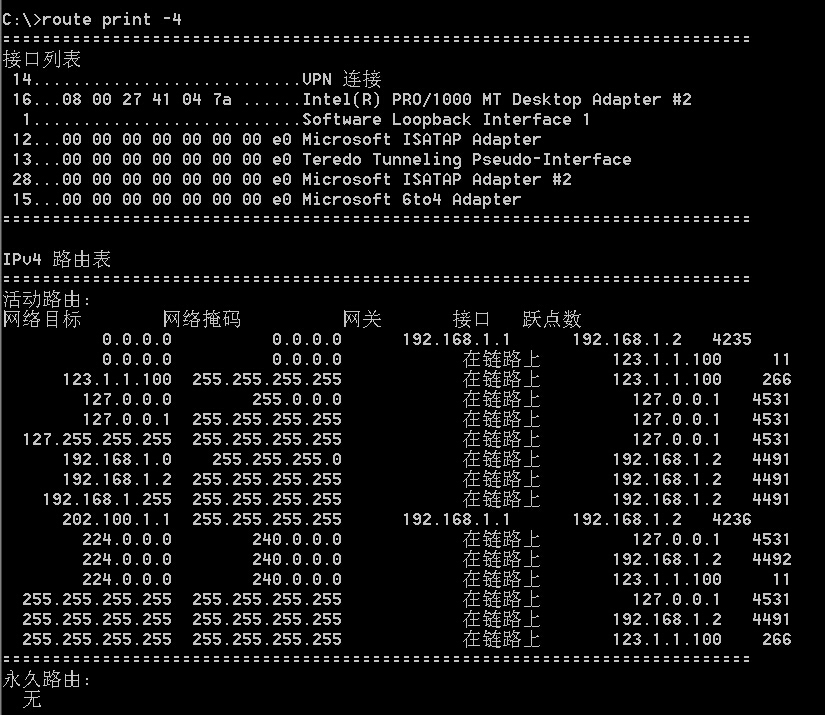
查看客户端路由:
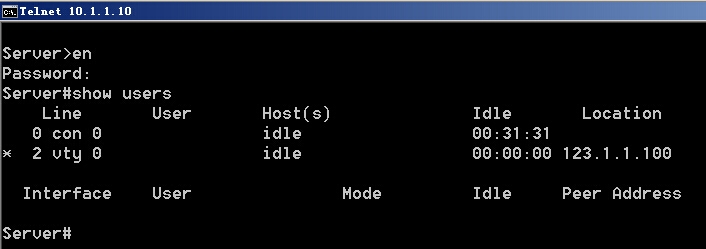
从客户端Telnet到Server:
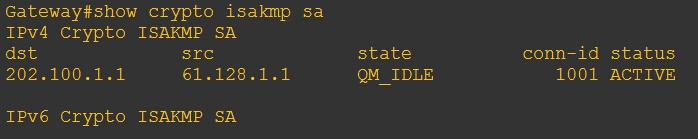
查看ISAKMP SA:
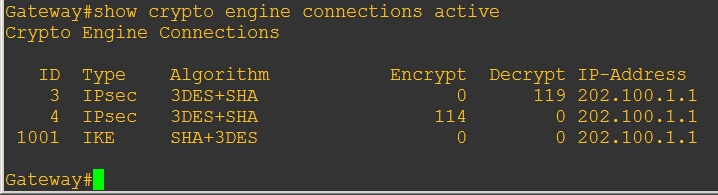
查看IKE和SA:
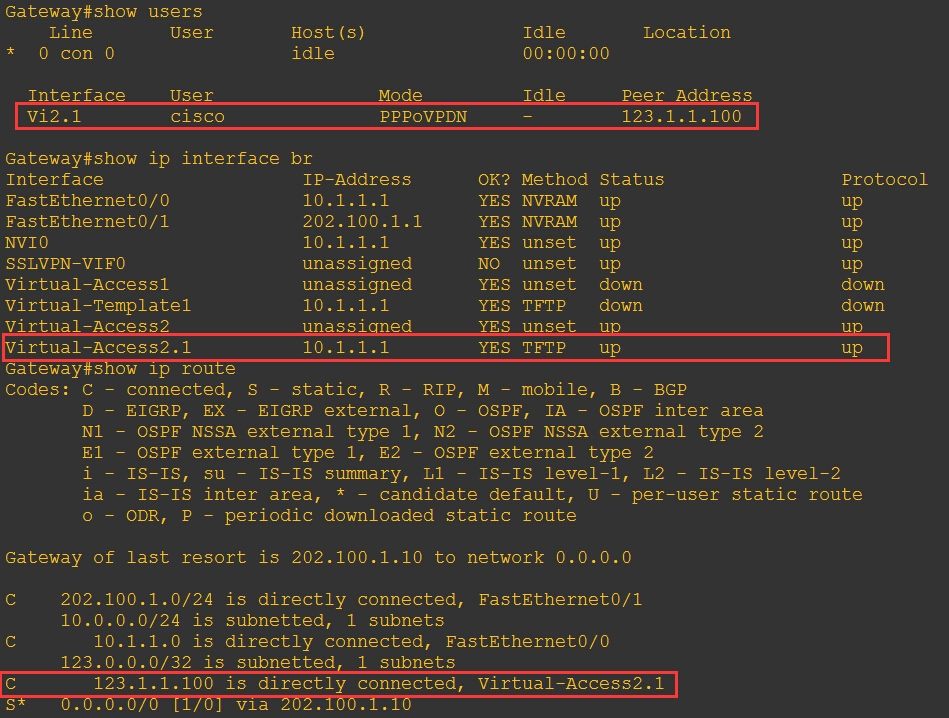
查看拨号上来的用户、接口和路由:
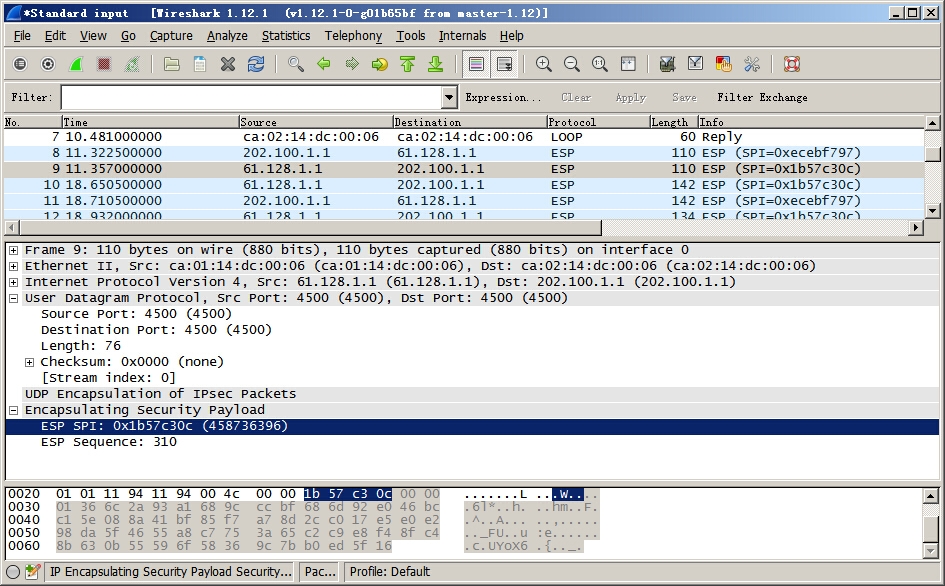
在ISP上抓包结果:
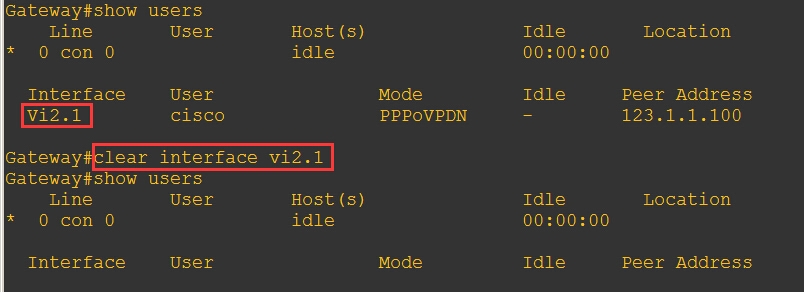
从路由器Gateway断开l2tp×××的方法:
首先查看一个远端用户是从哪个接口连上来的,再使用clear清楚端口:
转载于:https://blog.51cto.com/yinkai/1579190





















 890
890











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








