- 超文本传输协议http协议被用于在Web浏览器和网站服务器之间传递信息,http协议以明文方式发送内容,不提供任何方式的数据加密,安全性低。
- 安全套接字层超文本传输协议https,基于HTTP协议,通过SSL或TLS提供加密处理数据、验证对方身份以及数据完整性保护。
- https协议需要到CA申请证书,阿里云也提供了相应的服务,今天我们就手工生成证书来测试,当然浏览器通过https访问,会提示“不安全”,因为这个证书不是CA系统签发的,以后有项目需求,可以去阿里云购买SLL证书。
## 1、生成CA证书
**(1)查看openssl是否安装**
openssl version -a
- OPENSSLDIR: "/etc/pki/tls",这个是openssl的安装位置
**(2)搭建ca服务器:**
- 根据配置文件信息,到CA根目录,若没有则自己创建
cd /etc/pki/CA
mkdir -pv {certs,crl,newcerts,private}
touch {serial,index.txt}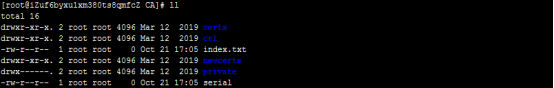
- 证书开始编号
echo 01 >> serial
- ca生成自己的私钥
(umask 077; openssl genrsa -out private/cakey.pem 2048)

- 生成自签证书
openssl req -new -x509 -key /etc/pki/CA/private/cakey.pem -out cacert.pem -days 365
**(3)颁发证书**
- CA搭好了,我们就可以使用这个来为其他证书签名。
- 生成私钥(位置随意)
(umask 077; openssl genrsa -out test.key 2048)

- 生成证书签署请求
openssl req -new -key test.key -out test.csr -days 365
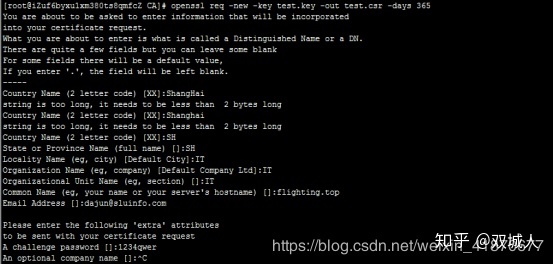
- 此处的CountryName、State、Locality Name、Organization Name、Organizational Unit Name必须和根证书CA的相同,这点注意一下。
**(4)在CA服务器上签署证书**
- 将3生成的.csr文件传输给ca服务器,ca服务器使用命令签署该证,当然我们测试,都在同一个服务器上,直接就在当前目录下操作了。
#颁发证书
openssl ca -in /etc/pki/CA/test.csr -out /etc/pki/CA/certs/test.crt -days 365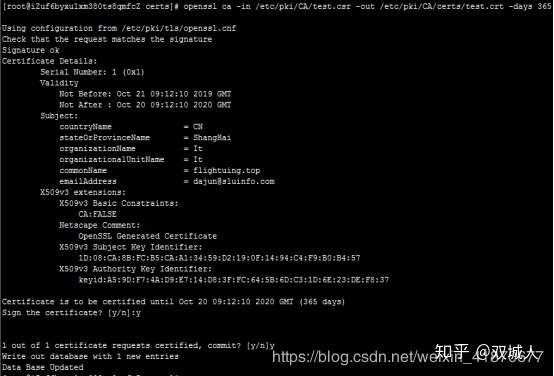
#查看证书信息
openssl x509 -in /etc/pki/CA/test.crt -noout -serial -subject
- 如何将.crt的ssl证书文件转换成.pem格式
openssl x509 -in test.crt -out test.pem
## 2、配置Nginx的证书
- 上面已经生成了CA证书
- 在nginx目录下新建crt目录,把生成的test.crt、test.key移动过去
cd /etc/nginx
mkdir crt
- **下面的比较重要,修改ngxin.conf**
user nginx;
pid /var/run/nginx.pid;
worker_processes auto;
worker_rlimit_nofile 65535;
events {
multi_accept on;
worker_connections 65535;
}
http {
charset utf-8;
sendfile on;
tcp_nopush on;
tcp_nodelay on;
server_tokens off;
log_not_found off;
types_hash_max_size 2048;
client_max_body_size 16M;
# MIME
include mime.types;
default_type application/octet-stream;
# logging
access_log /var/log/nginx/access.log;
error_log /var/log/nginx/error.log warn;
# SSL
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:10m;
ssl_session_tickets off;
# Mozilla Intermediate configuration
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:DHE-RSA-AES128-GCM-SHA256:DHE-RSA-AES256-GCM-SHA384;
# OCSP Stapling
ssl_stapling on;
ssl_stapling_verify on;
resolver 1.1.1.1 1.0.0.1 8.8.8.8 8.8.4.4 208.67.222.222 208.67.220.220 valid=60s;
resolver_timeout 2s;
# load configs
include /etc/nginx/conf.d/*.conf;
server {
listen 10061;
location /nginx_status {
stub_status on;
access_log off;
# allow 127.0.0.1;
# deny all;
}
}
}- include /etc/nginx/conf.d/*.conf;
- 这只是全局的配置,对于每个域名的配置,以及安全策略、代理之类的配置在/conf.cinclude配置
- Nginx 开启status用以监控状态信息,看下面的配置:
server {
listen 10061;
location /nginx_status {
stub_status on;
access_log off;
# allow 127.0.0.1;
# deny all;
}
}- 访问http://47.101.201.179:10061/nginx_status

- Active connections: 4 表示Nginx正在处理的活动连接数4个。
- server 13 表示Nginx启动到现在共处理了13个连接
- accepts 13 表示Nginx启动到现在共成功创建13次握手
- handled requests 14 表示总共处理了 14 次请求
- Reading:Nginx 读取到客户端的 Header 信息数
- Writing:Nginx 返回给客户端 Header 信息数
- Waiting:Nginx 已经处理完正在等候下一次请求指令的驻留链接(开启keep-alive的情况下,这个值等于Active-(Reading+Writing))
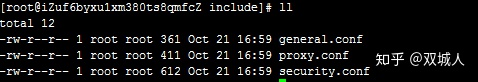
cd /etc/nginx/conf.d
- 新增****.conf,如图命名规则,可以清晰看出访问方式以及域名
- https.www.flighting.top.conf
# HTTP redirect
server {
# SSL开启方式
listen 443 ssl;
server_name www.flighting.top;
# SSL
ssl_certificate /etc/nginx/crt/test.crt;
ssl_certificate_key /etc/nginx/crt/test.key;
# security
#include conf.d/include/security.conf;
# logging
access_log /var/log/nginx/access.log;
error_log /var/log/nginx/error.log warn;
# reverse proxy
#location / {
# proxy_pass http://mps;
# include conf.d/include/proxy.conf;
#}
location / {
root /usr/share/nginx/html;
index index.html index.htm;
}
# additional config
#include conf.d/include/general.conf;
}
```
- http.www.flighting.top.conf
```bash
# HTTP redirect
server {
listen 80;
server_name www.flighting.top;
location / {
root /usr/share/nginx/html;
index index.html index.htm;
}
}- ssl_certificate 、ssl_certificate_key 就是crt下面的crt、key文件
- 下面来看include下面的几个文件
- general.conf
# favicon.ico
location = /favicon.ico {
log_not_found off;
access_log off;
}
# robots.txt
location = /robots.txt {
log_not_found off;
access_log off;
}
# gzip
gzip on;
gzip_vary on;
gzip_proxied any;
gzip_comp_level 6;
gzip_types text/plain text/css text/xml application/json application/javascript application/rss+xml application/atom+xml image/svg+xml;
```
- proxy.conf
```
# favicon.ico
location = /favicon.ico {
log_not_found off;
access_log off;
}
# robots.txt
location = /robots.txt {
log_not_found off;
access_log off;
}
# gzip
gzip on;
gzip_vary on;
gzip_proxied any;
gzip_comp_level 6;
gzip_types text/plain text/css text/xml application/json application/javascript application/rss+xml application/atom+xml image/svg+xml;
[root@iZuf6byxu1xm380ts8qmfcZ include]# cat proxy.conf
proxy_http_version 1.1;
proxy_cache_bypass $http_upgrade;
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Connection "upgrade";
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-Host $host;
proxy_set_header X-Forwarded-Port $server_port;- security.conf
# security headers
#add_header X-Frame-Options "SAMEORIGIN" always;
#add_header X-XSS-Protection "1; mode=block" always;
#add_header X-Content-Type-Options "nosniff" always;
add_header Referrer-Policy "no-referrer-when-downgrade" always;
#add_header Content-Security-Policy "default-src 'self' http: https: data: blob: 'unsafe-inline'" always;
#add_header Content-Security-Policy "default-src 'self' http: https: data: blob: 'unsafe-inline' 'unsafe-eval'" always;
add_header Strict-Transport-Security "max-age=31536000; includeSubDomains; preload" always;
# . files
location ~ /.(?!well-known) {
deny all;
}- 这些只是常用的,具体的看项目需求。
## 3、测试
- 由于域名未备案,所以只能访问ip
- 访问https://47.101.201.179,提示不安全的链接

- 访问http://47.101.201.179




















 2310
2310











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








