解压文件包发现三个文件,flag.enc、pubkey.pem和rsa.py个文件。
一、看到.pem先用openssl解开公钥n和e
在xshell输入命令行:
openssl rsa -bubin -text -modulus -in warmup -in pubkey.pem
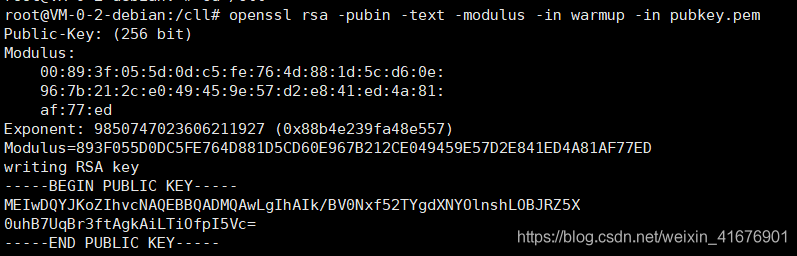
看到e和n了吗!!!
先把十六进制的n转换成十进制的n,如下:
e=9850747023606211927
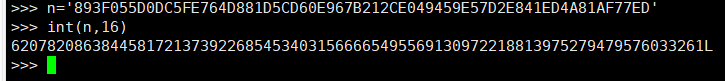
于是我们得到n=62078208638445817213739226854534031566665495569130972218813975279479576033261
对于rsa看到n啥也别想,先把p和q分解出来
use-http://www.factordb.com to decomposition factor
q=184333227921154992916659782580114145999
p=336771668019607304680919844592337860739
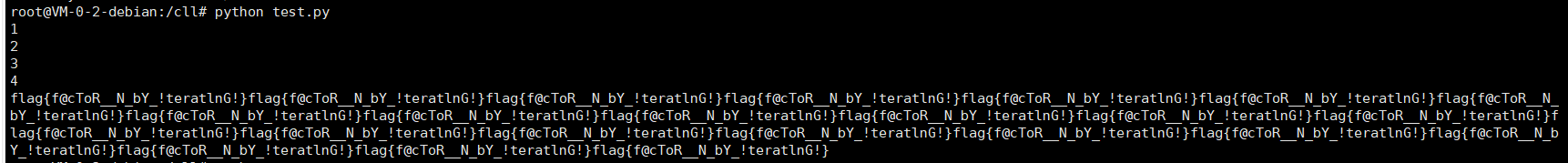
然后根据提供的rsa.py编写解密脚本:
#!/usr/bin/env python2.7
from gmpy import *
from Crypto.Util.number import getPrime
from Crypto.PublicKey import RSA
from Crypto.Cipher import PKCS1_v1_5
from base64 import b64decode
flag_encode=b64decode(open('flag.enc','r').read())
pub=RSA.importKey(open('pubkey.pem','r').read())
n=pub.n
e=pub.e
q=184333227921154992916659782580114145999
p=336771668019607304680919844592337860739
i=1
while 1:
print i
i+=1
n=q*p
if n >= int(flag_encode.encode('hex'),16):
fn=(p-1)*(q-1)
d=invert(e,fn)
prikey=RSA.construct((int(n),int(e),int(d)))
key=PKCS1_v1_5.new(prikey)
dec=key.decrypt(flag_encode,None)
break
else:
p=next_prime(p**2+q**2)
q=next_prime(2*q*p)
e=next_prime(e**2)
print dec
然后丢去xshell得到:





















 1783
1783











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








