目录
使用libmemunreachable+mallocdebug分析
使用lsan遇到困难
一般使用lsan来查memleak效率最高,不过针对cameraserver hook到asan库时有一些其他的报错。
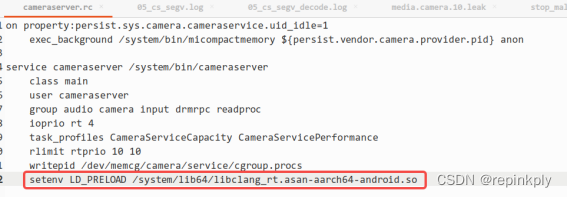
而且报错看起来还不太好解决:
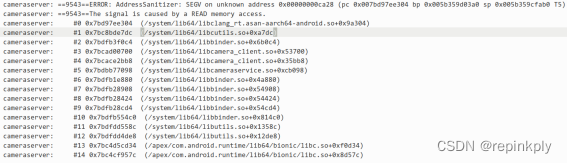
看下如何针对camerasever使能lsan,后续研究。
使用libmemunreachable+mallocdebug分析
原理
相关的原理可以参考官方说明:
https://cs.android.com/android/platform/superproject/+/master:system/memory/libmemunreachable/?q=libmemunreachable
据说到Android U(?)以后,还可以官方支持设置backtrace size,高级高级:
Starting with Android U, new malloc debug options have been added that allow specific sized allocation to be backtraced. The three new options are:
- backtrace_size
- backtrace_min_size
- backtrace_max_size
打开malloc debug
adb root
adb remount
adb shell setenforce 0
adb shell setprop libc.debug.malloc.program cameraserver
adb shell setprop libc.debug.malloc.options "\"backtrace\""
adb shell stop cameraserver
adb shell start cameraserver
dumpsys media.camera
使用命令adb shell dumpsys media.camera --unreachable
如果没有打开malloc debug的话,只能看到leak的size,没有backtrace:
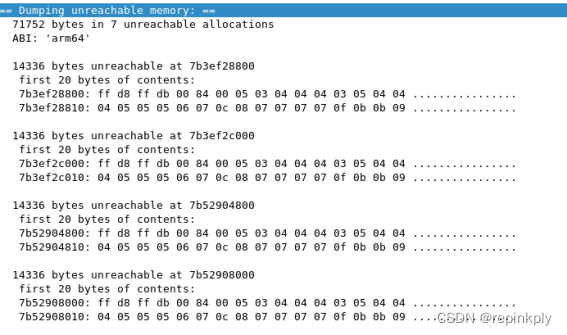
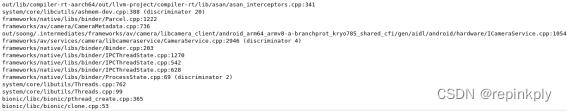
打开malloc debug的话,就可以看到backtrace:
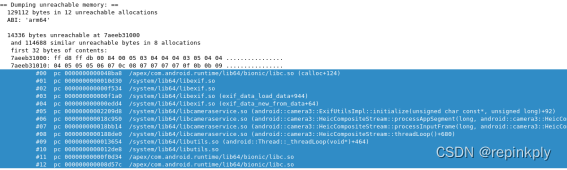
有backtrace的话就很好分析了。
Backtrace
wj@wj:~/SSD_1T/M2_code/prebuilts/clang/host/linux-x86/llvm-binutils-stable$ ./llvm-addr2line -Cfe ~/下载/nuwa_pre_symbols_1009.001_13.0_e8db6882b9_ssi/out/target/product/missi/symbols/system/lib64/libexif.so 0000000000010d28
exif_data_alloc
external/libexif/libexif/exif-data.c:74
wj@wj:~/SSD_1T/M2_code/prebuilts/clang/host/linux-x86/llvm-binutils-stable$ ./llvm-addr2line -Cfe ~/下载/nuwa_pre_symbols_1009.001_13.0_e8db6882b9_ssi/out/target/product/missi/symbols/system/lib64/libexif.so 000000000000f614
exif_data_load_data_content
external/libexif/libexif/exif-data.c:444
wj@wj:~/SSD_1T/M2_code/prebuilts/clang/host/linux-x86/llvm-binutils-stable$ ./llvm-addr2line -Cfe ~/下载/nuwa_pre_symbols_1009.001_13.0_e8db6882b9_ssi/out/target/product/missi/symbols/system/lib64/libexif.so 000000000000f168
exif_data_load_data
external/libexif/libexif/exif-data.c:912 (discriminator 2)
wj@wj:~/SSD_1T/M2_code/prebuilts/clang/host/linux-x86/llvm-binutils-stable$ ./llvm-addr2line -Cfe ~/下载/nuwa_pre_symbols_1009.001_13.0_e8db6882b9_ssi/out/target/product/missi/symbols/system/lib64/libexif.so 000000000000edd4
exif_data_new_from_data
external/libexif/libexif/exif-data.c:152
wj@wj:~/SSD_1T/M2_code/prebuilts/clang/host/linux-x86/llvm-binutils-stable$ ./llvm-addr2line -Cfe ~/下载/nuwa_pre_symbols_1009.001_13.0_e8db6882b9_ssi/out/target/product/missi/symbols/system/lib64/libcameraservice.so 000000000027c3dc
android::camera3::ExifUtilsImpl::initialize(unsigned char const*, unsigned long)
frameworks/av/services/camera/libcameraservice/utils/ExifUtils.cpp:312
wj@wj:~/SSD_1T/M2_code/prebuilts/clang/host/linux-x86/llvm-binutils-stable$ ./llvm-addr2line -Cfe ~/下载/nuwa_pre_symbols_1009.001_13.0_e8db6882b9_ssi/out/target/product/missi/symbols/system/lib64/libcameraservice.so 00000000001baefc
android::camera3::HeicCompositeStream::processAppSegment(long, android::camera3::HeicCompositeStream::InputFrame&)
frameworks/av/services/camera/libcameraservice/api2/HeicCompositeStream.cpp:985 (discriminator 4)
wj@wj:~/SSD_1T/M2_code/prebuilts/clang/host/linux-x86/llvm-binutils-stable$ ./llvm-addr2line -Cfe ~/下载/nuwa_pre_symbols_1009.001_13.0_e8db6882b9_ssi/out/target/product/missi/symbols/system/lib64/libcameraservice.so 00000000001b9f58
android::camera3::HeicCompositeStream::processInputFrame(long, android::camera3::HeicCompositeStream::InputFrame&)
frameworks/av/services/camera/libcameraservice/api2/HeicCompositeStream.cpp:881 (discriminator 4)
wj@wj:~/SSD_1T/M2_code/prebuilts/clang/host/linux-x86/llvm-binutils-stable$ ./llvm-addr2line -Cfe ~/下载/nuwa_pre_symbols_1009.001_13.0_e8db6882b9_ssi/out/target/product/missi/symbols/system/lib64/libcameraservice.so 00000000001b7240
android::camera3::HeicCompositeStream::threadLoop()
frameworks/av/services/camera/libcameraservice/api2/HeicCompositeStream.cpp:1754 (discriminator 6)根据backtarce解决 memleak 问题。
























 546
546











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










