原创 厦门微思网络
IPSG简介
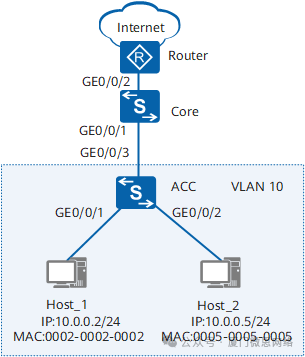
如图1所示,黑客(Host_2主机)私自修改自己的IP地址,使用研发部员工(Host_1主机)的IP地址和MAC地址,伪造合法的IP报文去攻击网络,但是网络管理员却以为是研发部员工在攻击网络。为了避免这种情况发生,在接入交换机上配置静态绑定表,并在连接终端的接口开启IP报文检查功能,只有符合静态绑定表项的报文才能正常访问内外网,不符合静态绑定表的报文给丢掉。
组网需求
如图1所示,用户网关在核心交换机Core上,在Core上部署了ACL指定固定主机可以访问外网,接入交换机ACC连接的Host通过静态方式配置IP地址。管理员希望Host使用管理员分配的固定IP地址上网,不允许私自修改IP地址非法获取外网访问权限。
图1IPSG防止静态主机私自更改IP地址组网图
配置思路
采用如下思路配置IPSG:
-
在用户网关Core上配置ACL,只允许IP地址为10.0.0.2和10.0.0.3的主机访问外网。
-
在接入交换机ACC上创建Host的静态绑定表,固定IP和MAC的绑定关系。
-
在接入交换机ACC上连接用户主机的接口使能IPSG,使Host只能使用管理员分配的固定IP地址上网。即:Host_1可以正常访问外网,Host_2无法访问外网,并且Host_2也无法通过私自修改IP地址来访问外网。
操作步骤
-
配置ACL
<HUAWEI> system-view
[HUAWEI] sysname Core
[Core] vlan batch 10
[Core] interface gigabitethernet 0/0/1
[Core-GigabitEthernet0/0/1] port link-type trunk
[Core-GigabitEthernet0/0/1] port trunk allow-pass vlan 10
[Core-GigabitEthernet0/0/1] quit
[Core] interface vlanif 10 //配置网关地址
[Core-Vlanif10] ip address 10.0.0.1 255.255.255.0
[Core-Vlanif10] quit
[Core] acl number 3001 //配置ACL
[Core-acl-adv-3001] rule permit ip source 10.0.0.2 0
[Core-acl-adv-3001] rule permit ip source 10.0.0.3 0
[Core-acl-adv-3001] rule deny ip source 10.0.0.0 0.0.0.255
[Core-acl-adv-3001] quit
[Core] traffic classifier c1 //配置基于ACL的流分类
[Core-classifier-c1] if-match acl 3001
[Core-classifier-c1] quit
[Core] traffic behavior b1 //配置流行为
[Core-behavior-b1] permit
[Core-behavior-b1] quit
[Core] traffic policy p1 //配置流策略
[Core-trafficpolicy-p1] classifier c1 behavior b1
[Core-trafficpolicy-p1] quit
[Core] interface gigabitethernet 0/0/2
[Core-GigabitEthernet0/0/2] traffic-policy p1 outbound //应用流策略
[Core-GigabitEthernet0/0/2] quit
-
创建Host的静态绑定表项
<HUAWEI> system-view
[HUAWEI] sysname ACC
[ACC] vlan batch 10 //配置VLAN,接入主机
[ACC] interface gigabitethernet 0/0/1
[ACC-GigabitEthernet0/0/1] port link-type access
[ACC-GigabitEthernet0/0/1] port default vlan 10
[ACC-GigabitEthernet0/0/1] quit
[ACC] interface gigabitethernet 0/0/2
[ACC-GigabitEthernet0/0/2] port link-type access
[ACC-GigabitEthernet0/0/2] port default vlan 10
[ACC-GigabitEthernet0/0/2] quit
[ACC] interface gigabitethernet 0/0/3
[ACC-GigabitEthernet0/0/3] port link-type trunk
[ACC-GigabitEthernet0/0/3] port trunk allow-pass vlan 10
[ACC-GigabitEthernet0/0/3] quit
[ACC] user-bind static ip-address 10.0.0.2 mac-address 0002-0002-0002 interface gigabitethernet 0/0/1 //创建Host_1的静态绑定表项
[ACC] user-bind static ip-address 10.0.0.5 mac-address 0005-0005-0005 interface gigabitethernet 0/0/2 //创建Host_2的静态绑定表项
-
使能IPSG功能
# 在连接Host_1的GE0/0/1接口使能IPSG功能。
[ACC] interface gigabitethernet 0/0/1
[ACC-GigabitEthernet0/0/1] ip source check user-bind enable
[ACC-GigabitEthernet0/0/1] quit
# 在连接Host_2的GE0/0/2接口使能IPSG功能。
[ACC] interface gigabitethernet 0/0/2
[ACC-GigabitEthernet0/0/2] ip source check user-bind enable
[ACC-GigabitEthernet0/0/2] quit
-
验证配置结果
在ACC上执行display dhcp static user-bind all命令,可以查看静态绑定表信息。
[ACC] display dhcp static user-bind all
DHCP static Bind-table:
Flags:O - outer vlan ,I - inner vlan ,P - Vlan-mapping
IP Address MAC Address VSI/VLAN(O/I/P) Interface
--------------------------------------------------------------------------------
10.0.0.2 0002-0002-0002 -- /-- /-- GE0/0/1
10.0.0.5 0005-0005-0005 -- /-- /-- GE0/0/2
--------------------------------------------------------------------------------
Print count: 2 Total count: 2
在ACC上执行display dhcp static user-bind all verbose命令,可以查看IPSG的状态,effective表示该条静态表项已生效。
[ACC] display dhcp static user-bind all verbose
DHCP static Bind-table:
Flags:O - outer vlan ,I - inner vlan ,P - Vlan-mapping
--------------------------------------------------------------------------------
IP Address : 10.0.0.2
MAC Address : 0002-0002-0002
VSI : --
VLAN(O/I/P) : -- /-- /--
Interface : GE0/0/1
IPSG Status : effective slot: <0>
--------------------------------------------------------------------------------
IP Address : 10.0.0.5
MAC Address : 0005-0005-0005
VSI : --
VLAN(O/I/P) : -- /-- /--
Interface : GE0/0/2
IPSG Status : effective slot: <0>
--------------------------------------------------------------------------------
Print count: 2 Total count: 2
Host_1可以访问外网,Host_2无法访问外网。将Host_2的IP地址更改为可以上网的IP地址10.0.0.3后依然无法访问外网,并且内网也无法访问。
详细配置文件
-
Core的配置文件
#
sysname Core
#
vlan batch 10
#
acl number 3001
rule 5 permit ip source 10.0.0.2 0
rule 10 permit ip source 10.0.0.3 0
rule 15 deny ip source 10.0.0.0 0.0.0.255
#
traffic classifier c1 operator or precedence 5
if-match acl 3001
#
traffic behavior b1
permit
#
traffic policy p1 match-order config
classifier c1 behavior b1
#
interface Vlanif10
ip address 10.0.0.1 255.255.255.0
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 10
#
interface GigabitEthernet0/0/2
traffic-policy p1 outbound
#
return
-
ACC的配置文件
#
sysname ACC
#
vlan batch 10
#
user-bind static ip-address 10.0.0.2 mac-address 0002-0002-0002 interface GigabitEthernet0/0/1
user-bind static ip-address 10.0.0.5 mac-address 0005-0005-0005 interface GigabitEthernet0/0/2
#
interface GigabitEthernet0/0/1
port link-type access
port default vlan 10
ip source check user-bind enable
#
interface GigabitEthernet0/0/2
port link-type access
port default vlan 10
ip source check user-bind enable
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 10
#
return

END
微思网络,始于2002年
专业IT认证培训22年,面向全国招生!
微思-主要课程有:
*网络技术:华为HCIA/ HCIP/HCIE;思科CCNA/CCNP/CCIE
*Linux技术:红帽 RHCE/RHCA
*K8S&容器:CKA/CKS
*数据库:ORACLE OCP/ OCM ;MySQL ;达梦数据库
*虚拟化:VMware VCP/VCAP
*安全认证:CISP体系/CISSP/ CISA;CCSK;CISAW体系
*管理类:PMP 项目管理;软考中/高项;ITIL体系;Togaf
其他课程如:ACP;Azure...
— 年度热文 —






















 2630
2630

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








