六.暴力破解密码
目前的登陆和修改密码,没有错误次数的限制。
Solution: 是否可以加入新的逻辑:单位时间内输入错误次数大于一个数值时,改账号会被冻结。可以由改company的admin 解冻 或者发送申请到 sunnet后由sunnet公司解冻。
1.web.config里加链接字段:
- <configuration>
- <connectionStrings >
- <add name="myConnectionString"
- connectionString="Server=10.231.248.177;Database=testdb;User ID=sa;Password=pa$$word;Trusted_Connection=False;"
- providerName="System.Data.SqlClient"/>
- </connectionStrings>
2.拖几个控件在form里:
- <form id="form1" runat="server">
- <asp:Label ID="LU" runat="server" Text="User Name:"></asp:Label>
- <asp:TextBox ID="TBU" runat="server"></asp:TextBox>
- <br/>
- <asp:Label ID="LP" runat="server" Text="Password:"></asp:Label>
- <asp:TextBox ID="TBP" runat="server"></asp:TextBox>
- <br/>
- <asp:Button ID="Login" runat="server" Text="Login" OnClick="Login_Click" />
- <div>
3.写登录事件:
- protected void Login_Click(object sender, EventArgs e)
- {
- using(SqlConnection con = new SqlConnection(WebConfigurationManager.ConnectionStrings["myConnectionString"].ConnectionString))
- {
- con.Open();
- SqlCommand cmd = new SqlCommand();
- cmd.CommandText = "SELECT Count(1) FROM [User] where UserName='" + TBU.Text.Trim() + "' and Password='" + TBP.Text.Trim() + "'";
- cmd.CommandType = CommandType.Text;
- cmd.Connection = con;
- int count =(int) cmd.ExecuteScalar();
- Response.Write(cmd.CommandText);
- if (count > 0)
- {
- Response.Write("<script>alert('Login pass!');</script>");
- }
- else
- {
- Response.Write("<script>alert('Login fail!');</script>");
- }
- }
- }
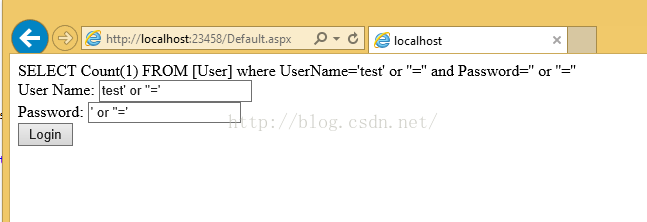
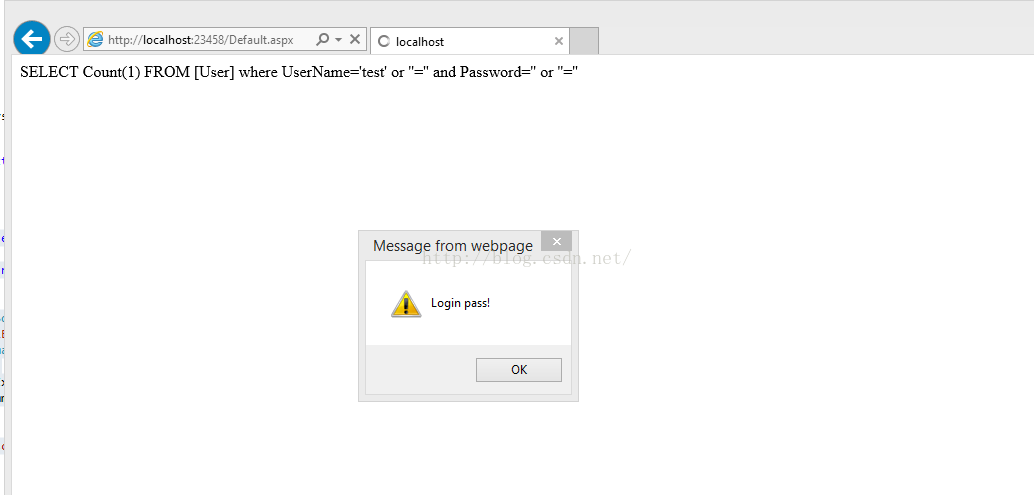
4.构造SQL注入登录:
用户名输入:test' or ''='
密码输入:' or ''='
或者
用户名输入:test
密码输入:' or ''='
如图:
其他ASP.net SQL注入的例子,如果有兴趣可以参考下:
http://www.codeproject.com/Articles/459324/Understading-SQL-Injection-and-Creating-SQL-Inject






















 133
133

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








