目标 利用spring security实现与自定义 openid的对接
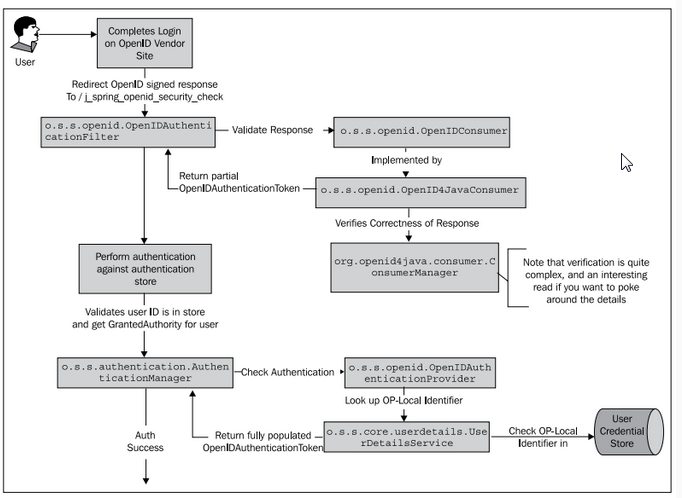
大概说一些spring security的账户验证的流程(太细的地方我也不清楚)
1. 对未登陆的用户会被AuthenticationProcessingFilter拦截进行处理,这里主要是读取用户的信息(如果是密码登陆就是在这里获取账号(username)和密码(password),如果是openid就可以在这里让用户跳转到openid service)
2. 在Filter中会生成用户的验证的信息Authentication
3. 然后有会有一个providerManager负责管理改filer所需provider,然后循环调用provider的authenticate方法进行用户,对于每一个provider都有一个对应的userDetailsService进行校验(对于密码和账号就在这里验证,对于openid前面在filter中就有一个标志来表示openid验证情况)
4. 然后成功就会调用登陆成功的handle,失败调用失败的handle
其中 vilidate respoense到 openIDConsumer是我们可以自己定义的openid的验证方式,还有userDetails也是可以我们自定义
<http>
...
<!--首先在http标签里面注释掉原来的登陆拦截器,然后在这里加入自定义的openidfilter-->
<custom-filter ref="openidLoginFilter" after="PRE_AUTH_FILTER"/>
...
</http>
<!--自定义的拦截器,然后自定义登陆成功与失败的Handle和自定义的provider-->
<beans:bean id="openidLoginFilter"
class="com.netease.urs.monitor.filter.MySpecialAuthenticationFilter">
<beans:property name="authenticationManager" ref="authenticationManager"/>
<beans:property name="authenticationSuccessHandler"
ref="authenticationSuccessHandler"/>
<







 本文介绍了如何使用Spring Security实现与自定义OpenID的对接。通过AuthenticationProcessingFilter拦截未登录用户,根据不同的验证方式(如密码或OpenID)进行用户认证。详细讲述了OpenID验证流程,包括自定义OpenID过滤器、OpenID验证响应处理和用户详情服务,以实现权限管理。
本文介绍了如何使用Spring Security实现与自定义OpenID的对接。通过AuthenticationProcessingFilter拦截未登录用户,根据不同的验证方式(如密码或OpenID)进行用户认证。详细讲述了OpenID验证流程,包括自定义OpenID过滤器、OpenID验证响应处理和用户详情服务,以实现权限管理。
 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 5万+
5万+

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








