接着上一篇文章SpringSecurity:自定义Form表单中的项目:spring-security-form,继续演示开启CSRF防护的场景(当时关闭了CSRF:.csrf().disable())。
依赖不变,核心依赖为Web,SpringSecurity与Thymeleaf:
<dependencies>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-web</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-thymeleaf</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-security</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-devtools</artifactId>
<scope>runtime</scope>
<optional>true</optional>
</dependency>
<dependency>
<groupId>org.projectlombok</groupId>
<artifactId>lombok</artifactId>
<optional>true</optional>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-test</artifactId>
<scope>test</scope>
</dependency>
</dependencies>
从官网中可以知道,CSRF防护的关键在于我们发请求时附带一个随机数(CSRF token),而这个随机数不会被浏览器自动携带(eg: Cookie就会被浏览器自动带上)。 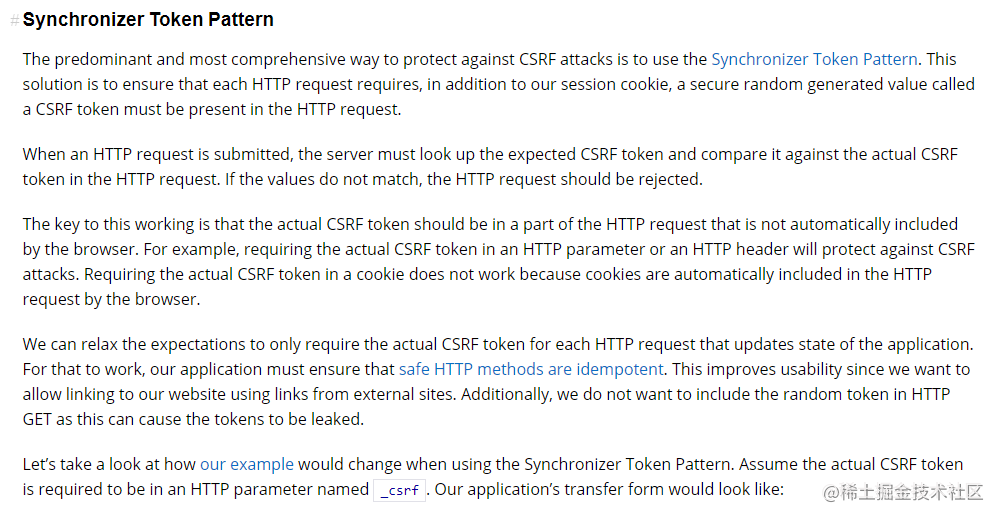
实验0:登录时的CSRF防护
显然,我们这里的登录请求是个POST方法(SpringSecurity默认忽略"GET", “HEAD”, “TRACE”, "OPTIONS"等幂等请求的CSRF拦截)。登录时必须携带_csrf参数,与认证信息一并提交,否则报403。
- 后端安全配置(默认开启
CSRF)
@Override
protected void configure(HttpSecurity http) throws Exception {
http.authorizeRequests()
.antMatchers("/user/add").hasAuthority("p1")
.antMatchers("/user/query").hasAuthority("p2")
.antMatchers("/user/**").authenticated()
.anyRequest().permitAll() // Let other request pass
.and()
// .csrf().disable() // turn off csrf, or will be 403 forbidden
.formLogin() // Support form and HTTPBasic
.l







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 1740
1740











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








