总结
互联网大厂比较喜欢的人才特点:对技术有热情,强硬的技术基础实力;主动,善于团队协作,善于总结思考。无论是哪家公司,都很重视高并发高可用技术,重视基础,所以千万别小看任何知识。面试是一个双向选择的过程,不要抱着畏惧的心态去面试,不利于自己的发挥。同时看中的应该不止薪资,还要看你是不是真的喜欢这家公司,是不是能真的得到锻炼。其实我写了这么多,只是我自己的总结,并不一定适用于所有人,相信经过一些面试,大家都会有这些感触。
**另外本人还整理收藏了2021年多家公司面试知识点以及各种技术点整理 **
下面有部分截图希望能对大家有所帮助。

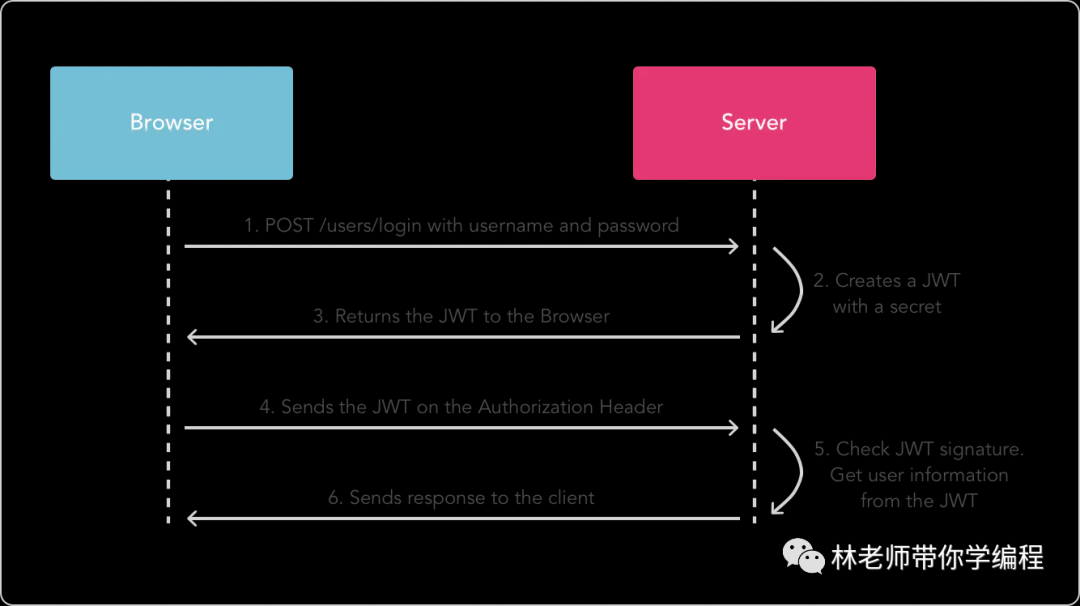
注意:secret是保存在服务器端的,jwt的签发生成也是在服务器端的,secret就是用来进行jwt的签发和jwt的验证,所以,它就是你服务端的私钥,在任何场景都不应该流露出去。一旦客户端得知这个secret, 那就意味着客户端是可以自我签发jwt了。
二、案例demo
JWT的概念讲完了,接下来就给大家详细的介绍一下代码的具体实现,客户端和服务器调用的流程,可以参照下面过程:
引入JWT和Spring Security依赖
org.springframework.boot
spring-boot-starter-security
io.jsonwebtoken
jjwt
0.9.1
添加Web配置文件,我们需要将除了登陆授权以外的接口,都进行过滤拦截,校验Token的合法性。
@Configuration
@EnableWebSecurity
@EnableGlobalMethodSecurity(prePostEnabled = true)
public class WebSecurityConfig extends WebSecurityConfigurerAdapter {
@Autowired
private UserDetailsService userDetailsService;
@Autowired
public void configureAuthentication(AuthenticationManagerBuilder authenticationManagerBuilder) throws Exception {
authenticationManagerBuilder
// 设置UserDetailsService
.userDetailsService(userDetailsService)
// 使用BCrypt进行密码的hash
.passwordEncoder(passwordEncoder());
}
// 装载BCrypt密码编码器
@Bean
public PasswordEncoder passwordEncoder() {
return new BCryptPasswordEncoder();
}
@Bean
public JwtAuthenticationTokenFilter authenticationTokenFilterBean() throws Exception {
return new JwtAuthenticationTokenFilter();
}
@Override
protected void configure(AuthenticationManagerBuilder auth) throws Exception {
auth.userDetailsService(userDetailsService);
}
@Bean
@Override
public AuthenticationManager authenticationManagerBean() throws Exception {
return super.authenticationManagerBean();
}
@Override
protected void configure(HttpSecurity httpSecurity) throws Exception {
httpSecurity
// 由于使用的是JWT,我们这里不需要csrf
.csrf().disable()
// 基于token,所以不需要session
.sessionManagement().sessionCreationPolicy(SessionCreationPolicy.STATELESS).and()
.authorizeRequests()
.antMatchers(HttpMethod.OPTIONS, “/**”).permitAll()
// 允许对于网站静态资源的无授权访问
.antMatchers(
HttpMethod.GET,
“/”,
“/*.html”,
“/favicon.ico”,
“/**/*.html”,
“/**/*.css”,
“/**/*.js”
).permitAll()
// 授权接口放通token校验
.antMatchers(“/authority/**/authorization/”).permitAll()
// 除上面外的所有请求全部需要鉴权认证
.anyRequest().authenticated();
// 添加JWT filter
httpSecurity.addFilterBefore(authenticationTokenFilterBean(), UsernamePasswordAuthenticationFilter.class);
// 禁用缓存
httpSecurity.headers().cacheControl();
}
}
Web配置文件中我们可以看到,还需要UserDetailsService和JwtAuthenticationTokenFilter。UserDetailsService是Spring Security内部接口,我们需要实现该接口的loadUserByUsername方法,将查询到username和password返回,具体代码如下所示:
@Slf4j
@Service
public class UserDetailServiceImpl implements UserDetailsService {
@Autowired
private TamadbUserMapper userMapper;
@Override
public UserDetails loadUserByUsername(String userName) throws UsernameNotFoundException {
TamadbUser userPo = userMapper.getUserBaseInfo(Integer.valueOf(userName));
if (userPo == null) {
log.error(“loadUserByUsername—>userName:{}不存在”, userName);
throw new UsernameNotFoundException(“用户名不存在”);
}
SysUserPo user = new SysUserPo();
user.setUsername(userPo.getId() + “”);
user.setPassword(userPo.getPassword());
BCryptPasswordEncoder encoder = new BCryptPasswordEncoder();
final String rawPassword = user.getPassword();
user.setPassword(encoder.encode(rawPassword));
return user;
}
}
userMapper.getUserBaseInfo方法就是一个dao,用来查询数据库的用户信息,因为WebSecurityConfig配置文件,对密码配置了BCryptPasswordEncoder加密,但是数据库存储的是md5生成的密码,所以我们需要对密码进行等价加密。
我们接着来看一下JwtAuthenticationTokenFilter过滤器的内容:
@Component
@Log4j2
public class JwtAuthenticationTokenFilter extends OncePerRequestFilter {
@Autowired(required = false)
private UserDetailsService userDetailsService;
@Value(“${jwt.header}”)
private String header;
@Value(“${jwt.tokenHead}”)
private String tokenHead;
@Autowired
private JwtTokenUtil jwtTokenUtil;
@Override
protected void doFilterInternal(
HttpServletRequest request, HttpServletResponse response,
FilterChain chain) throws ServletException, IOException {
String authHeader = request.getHeader(this.header);
if (authHeader != null && authHeader.startsWith(tokenHead) && authHeader.length() > tokenHead.length() + 1) {
// The part after "Bearer "
final String authToken = authHeader.substring(tokenHead.length() + 1);
String username = jwtTokenUtil.getUsernameFromToken(authToken);
log.info(“checking authentication,username:{},authToken:{}”, username, authToken);
// 校验token是否有效合法
if (username != null && SecurityContextHolder.getContext().getAuthentication() == null) {
UserDetails userDetails = this.userDetailsService.loadUserByUsername(username);
// 校验token是否过期
if (jwtTokenUtil.validateToken(authToken, userDetails)) {
UsernamePasswordAuthenticationToken authentication = new UsernamePasswordAuthenticationToken(
userDetails, null, userDetails.getAuthorities());
authentication.setDetails(new WebAuthenticationDetailsSource().buildDetails(
request));
log.info("authenticated user " + username + “, setting security context”);
SecurityContextHolder.getContext().setAuthentication(authentication);
} else {
log.error(“token过期,token:{}”, authToken);
}
} else {
log.error(“token失效,无法获取到用户信息,token:{}”, authHeader);
}
}
chain.doFilter(request, response);
}
}
过滤器就做一件事情,获取Http头部的Token信息,然后通过jwtTokenUtil解密Token,获取用户信息,最后检验Token是否过期。
我们最后来看看jwtTokenUtil工具类中,是如何生成、解密Token的。
@Component
@Log4j2
public class JwtTokenUtil implements Serializable {
private static final long serialVersionUID = -3301605591108950415L;
/**
- 用户id
*/
private static final String CLAIM_KEY_USERNAME = “sub”;
/**
- 用户登录信息
*/
private static final String AUTHORITY_USER_DETAIL = “detail”;
/**
- token创建时间
*/
private static final String CLAIM_KEY_CREATED = “created”;
@Value(“${jwt.secret}”)
private String secret;
@Value(“${jwt.expiration.pc.access}”)
private Long pcAccessExpiration;
@Value(“${jwt.expiration.pc.refresh}”)
private Long pcRefreshExpiration;
@Value(“${jwt.expiration.wechat.access}”)
private Long weChatAccessExpiration;
@Value(“${jwt.expiration.wechat.refresh}”)
private Long weChatRefreshExpiration;
/**
-
获取用户token
-
@param token
-
@return
*/
public String getUsernameFromToken(String token) {
String username;
try {
final Claims claims = getClaimsFromToken(token);
username = claims.getSubject();
} catch (Exception e) {
username = null;
}
return username;
}
/**
-
获取用户token
-
@param token
-
@return
*/
public AuthorityUserDto getUserDetailFromToken(String token) {
AuthorityUserDto detail;
try {
final Claims claims = getClaimsFromToken(token);
Object detailObject = claims.get(AUTHORITY_USER_DETAIL);
Gson gson = new Gson();
// 解析json
detail = gson.fromJson(gson.toJson(detailObject), AuthorityUserDto.class);
} catch (Exception e) {
detail = null;
}
return detail;
}
/**
-
获取token的创建时间
-
@param token
-
@return
*/
public Date getCreatedDateFromToken(String token) {
Date created;
try {
final Claims claims = getClaimsFromToken(token);
created = new Date((Long) claims.get(CLAIM_KEY_CREATED));
} catch (Exception e) {
created = null;
}
return created;
}
/**
-
获取token的过期时间
-
@param token
-
@return
*/
public Date getExpirationDateFromToken(String token) {
Date expiration;
try {
final Claims claims = getClaimsFromToken(token);
expiration = claims.getExpiration();
} catch (Exception e) {
expiration = null;
}
return expiration;
}
/**
-
调用jar生成token令牌
-
@param token
-
@return
*/
private Claims getClaimsFromToken(String token) {
Claims claims;
try {
claims = Jwts.parser()
.setSigningKey(secret)
.parseClaimsJws(token)
.getBody();
} catch (Exception e) {
log.error(“解析token是失败:错误信息:{}”, com.fourkmiles.common.util.ExceptionUtil.formatException(e));
claims = null;
}
return claims;
}
/**
-
生成过期时间
-
@param tokenExpirationDto
-
@return
*/
private Date generateExpirationDate(TokenExpirationDto tokenExpirationDto) {
Date expirationDate = null;
ChannelEnum channelEnum = tokenExpirationDto.getChannelEnum();
TokenEnum tokenEnum = tokenExpirationDto.getTokenEnum();
if (channelEnum.getType() == ChannelEnum.PC_CHANNEL.getType()) {
if (tokenEnum.getType() == TokenEnum.ACCESS_TOKEN.getType()) {
expirationDate = new Date(System.currentTimeMillis() + pcAccessExpiration * 1000);
} else {
expirationDate = new Date(System.currentTimeMillis() + pcRefreshExpiration * 1000);
}
} else {
if (tokenEnum.getType() == TokenEnum.ACCESS_TOKEN.getType()) {
expirationDate = new Date(System.currentTimeMillis() + weChatAccessExpiration * 1000);
} else {
expirationDate = new Date(System.currentTimeMillis() + weChatRefreshExpiration * 1000);
}
}
return expirationDate;
}
/**
-
校验token是否过期
-
@param token
-
@return
*/
private Boolean isTokenExpired(String token) {
final Date expiration = getExpirationDateFromToken(token);
return expiration.before(new Date());
}
/**
-
生成token
读者福利
分享一份自己整理好的Java面试手册,还有一些面试题pdf
不要停下自己学习的脚步


m.currentTimeMillis() + weChatRefreshExpiration * 1000);
}
}
return expirationDate;
}
/**
-
校验token是否过期
-
@param token
-
@return
*/
private Boolean isTokenExpired(String token) {
final Date expiration = getExpirationDateFromToken(token);
return expiration.before(new Date());
}
/**
-
生成token
读者福利
分享一份自己整理好的Java面试手册,还有一些面试题pdf
不要停下自己学习的脚步
[外链图片转存中…(img-ck1Q6hsu-1715299069747)]
[外链图片转存中…(img-WbftPTy6-1715299069748)]






















 1069
1069











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








