下载看到附件:
import libnum
from Crypto.Util import number
from secret import flag
size = 128
e = 65537
p = number.getPrime(size)
q = number.getPrime(size)
n = p*q
m = libnum.s2n(flag)
c = pow(m, e, n)
print('n = %d' % n)
print('c = %d' % c)n = 88503001447845031603457048661635807319447136634748350130947825183012205093541
c = 40876621398366534035989065383910105526025410999058860023908252093679681817257认识RSA:


简单分析:
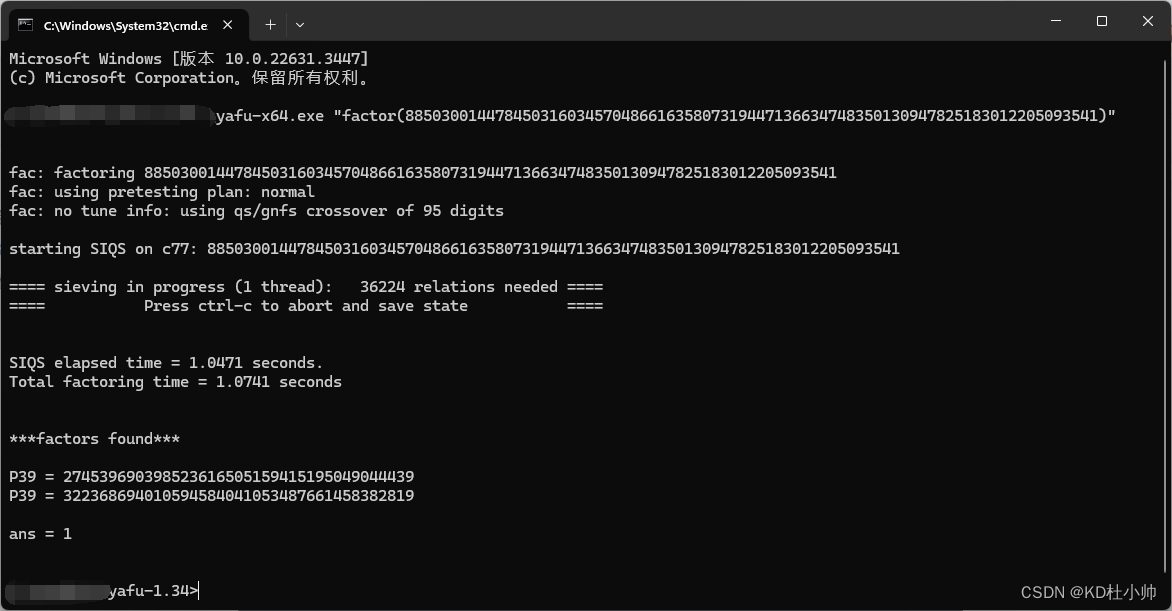
下载yafu:https://blog.csdn.net/CliffordR/article/details/82747087
yafu分解n:
exp:
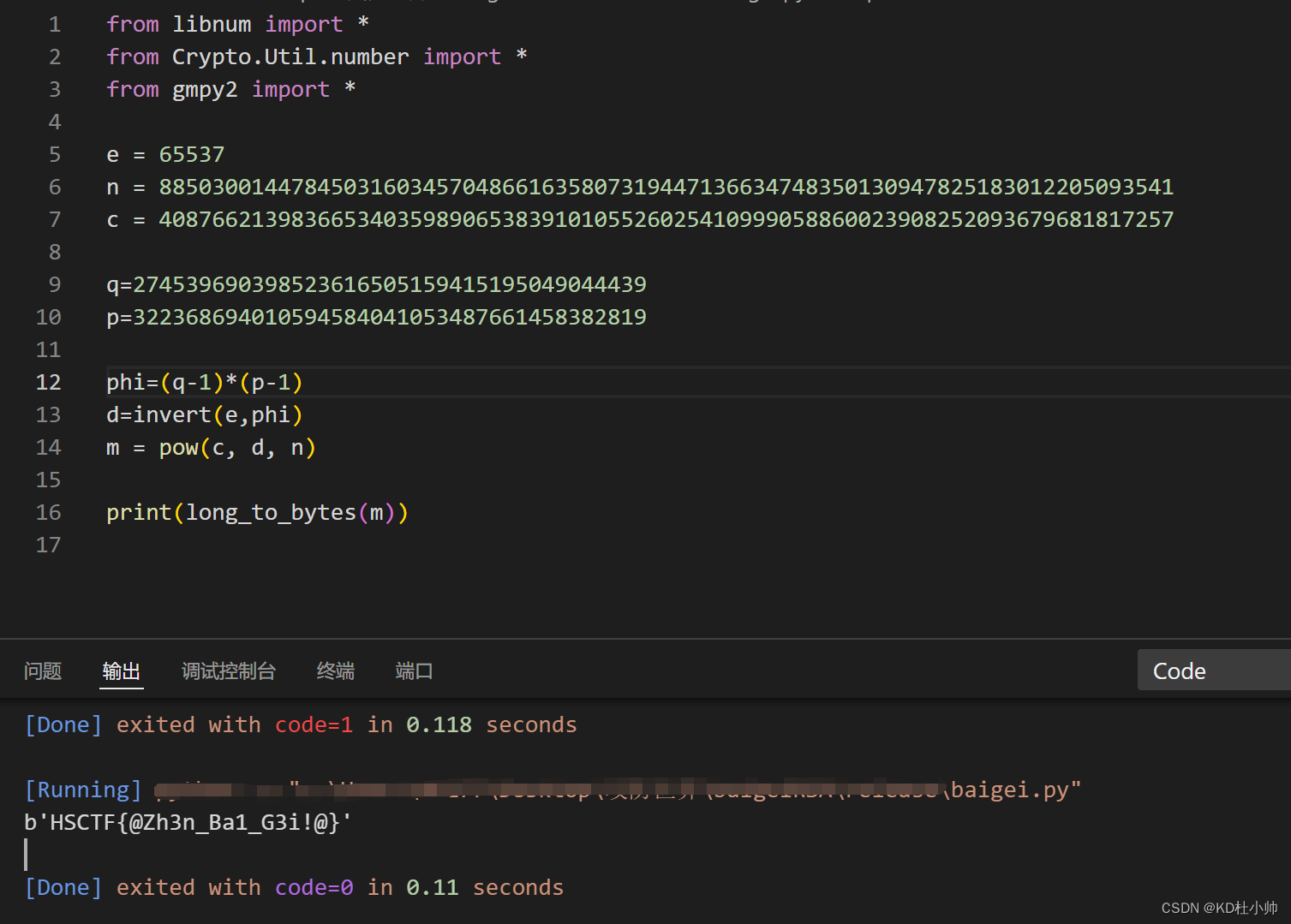
from libnum import *
from Crypto.Util.number import *
from gmpy2 import *
e = 65537
n = 88503001447845031603457048661635807319447136634748350130947825183012205093541
c = 40876621398366534035989065383910105526025410999058860023908252093679681817257
q=274539690398523616505159415195049044439
p=322368694010594584041053487661458382819
phi=(q-1)*(p-1)
d=invert(e,phi)
m = pow(c, d, n)
print(long_to_bytes(m))
flag:
HSCTF{@Zh3n_Ba1_G3i!@}





















 732
732











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








