exe,pyc文件转py
pip install uncompyle6
假设我们有一个名为test.exe的可执行文件,我们要将它反编译成Python脚本,可以使用以下命令:
uncompyle6 test.exe > test.py
其中,test.exe为可执行文件的名称,test.py为反编译后的Python脚本的文件名。反编译完成后,我们就可以打开test.py文件,查看可执行文件的源代码。
以下是一个Python脚本的源代码:
print("Hello, World!")
我们可以将其编译为可执行文件,然后再将其反编译成Python脚本。以Windows系统为例,编译命令如下:
pyinstaller -F test.py
反编译命令如下:
uncompyle6 dist/test.exe > test_decompile.py
反编译生成的Python脚本代码如下:
# uncompyle6 version 3.7.4
# Python bytecode 3.7 (3394)
# Decompiled from: Python 3.7.9 (default, Aug 31 2020, 17:10:11)
# [MSC v.1916 64 bit (AMD64)]
# Embedded file name: c:/Users/lily/Desktop/python_proj/test/dist/test.exe
# Compiled at: 2021-10-14 10:16:02
# Size of source mod 2**32: 20 bytes
print('Hello, World!')
可以看到,反编译生成的Python脚本与原始脚本完全一致。
但是不是所有的都适用
eg:[NISACTF 2022]ezpython
这是我第一次写到python的反编译题,所以我会比较详细的写一下这道题的具体流程和工具的简单使用 方法
工具:
1.pyinstxtractor.py
下载地址:https://sourceforge.net/projects/pyinstallerextractor/
2.HEX编辑器,我这里使用winHEX
下载地址:https://www.jb51.net/softs/16546.html#download
- uncompyle 库
可在命令框中输入:pip install uncompyle6 进行安装
介绍完工具,我们开始做题
本题是一个python写的且编译为exe格式的文件,我们想要查看他的源码,我们就需要想办法把exe反编 译成py文件
1.反编译步骤
首先,我们先将 pyinstxtractor.py 工具与我们要反编译的 .exe 文件放入同一个工作目录下:
然后在当前目录打开终端,输入 python pyinstxtractor.py 文件名.exe :并回车运行
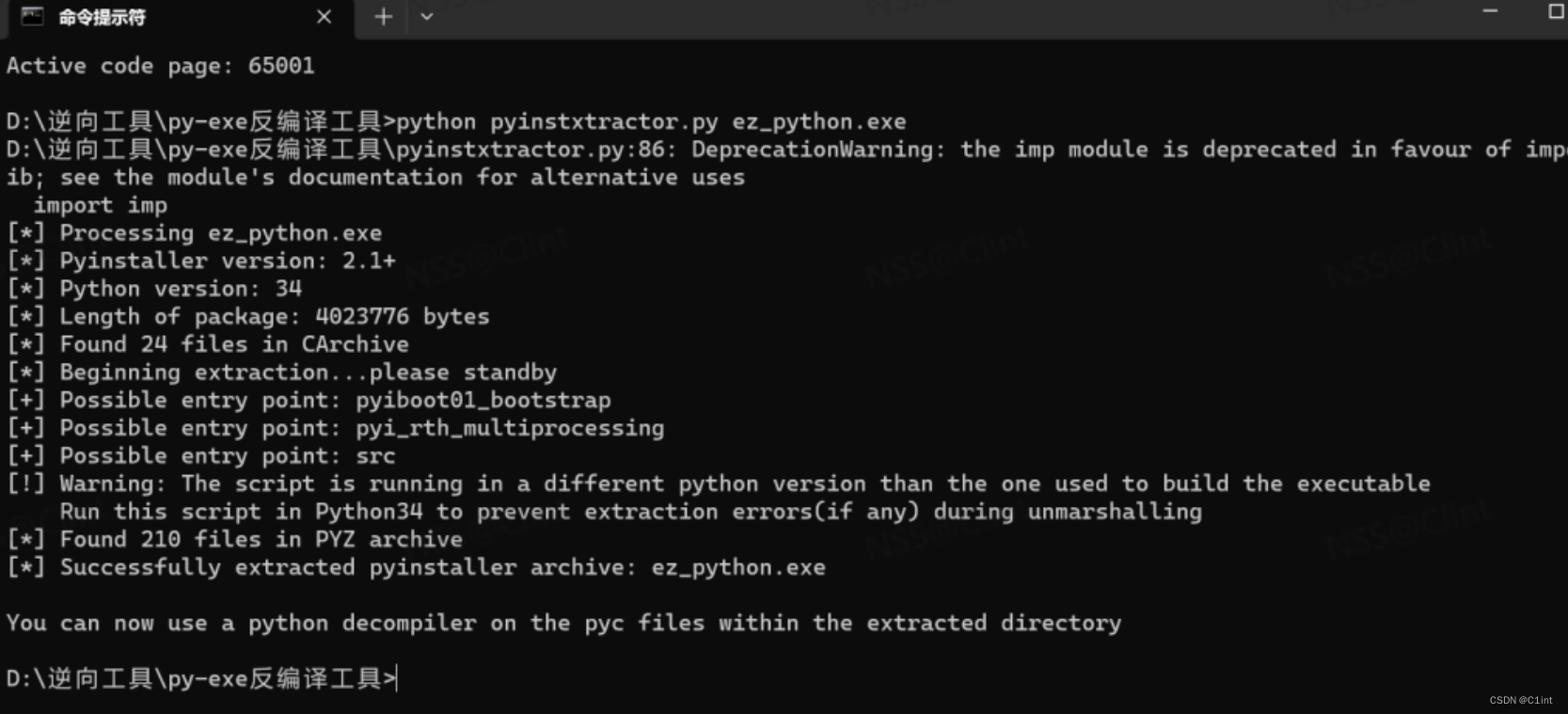
运行完成后,在此文件夹下我们会发现多了一个 文件名.exe_extracted 的文件夹
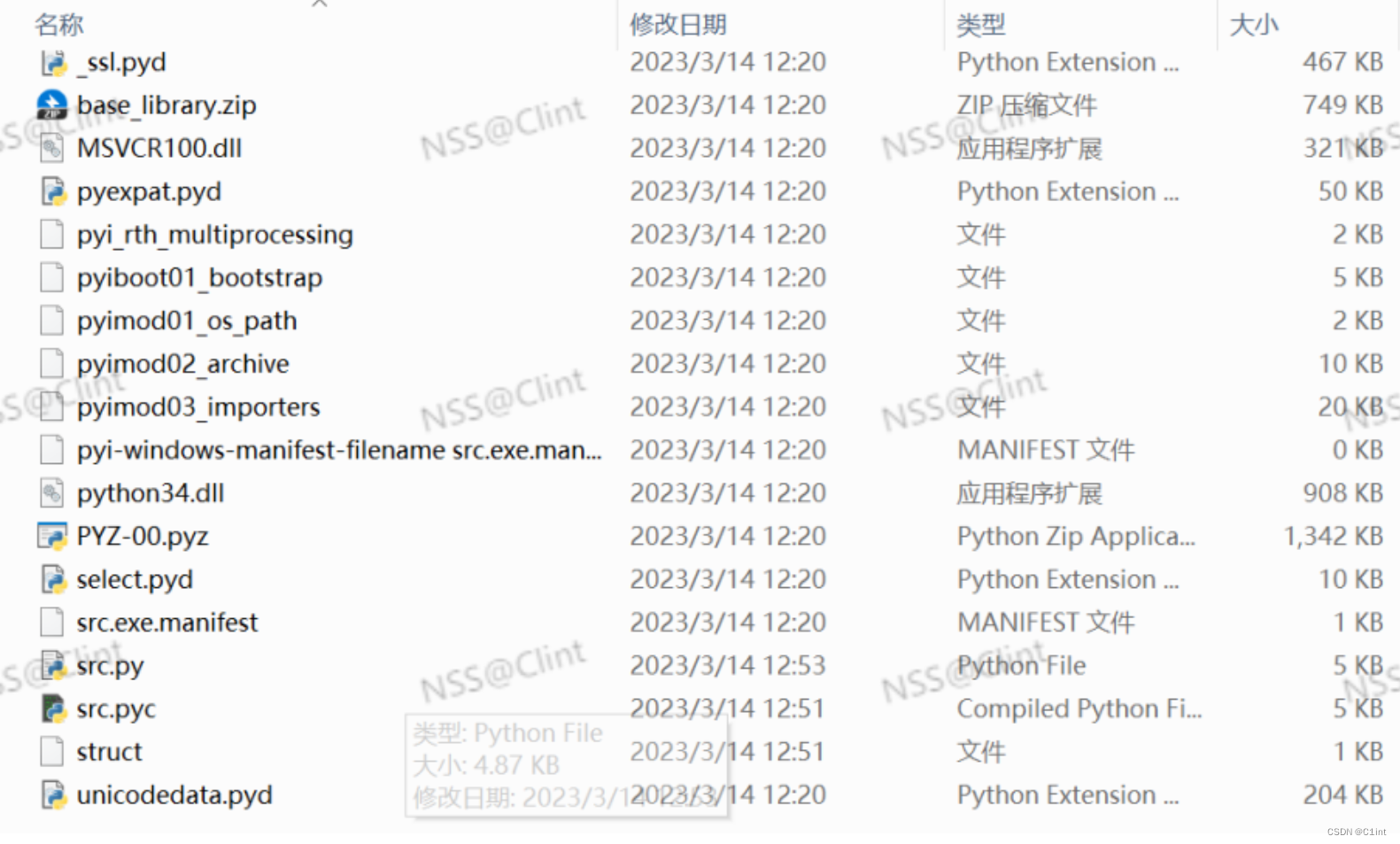
进入该文件夹,里面有许许多多后缀为 .dll 和 .pyd 的文件,还有一个名为 PYZ00.pyz_extracted 的文件夹,这个文件夹里放的是程序引入的依赖库,如果你引入过自己其他 的 .py 文件,就可以用类似的方法将依赖的 .py 文件反编译出来。
目录里种有两个没有后缀的文件,这就是我们反编译的重点

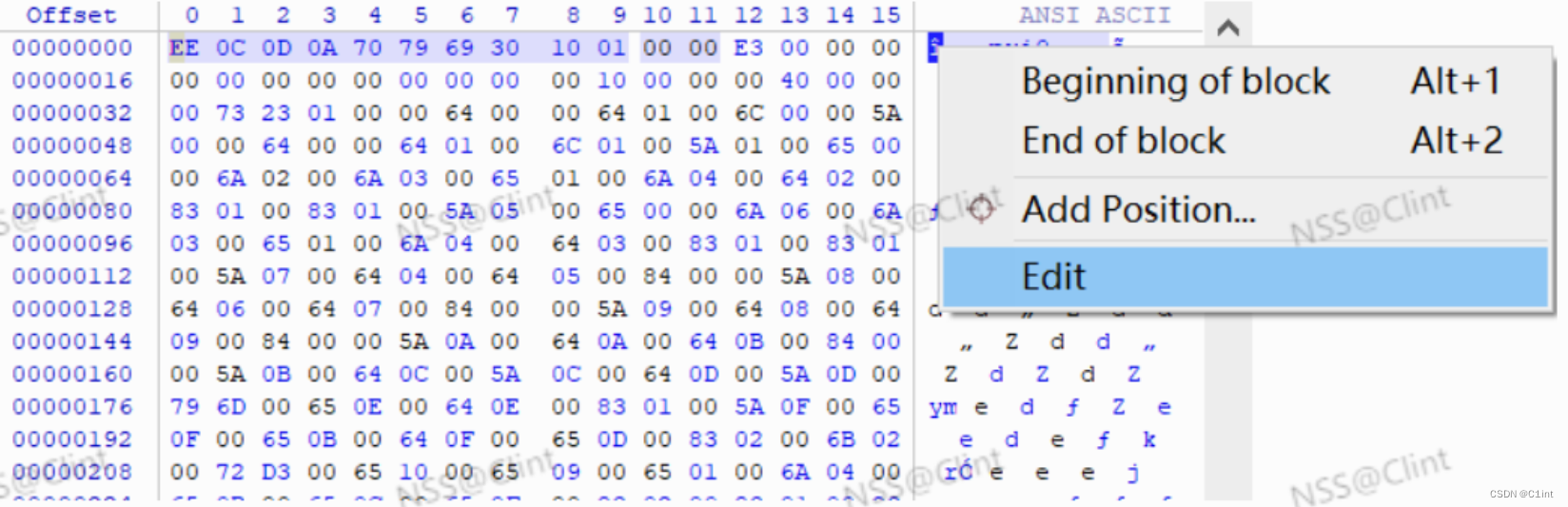
为src文件添加.pyc的后缀,并用HEX编辑器打开src和struct文件
由于某些我也不懂的原因,直接将src添加.pyc后缀后所编译的py文件是缺少Magic Number的,所以我 们要用struct文件的文件头来修复src文件的文件头
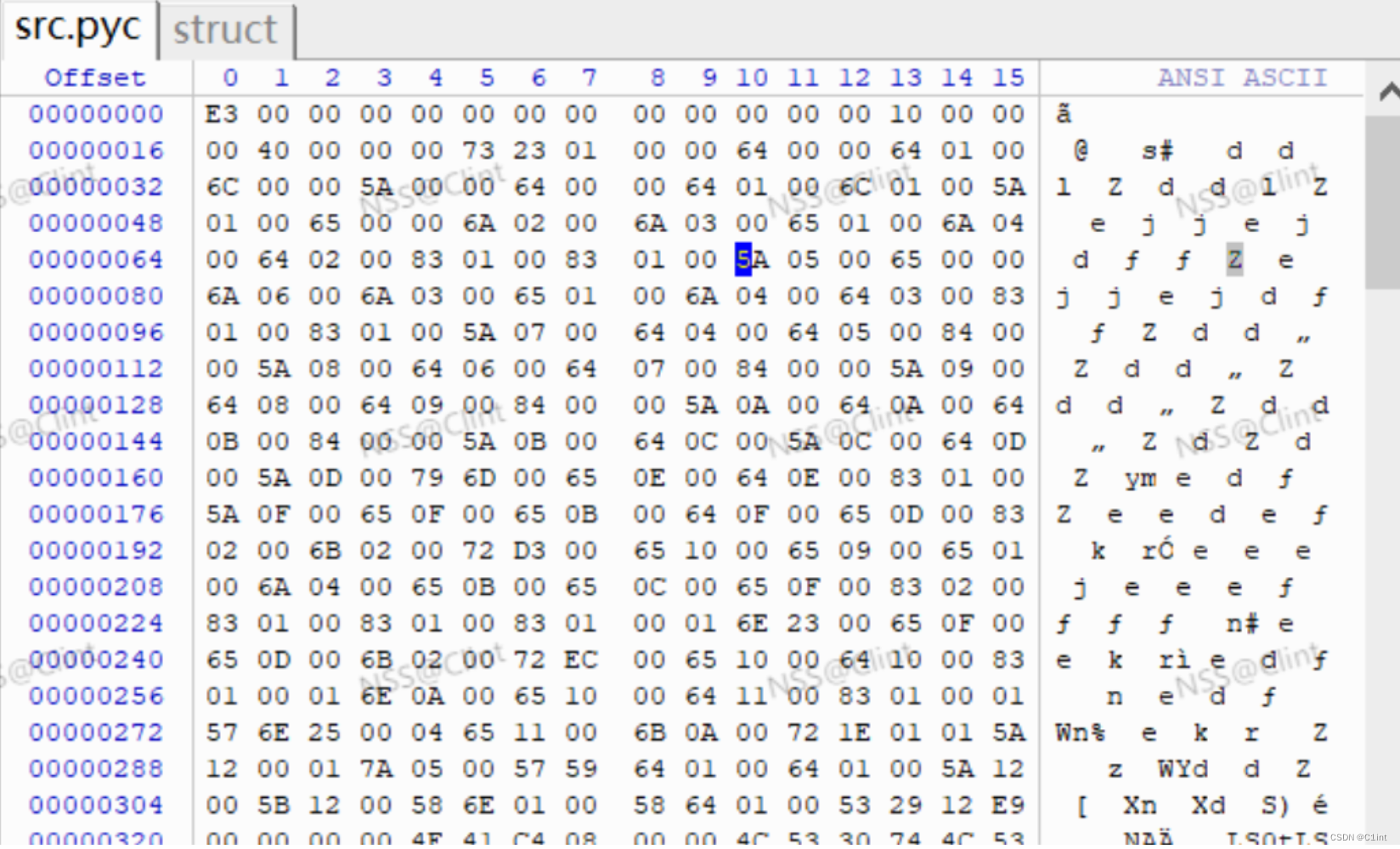
由于src文件直接是以E3开头的,所以我们这里直接将strcut文件E3前面的11字节复制到src文件的文件 头就可以了
如果不是直接以E3开头,就比较两个文件E3前面的字节,将src文件E3前面的字节改为struct文件 E3前面的字节即可
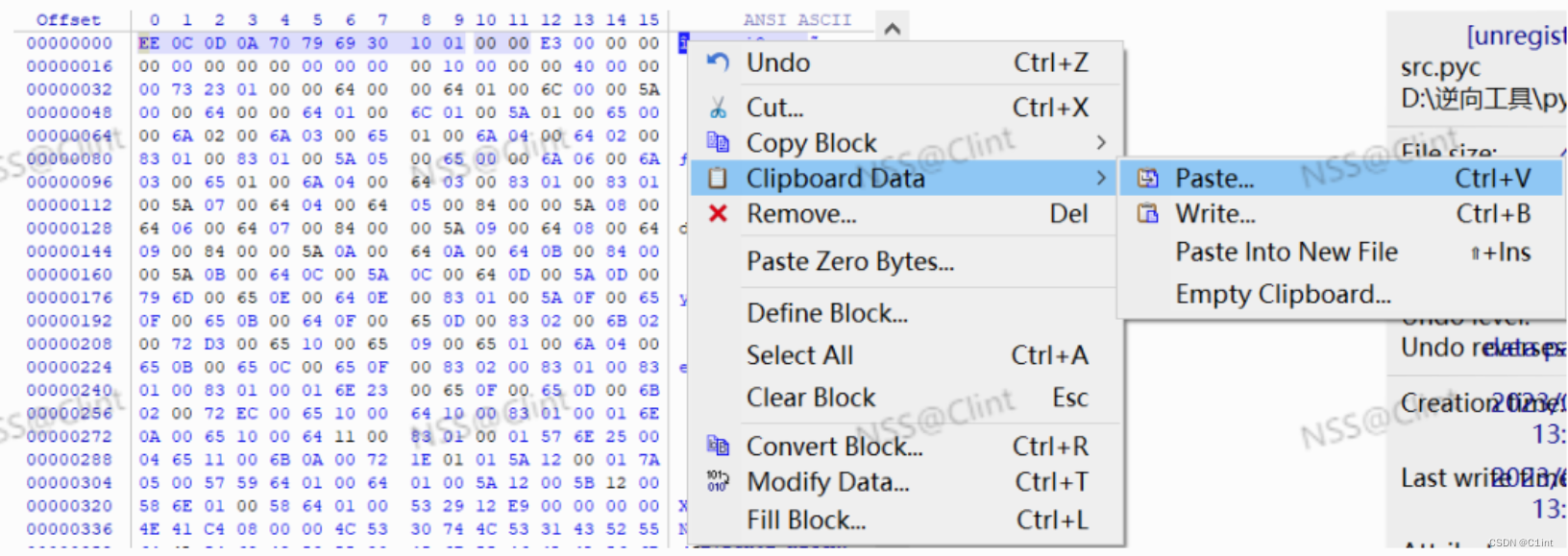
具体步骤:右键ANSI ASCII开头的字节,并点击Edit->Clipboard Data->Paste即可
这样我们的src文件就有Magic Number了
下面进行我们的最后一步,回到目录下,打开控制台,输入命令 uncompyle6 文件名.pyc > 文件名.py 回车执行,就可以看到目录下生成了 .py 文件了
# uncompyle6 version 3.9.0
# Python bytecode version base 3.4 (3310)
# Decompiled from: Python 3.8.0 (tags/v3.8.0:fa919fd, Oct 14 2019, 19:21:23) [MSC v.1916 32 bit (Intel)]
# Embedded file name: src.py
# Compiled at: 1995-09-28 00:18:56
# Size of source mod 2**32: 272 bytes
import rsa, base64
key1 = rsa.PrivateKey.load_pkcs1(base64.b64decode('LS0tLS1CRUdJTiBSU0EgUFJJVkFURSBLRVktLS0tLQpNSUlFcVFJQkFBS0NBUUVBcVJUZ0xQU3BuT0ZDQnJvNHR1K1FBWXFhTjI2Uk42TzY1bjBjUURGRy9vQ1NJSU00ClNBeEVWaytiZHpSN2FucVNtZ1l5MEhRWGhDZTM2U2VGZTF0ejlrd0taL3UzRUpvYzVBSzR1NXZ4UW5QOWY1cTYKYVFsbVAvVjJJTXB5NFFRNlBjbUVoNEtkNm81ZWRJUlB2SHd6V0dWS09OQ3BpL0taQ082V0tWYkpXcWh3WGpEQgpsSDFNVURzZ1gyVUM4b3Bodnk5dXIyek9kTlBocElJZHdIc1o5b0ZaWWtaMUx5Q0lRRXRZRmlKam1GUzJFQ1RVCkNvcU9acnQxaU5jNXVhZnFvZlB4eHlPb2wwYVVoVGhiaHE4cEpXL3FPSFdYd0xJbXdtNk96YXFVeks4NEYyY3UKYWRiRE5zeVNvaElHaHYzd0lBVThNSlFnOEthd1Z3ZHBzRWhlSXdJREFRQUJBb0lCQURBazdwUStjbEZtWHF1Vgp1UEoyRWxZdUJpMkVnVHNMbHZ0c1ltL3cyQnM5dHQ0bEh4QjgxYlNSNUYyMEJ2UlJ4STZ3OXlVZCtWZzdDd1lMCnA5bHhOL3JJdWluVHBkUEhYalNhaGNsOTVOdWNOWEZ4T0dVU05SZy9KNHk4dUt0VHpkV3NITjJORnJRa0o4Y2IKcWF5czNOM3RzWTJ0OUtrUndjbUJGUHNJalNNQzB5UkpQVEE4cmNqOFkranV3SHZjbUJPNHVFWXZXeXh0VHR2UQova0RQelBqdTBuakhkR055RytkSDdkeHVEV2Jxb3VZQnRMdzllZGxXdmIydTJ5YnZzTXl0NWZTOWF1a01NUjNoCnBhaDRMcU1LbC9ETTU3cE44Vms0ZTU3WE1zZUJLWm1hcEptcVNnSGdjajRPNWE2R1RvelN1TEVoTmVGY0l2Tm8KWFczTEFHRUNnWWtBc0J0WDNVcFQ3aUcveE5BZDdSWER2MENOY1k1QnNZOGY4NHQ3dGx0U2pjSWdBKy9nUjFMZQpzb2gxY1RRd1RadUYyRTJXL1hHU3orQmJDTVVySHNGWmh1bXV6aTBkbElNV3ZhU0dvSlV1OGpNODBlUjRiVTRyCmdYQnlLZVZqelkzNVlLejQ5TEVBcFRQcTZRYTVQbzhRYkF6czhuVjZtNXhOQkNPc0pQQ29zMGtCclFQaGo5M0cKOFFKNUFQWEpva0UrMmY3NXZlazZNMDdsaGlEUXR6LzRPYWRaZ1MvUVF0eWRLUmg2V3VEeGp3MytXeXc5ZjNUcAp5OXc0RmtLRzhqNVRpd1RzRmdzem94TGo5TmpSUWpqb3cyVFJGLzk3b2NxMGNwY1orMUtsZTI1cEJ3bk9yRDJBCkVpMUVkMGVEV3dJR2gzaFhGRmlRSzhTOG5remZkNGFMa1ZxK1V3S0JpRXRMSllIamFZY0N2dTd5M0JpbG1ZK0gKbGZIYkZKTkowaXRhazRZZi9XZkdlOUd6R1h6bEhYblBoZ2JrZlZKeEVBU3ZCOE5NYjZ5WkM5THdHY09JZnpLRApiczJQMUhuT29rWnF0WFNxMCt1UnBJdEkxNFJFUzYySDJnZTNuN2dlMzJSS0VCYnVKb3g3YWhBL1k2d3ZscUhiCjFPTEUvNnJRWk0xRVF6RjRBMmpENmdlREJVbHhWTUVDZVFDQjcyUmRoYktNL3M0TSsvMmYyZXI4Y2hwT01SV1oKaU5Hb3l6cHRrby9sSnRuZ1RSTkpYSXdxYVNCMldCcXpndHNSdEhGZnpaNlNyWlJCdTd5Y0FmS3dwSCtUd2tsNQpoS2hoSWFTNG1vaHhwUVNkL21td1JzbTN2NUNDdXEvaFNtNmNXYTdFOVZxc25heGQzV21tQ2VqTnp0MUxQWUZNCkxZMENnWWdKUHhpVTVraGs5cHB6TVAwdWU0clA0Z2YvTENldEdmQjlXMkIyQU03eW9VM2VsMWlCSEJqOEZ3UFQKQUhKUWtCeTNYZEh3SUpGTUV1RUZSSFFzcUFkSTlYVDBzL2V0QTg1Y3grQjhjUmt3bnFHakFseW1PdmJNOVNrMgptMnRwRi8rYm56ZVhNdFA3c0ZoR3NHOXJ5SEZ6UFNLY3NDSDhXWWx0Y1pTSlNDZHRTK21qblAwelArSjMKLS0tLS1FTkQgUlNBIFBSSVZBVEUgS0VZLS0tLS0K'))
key2 = rsa.PublicKey.load_pkcs1(base64.b64decode('LS0tLS1CRUdJTiBSU0EgUFVCTElDIEtFWS0tLS0tCk1JSUJDZ0tDQVFFQXFSVGdMUFNwbk9GQ0JybzR0dStRQVlxYU4yNlJONk82NW4wY1FERkcvb0NTSUlNNFNBeEUKVmsrYmR6UjdhbnFTbWdZeTBIUVhoQ2UzNlNlRmUxdHo5a3dLWi91M0VKb2M1QUs0dTV2eFFuUDlmNXE2YVFsbQpQL1YySU1weTRRUTZQY21FaDRLZDZvNWVkSVJQdkh3eldHVktPTkNwaS9LWkNPNldLVmJKV3Fod1hqREJsSDFNClVEc2dYMlVDOG9waHZ5OXVyMnpPZE5QaHBJSWR3SHNaOW9GWllrWjFMeUNJUUV0WUZpSmptRlMyRUNUVUNvcU8KWnJ0MWlOYzV1YWZxb2ZQeHh5T29sMGFVaFRoYmhxOHBKVy9xT0hXWHdMSW13bTZPemFxVXpLODRGMmN1YWRiRApOc3lTb2hJR2h2M3dJQVU4TUpRZzhLYXdWd2Rwc0VoZUl3SURBUUFCCi0tLS0tRU5EIFJTQSBQVUJMSUMgS0VZLS0tLS0K'))
def encrypt1(message):
crypto_text = rsa.encrypt(message.encode(), key2)
return crypto_text
def decrypt1(message):
message_str = rsa.decrypt(message, key1).decode()
return message_str
def encrypt2(tips, key):
ltips = len(tips)
lkey = len(key)
secret = []
num = 0
for each in tips:
if num >= lkey:
num = num % lkey
secret.append(chr(ord(each) ^ ord(key[num])))
num += 1
return base64.b64encode(''.join(secret).encode()).decode()
def decrypt2(secret, key):
tips = base64.b64decode(secret.encode()).decode()
ltips = len(tips)
lkey = len(key)
secret = []
num = 0
for each in tips:
if num >= lkey:
num = num % lkey
secret.append(chr(ord(each) ^ ord(key[num])))
num += 1
return ''.join(secret)
flag = 'IAMrG1EOPkM5NRI1cChQDxEcGDZMURptPzgHJHUiN0ASDgUYUB4LGQMUGAtLCQcJJywcFmddNno/PBtQbiMWNxsGLiFuLwpiFlkyP084Ng0lKj8GUBMXcwEXPTJrRDMdNwMiHVkCBFklHgIAWQwgCz8YQhp6E1xUHgUELxMtSh0xXzxBEisbUyYGOx1DBBZWPg1CXFkvJEcxO0ADeBwzChIOQkdwXQRpQCJHCQsaFE4CIjMDcwswTBw4BS9mLVMLLDs8HVgeQkscGBEBFSpQFQQgPTVRAUpvHyAiV1oPE0kyADpDbF8AbyErBjNkPh9PHiY7O1ZaGBADMB0PEVwdCxI+MCcXARZiPhwfH1IfKitGOF42FV8FTxwqPzBPAVUUOAEKAHEEP2QZGjQVV1oIS0QBJgBDLx1jEAsWKGk5Nw03MVgmWSE4Qy5LEghoHDY+OQ9dXE44Th0='
key = 'this is key'
try:
result = input('please input key: ')
if result == decrypt2('AAAAAAAAAAAfFwwRSAIWWQ==', key):
print(decrypt1(base64.b64decode(decrypt2(flag, result))))
else:
if result == key:
print('flag{0e26d898-b454-43de-9c87-eb3d122186bc}')
else:
print('key is error.')
except Exception as e:
pass
# okay decompiling src.pyc
脚本:
flag =
'IAMrG1EOPkM5NRI1cChQDxEcGDZMURptPzgHJHUiN0ASDgUYUB4LGQMUGAtLCQcJJywcFmddNno/PBt
QbiMWNxsGLiFuLwpiFlkyP084Ng0lKj8GUBMXcwEXPTJrRDMdNwMiHVkCBFklHgIAWQwgCz8YQhp6E1x
UHgUELxMtSh0xXzxBEisbUyYGOx1DBBZWPg1CXFkvJEcxO0ADeBwzChIOQkdwXQRpQCJHCQsaFE4CIjM
DcwswTBw4BS9mLVMLLDs8HVgeQkscGBEBFSpQFQQgPTVRAUpvHyAiV1oPE0kyADpDbF8AbyErBjNkPh9
PHiY7O1ZaGBADMB0PEVwdCxI+MCcXARZiPhwfH1IfKitGOF42FV8FTxwqPzBPAVUUOAEKAHEEP2QZGjQ
VV1oIS0QBJgBDLx1jEAsWKGk5Nw03MVgmWSE4Qy5LEghoHDY+OQ9dXE44Th0='
key = 'this is key'
result = decrypt2('AAAAAAAAAAAfFwwRSAIWWQ==', key)
print(decrypt1(base64.b64decode(decrypt2(flag, result))))
#flag{5236cb7d-f4a7-4080-9bde-8b9e061609ad
oHDY+OQ9dXE44Th0=’
key = ‘this is key’
result = decrypt2(‘AAAAAAAAAAAfFwwRSAIWWQ==’, key)
print(decrypt1(base64.b64decode(decrypt2(flag, result))))
#flag{5236cb7d-f4a7-4080-9bde-8b9e061609ad





















 3006
3006











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








