printf("\n");
}
int main()
{
printf(“\ncase1:==============================\n”);
// case 1//
const uint8_t key[16] = {0x2b, 0x7e, 0x15, 0x16, 0x28, 0xae, 0xd2, 0xa6, 0xab, 0xf7, 0x15, 0x88, 0x09, 0xcf, 0x4f, 0x3c};
const uint8_t pt[16] = {0x32, 0x43, 0xf6, 0xa8, 0x88, 0x5a, 0x30, 0x8d, 0x31, 0x31, 0x98, 0xa2, 0xe0, 0x37, 0x07, 0x34};
uint8_t ct[16] = {0}; // 外部申请输出数据内存,用于加密后的数据
uint8_t plain[16] = {0}; // 外部申请输出数据内存,用于解密后的数据
aesEncrypt(key, 16, pt, ct, 16); // 加密
printHex((uint8_t *)pt, 16, "plain data:"); // 打印初始明文数据
printf("expect cipher:\n39 25 84 1D 02 DC 09 FB DC 11 85 97 19 6A 0B 32\n"); // 正常解密后的数据内容
printHex(ct, 16, "after encryption:"); // 打印加密后的密文
aesDecrypt(key, 16, ct, plain, 16); // 解密
printHex(plain, 16, "after decryption:"); // 打印解密后的明文数据
printf("\ncase2:==============================\n");
// case 2
// 16字节字符串形式秘钥
const uint8_t key2[] = "1234567890123456";
// 32字节长度字符串明文
const uint8_t *data = (uint8_t *)"abcdefghijklmnopqrstuvwxyz123456";
uint8_t ct2[32] = {0}; // 外部申请输出数据内存,用于存放加密后数据
uint8_t plain2[32] = {0}; // 外部申请输出数据内存,用于存放解密后数据
// 加密32字节明文
aesEncrypt(key2, 16, data, ct2, 32);
printf("\nplain text:\n%s\n", data);
printf("expect ciphertext:\nfcad715bd73b5cb0488f840f3bad7889\n");
printHex(ct2, 32, "after encryption:");
// 解密32字节密文
aesDecrypt(key2, 16, ct2, plain2, 32);
// 打印16进制形式的解密后的明文
printHex(plain2, 32, "after decryption:");
// 因为加密前的数据为可见字符的字符串,打印解密后的明文字符,与加密前明文进行对比
printf("output plain text:\n");
for (int i = 0; i < 32; ++i)
{
printf("%c", plain2[i]);
}
return 0;
}
---
### Tea
明文:2个32位无符号整数,即8字节
密钥:4个32位无符号整数
密文:2个32位无符号整数,即8字节
#### tea\_C++实现
#include <stdio.h>
#include <stdint.h>
// 加密函数
void encrypt(uint32_t *v, uint32_t *k)
{
uint32_t v0 = v[0], v1 = v[1], sum = 0, i;
uint32_t delta = 0x9e3779b9;
uint32_t k0 = k[0], k1 = k[1], k2 = k[2], k3 = k[3];
for (i = 0; i < 32; i++)
{
sum += delta;
v0 += ((v1 << 4) + k0) ^ (v1 + sum) ^ ((v1 >> 5) + k1);
v1 += ((v0 << 4) + k2) ^ (v0 + sum) ^ ((v0 >> 5) + k3);
}
v[0] = v0;
v[1] = v1;
}
// 解密函数
void decrypt(uint32_t *v, uint32_t *k)
{
uint32_t v0 = v[0], v1 = v[1], sum = 0xC6EF3720, i;
uint32_t delta = 0x9e3779b9;
uint32_t k0 = k[0], k1 = k[1], k2 = k[2], k3 = k[3];
for (i = 0; i < 32; i++)
{
v1 -= ((v0 << 4) + k2) ^ (v0 + sum) ^ ((v0 >> 5) + k3);
v0 -= ((v1 << 4) + k0) ^ (v1 + sum) ^ ((v1 >> 5) + k1);
sum -= delta;
}
v[0] = v0;
v[1] = v1;
}
int main()
{
// v为要加解密的数据,两个32位无符号整数
uint32_t v[2] = {0x0F141297,0x985A36E8};
// k为加解密密钥,4个32位无符号整数,密钥长度为128位
uint32_t k[4] = {0x636c6557,0x5f656d6f,0x48575f32,0x46544355};
/*
s2[0] = 0x7CC261B30BFA9228LL;
s2[1] = 0xA1F3B16FD0860834LL;
s2[2] = 0xA95B1A3E11FB4D32LL;
s2[3] = 0x985A36E80F141297LL;
*/
// c = [0x7CC261B3,0x0BFA9228, 0xA1F3B16F,0xD0860834, 0xA95B1A3E ,0x11FB4D32, 0x985A36E8 ,0x0F141297]
// key = [0x57656C63,0x6F6D655F,0x325F5748,0x55435446]
// encrypt(v7, "Welcome\_2\_WHUCTF");要每四个字母倒过来转换成16进制,然后密文也要符合小端模式。
int n = sizeof(v) / sizeof(uint32\_t);
printf("加密前原始数据:0x%x 0x%x\n", v[0], v[1]);
//encrypt(v, k);
printf("加密后的数据:0x%x 0x%x\n", v[0], v[1]);
decrypt(v, k);
printf("解密后的数据:0x%x 0x%x\n", v[0], v[1]);
for (int i = 0; i < n; i++)
{
for (int j = 0; j < sizeof(uint32\_t) / sizeof(uint8\_t); j++)
{
printf("%c", (v[i] >> (j \* 8)) & 0xFF);
}
}
printf("\n");
return 0;
//whuctf{You\_Wanna\_Haave\_A\_Drink?}
}
#### tea\_Pathon实现
from ctypes import *
def encrypt(v, k):
v0, v1 = c_uint32(v[0]), c_uint32(v[1])
delta = 0x9e3779b9
k0, k1, k2, k3 = k[0], k[1], k[2], k[3]
total = c_uint32(0)
for i in range(32):
total.value += delta
v0.value += ((v1.value<<4) + k0) ^ (v1.value + total.value) ^ ((v1.value>>5) + k1)
v1.value += ((v0.value<<4) + k2) ^ (v0.value + total.value) ^ ((v0.value>>5) + k3)
return v0.value, v1.value
def decrypt(v, k):
v0, v1 = c_uint32(v[0]), c_uint32(v[1])
delta = 0x9e3779b9
k0, k1, k2, k3 = k[0], k[1], k[2], k[3]
total = c_uint32(delta \* 32)
for i in range(32):
v1.value -= ((v0.value<<4) + k2) ^ (v0.value + total.value) ^ ((v0.value>>5) + k3)
v0.value -= ((v1.value<<4) + k0) ^ (v1.value + total.value) ^ ((v1.value>>5) + k1)
total.value -= delta
return v0.value, v1.value
test
if name == “__main__”:
# 待加密的明文,两个32位整型,即64bit的明文数据
value = [0x12345678, 0x78563412]
# 四个key,每个是32bit,即密钥长度为128bit
key = [0x1, 0x2, 0x3, 0x4]
print("Data is : ", hex(value[0]), hex(value[1]))
res = encrypt(value, key)
print("Encrypted data is : ", hex(res[0]), hex(res[1]))
res = decrypt(res, key)
print("Decrypted data is : ", hex(res[0]), hex(res[1]))
“”"
Data is : 0x12345678 0x78563412
Encrypted data is : 0x9a65a69a 0x67ed00f6
Decrypted data is : 0x12345678 0x78563412
“”"
#### xtea
from ctypes import *
def encrypt(v, key):
v0, v1 = c_uint32(v[0]), c_uint32(v[1])
delta = 0x9E3779B9
total = c_uint32(0)
for i in range(32):
v0.value += (((v1.value << 4) ^ (v1.value >> 5)) + v1.value) ^ (total.value + key[total.value & 3])
total.value += delta
v1.value += (((v0.value << 4) ^ (v0.value >> 5)) + v0.value) ^ (total.value + key[(total.value>>11) & 3])
return v0.value, v1.value
def decrypt(v, key):
v0, v1 = c_uint32(v[0]), c_uint32(v[1])
delta = 0x9E3779B9
total = c_uint32(delta \* 32)
for i in range(32):
v1.value -= (((v0.value << 4) ^ (v0.value >> 5)) + v0.value) ^ (total.value + key[(total.value>>11) & 3])
total.value -= delta
v0.value -= (((v1.value << 4) ^ (v1.value >> 5)) + v1.value) ^ (total.value + key[total.value & 3])
return v0.value, v1.value
test
if name == “__main__”:
# 待加密的明文,两个32位整型,即64bit的明文数据
value = [0x12345678, 0x78563412]
# 四个key,每个是32bit,即密钥长度为128bit
key = [0x1, 0x2, 0x3, 0x4]
print("Data is : ", hex(value[0]), hex(value[1]))
res = encrypt(value, key)
print("Encrypted data is : ", hex(res[0]), hex(res[1]))
res = decrypt(res, key)
print("Decrypted data is : ", hex(res[0]), hex(res[1]))
“”"
Data is : 0x12345678 0x78563412
Encrypted data is : 0xae685ec7 0x59af4238
Decrypted data is : 0x12345678 0x78563412
“”"
#### xxtea
from ctypes import *
def MX(z, y, total, key, p, e):
temp1 = (z.value>>5 ^ y.value<<2) + (y.value>>3 ^ z.value<<4)
temp2 = (total.value ^ y.value) + (key[(p&3) ^ e.value] ^ z.value)
return c_uint32(temp1 ^ temp2)
def encrypt(n, v, key):
delta = 0x9e3779b9
rounds = 6 + 52//n
total = c_uint32(0)
z = c_uint32(v[n-1])
e = c_uint32(0)
while rounds > 0:
total.value += delta
e.value = (total.value >> 2) & 3
for p in range(n-1):
y = c_uint32(v[p+1])
v[p] = c_uint32(v[p] + MX(z,y,total,key,p,e).value).value
z.value = v[p]
y = c_uint32(v[0])
v[n-1] = c_uint32(v[n-1] + MX(z,y,total,key,n-1,e).value).value
z.value = v[n-1]
rounds -= 1
return v
def decrypt(n, v, key):
delta = 0x9e3779b9
rounds = 6 + 52//n
total = c_uint32(rounds \* delta)
y = c_uint32(v[0])
e = c_uint32(0)
while rounds > 0:
e.value = (total.value >> 2) & 3
for p in range(n-1, 0, -1):
z = c_uint32(v[p-1])
v[p] = c_uint32((v[p] - MX(z,y,total,key,p,e).value)).value
y.value = v[p]
z = c_uint32(v[n-1])
v[0] = c_uint32(v[0] - MX(z,y,total,key,0,e).value).value
y.value = v[0]
total.value -= delta
rounds -= 1
return v
test
if name == “__main__”:
# 该算法中每次可加密不只64bit的数据,并且加密的轮数由加密数据长度决定
v = [0x12345678, 0x78563412]
k = [0x1, 0x2, 0x3, 0x4]
n = 2
print("Data is : ", hex(v[0]), hex(v[1]))
res = encrypt(n, v, k)
print("Encrypted data is : ", hex(res[0]), hex(res[1]))
res = decrypt(n, res, k)
print("Decrypted data is : ", hex(res[0]), hex(res[1]))
“”"
Data is : 0x12345678 0x78563412
Encrypted data is : 0xef86c2bb 0x25f31b5e
Decrypted data is : 0x12345678 0x78563412
“”"
---
### RSA
import rsa
生成RSA密钥对
public_key, private_key = rsa.newkeys(2048)
要加密的数据
message = b"Hello, RSA!"
使用RSA公钥加密数据
encrypted_data = rsa.encrypt(message, public_key)
使用RSA私钥解密数据
decrypted_data = rsa.decrypt(encrypted_data, private_key)
print(“解密后的数据:”, decrypted_data)
---
### Z3
网上一搜就道的例子,易于理解,但re题不会这么容易。
from z3 import *
#整数求解
a, s, d = Ints(‘a s d’)
x = Solver()
x.add(a-d == 18)
x.add(a+s == 12)
x.add(s-d == 20)
check = x.check()
print(check)
model = x.model()
print(model)
sat
[a = 5, d = -13, s = 7]
from z3 import *
#有理数(Real)型解方程求解
x = Real(‘x’)
y = Real(‘y’)
s = Solver()
s.add(x**2 + y**2 == 3)
s.add(x**3 == 2)
check = s.check()
print(check)
model = s.model()
print(model)
sat
[y = -1.1885280594?, x = 1.2599210498?]
from z3 import *
#位向量(BitVec)型解方程
x, y, z = BitVecs(‘x y z’, 8)
s = Solver()
s.add(x ^ y & z == 12)
s.add(y & z >> 3 == 3)
s.add(z ^ y == 4)
check = s.check()
print(check)
model = s.model()
print(model)
sat
[z = 27, y = 31, x = 23]
你会发现,当你做RE题时,这三个样例远远不够。我们需要更优秀顺滑的操作!!!,给你几个示例吧
input = [BitVec(‘input[%d]’ % i, 16) for i in range(42)] # 这样好处是可以直接把结果复制粘粘出来成为代码再组织输出,有效解决了flag错序顺序情况
values = [Int(‘v[%d]’ % i) for i in range(16)]
还可以将多个语句之间的等值关系加入进去,下例是矩阵乘法用z3运算。
from z3 import *
flag矩阵*key矩阵得到enc矩阵
现在反求flag矩阵
key = [0, -2, -1, 4, 1,
-1, 1, 0, 0, -1,
-3, -2, 0, -10, -1,
-1, -2, 1, -13, -1,
-6, -1, -2, 1, -2,]
enc = [0x76, 0x74, 0xf5, 0x2f, 0x53,
0x48, 0x74, 0x45, 0xa4, 0x5f,
0xfc, 0x63, 0x1, 0xd0, 0xf8,
0xaa, 0x79, 0x46, 0x11, 0x7e,
0x1d, 0x91, 0x7e, 0x8e, 0xca]
flag = [Int(‘flag[%d]’ % i) for i in range(25)] # 定义flag矩阵
s = Solver() # 创建一个求解器
print(flag) # 输出flag矩阵样貌
for i in range(25):
s.add(flag[i] < 0xff)
s.add(flag[i] >= 0)
for i in range(5):
for j in range(5):
v12 = 0
for k in range(5):
v8 = (v12 + key[5 * i + k] * flag[5 * k + j]) % 256 # 矩阵乘法
v12 = v8
s.add(v8 == enc[i * 5 + j]) # 加入求解器中
print(‘calculating…’)
if (s.check() == sat): # 判断结果为sat,表示有解
print(s.model())
else:
print(‘no’)
kkk=s.model()
for i in s.model():
print(i, end=‘’)
灵活使用!!!才是绝技
v20=[BitVec(‘v20[%d]’%i,16) for i in range(25)]
v22=[v21[25-i-1] for i in range(25)]
v23=[0 for i in range(25)]
s1=Solver()
for i in range(25):
s1.add(v20[i]>=0)
s1.add(v20[i]<=0xff)
#s1.add(v20[i]==v21[25-i-1])
v23[24] = (v20[24] + v20[13] + v20[14] + 3)&0xff
v23[23] = (v20[11] ^ v20[10]) + v20[23]&0xff
v23[22] = (v20[22] + (v20[10] + v20[9]))&0xff
v23[21] = ((v20[7] ^ 0x17) + v20[21])&0xff
v23[20] = (v20[20] + (v20[4] + (v20[15] - 5)))&0xff
v23[19] = (v20[19] + v20[3] - v20[1])&0xff
v23[18] = (v20[18] + (v20[16] + v20[17]))&0xff
v23[17] = (v20[17] + (v20[1] - v20[4] + 17))&0xff
v23[16] = (v20[16] + (v20[5] ^ (v20[6] + 1)))&0xff
v23[15] = ((v20[7] + v20[15]) - v20[8])&0xff
v23[14] = (v20[14] + (v20[10] + v20[9]))&0xff
v23[13] = (v20[12] + (v20[11] + (v20[13] - 7)))&0xff
v23[12] = (v20[12] + v23[13])&0xff
v23[11] = (v20[11] + (v23[17] ^ v23[16]))&0xff
v23[10] = (v23[19] + (v23[20] + (v20[10] + 12)))&0xff
v23[9] = (v23[21] + (v20[9] + 8))&0xff
v23[8] = ((v23[22] ^ 0x4D) + v20[8])&0xff
v23[7] = (v20[7] + (2 * (v23[23] & 0xF9 ^ 0x11) + (v23[23] ^ 0xEE)))&0xff
v23[6] = ((v23[7] ^ v23[9]) + v20[6])&0xff
v23[5] = (v23[12] + (v23[10] + v20[5]))&0xff
v23[4] = (v20[4] + v23[13])&0xff
v23[3] = (v23[16] + (v20[3] + v23[18]))&0xff
v23[2] = (v23[19] + v20[2])&0xff
v23[1] = ((v23[24] ^ v23[22]) + v20[1])&0xff
v23[0] = (v20[0] + (v23[23] + 24))&0xff
for i in range(25):
s1.add(v23[i]==v22[i])
if s1.check()==sat:
print(s1.model())
else:
print(‘no’)
### ECC
出现极少,暂不说明。
---
### DES
DES算法特点:
是一种对称分组加密算法。
分组比较短,最大64位。
密钥太短。DES密钥长度是56bit,从规格上来说,DES的密钥长度是64bit,但由于每隔7bit会设置一个错误检查的bit,因此实质上其密钥长度是56bit。
密码生命周期短。
运算速度较慢。
常见的对称加密: AES, DES, 3DES。
from Crypto.Cipher import DES
key = b’abcdefgh’ # 密钥 8位或16位,必须为bytes
def pad(text):
# 如果text不是8的倍数【加密文本text必须为8的倍数!】,补足为8的倍数
while len(text) % 8 != 0:
text += ’ ’
return text
des = DES.new(key, DES.MODE_ECB) # 创建DES实例
text = ‘Python rocks!’
padded_text = pad(text)
encrypted_text = des.encrypt(padded_text.encode(‘utf-8’)) # 加密
print(encrypted_text)
b’>\xfc\x1f\x16x\x87\xb2\x93\x0e\xfcH\x02\xd59VQ’
plain_text = des.decrypt(encrypted_text).decode().rstrip(’ ') # 解密
print(plain_text)
Python rocks!
YYYYiJceGQ3Q1JceGI0XHgxMFx4MWJceGU1XHhiMlZceDE1XHgxZEZJXHhkMFx4OTg8XHhlNlx4ZDd4OVx4ZTdceGY2R1x4MTJceGZiXHg4OVx4ZTFceGNiXHg5OC5ceGRjdFx4MDZceGVkdU96XHhkNFx4OTBceDExXHhkMDQnXHhhNFx0TnEkXHhmZXtceDlhXHhjOVx4YjJceDA4XHhjNDYiYYY
---
### CRC32
**循环冗余校验(CRC)是用于检测数据损坏的错误检测码。**发送数据时,会根据数据内容生成简短的校验和,并将其与数据一起发送。接收数据时,将再次生成校验和并将其与发送的校验和进行比较。如果两者相等,则没有数据损坏。所述**CRC-32算法**本身**转换可变长度字符串转换成8个字符的字符串**。
以下是加密函数:
#include <stdio.h>
#include <string.h>
static const unsigned int crc32tab[] = {
0x00000000, 0x77073096, 0xee0e612c, 0x990951ba, 0x076dc419, 0x706af48f, 0xe963a535, 0x9e6495a3,
0x0edb8832, 0x79dcb8a4, 0xe0d5e91e, 0x97d2d988, 0x09b64c2b, 0x7eb17cbd, 0xe7b82d07, 0x90bf1d91,
0x1db71064, 0x6ab020f2, 0xf3b97148, 0x84be41de, 0x1adad47d, 0x6ddde4eb, 0xf4d4b551, 0x83d385c7,
0x136c9856, 0x646ba8c0, 0xfd62f97a, 0x8a65c9ec, 0x14015c4f, 0x63066cd9, 0xfa0f3d63, 0x8d080df5,
0x3b6e20c8, 0x4c69105e, 0xd56041e4, 0xa2677172, 0x3c03e4d1, 0x4b04d447, 0xd20d85fd, 0xa50ab56b,
0x35b5a8fa, 0x42b2986c, 0xdbbbc9d6, 0xacbcf940, 0x32d86ce3, 0x45df5c75, 0xdcd60dcf, 0xabd13d59,
0x26d930ac, 0x51de003a, 0xc8d75180, 0xbfd06116, 0x21b4f4b5, 0x56b3c423, 0xcfba9599, 0xb8bda50f,
0x2802b89e, 0x5f058808, 0xc60cd9b2, 0xb10be924, 0x2f6f7c87, 0x58684c11, 0xc1611dab, 0xb6662d3d,
0x76dc4190, 0x01db7106, 0x98d220bc, 0xefd5102a, 0x71b18589, 0x06b6b51f, 0x9fbfe4a5, 0xe8b8d433,
0x7807c9a2, 0x0f00f934, 0x9609a88e, 0xe10e9818, 0x7f6a0dbb, 0x086d3d2d, 0x91646c97, 0xe6635c01,
0x6b6b51f4, 0x1c6c6162, 0x856530d8, 0xf262004e, 0x6c0695ed, 0x1b01a57b, 0x8208f4c1, 0xf50fc457,
0x65b0d9c6, 0x12b7e950, 0x8bbeb8ea, 0xfcb9887c, 0x62dd1ddf, 0x15da2d49, 0x8cd37cf3, 0xfbd44c65,
0x4db26158, 0x3ab551ce, 0xa3bc0074, 0xd4bb30e2, 0x4adfa541, 0x3dd895d7, 0xa4d1c46d, 0xd3d6f4fb,
0x4369e96a, 0x346ed9fc, 0xad678846, 0xda60b8d0, 0x44042d73, 0x33031de5, 0xaa0a4c5f, 0xdd0d7cc9,
0x5005713c, 0x270241aa, 0xbe0b1010, 0xc90c2086, 0x5768b525, 0x206f85b3, 0xb966d409, 0xce61e49f,
0x5edef90e, 0x29d9c998, 0xb0d09822, 0xc7d7a8b4, 0x59b33d17, 0x2eb40d81, 0xb7bd5c3b, 0xc0ba6cad,
0xedb88320, 0x9abfb3b6, 0x03b6e20c, 0x74b1d29a, 0xead54739, 0x9dd277af, 0x04db2615, 0x73dc1683,
0xe3630b12, 0x94643b84, 0x0d6d6a3e, 0x7a6a5aa8, 0xe40ecf0b, 0x9309ff9d, 0x0a00ae27, 0x7d079eb1,
0xf00f9344, 0x8708a3d2, 0x1e01f268, 0x6906c2fe, 0xf762575d, 0x806567cb, 0x196c3671, 0x6e6b06e7,
0xfed41b76, 0x89d32be0, 0x10da7a5a, 0x67dd4acc, 0xf9b9df6f, 0x8ebeeff9, 0x17b7be43, 0x60b08ed5,
0xd6d6a3e8, 0xa1d1937e, 0x38d8c2c4, 0x4fdff252, 0xd1bb67f1, 0xa6bc5767, 0x3fb506dd, 0x48b2364b,
0xd80d2bda, 0xaf0a1b4c, 0x36034af6, 0x41047a60, 0xdf60efc3, 0xa867df55, 0x316e8eef, 0x4669be79,
0xcb61b38c, 0xbc66831a, 0x256fd2a0, 0x5268e236, 0xcc0c7795, 0xbb0b4703, 0x220216b9, 0x5505262f,
0xc5ba3bbe, 0xb2bd0b28, 0x2bb45a92, 0x5cb36a04, 0xc2d7ffa7, 0xb5d0cf31, 0x2cd99e8b, 0x5bdeae1d,
0x9b64c2b0, 0xec63f226, 0x756aa39c, 0x026d930a, 0x9c0906a9, 0xeb0e363f, 0x72076785, 0x05005713,
0x95bf4a82, 0xe2b87a14, 0x7bb12bae, 0x0cb61b38, 0x92d28e9b, 0xe5d5be0d, 0x7cdcefb7, 0x0bdbdf21,
0x86d3d2d4, 0xf1d4e242, 0x68ddb3f8, 0x1fda836e, 0x81be16cd, 0xf6b9265b, 0x6fb077e1, 0x18b74777,
0x88085ae6, 0xff0f6a70, 0x66063bca, 0x11010b5c, 0x8f659eff, 0xf862ae69, 0x616bffd3, 0x166ccf45,
0xa00ae278, 0xd70dd2ee, 0x4e048354, 0x3903b3c2, 0xa7672661, 0xd06016f7, 0x4969474d, 0x3e6e77db,
0xaed16a4a, 0xd9d65adc, 0x40df0b66, 0x37d83bf0, 0xa9bcae53, 0xdebb9ec5, 0x47b2cf7f, 0x30b5ffe9,
0xbdbdf21c, 0xcabac28a, 0x53b39330, 0x24b4a3a6, 0xbad03605, 0xcdd70693, 0x54de5729, 0x23d967bf,
0xb3667a2e, 0xc4614ab8, 0x5d681b02, 0x2a6f2b94, 0xb40bbe37, 0xc30c8ea1, 0x5a05df1b, 0x2d02ef8d};
static unsigned int crc32(const unsigned char *buf, unsigned int size)
{
unsigned int i, crc;
crc = 0xFFFFFFFF;
for (i = 0; i < size; i++)
crc = crc32tab[(crc ^ buf[i]) & 0xff] ^ (crc >> 8);
return crc ^ 0xFFFFFFFF;
}
int main()
{
char *plaintext = “flag{3F6BC006-BA9F-DCE6-388A-0E338613E029}”;
printf(“0x%x”, crc32(plaintext + 5, strlen(plaintext) - 6));
}
---
### 16<->str
在写python脚本时,往往会使用很多数据类型转换,Crypto.Util.number是最为常见的好工具。
总结:16进制->整数->字节码->decode(“UTF-8”)->字符串
字符串->字节码->整数->16进制
‘’‘16进制转字符串’‘’
from Crypto.Util.number import *
c = 0x666c61677b32303665383539643865383534633466363030636231323735376262663966357d
print(long_to_bytes©.decode(‘utf-8’))
结果:flag{206e859d8e854c4f600cb12757bbf9f5}
‘’‘字符串转16进制’‘’
m = ‘flag{206e859d8e854c4f600cb12757bbf9f5}’ # 字符串状态
m = bytes_to_long(m.encode(‘utf-8’)) # 10进制状态
print(hex(m)) # 16进制状态
结果:666c61677b32303665383539643865383534633466363030636231323735376262663966357d
---
### RC4
#### Python实现
from Crypto.Cipher import ARC4
import base64
def rc4_encrypt(data, key1): # 加密
key = bytes(key1, encoding=‘utf-8’)
enc = ARC4.new(key)
res = enc.encrypt(data.encode(‘utf-8’))
res = base64.b64encode(res)
res = str(res, ‘utf-8’)
return res
def rc4_decrypt(data, key1): # 解密
data = base64.b64decode(data)
key = bytes(key1, encoding=‘utf-8’)
enc = ARC4.new(key)
res = enc.decrypt(data)
res = str(res, ‘gbk’)
return res
if name == “__main__”:
data = ‘nihao’ # 需要加密的内容
key = ‘123456’ # 加密key
encrypt_data = rc4_encrypt(data, key) # 加密方法
print(‘加密后:’, encrypt_data)
print(‘解密后:’, rc4_decrypt(encrypt_data, key)) # 解密方法
#### C++实现
/初始化函数/
void rc4_init(unsigned char *s, unsigned char *key, unsigned long Len)
{
int i = 0, j = 0;
char k[256] = {0};
unsigned char tmp = 0;
for (i = 0; i < 256; i++)
{
s[i] = i;
k[i] = key[i % Len];
}
for (i = 0; i < 256; i++)
{
j = (j + s[i] + k[i]) % 256;
tmp = s[i];
s[i] = s[j]; // 交换s[i]和s[j]
s[j] = tmp;
}
}
/加解密/
void rc4_crypt(unsigned char *s, unsigned char *Data, unsigned long Len)
{
int i = 0, j = 0, t = 0;
unsigned long k = 0;
unsigned char tmp;
for (k = 0; k < Len; k++)
{
i = (i + 1) % 256;
j = (j + s[i]) % 256;
tmp = s[i];
s[i] = s[j]; // 交换s[x]和s[y]
s[j] = tmp;
t = (s[i] + s[j]) % 256;
Data[k] ^= s[t];
}
}
int main()
{
unsigned char s[256] = {0}, s2[256] = {0}; // S-box
char key[256] = {"happynewyear"};
char pData[512] = "这是一个用来加密的数据Data";
unsigned long len = strlen(pData);
int i;
printf("pData=%s\n", pData);
printf("key=%s,length=%d\n\n", key, strlen(key));
rc4_init(s, (unsigned char *)key, strlen(key)); // 已经完成了初始化
printf("完成对S[i]的初始化,如下:\n\n");
for (i = 0; i < 256; i++)
{
printf("%02X", s[i]);
if (i && (i + 1) % 16 == 0)
putchar('\n');
}
printf("\n\n");
for (i = 0; i < 256; i++) // 用s2[i]暂时保留经过初始化的s[i],很重要的!!!
{
s2[i] = s[i];
}
printf("已经初始化,现在加密:\n\n");
rc4_crypt(s, (unsigned char *)pData, len); // 加密
printf("pData=%s\n\n", pData);
printf("已经加密,现在解密:\n\n");
// rc4_init(s,(unsignedchar*)key,strlen(key));//初始化密钥
rc4_crypt(s2, (unsigned char *)pData, len); // 解密
printf("pData=%s\n\n", pData);
return 0;
}
### 矩阵乘法
在RE中矩阵乘法有时也是很令人脑疼。
一方面我们可以调用numpy库。
另一方面,遇到魔改的矩阵乘法,通常在每次运算时加减一个值,我们也可以用z3求解器消灭它。
#### numpy
a=[0x00000017, 0x0000000D, 0x00000004, 0x00000030, 0x00000029, 0x00000029, 0x0000002A, 0x00000021, 0x0000001E, 0x00000003, 0x00000045, 0x00000001, 0x0000000D, 0x0000002D, 0x00000029, 0x00000040, 0x00000008, 0x00000050, 0x0000000F, 0x0000002A, 0x00000038, 0x00000013, 0x0000003E, 0x00000046, 0x00000017, 0x0000003F, 0x0000001E, 0x00000044, 0x00000011, 0x00000038, 0x0000005C, 0x0000000C, 0x00000010, 0x00000040, 0x0000001F, 0x00000003, 0x00000011, 0x00000047, 0x0000003A, 0x00000009, 0x00000040, 0x00000053, 0x00000047, 0x00000034, 0x00000063, 0x00000059, 0x0000004C, 0x00000044, 0x00000001, 0x00000063, 0x00000010, 0x00000010, 0x00000034, 0x0000002B, 0x00000000, 0x0000002C, 0x00000032, 0x00000020, 0x00000032, 0x0000001F, 0x00000014, 0x0000003F, 0x00000002, 0x00000063, 0x00000000, 0x00000039, 0x0000004F, 0x0000002B, 0x00000047, 0x00000013, 0x00000050, 0x0000005C, 0x0000005D, 0x0000003A, 0x00000054, 0x0000004A, 0x00000051, 0x0000002D, 0x00000037, 0x00000015, 0x00000001, 0x00000063, 0x0000001E, 0x0000001C, 0x00000038, 0x00000001, 0x0000000C, 0x0000004D, 0x0000005C, 0x00000004, 0x00000025, 0x00000043, 0x0000003C, 0x00000036, 0x00000033, 0x0000004F, 0x00000026, 0x00000057, 0x00000030, 0x00000010]
v16=[0]*40
v16[0] = 33211;
v16[1] = 36113;
v16[2] = 28786;
v16[3] = 44634;
v16[4] = 30174;
v16[5] = 39163;
v16[6] = 34923;
v16[7] = 44333;
v16[8] = 33574;
v16[9] = 23555;
v16[10] = 35015;
v16[11] = 42724;
v16[12] = 34160;
v16[13] = 49166;
v16[14] = 35770;
v16[15] = 45984;
v16[16] = 39754;
v16[17] = 51672;
v16[18] = 38323;
v16[19] = 27511;
v16[20] = 31334;
v16[21] = 34214;
v16[22] = 28014;
v16[23] = 41090;
v16[24] = 29258;
v16[25] = 37905;
v16[26] = 33777;
v16[27] = 39812;
v16[28] = 29442;
v16[29] = 22225;
v16[30] = 30853;
v16[31] = 35330;
v16[32] = 30393;
v16[33] = 41247;
v16[34] = 30439;
v16[35] = 39434;
v16[36] = 31587;
v16[37] = 46815;
v16[38] = 35205;
v16[39] = 20689;
data=[]
for i in range(10):
d=[]
for j in range(10):
d.append(a[j*10+i])
data.append(d)
import numpy as np
key=[]
for i in range(4):
d=[]
for j in range(10):
d.append(v16[j+i*10])
key.append(d)
A=np.matrix(data).I # 逆矩阵
B=np.matrix(key).T # 转置矩阵
x=np.dot(A,B) # 矩阵相乘
y=x.T.round().tolist()
print(‘’.join(chr(int(i)) for i in y[0]+y[1]+y[2]+y[3]))
[numpy教程:矩阵matrix及其运算\_np.matrix-CSDN博客]( )
#### z3在矩阵乘法中的应用
from z3 import *
flag矩阵*key矩阵得到enc矩阵
现在反求flag矩阵
key = [0, -2, -1, 4, 1,
-1, 1, 0, 0, -1,
-3, -2, 0, -10, -1,
-1, -2, 1, -13, -1,
-6, -1, -2, 1, -2,]
enc = [0x76, 0x74, 0xf5, 0x2f, 0x53,
0x48, 0x74, 0x45, 0xa4, 0x5f,
0xfc, 0x63, 0x1, 0xd0, 0xf8,
0xaa, 0x79, 0x46, 0x11, 0x7e,
0x1d, 0x91, 0x7e, 0x8e, 0xca]
flag = [Int(‘flag[%d]’ % i) for i in range(25)] # 定义flag矩阵
s = Solver() # 创建一个求解器
print(flag) # 输出flag矩阵样貌
for i in range(25):
s.add(flag[i] < 0xff)
s.add(flag[i] >= 0)
for i in range(5):
for j in range(5):
v12 = 0
for k in range(5):
v8 = (v12 + key[5 * i + k] * flag[5 * k + j]) % 256 # 矩阵乘法
v12 = v8
s.add(v8 == enc[i * 5 + j]) # 加入求解器中
print(‘calculating…’)
if (s.check() == sat): # 判断结果为sat,表示有解
print(s.model())
else:
print(‘no’)
kkk=s.model()
for i in s.model():
print(i, end=‘’)
### Blowfish
数据多,文件便一式两份,一般可以用ida的插件找到其踪迹。
**blowfish.py**
import Crypto.Util.number
import copy
from Blow_BOX import *
key_pbox = [0 for i in range(18)]
Encrypt = []
def init_key_pbox(_key):
index = 0
for i in range(18):
for j in range(4):
key_pbox[i] = ord(_key[index]) | (key_pbox[i] << 8)
index += 1
if index >= len(_key):
index = 0
for i in range(18):
p_box[i] ^= key_pbox[i]
def Fn(Left):
a = (Left & 0xff000000) >> 24
b = (Left & 0x00ff0000) >> 16
c = (Left & 0x0000ff00) >> 8
d = Left & 0x000000ff
Sa = s_box[0][a]
Sb = s_box[1][b]
Sc = s_box[2][c]
Sd = s_box[3][d]
return (((Sa + Sb) ^ Sc) + Sd) & 0xffffffff
def Blow_Main_Encrypt(Left, Right):
for i in range(16):
Left ^= p_box[i]
Right ^= Fn(Left)
Temp = Left
Left = Right
Right = Temp
Temp = Left
Left = Right ^ p_box[17]
Right = Temp ^ p_box[16]
return Left, Right
def Blow_Main_Decrypt(Left, Right):
for i in range(17, 1, -1):
Left ^= p_box[i]
Right ^= Fn(Left)
Temp = Left
Left = Right
Right = Temp
Temp = Left
Left = Right ^ p_box[0]
Right = Temp ^ p_box[1]
return Left, Right
def Change_Box():
Left = 0
Right = 0
for i in range(0, 18, 2):
Left, Right = Blow_Main_Encrypt(Left, Right)
p_box[i] = Left
p_box[i + 1] = Right
for i in range(4):
for j in range(0, 256, 2):
Left, Right = Blow_Main_Encrypt(Left, Right)
s_box[i][j] = Left
s_box[i][j + 1] = Right
def BlowFish_Encrypt(data):
while len(data) % 8:
data += ‘0’
cipher = ‘’
for i in range(0, len(data), 8):
Left = (ord(data[i]) << 24) | (ord(data[i + 1]) << 16) | (ord(data[i + 2]) << 8) | (ord(data[i + 3]))
Right = (ord(data[i + 4]) << 24) | (ord(data[i + 5]) << 16) | (ord(data[i + 6]) << 8) | (ord(data[i + 7]))
Left, Right = Blow_Main_Encrypt(Left, Right)
cipher += hex(Left)[2:]
cipher += hex(Right)[2:]
global Encrypt
Encrypt = []
print(cipher)
return cipher
def BlowFish_Decrypt(cipher):
plain = ‘’
for i in range(0, len(cipher), 16):
Left = cipher[i:i + 8]
Right = cipher[i + 8:i + 16]
Left = int(Left, base=16)
Right = int(Right, base=16)
Left, Right = Blow_Main_Decrypt(Left, Right)
plain += hex(Left)[2:]
plain += hex(Right)[2:]
plain = int(plain, base=16)
print(Crypto.Util.number.long_to_bytes(plain))
global Encrypt
Encrypt = []
if name == ‘__main__’:
key = “keykeykeykeykey”
init_key_pbox(key)
Change_Box()
data = "flag{asdasdasdasdasdasdasdasdasdasd}"
encrypted_data = BlowFish_Encrypt(data)
cipher = 'data.'
BlowFish_Decrypt(cipher)
m = input("PLZ choose a model: 1.Encrypt 2.Decrypt 3.exit\n")
**Blow\_BOX.py文件**
p_box = [
0x243F6A88, 0x85A308D3, 0x13198A2E, 0x03707344,
0xA4093822, 0x299F31D0, 0x082EFA98, 0xEC4E6C89,
0x452821E6, 0x38D01377, 0xBE5466CF, 0x34E90C6C,
0xC0AC29B7, 0xC97C50DD, 0x3F84D5B5, 0xB5470917,
0x9216D5D9, 0x8979FB1B]
s_box = [
[0xD1310BA6, 0x98DFB5AC, 0x2FFD72DB, 0xD01ADFB7,
0xB8E1AFED, 0x6A267E96, 0xBA7C9045, 0xF12C7F99,
0x24A19947, 0xB3916CF7, 0x0801F2E2, 0x858EFC16,
0x636920D8, 0x71574E69, 0xA458FEA3, 0xF4933D7E,
0x0D95748F, 0x728EB658, 0x718BCD58, 0x82154AEE,
0x7B54A41D, 0xC25A59B5, 0x9C30D539, 0x2AF26013,
0xC5D1B023, 0x286085F0, 0xCA417918, 0xB8DB38EF,
0x8E79DCB0, 0x603A180E, 0x6C9E0E8B, 0xB01E8A3E,
0xD71577C1, 0xBD314B27, 0x78AF2FDA, 0x55605C60,
0xE65525F3, 0xAA55AB94, 0x57489862, 0x63E81440,
0x55CA396A, 0x2AAB10B6, 0xB4CC5C34, 0x1141E8CE,
0xA15486AF, 0x7C72E993, 0xB3EE1411, 0x636FBC2A,
0x2BA9C55D, 0x741831F6, 0xCE5C3E16, 0x9B87931E,
0xAFD6BA33, 0x6C24CF5C, 0x7A325381, 0x28958677,
0x3B8F4898, 0x6B4BB9AF, 0xC4BFE81B, 0x66282193,
0x61D809CC, 0xFB21A991, 0x487CAC60, 0x5DEC8032,
0xEF845D5D, 0xE98575B1, 0xDC262302, 0xEB651B88,
0x23893E81, 0xD396ACC5, 0x0F6D6FF3, 0x83F44239,
0x2E0B4482, 0xA4842004, 0x69C8F04A, 0x9E1F9B5E,
0x21C66842, 0xF6E96C9A, 0x670C9C61, 0xABD388F0,
0x6A51A0D2, 0xD8542F68, 0x960FA728, 0xAB5133A3,
0x6EEF0B6C, 0x137A3BE4, 0xBA3BF050, 0x7EFB2A98,
0xA1F1651D, 0x39AF0176, 0x66CA593E, 0x82430E88,
0x8CEE8619, 0x456F9FB4, 0x7D84A5C3, 0x3B8B5EBE,
0xE06F75D8, 0x85C12073, 0x401A449F, 0x56C16AA6,
0x4ED3AA62, 0x363F7706, 0x1BFEDF72, 0x429B023D,
0x37D0D724, 0xD00A1248, 0xDB0FEAD3, 0x49F1C09B,
0x075372C9, 0x80991B7B, 0x25D479D8, 0xF6E8DEF7,
0xE3FE501A, 0xB6794C3B, 0x976CE0BD, 0x04C006BA,
0xC1A94FB6, 0x409F60C4, 0x5E5C9EC2, 0x196A2463,
0x68FB6FAF, 0x3E6C53B5, 0x1339B2EB, 0x3B52EC6F,
0x6DFC511F, 0x9B30952C, 0xCC814544, 0xAF5EBD09,
0xBEE3D004, 0xDE334AFD, 0x660F2807, 0x192E4BB3,
0xC0CBA857, 0x45C8740F, 0xD20B5F39, 0xB9D3FBDB,
0x5579C0BD, 0x1A60320A, 0xD6A100C6, 0x402C7279,
0x679F25FE, 0xFB1FA3CC, 0x8EA5E9F8, 0xDB3222F8,
0x3C7516DF, 0xFD616B15, 0x2F501EC8, 0xAD0552AB,
0x323DB5FA, 0xFD238760, 0x53317B48, 0x3E00DF82,
0x9E5C57BB, 0xCA6F8CA0, 0x1A87562E, 0xDF1769DB,
0xD542A8F6, 0x287EFFC3, 0xAC6732C6, 0x8C4F5573,
0x695B27B0, 0xBBCA58C8, 0xE1FFA35D, 0xB8F011A0,
0x10FA3D98, 0xFD2183B8, 0x4AFCB56C, 0x2DD1D35B,
0x9A53E479, 0xB6F84565, 0xD28E49BC, 0x4BFB9790,
0xE1DDF2DA, 0xA4CB7E33, 0x62FB1341, 0xCEE4C6E8,
0xEF20CADA, 0x36774C01, 0xD07E9EFE, 0x2BF11FB4,
0x95DBDA4D, 0xAE909198, 0xEAAD8E71, 0x6B93D5A0,
0xD08ED1D0, 0xAFC725E0, 0x8E3C5B2F, 0x8E7594B7,
0x8FF6E2FB, 0xF2122B64, 0x8888B812, 0x900DF01C,
0x4FAD5EA0, 0x688FC31C, 0xD1CFF191, 0xB3A8C1AD,
0x2F2F2218, 0xBE0E1777, 0xEA752DFE, 0x8B021FA1,
0xE5A0CC0F, 0xB56F74E8, 0x18ACF3D6, 0xCE89E299,
0xB4A84FE0, 0xFD13E0B7, 0x7CC43B81, 0xD2ADA8D9,
0x165FA266, 0x80957705, 0x93CC7314, 0x211A1477,
0xE6AD2065, 0x77B5FA86, 0xC75442F5, 0xFB9D35CF,
0xEBCDAF0C, 0x7B3E89A0, 0xD6411BD3, 0xAE1E7E49,
0x00250E2D, 0x2071B35E, 0x226800BB, 0x57B8E0AF,
0x2464369B, 0xF009B91E, 0x5563911D, 0x59DFA6AA,
0x78C14389, 0xD95A537F, 0x207D5BA2, 0x02E5B9C5,
0x83260376, 0x6295CFA9, 0x11C81968, 0x4E734A41,
0xB3472DCA, 0x7B14A94A, 0x1B510052, 0x9A532915,
0xD60F573F, 0xBC9BC6E4, 0x2B60A476, 0x81E67400,
0x08BA6FB5, 0x571BE91F, 0xF296EC6B, 0x2A0DD915,
0xB6636521, 0xE7B9F9B6, 0xFF34052E, 0xC5855664,
0x53B02D5D, 0xA99F8FA1, 0x08BA4799, 0x6E85076A],
[0x4B7A70E9, 0xB5B32944, 0xDB75092E, 0xC4192623,
0xAD6EA6B0, 0x49A7DF7D, 0x9CEE60B8, 0x8FEDB266,
0xECAA8C71, 0x699A17FF, 0x5664526C, 0xC2B19EE1,
0x193602A5, 0x75094C29, 0xA0591340, 0xE4183A3E,
0x3F54989A, 0x5B429D65, 0x6B8FE4D6, 0x99F73FD6,
0xA1D29C07, 0xEFE830F5, 0x4D2D38E6, 0xF0255DC1,
0x4CDD2086, 0x8470EB26, 0x6382E9C6, 0x021ECC5E,
0x09686B3F, 0x3EBAEFC9, 0x3C971814, 0x6B6A70A1,
0x687F3584, 0x52A0E286, 0xB79C5305, 0xAA500737,
0x3E07841C, 0x7FDEAE5C, 0x8E7D44EC, 0x5716F2B8,
0xB03ADA37, 0xF0500C0D, 0xF01C1F04, 0x0200B3FF,
0xAE0CF51A, 0x3CB574B2, 0x25837A58, 0xDC0921BD,
0xD19113F9, 0x7CA92FF6, 0x94324773, 0x22F54701,
0x3AE5E581, 0x37C2DADC, 0xC8B57634, 0x9AF3DDA7,
0xA9446146, 0x0FD0030E, 0xECC8C73E, 0xA4751E41,
0xE238CD99, 0x3BEA0E2F, 0x3280BBA1, 0x183EB331,
0x4E548B38, 0x4F6DB908, 0x6F420D03, 0xF60A04BF,
0x2CB81290, 0x24977C79, 0x5679B072, 0xBCAF89AF,
0xDE9A771F, 0xD9930810, 0xB38BAE12, 0xDCCF3F2E,
0x5512721F, 0x2E6B7124, 0x501ADDE6, 0x9F84CD87,
0x7A584718, 0x7408DA17, 0xBC9F9ABC, 0xE94B7D8C,
0xEC7AEC3A, 0xDB851DFA, 0x63094366, 0xC464C3D2,
0xEF1C1847, 0x3215D908, 0xDD433B37, 0x24C2BA16,
0x12A14D43, 0x2A65C451, 0x50940002, 0x133AE4DD,
0x71DFF89E, 0x10314E55, 0x81AC77D6, 0x5F11199B,
0x043556F1, 0xD7A3C76B, 0x3C11183B, 0x5924A509,
0xF28FE6ED, 0x97F1FBFA, 0x9EBABF2C, 0x1E153C6E,
0x86E34570, 0xEAE96FB1, 0x860E5E0A, 0x5A3E2AB3,
0x771FE71C, 0x4E3D06FA, 0x2965DCB9, 0x99E71D0F,
0x803E89D6, 0x5266C825, 0x2E4CC978, 0x9C10B36A,
0xC6150EBA, 0x94E2EA78, 0xA5FC3C53, 0x1E0A2DF4,
0xF2F74EA7, 0x361D2B3D, 0x1939260F, 0x19C27960,
0x5223A708, 0xF71312B6, 0xEBADFE6E, 0xEAC31F66,
0xE3BC4595, 0xA67BC883, 0xB17F37D1, 0x018CFF28,
0xC332DDEF, 0xBE6C5AA5, 0x65582185, 0x68AB9802,
0xEECEA50F, 0xDB2F953B, 0x2AEF7DAD, 0x5B6E2F84,
0x1521B628, 0x29076170, 0xECDD4775, 0x619F1510,
0x13CCA830, 0xEB61BD96, 0x0334FE1E, 0xAA0363CF,
0xB5735C90, 0x4C70A239, 0xD59E9E0B, 0xCBAADE14,
0xEECC86BC, 0x60622CA7, 0x9CAB5CAB, 0xB2F3846E,
0x648B1EAF, 0x19BDF0CA, 0xA02369B9, 0x655ABB50,
0x40685A32, 0x3C2AB4B3, 0x319EE9D5, 0xC021B8F7,
0x9B540B19, 0x875FA099, 0x95F7997E, 0x623D7DA8,
0xF837889A, 0x97E32D77, 0x11ED935F, 0x16681281,
0x0E358829, 0xC7E61FD6, 0x96DEDFA1, 0x7858BA99,
0x57F584A5, 0x1B227263, 0x9B83C3FF, 0x1AC24696,
0xCDB30AEB, 0x532E3054, 0x8FD948E4, 0x6DBC3128,
0x58EBF2EF, 0x34C6FFEA, 0xFE28ED61, 0xEE7C3C73,
0x5D4A14D9, 0xE864B7E3, 0x42105D14, 0x203E13E0,
0x45EEE2B6, 0xA3AAABEA, 0xDB6C4F15, 0xFACB4FD0,
0xC742F442, 0xEF6ABBB5, 0x654F3B1D, 0x41CD2105,
0xD81E799E, 0x86854DC7, 0xE44B476A, 0x3D816250,
0xCF62A1F2, 0x5B8D2646, 0xFC8883A0, 0xC1C7B6A3,
0x7F1524C3, 0x69CB7492, 0x47848A0B, 0x5692B285,
0x095BBF00, 0xAD19489D, 0x1462B174, 0x23820E00,
0x58428D2A, 0x0C55F5EA, 0x1DADF43E, 0x233F7061,
0x3372F092, 0x8D937E41, 0xD65FECF1, 0x6C223BDB,
0x7CDE3759, 0xCBEE7460, 0x4085F2A7, 0xCE77326E,
0xA6078084, 0x19F8509E, 0xE8EFD855, 0x61D99735,
0xA969A7AA, 0xC50C06C2, 0x5A04ABFC, 0x800BCADC,
0x9E447A2E, 0xC3453484, 0xFDD56705, 0x0E1E9EC9,
0xDB73DBD3, 0x105588CD, 0x675FDA79, 0xE3674340,
0xC5C43465, 0x713E38D8, 0x3D28F89E, 0xF16DFF20,
0x153E21E7, 0x8FB03D4A, 0xE6E39F2B, 0xDB83ADF7],
[0xE93D5A68, 0x948140F7, 0xF64C261C, 0x94692934,
0x411520F7, 0x7602D4F7, 0xBCF46B2E, 0xD4A20068,
0xD4082471, 0x3320F46A, 0x43B7D4B7, 0x500061AF,
0x1E39F62E, 0x97244546, 0x14214F74, 0xBF8B8840,
0x4D95FC1D, 0x96B591AF, 0x70F4DDD3, 0x66A02F45,
0xBFBC09EC, 0x03BD9785, 0x7FAC6DD0, 0x31CB8504,
0x96EB27B3, 0x55FD3941, 0xDA2547E6, 0xABCA0A9A,
0x28507825, 0x530429F4, 0x0A2C86DA, 0xE9B66DFB,
0x68DC1462, 0xD7486900, 0x680EC0A4, 0x27A18DEE,
0x4F3FFEA2, 0xE887AD8C, 0xB58CE006, 0x7AF4D6B6,
0xAACE1E7C, 0xD3375FEC, 0xCE78A399, 0x406B2A42,
0x20FE9E35, 0xD9F385B9, 0xEE39D7AB, 0x3B124E8B,
0x1DC9FAF7, 0x4B6D1856, 0x26A36631, 0xEAE397B2,
0x3A6EFA74, 0xDD5B4332, 0x6841E7F7, 0xCA7820FB,
0xFB0AF54E, 0xD8FEB397, 0x454056AC, 0xBA489527,
0x55533A3A, 0x20838D87, 0xFE6BA9B7, 0xD096954B,
0x55A867BC, 0xA1159A58, 0xCCA92963, 0x99E1DB33,
0xA62A4A56, 0x3F3125F9, 0x5EF47E1C, 0x9029317C,
0xFDF8E802, 0x04272F70, 0x80BB155C, 0x05282CE3,
0x95C11548, 0xE4C66D22, 0x48C1133F, 0xC70F86DC,
0x07F9C9EE, 0x41041F0F, 0x404779A4, 0x5D886E17,
0x325F51EB, 0xD59BC0D1, 0xF2BCC18F, 0x41113564,
0x257B7834, 0x602A9C60, 0xDFF8E8A3, 0x1F636C1B,
0x0E12B4C2, 0x02E1329E, 0xAF664FD1, 0xCAD18115,
0x6B2395E0, 0x333E92E1, 0x3B240B62, 0xEEBEB922,
0x85B2A20E, 0xE6BA0D99, 0xDE720C8C, 0x2DA2F728,
0xD0127845, 0x95B794FD, 0x647D0862, 0xE7CCF5F0,
0x5449A36F, 0x877D48FA, 0xC39DFD27, 0xF33E8D1E,
0x0A476341, 0x992EFF74, 0x3A6F6EAB, 0xF4F8FD37,
0xA812DC60, 0xA1EBDDF8, 0x991BE14C, 0xDB6E6B0D,
0xC67B5510, 0x6D672C37, 0x2765D43B, 0xDCD0E804,
0xF1290DC7, 0xCC00FFA3, 0xB5390F92, 0x690FED0B,
0x667B9FFB, 0xCEDB7D9C, 0xA091CF0B, 0xD9155EA3,
0xBB132F88, 0x515BAD24, 0x7B9479BF, 0x763BD6EB,
0x37392EB3, 0xCC115979, 0x8026E297, 0xF42E312D,
0x6842ADA7, 0xC66A2B3B, 0x12754CCC, 0x782EF11C,
0x6A124237, 0xB79251E7, 0x06A1BBE6, 0x4BFB6350,
0x1A6B1018, 0x11CAEDFA, 0x3D25BDD8, 0xE2E1C3C9,
0x44421659, 0x0A121386, 0xD90CEC6E, 0xD5ABEA2A,
0x64AF674E, 0xDA86A85F, 0xBEBFE988, 0x64E4C3FE,
0x9DBC8057, 0xF0F7C086, 0x60787BF8, 0x6003604D,
0xD1FD8346, 0xF6381FB0, 0x7745AE04, 0xD736FCCC,
0x83426B33, 0xF01EAB71, 0xB0804187, 0x3C005E5F,
0x77A057BE, 0xBDE8AE24, 0x55464299, 0xBF582E61,
0x4E58F48F, 0xF2DDFDA2, 0xF474EF38, 0x8789BDC2,
0x5366F9C3, 0xC8B38E74, 0xB475F255, 0x46FCD9B9,
0x7AEB2661, 0x8B1DDF84, 0x846A0E79, 0x915F95E2,
0x466E598E, 0x20B45770, 0x8CD55591, 0xC902DE4C,
0xB90BACE1, 0xBB8205D0, 0x11A86248, 0x7574A99E,
0xB77F19B6, 0xE0A9DC09, 0x662D09A1, 0xC4324633,
0xE85A1F02, 0x09F0BE8C, 0x4A99A025, 0x1D6EFE10,
0x1AB93D1D, 0x0BA5A4DF, 0xA186F20F, 0x2868F169,
0xDCB7DA83, 0x573906FE, 0xA1E2CE9B, 0x4FCD7F52,
0x50115E01, 0xA70683FA, 0xA002B5C4, 0x0DE6D027,
0x9AF88C27, 0x773F8641, 0xC3604C06, 0x61A806B5,
0xF0177A28, 0xC0F586E0, 0x006058AA, 0x30DC7D62,
0x11E69ED7, 0x2338EA63, 0x53C2DD94, 0xC2C21634,
0xBBCBEE56, 0x90BCB6DE, 0xEBFC7DA1, 0xCE591D76,
0x6F05E409, 0x4B7C0188, 0x39720A3D, 0x7C927C24,
0x86E3725F, 0x724D9DB9, 0x1AC15BB4, 0xD39EB8FC,
0xED545578, 0x08FCA5B5, 0xD83D7CD3, 0x4DAD0FC4,
0x1E50EF5E, 0xB161E6F8, 0xA28514D9, 0x6C51133C,
0x6FD5C7E7, 0x56E14EC4, 0x362ABFCE, 0xDDC6C837,
0xD79A3234, 0x92638212, 0x670EFA8E, 0x406000E0],
[0x3A39CE37, 0xD3FAF5CF, 0xABC27737, 0x5AC52D1B,
0x5CB0679E, 0x4FA33742, 0xD3822740, 0x99BC9BBE,
0xD5118E9D, 0xBF0F7315, 0xD62D1C7E, 0xC700C47B,
0xB78C1B6B, 0x21A19045, 0xB26EB1BE, 0x6A366EB4,
0x5748AB2F, 0xBC946E79, 0xC6A376D2, 0x6549C2C8,
0x530FF8EE, 0x468DDE7D, 0xD5730A1D, 0x4CD04DC6,
0x2939BBDB, 0xA9BA4650, 0xAC9526E8, 0xBE5EE304,
0xA1FAD5F0, 0x6A2D519A, 0x63EF8CE2, 0x9A86EE22,
0xC089C2B8, 0x43242EF6, 0xA51E03AA, 0x9CF2D0A4,
0x83C061BA, 0x9BE96A4D, 0x8FE51550, 0xBA645BD6,
0x2826A2F9, 0xA73A3AE1, 0x4BA99586, 0xEF5562E9,
0xC72FEFD3, 0xF752F7DA, 0x3F046F69, 0x77FA0A59,
0x80E4A915, 0x87B08601, 0x9B09E6AD, 0x3B3EE593,
0xE990FD5A, 0x9E34D797, 0x2CF0B7D9, 0x022B8B51,
0x96D5AC3A, 0x017DA67D, 0xD1CF3ED6, 0x7C7D2D28,
0x1F9F25CF, 0xADF2B89B, 0x5AD6B472, 0x5A88F54C,
0xE029AC71, 0xE019A5E6, 0x47B0ACFD, 0xED93FA9B,
0xE8D3C48D, 0x283B57CC, 0xF8D56629, 0x79132E28,
0x785F0191, 0xED756055, 0xF7960E44, 0xE3D35E8C,
0x15056DD4, 0x88F46DBA, 0x03A16125, 0x0564F0BD,
0xC3EB9E15, 0x3C9057A2, 0x97271AEC, 0xA93A072A,
0x1B3F6D9B, 0x1E6321F5, 0xF59C66FB, 0x26DCF319,
0x7533D928, 0xB155FDF5, 0x03563482, 0x8ABA3CBB,
0x28517711, 0xC20AD9F8, 0xABCC5167, 0xCCAD925F,
0x4DE81751, 0x3830DC8E, 0x379D5862, 0x9320F991,
0xEA7A90C2, 0xFB3E7BCE, 0x5121CE64, 0x774FBE32,
0xA8B6E37E, 0xC3293D46, 0x48DE5369, 0x6413E680,
0xA2AE0810, 0xDD6DB224, 0x69852DFD, 0x09072166,
0xB39A460A, 0x6445C0DD, 0x586CDECF, 0x1C20C8AE,
0x5BBEF7DD, 0x1B588D40, 0xCCD2017F, 0x6BB4E3BB,
0xDDA26A7E, 0x3A59FF45, 0x3E350A44, 0xBCB4CDD5,
0x72EACEA8, 0xFA6484BB, 0x8D6612AE, 0xBF3C6F47,
0xD29BE463, 0x542F5D9E, 0xAEC2771B, 0xF64E6370,
0x740E0D8D, 0xE75B1357, 0xF8721671, 0xAF537D5D,
0x4040CB08, 0x4EB4E2CC, 0x34D2466A, 0x0115AF84,
0xE1B00428, 0x95983A1D, 0x06B89FB4, 0xCE6EA048,
0x6F3F3B82, 0x3520AB82, 0x011A1D4B, 0x277227F8,
0x611560B1, 0xE7933FDC, 0xBB3A792B, 0x344525BD,
0xA08839E1, 0x51CE794B, 0x2F32C9B7, 0xA01FBAC9,
0xE01CC87E, 0xBCC7D1F6, 0xCF0111C3, 0xA1E8AAC7,
0x1A908749, 0xD44FBD9A, 0xD0DADECB, 0xD50ADA38,
0x0339C32A, 0xC6913667, 0x8DF9317C, 0xE0B12B4F,
0xF79E59B7, 0x43F5BB3A, 0xF2D519FF, 0x27D9459C,
0xBF97222C, 0x15E6FC2A, 0x0F91FC71, 0x9B941525,
0xFAE59361, 0xCEB69CEB, 0xC2A86459, 0x12BAA8D1,
0xB6C1075E, 0xE3056A0C, 0x10D25065, 0xCB03A442,
0xE0EC6E0E, 0x1698DB3B, 0x4C98A0BE, 0x3278E964,
0x9F1F9532, 0xE0D392DF, 0xD3A0342B, 0x8971F21E,
0x1B0A7441, 0x4BA3348C, 0xC5BE7120, 0xC37632D8,
0xDF359F8D, 0x9B992F2E, 0xE60B6F47, 0x0FE3F11D,
0xE54CDA54, 0x1EDAD891, 0xCE6279CF, 0xCD3E7E6F,
0x1618B166, 0xFD2C1D05, 0x848FD2C5, 0xF6FB2299,
0xF523F357, 0xA6327623, 0x93A83531, 0x56CCCD02,
0xACF08162, 0x5A75EBB5, 0x6E163697, 0x88D273CC,
0xDE966292, 0x81B949D0, 0x4C50901B, 0x71C65614,
0xE6C6C7BD, 0x327A140A, 0x45E1D006, 0xC3F27B9A,
0xC9AA53FD, 0x62A80F00, 0xBB25BFE2, 0x35BDD2F6,
0x71126905, 0xB2040222, 0xB6CBCF7C, 0xCD769C2B,
0x53113EC0, 0x1640E3D3, 0x38ABBD60, 0x2547ADF0,
0xBA38209C, 0xF746CE76, 0x77AFA1C5, 0x20756060,
0x85CBFE4E, 0x8AE88DD8, 0x7AAAF9B0, 0x4CF9AA7E,
0x1948C25C, 0x02FB8A8C, 0x01C36AE4, 0xD6EBE1F9,
0x90D4F869, 0xA65CDEA0, 0x3F09252D, 0xC208E69F,
0xB74E6132, 0xCE77E25B, 0x578FDFE3, 0x3AC372E6]]
---
## 做题技巧
---

>
> 有明显的:
>
>
>
>
>
>
> ```
> v1 = 4 \* FindIndex(v14, (unsigned int)a1[i]);
> v2 = (unsigned int)FindIndex(v14, (unsigned int)a1[i + 1]) >> 4;
> v4 = 16 \* FindIndex(v14, (unsigned int)a1[i + 1]);
> v5 = (unsigned int)FindIndex(v14, (unsigned int)a1[i + 2]) >> 2;
> v7 = (unsigned int)FindIndex(v14, (unsigned int)a1[i + 2]) << 6;
> Index = FindIndex(v14, (unsigned int)a1[i + 3]);
>
> ```
>
> 规律为:
>
>
> `i -> i+1 -> i+1 -> i+2 -> i+2 -> i+3`
>
>
> `4 -> 2 -> 6`
>
>
>
---
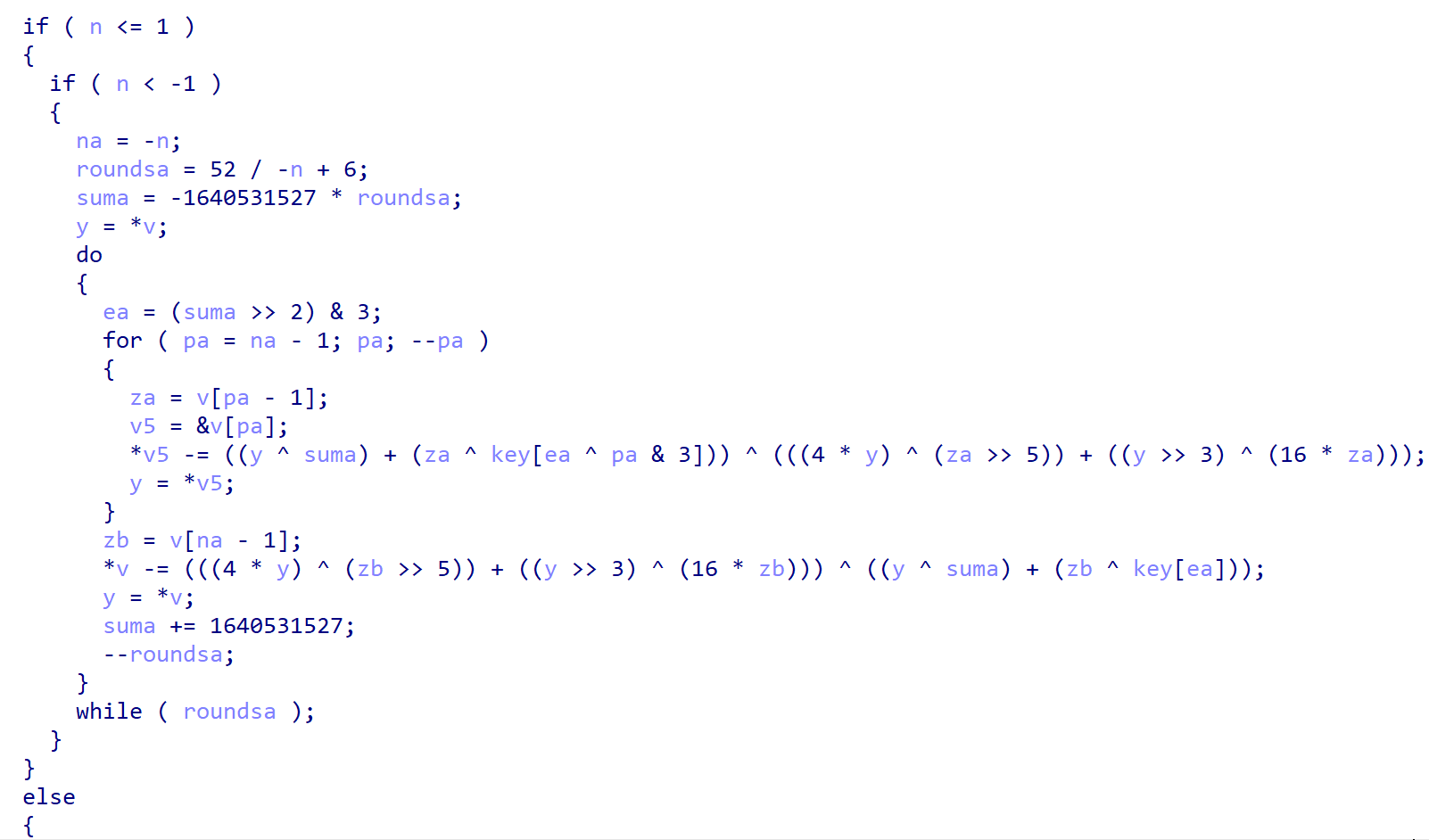
### Tea
#### tea
>
> ##### 步骤:
>
>
> 1. 查看是不是tea加密
> 2. 若是key加密,查看其关键数字是否被修改
> 3. 找到key(4个32位无符号整数)
> 4. 直接上脚本解密
>
>
>

>
> 1. >> 5
> 2. 有时候16\*会写成<<4
> 3. -= 0x61C88647(1,640,531,527);0x9e3779b9(2,654,435,769)
> 4. 循环32次
>
>
>
import pytea
import os
def generate_key():
return os.urandom(16)
def encrypt_data(data, key):
tea = pytea.TEA(key)
encrypt_data = tea.encrypt(data)
return encrypt_data
def decrypt_data(encrypted_data, key):
tea = pytea.TEA(key)
decrypted_data = tea.decrypt(encrypted_data)
return decrypted_data
key = generate_key()
data = b"hello world"
encrypted_data = encrypt_data(data, key)
print(“加密后的数据:”, encrypted_data)
decrypted_data = decrypt_data(encrypted_data, key)
print(“解密后的数据:”, decrypted_data)
---
#### xTea

>
> 有明显的:
>
>
> 1. >> 5,&3 ;>>11
> 2. 有时候16\*会写成<<4
> 3. -= 0x61C88647(1,640,531,527);0x9e3779b9(2,654,435,769)
> 4. 循环32次
>
>
>
#### xxtea
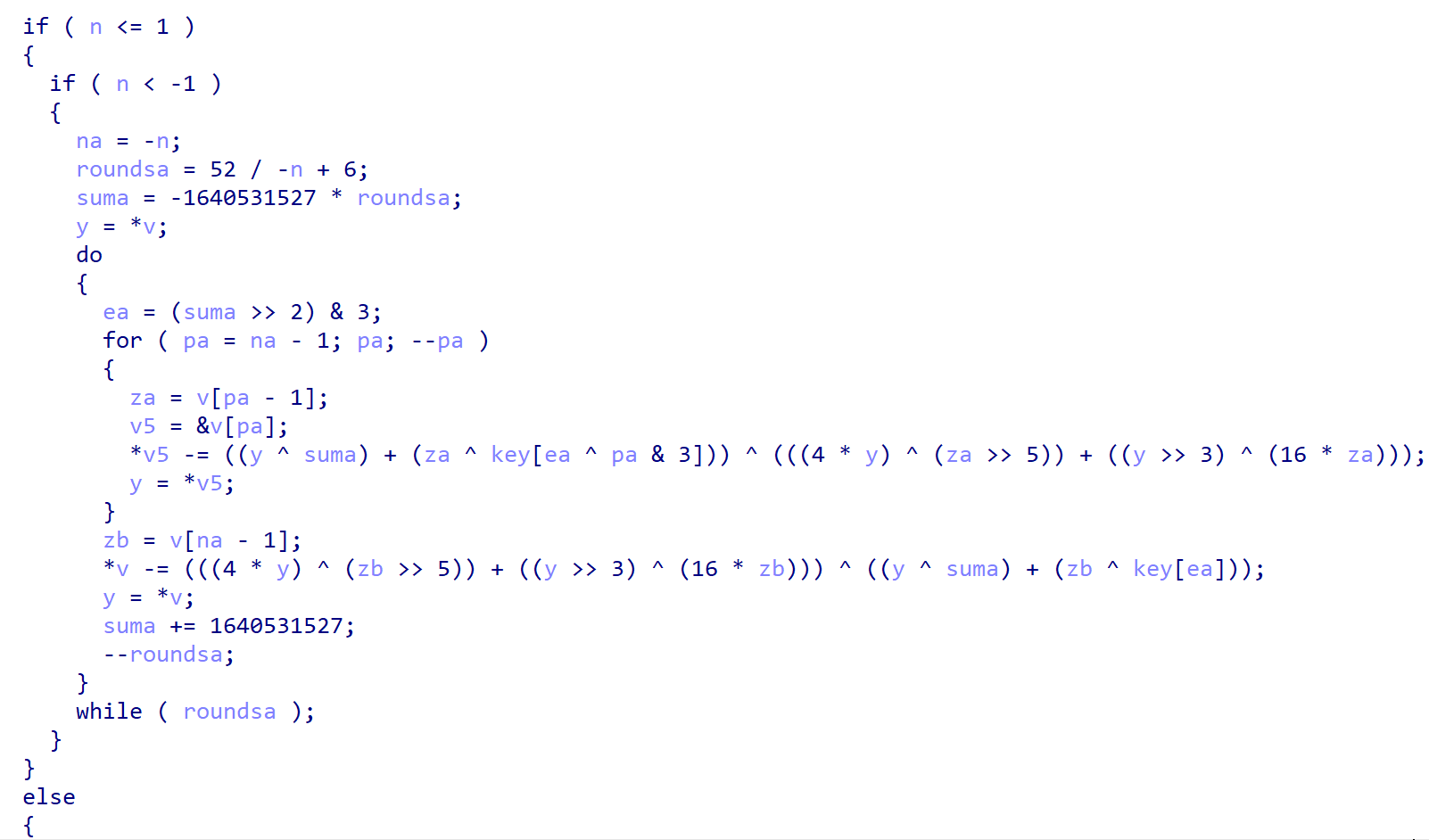
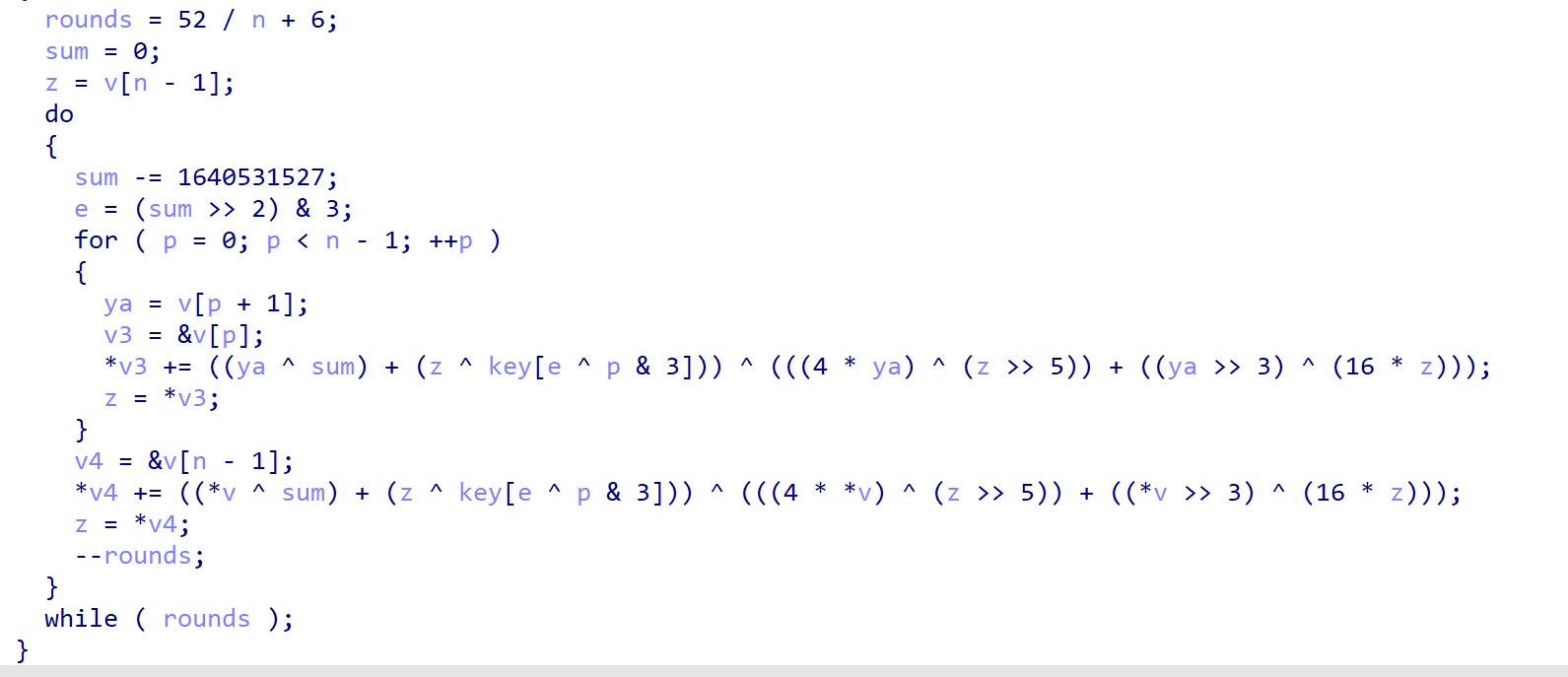
>
> 有明显的:
>
>
> 1. 3,4,5,16
> 2. 有时候16\*会写成<<4
> 3. -= 0x61C88647(1,640,531,527);0x9e3779b9(2,654,435,769)
> 4. 循环32次
>
>
>
import xxtea
加密
data = b"hello world!"
key = b’secretkeysecretk’ #16字节
encrypt_data = xxtea.encrypt(data, key)
print(encrypt_data)
解密
decrypt_data = xxtea.decrypt(encrypt_data, key)
print(decrypt_data)
---
### DES
from Crypto.Cipher import DES
def des_cbc_encode(key,iv,data):
# key: 8个字节
# data: 明文数据,utf-8格式
des = DES.new(key, mode=DES.MODE_CBC, IV=iv)
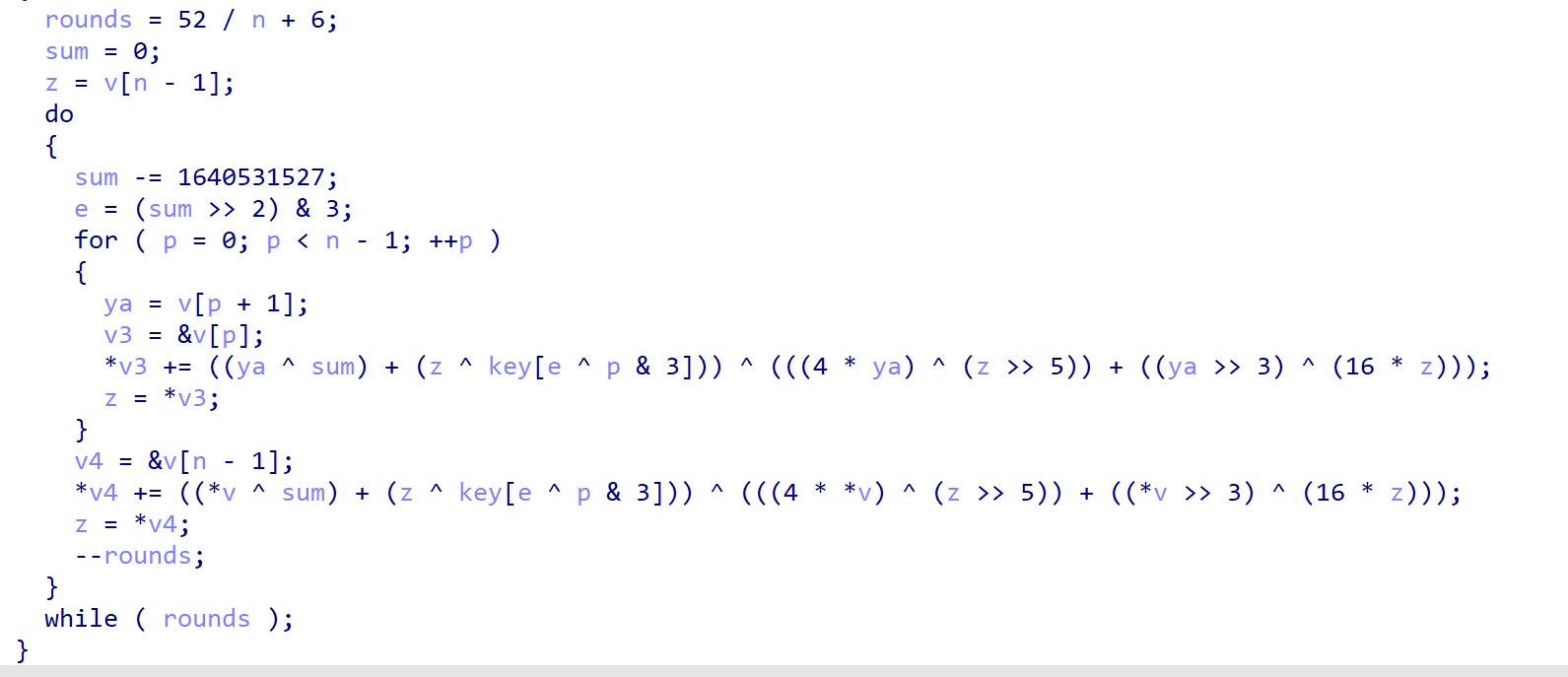
自我介绍一下,小编13年上海交大毕业,曾经在小公司待过,也去过华为、OPPO等大厂,18年进入阿里一直到现在。
深知大多数Python工程师,想要提升技能,往往是自己摸索成长或者是报班学习,但对于培训机构动则几千的学费,着实压力不小。自己不成体系的自学效果低效又漫长,而且极易碰到天花板技术停滞不前!
因此收集整理了一份《2024年Python开发全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友,同时减轻大家的负担。
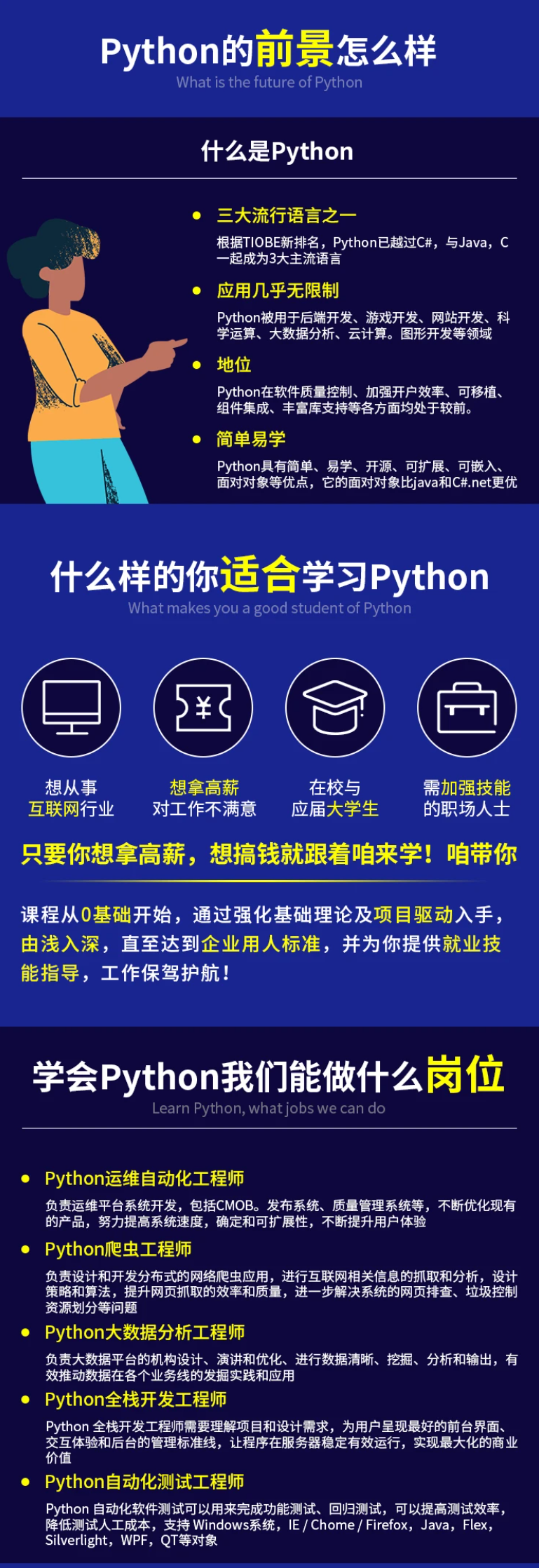
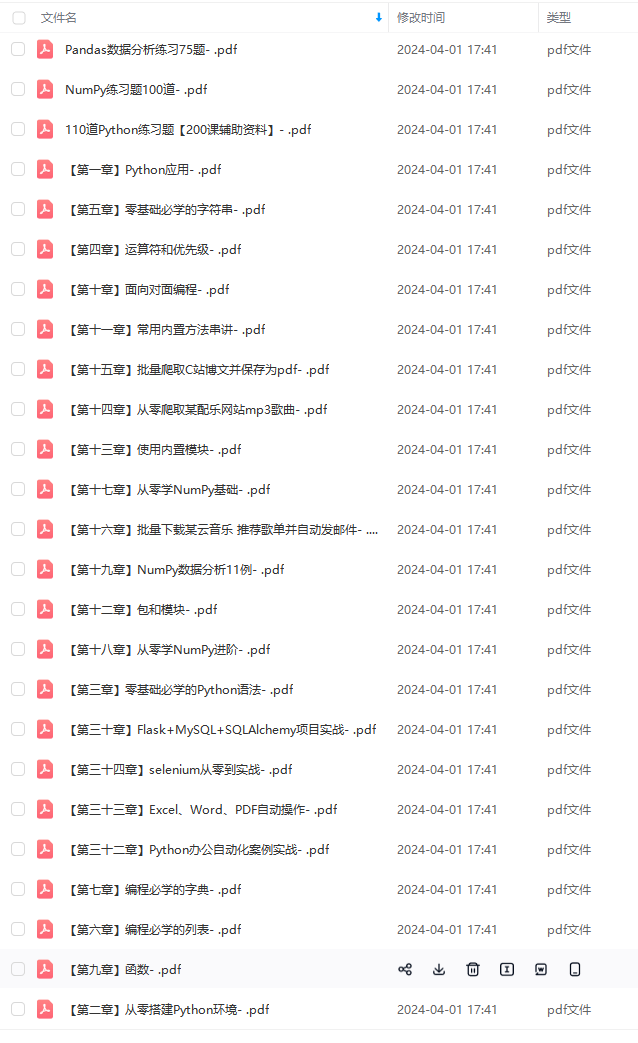
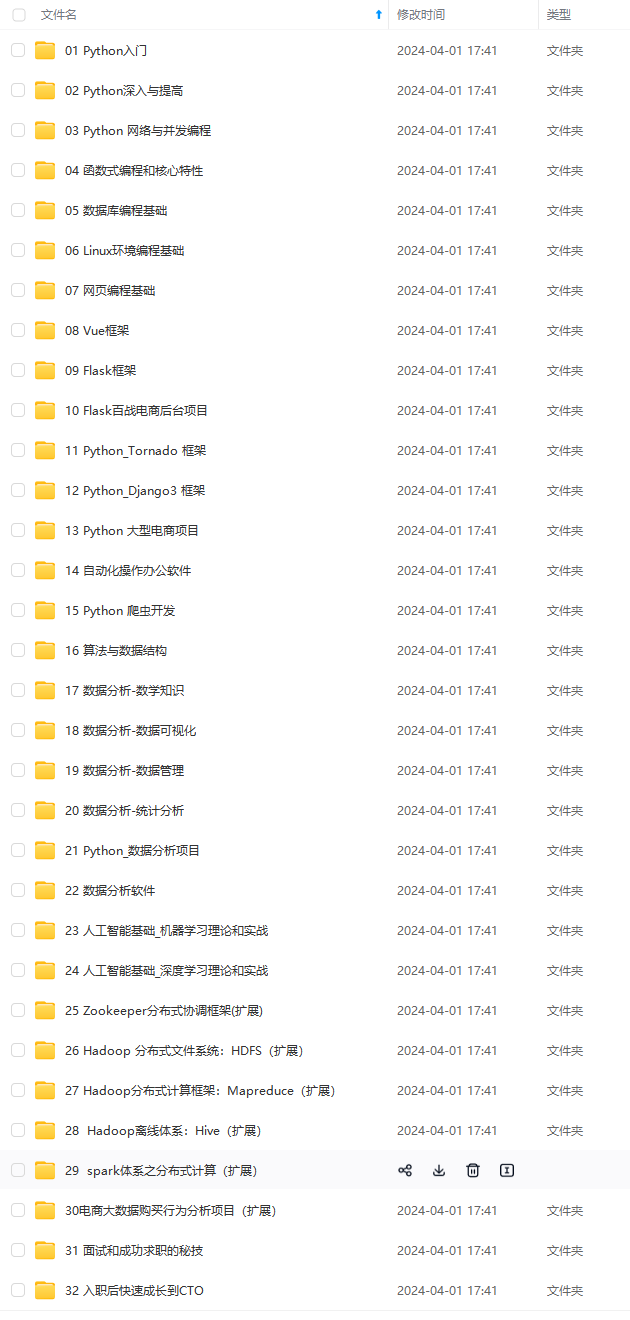
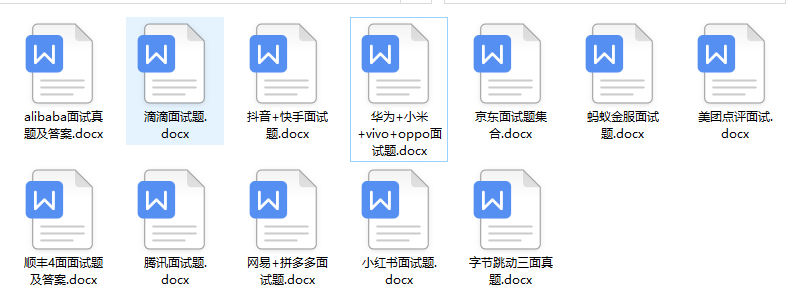
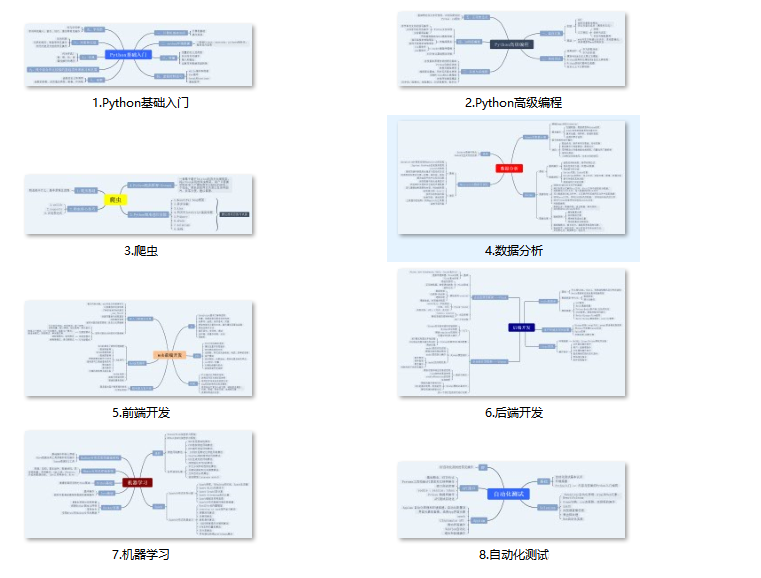
既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,基本涵盖了95%以上前端开发知识点,真正体系化!
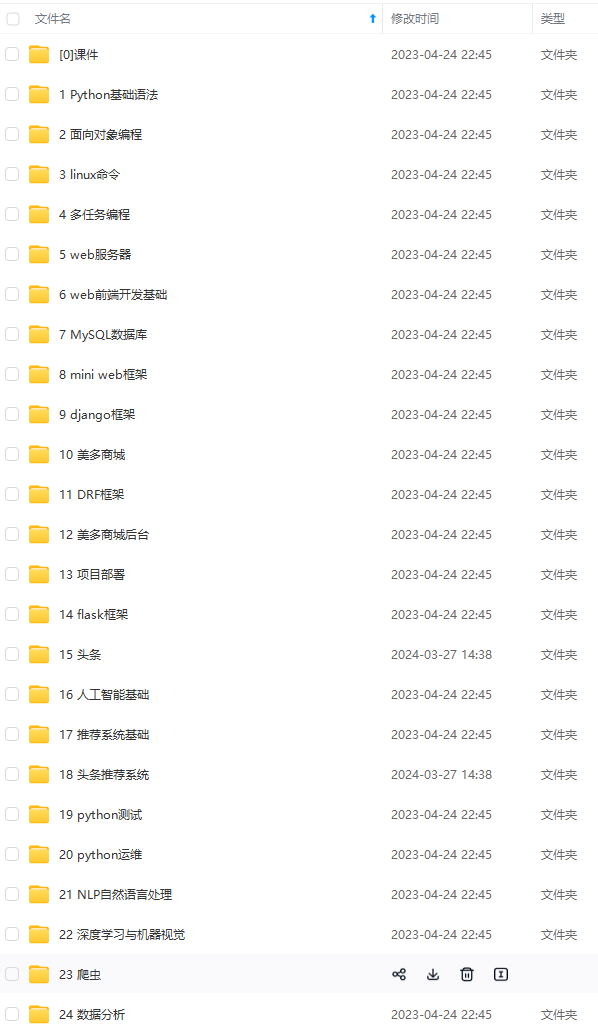
由于文件比较大,这里只是将部分目录大纲截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且后续会持续更新
如果你觉得这些内容对你有帮助,可以扫码获取!!!(备注:Python)
xxtea
有明显的:
- 3,4,5,16
- 有时候16*会写成<<4
- -= 0x61C88647(1,640,531,527);0x9e3779b9(2,654,435,769)
- 循环32次
import xxtea
# 加密
data = b"hello world!"
key = b'secretkeysecretk' #16字节
encrypt_data = xxtea.encrypt(data, key)
print(encrypt_data)
# 解密
decrypt_data = xxtea.decrypt(encrypt_data, key)
print(decrypt_data)
DES
from Crypto.Cipher import DES
def des\_cbc\_encode(key,iv,data):
# key: 8个字节
# data: 明文数据,utf-8格式
des = DES.new(key, mode=DES.MODE_CBC, IV=iv)
**自我介绍一下,小编13年上海交大毕业,曾经在小公司待过,也去过华为、OPPO等大厂,18年进入阿里一直到现在。**
**深知大多数Python工程师,想要提升技能,往往是自己摸索成长或者是报班学习,但对于培训机构动则几千的学费,着实压力不小。自己不成体系的自学效果低效又漫长,而且极易碰到天花板技术停滞不前!**
**因此收集整理了一份《2024年Python开发全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友,同时减轻大家的负担。**
[外链图片转存中...(img-MeCrrO40-1713551949106)]
[外链图片转存中...(img-Lv4cdd1c-1713551949107)]
[外链图片转存中...(img-PJzLbJkv-1713551949107)]
[外链图片转存中...(img-wewagtcT-1713551949108)]
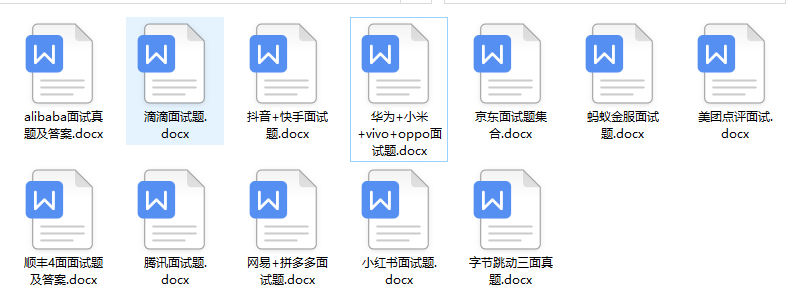
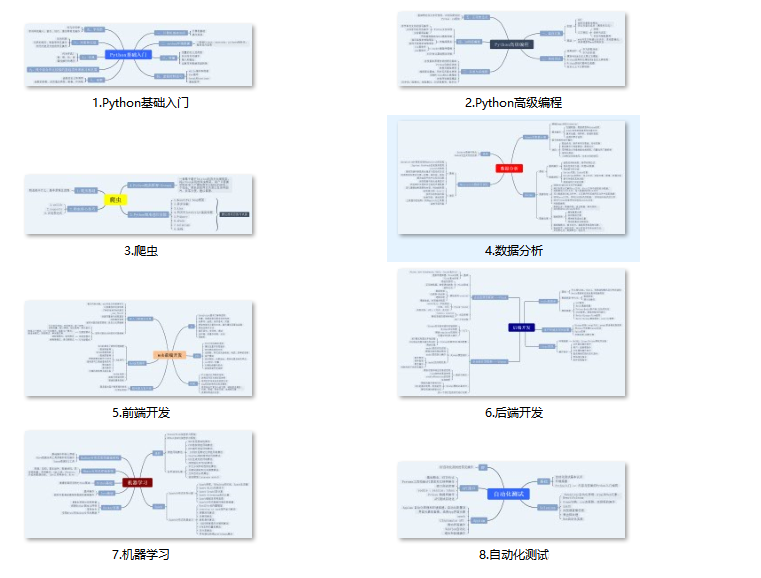
**既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,基本涵盖了95%以上前端开发知识点,真正体系化!**
**由于文件比较大,这里只是将部分目录大纲截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且后续会持续更新**
**如果你觉得这些内容对你有帮助,可以扫码获取!!!(备注:Python)**























 1955
1955

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








