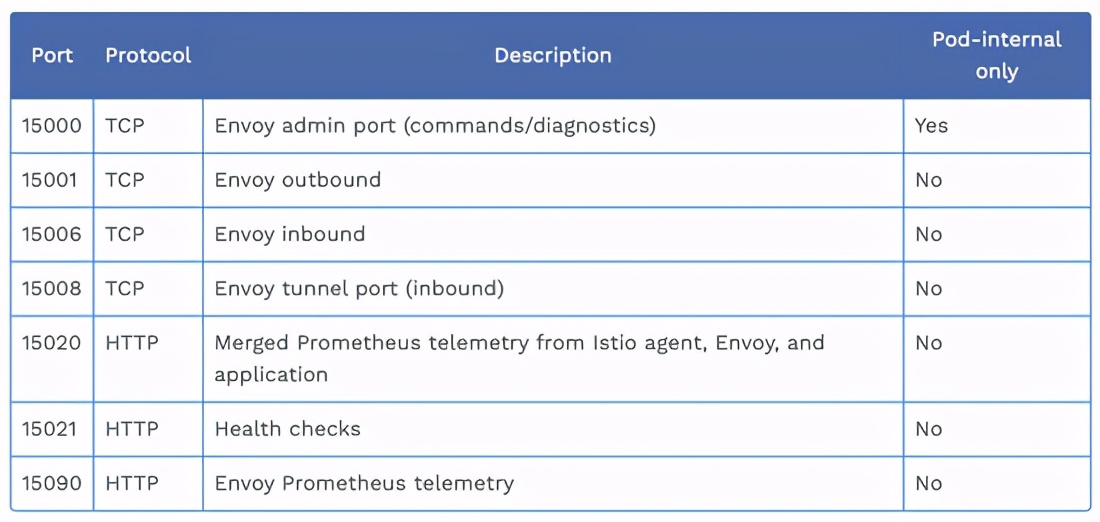
其会使用的全部服务端口信息如下:
Telemetry & Health 服务
=====================
Telemetry服务端口为15090,用于对外提供Envoy的性能统计指标。
curl http://127.0.0.1:15090/stats/prometheus
TYPE envoy_cluster_assignment_stale counter
envoy_cluster_assignment_stale{cluster_name=“xds-grpc”} 0
TYPE envoy_cluster_assignment_timeout_received counter
envoy_cluster_assignment_timeout_received{cluster_name=“xds-grpc”} 0
TYPE envoy_cluster_bind_errors counter
envoy_cluster_bind_errors{cluster_name=“xds-grpc”} 0
TYPE envoy_cluster_default_total_match_count counter
envoy_cluster_default_total_match_count{cluster_name=“xds-grpc”} 1
TYPE envoy_cluster_http2_dropped_headers_with_underscores counter
envoy_cluster_http2_dropped_headers_with_underscores{cluster_name=“xds-grpc”} 0
TYPE envoy_cluster_http2_header_overflow counter
envoy_cluster_http2_header_overflow{cluster_name=“xds-grpc”} 0
…
Health Check服务如下:
curl http://127.0.0.1:15021/healthz/ready -v
* Trying 127.0.0.1:15021…
- Connected to 127.0.0.1 (127.0.0.1) port 15021 (#0)
GET /healthz/ready HTTP/1.1
Host: 127.0.0.1:15021
User-Agent: curl/7.69.1
Accept: /
- Mark bundle as not supporting multiuse
< HTTP/1.1 200 OK
< date: Tue, 16 Mar 2021 05:31:43 GMT
< content-length: 0
< x-envoy-upstream-service-time: 0
< server: envoy
<
- Connection #0 to host 127.0.0.1 left intact
Debug 服务
========
15000端口提供了Envoy admin API,该端口绑定在本地环回地址上,只能在Pod内访问。当攻击者控制了某容器,即可请求该服务来获取敏感信息。
curl http://127.0.0.1:15000/help
admin commands are:
/: Admin home page
/certs: print certs on machine
/clusters: upstream cluster status
/config_dump: dump current Envoy configs (experimental)
/contention: dump current Envoy mutex contention stats (if enabled)
/cpuprofiler: enable/disable the CPU profiler
/drain_listeners: drain listeners
/healthcheck/fail: cause the server to fail health checks
/healthcheck/ok: cause the server to pass health checks
/heapprofiler: enable/disable the heap profiler
/help: print out list of admin commands
/hot_restart_version: print the hot restart compatibility version
/init_dump: dump current Envoy init manager information (experimental)
/listeners: print listener info
/logging: query/change logging levels
/memory: print current allocation/heap usage
/quitquitquit: exit the server
/ready: print server state, return 200 if LIVE, otherwise return 503
/reopen_logs: reopen access logs
/reset_counters: reset all counters to zero
/runtime: print runtime values
/runtime_modify: modify runtime values
/server_info: print server version/status information
/stats: print server stats
/stats/prometheus: print server stats in prometheus format
/stats/recentlookups: Show recent stat-name lookups
/stats/recentlookups/clear: clear list of stat-name lookups and counter
/stats/recentlookups/disable: disable recording of reset stat-name lookup names
/stats/recentlookups/enable: enable recording of reset stat-name lookup names
curl http://127.0.0.1:15000/config_dump
{
“configs”: [
{
“@type”: “type.googleapis.com/envoy.admin.v3.BootstrapConfigDump”,
“bootstrap”: {
“node”: {
“id”: “sidecar172.17.0.3sleep-5d4c8b88ff-wgzkh.foo~foo.svc.cluster.local”,
“cluster”: “sleep.foo”,
“metadata”: {
“NAMESPACE”: “foo”,
“EXCHANGE_KEYS”: “NAME,NAMESPACE,INSTANCE_IPS,LABELS,OWNER,PLATFORM_METADATA,WORKLOAD_NAME,MESH_ID,SERVICE_ACCOUNT,CLUSTER_ID”,
“INSTANCE_IPS”: “172.17.0.3”,
“POD_PORTS”: “[\n]”,
“INTERCEPTION_MODE”: “REDIRECT”,
“MESH_ID”: “cluster.local”,
“SERVICE_ACCOUNT”: “sleep”,
“OWNER”: “kubernetes://apis/apps/v1/namespaces/default/deployments/sleep”,
“WORKLOAD_NAME”: “sleep”,
“ISTIO_VERSION”: “1.8.2”,
“PROXY_CONFIG”: {
“tracing”: {
“zipkin”: {
“address”: “zipkin.istio-system:9411”
}
},
“statusPort”: 15020,
“serviceCluster”: “sleep.foo”,
“envoyMetricsService”: {},
“binaryPath”: “/usr/local/bin/envoy”,
“discoveryAddress”: “istiod.istio-system.svc:15012”,
“concurrency”: 2,
“envoyAccessLogService”: {},
“statNameLength”: 189,
“configPath”: “./etc/istio/proxy”,
“parentShutdownDuration”: “60s”,
“proxyAdminPort”: 15000,
“controlPlaneAuthPolicy”: “MUTUAL_TLS”,
“drainDuration”: “45s”,
“proxyMetadata”: {
“DNS_AGENT”: “”
},
“terminationDrainDuration”: “5s”
},
…
}
控制面风险
=====
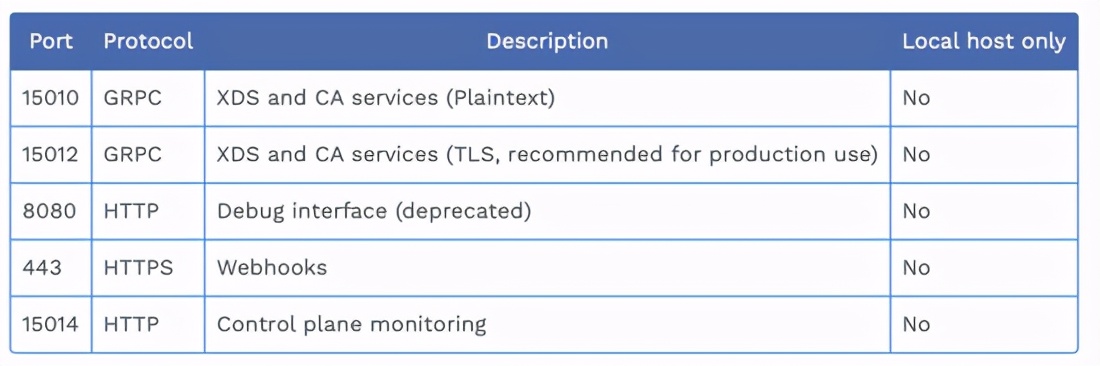
其会使用的全部服务端口信息如下:
XDS 服务
======
xDS协议是Envoy获取配置信息的传输协议,也是Istio与Envoy连接的桥梁。Istio控制面的XDS服务提供了各种类型的服务发现能力。需要了解的是,在Istio中XDS和CA服务一起通过端口15010和15012暴露,其中15010提供明文传输,而15012提供了TLS支持。由于端口15010对外暴露了非TLS的XDS服务,那么在集群内意味着我们就可以通过请求控制面的该明文的服务来获取敏感的信息。
./xds -u istiod.istio-system:15010 -v 3
Response CDS 23
{“name”:“BlackHoleCluster”,“type”:“STATIC”,“connectTimeout”:“10s”}
{“name”:“InboundPassthroughClusterIpv4”,“type”:“ORIGINAL_DST”,“connectTimeout”:“10s”,“lbPolicy”:“CLUSTER_PROVIDED”,“circuitBreakers”:{“thresholds”:[{“maxConnections”:4294967295,“maxPendingRequests”:4294967295,“maxRequests”:4294967295,“maxRetries”:4294967295}]},“upstreamBindConfig”:{“sourceAddress”:{“address”:“127.0.0.6”,“portValue”:0}},“protocolSelection”:“USE_DOWNSTREAM_PROTOCOL”}
{“name”:“PassthroughCluster”,“type”:“ORIGINAL_DST”,“connectTimeout”:“10s”,“lbPolicy”:“CLUSTER_PROVIDED”,“circuitBreakers”:{“thresholds”:[{“maxConnections”:4294967295,“maxPendingRequests”:4294967295,“maxRequests”:4294967295,“maxRetries”:4294967295}]},“protocolSelection”:“USE_DOWNSTREAM_PROTOCOL”}
{“name”:“inbound|80||”,“type”:“STATIC”,“connectTimeout”:“10s”,“loadAssignment”:{“clusterName”:“inbound|80||”,“endpoints”:[{“lbEndpoints”:[{“endpoint”:{“address”:{“socketAddress”:{“address”:“127.0.0.1”,“portValue”:80}}}}]}]},“circuitBreakers”:{“thresholds”:[{“maxConnections”:4294967295,“maxPendingRequests”:4294967295,“maxRequests”:4294967295,“maxRetries”:4294967295}]},“metadata”:{“filterMetadata”:{“istio”:{“services”:[{“host”:“sleep.foo.svc.cluster.local”,“name”:“sleep”,“namespace”:“foo”}]}}}}
{“transportSocketMatches”:[{“name”:“tlsMode-istio”,“match”:{“tlsMode”:“istio”},“transportSocket”:{“name”:“envoy.transport_sockets.tls”,“typedConfig”:{“@type”:“type.googleapis.com/envoy.extensions.transport_sockets.tls.v3.UpstreamTlsContext”,“commonTlsContext”:{“tlsCertificateSdsSecretConfigs”:[{“name”:“default”,“sdsConfig”:{“apiConfigSource”:{“apiType”:“GRPC”,“transportApiVersion”:“V3”,“grpcServices”:[{“envoyGrpc”:{“clusterName”:“sds-grpc”}}]},“initialFetchTimeout”:“0s”,“resourceApiVersion”:“V3”}}],“combinedValidationContext”:{“defaultValidationContext”:{},“validationContextSdsSecretConfig”:{“name”:“ROOTCA”,“sdsConfig”:{“apiConfigSource”:{“apiType”:“GRPC”,“transportApiVersion”:“V3”,“grpcServices”:[{“envoyGrpc”:{“clusterName”:“sds-grpc”}}]},“initialFetchTimeout”:“0s”,“resourceApiVersion”:“V3”}}},“alpnProtocols”:[“istio-peer-exchange”,“istio”,“h2”]},“sni”:“outbound_.15010_._.istiod.istio-system.svc.cluster.local”}}},{“name”:“tlsMode-disabled”,“match”:{},“transportSocket”:{“name”:“envoy.transport_sockets.raw_buffer”}}],“name”:“outbound|15010||istiod.istio-system.svc.cluster.local”,“type”:“EDS”,“edsClusterConfig”:{“edsConfig”:{“ads”:{},“resourceApiVersion”:“V3”},“serviceName”:“outbound|15010||istiod.istio-system.svc.cluster.local”},“connectTimeout”:“10s”,“circuitBreakers”:{“thresholds”:[{“maxConnections”:4294967295,“maxPendingRequests”:4294967295,“maxRequests”:4294967295,“maxRetries”:4294967295}]},“http2ProtocolOptions”:{“maxConcurrentStreams”:1073741824},“metadata”:{“filterMetadata”:{“istio”:{“default_original_port”:15010,“services”:[{“host”:“istiod.istio-system.svc.cluster.local”,“name”:“istiod”,“namespace”:“istio-system”}]}}}}
…
对此,我们可以在istiod配置中增加 --grpcAddr=“” 来禁用该端口。
Debug 服务
========
在istiod即Istio的控制面中同时也提供了Debug服务,这是我们在这些服务中应该注意的重点,它在默认情况下开启,其中端口15014(Control plane monitoring)和端口8080(Debug interface)提供了该服务。通过该服务我们可以获取到集群内的各种信息。
比如在我们在配置某些服务的AuthorizationPolicy,为其提供某种授权验证方式后。
我们可以通过Pilot debug API轻松获取到其配置信息,从而利用这些信息通过授权验证。这是东西向流量中很大的安全隐患,如果使用了Istio,那么请最好排查该功能的存在可能造成的影响。
curl http://istiod.istio-system:15014/debug/configz
…
{
“kind”: “AuthorizationPolicy”,
“apiVersion”: “security.istio.io/v1beta1”,
“metadata”: {
“name”: “httpbin”,
“namespace”: “foo”,
“resourceVersion”: “3693”,
“creationTimestamp”: “2021-02-20T11:52:33Z”,
“annotations”: {
“kubectl.kubernetes.io/last-applied-configuration”: “{“apiVersion”:“security.istio.io/v1beta1”,“kind”:“AuthorizationPolicy”,“metadata”:{“annotations”:{},“name”:“httpbin”,“namespace”:“foo”},“spec”:{“rules”:[{“from”:[{“source”:{“requestPrincipals”:[”*“]}}]},{“to”:[{“operation”:{“notPaths”:[”/ip"]}}]}],“selector”:{“matchLabels”:{“app”:“httpbin”}}}}\n"
}
},
“spec”: {
“rules”: [
{
“from”: [
{
“source”: {
“requestPrincipals”: [
“*”
]
}
}
]
},
{
“to”: [
{
“operation”: {
“notPaths”: [
自我介绍一下,小编13年上海交大毕业,曾经在小公司待过,也去过华为、OPPO等大厂,18年进入阿里一直到现在。
深知大多数Java工程师,想要提升技能,往往是自己摸索成长或者是报班学习,但对于培训机构动则几千的学费,着实压力不小。自己不成体系的自学效果低效又漫长,而且极易碰到天花板技术停滞不前!
因此收集整理了一份《2024年Java开发全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友,同时减轻大家的负担。

既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,基本涵盖了95%以上Java开发知识点,真正体系化!
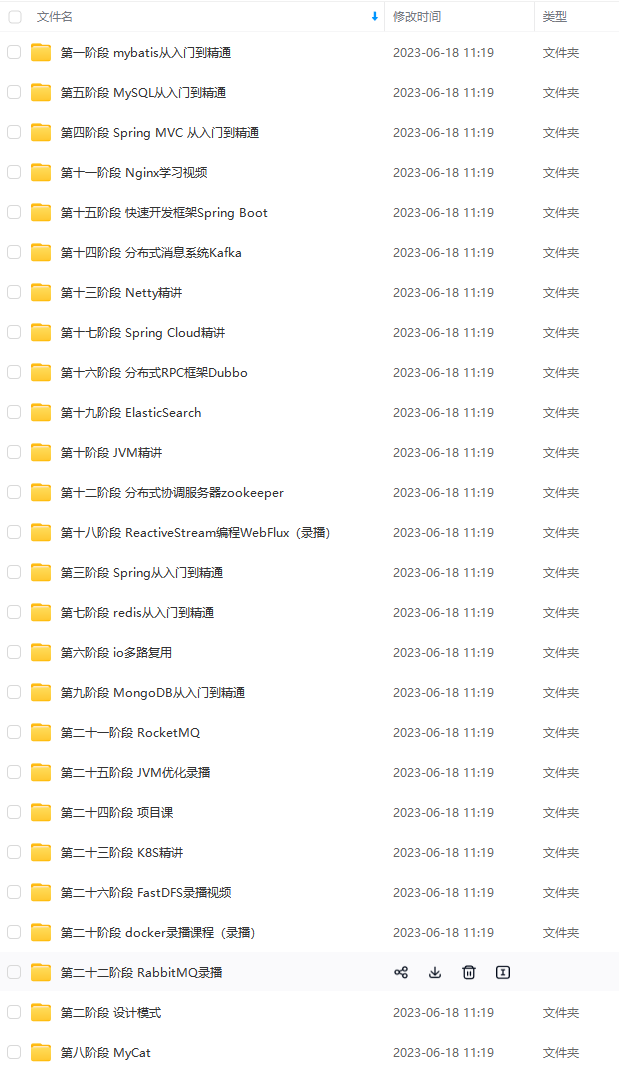
由于文件比较大,这里只是将部分目录截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且会持续更新!
如果你觉得这些内容对你有帮助,可以扫码获取!!(备注Java获取)

最后
本人也收藏了一份Java面试核心知识点来应付面试,借着这次机会可以送给我的读者朋友们:
目录:

Java面试核心知识点
一共有30个专题,足够读者朋友们应付面试啦,也节省朋友们去到处搜刮资料自己整理的时间!

Java面试核心知识点
《互联网大厂面试真题解析、进阶开发核心学习笔记、全套讲解视频、实战项目源码讲义》点击传送门即可获取!
src=“https://img-blog.csdnimg.cn/img_convert/2c728e365a597bde583610a3bfb75527.jpeg” alt=“img” style=“zoom: 33%;” />
最后
本人也收藏了一份Java面试核心知识点来应付面试,借着这次机会可以送给我的读者朋友们:
目录:
[外链图片转存中…(img-1Ndk3wUG-1713734618859)]
Java面试核心知识点
一共有30个专题,足够读者朋友们应付面试啦,也节省朋友们去到处搜刮资料自己整理的时间!
[外链图片转存中…(img-xTnqkPrW-1713734618859)]
Java面试核心知识点
《互联网大厂面试真题解析、进阶开发核心学习笔记、全套讲解视频、实战项目源码讲义》点击传送门即可获取!






















 326
326











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








