“size”: 2048
},
“names”: [
{
“C”: “CN”,
“L”: “FJ”,
“ST”: “Xia Men”
}
]
}
EOF
5、生成CA证书
[root@localhost etcd]# cfssl gencert -initca ca-csr.json | cfssljson -bare ca -#将会生成以下几个文件:
ca-key.pem
ca.csr
ca.pem
6、生成服务器端证书
[root@localhost etcd]# cat > server.json <<EOF
{
“CN”: “WAE Etcd Server”,
“hosts”: [
“127.0.0.1”,
“etcd1-com-hakim.com”,
“etcd2-com-hakim.com”,
“etcd3-com-hakim.com”,
“etcd4-com-hakim.com”,
“etcd5-com-hakim.com”
],
“key”: {
“algo”: “rsa”,
“size”: 2048
},
“names”: [
{
“C”: “CN”,
“L”: “FJ”,
“ST”: “Xia Men”
}
]
}
EOF
[root@localhost etcd]# cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=server server.json | cfssljson -bare server
7、生成对等证书
$ cp server.json member.json
$ cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=peer member.json | cfssljson -bare member
8、生成客户端证书
[root@localhost etcd]# cat > client.json <<EOF
{
“CN”: “client”,
“hosts”: [“”],
“key”: {
“algo”: “rsa”,
“size”: 2048
},
“names”: [
{
“C”: “CN”,
“L”: “FJ”,
“ST”: “Xia Men”
}
]
}
EOF
[root@localhost etcd]# cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=client client.json | cfssljson -bare client
9、保存证书和密钥
将所有 pem 文件复制到 /etc/etcd/etcd-ca/ 目录下,命令如下:
[root@localhost etcd]# mkdir /etc/etcd/etcd-ca/
[root@localhost etcd]# cp *.pem /etc/etcd/etcd-ca/
三、配置Etcd
增加etcd配置文件,内容如下:
[root@localhost etcd]# vim /etc/etcd/etcd.conf
[member]
ETCD_NAME=etcd1
ETCD_DATA_DIR=“/var/lib/etcd/data”
ETCD_LISTEN_PEER_URLS=“https://0.0.0.0:2380”
ETCD_LISTEN_CLIENT_URLS=“https://0.0.0.0:2379”
#[cluster]
ETCD_INITIAL_ADVERTISE_PEER_URLS=“https://etcd1-com-hakim.com:2380”
ETCD_INITIAL_CLUSTER=“etcd1=https://etcd1-com-hakim.com:2380,etcd2=https://etcd2-com-hakim.com:2380,etcd3=https://etcd3-com-hakim.com:2380,etcd4=https://etcd4-com-hakim.com:2380,etcd5=https://etcd5-com-hakim.com:2380”
ETCD_INITIAL_CLUSTER_STATE=“new”
ETCD_INITIAL_CLUSTER_TOKEN=“etcd-cluster”
ETCD_ADVERTISE_CLIENT_URLS=“https://etcd1-com-hakim.com:2379”
#[security]
ETCD_CERT_FILE=“/etc/etcd/etcd-ca/server.pem”
ETCD_KEY_FILE=“/etc/etcd/etcd-ca/server-key.pem”
ETCD_CLIENT_CERT_AUTH=“true”
ETCD_TRUSTED_CA_FILE=“/etc/etcd/etcd-ca/ca.pem”
ETCD_AUTO_TLS=“true”
ETCD_PEER_CERT_FILE=“/etc/etcd/etcd-ca/member.pem”
ETCD_PEER_KEY_FILE=“/etc/etcd/etcd-ca/member-key.pem”
ETCD_PEER_CLIENT_CERT_AUTH=“true”
ETCD_PEER_TRUSTED_CA_FILE=“/etc/etcd/etcd-ca/ca.pem”
ETCD_PEER_AUTO_TLS=“true”
注:上述参数详细解释请参考另一篇文章,传送门如下:
配置etcd开机自启动,修改 /usr/lib/systemd/system/etcd.service,内容如下:
[Unit]
Description=Etcd Server
After=network.target
[Service]
Type=notify
WorkingDirectory=/var/lib/etcd/
EnvironmentFile=/etc/etcd/etcd.conf
ExecStart=/usr/bin/etcd \
–name=${ETCD_NAME} \
–data-dir=${ETCD_DATA_DIR} \
–listen-peer-urls=${ETCD_LISTEN_PEER_URLS} \
–listen-client-urls=${ETCD_LISTEN_CLIENT_URLS},http://127.0.0.1:2379 \
–advertise-client-urls=${ETCD_ADVERTISE_CLIENT_URLS} \
–initial-advertise-peer-urls=${ETCD_INITIAL_ADVERTISE_PEER_URLS} \
–initial-cluster=${ETCD_INITIAL_CLUSTER} \
–initial-cluster-token=${ETCD_INITIAL_CLUSTER_TOKEN} \
–initial-cluster-state=${ETCD_INITIAL_CLUSTER_STATE} \
–cert-file=${ETCD_CERT_FILE} \
–key-file=${ETCD_KEY_FILE} \
–trusted-ca-file=${ETCD_TRUSTED_CA_FILE} \
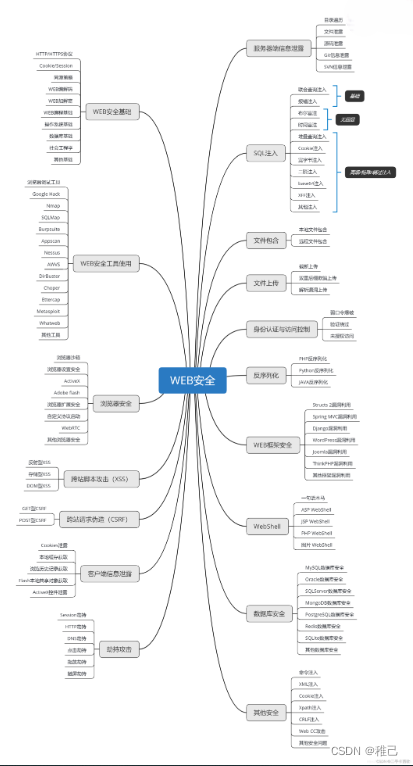
学习路线:
这个方向初期比较容易入门一些,掌握一些基本技术,拿起各种现成的工具就可以开黑了。不过,要想从脚本小子变成黑客大神,这个方向越往后,需要学习和掌握的东西就会越来越多以下是网络渗透需要学习的内容:
网上学习资料一大堆,但如果学到的知识不成体系,遇到问题时只是浅尝辄止,不再深入研究,那么很难做到真正的技术提升。
一个人可以走的很快,但一群人才能走的更远!不论你是正从事IT行业的老鸟或是对IT行业感兴趣的新人,都欢迎加入我们的的圈子(技术交流、学习资源、职场吐槽、大厂内推、面试辅导),让我们一起学习成长!






















 2657
2657

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








