giantbranch@ubuntu:~/_RE_Cirno.jpg.extracted$
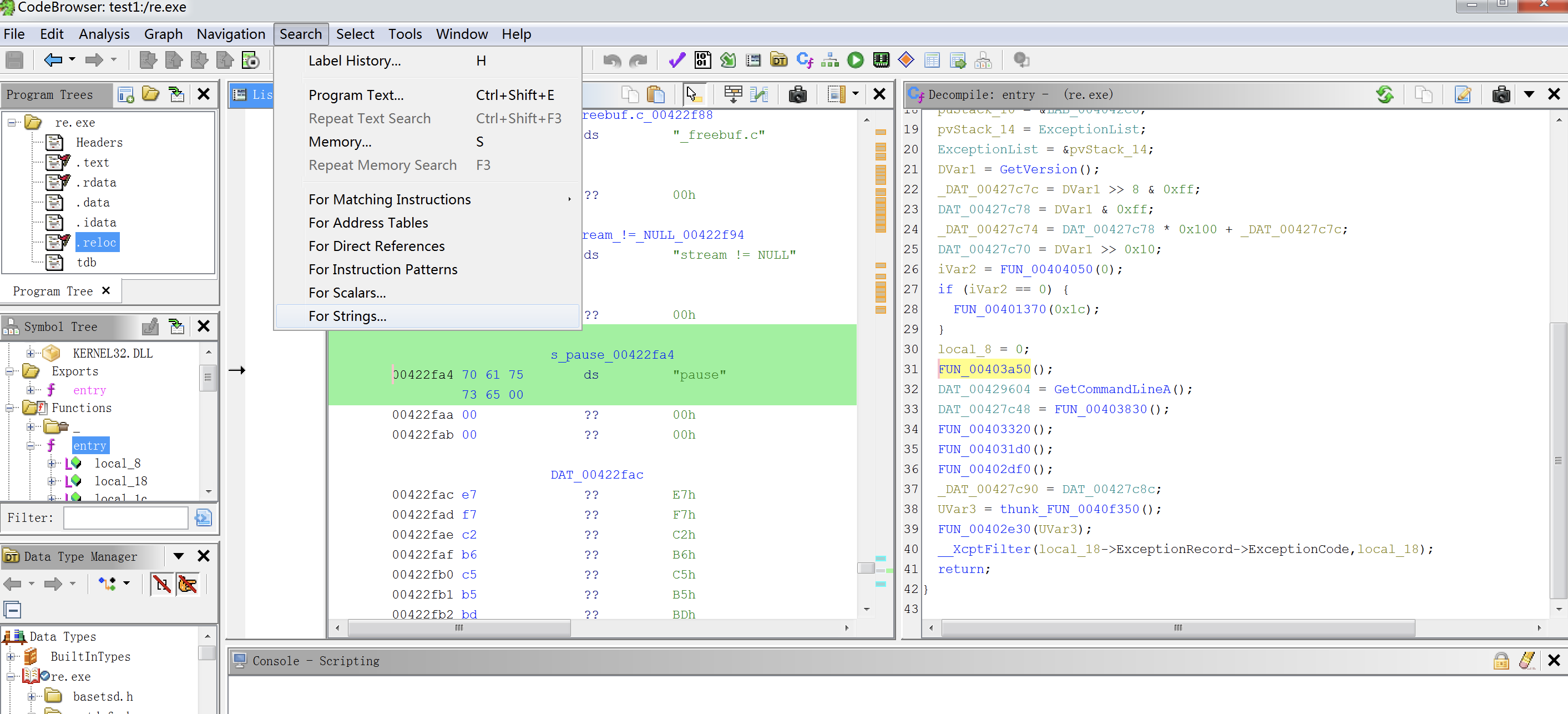
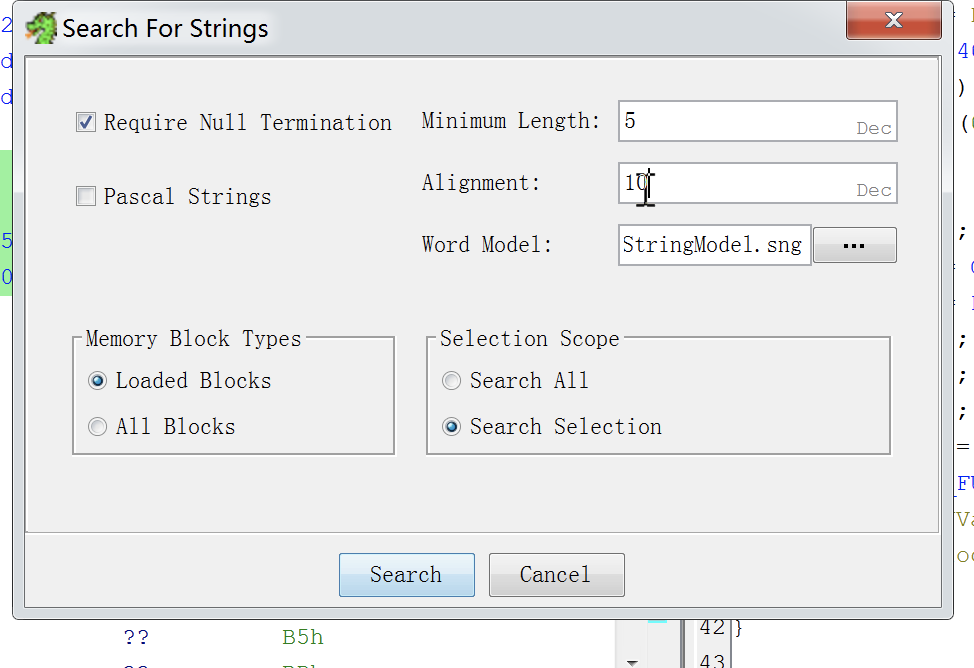
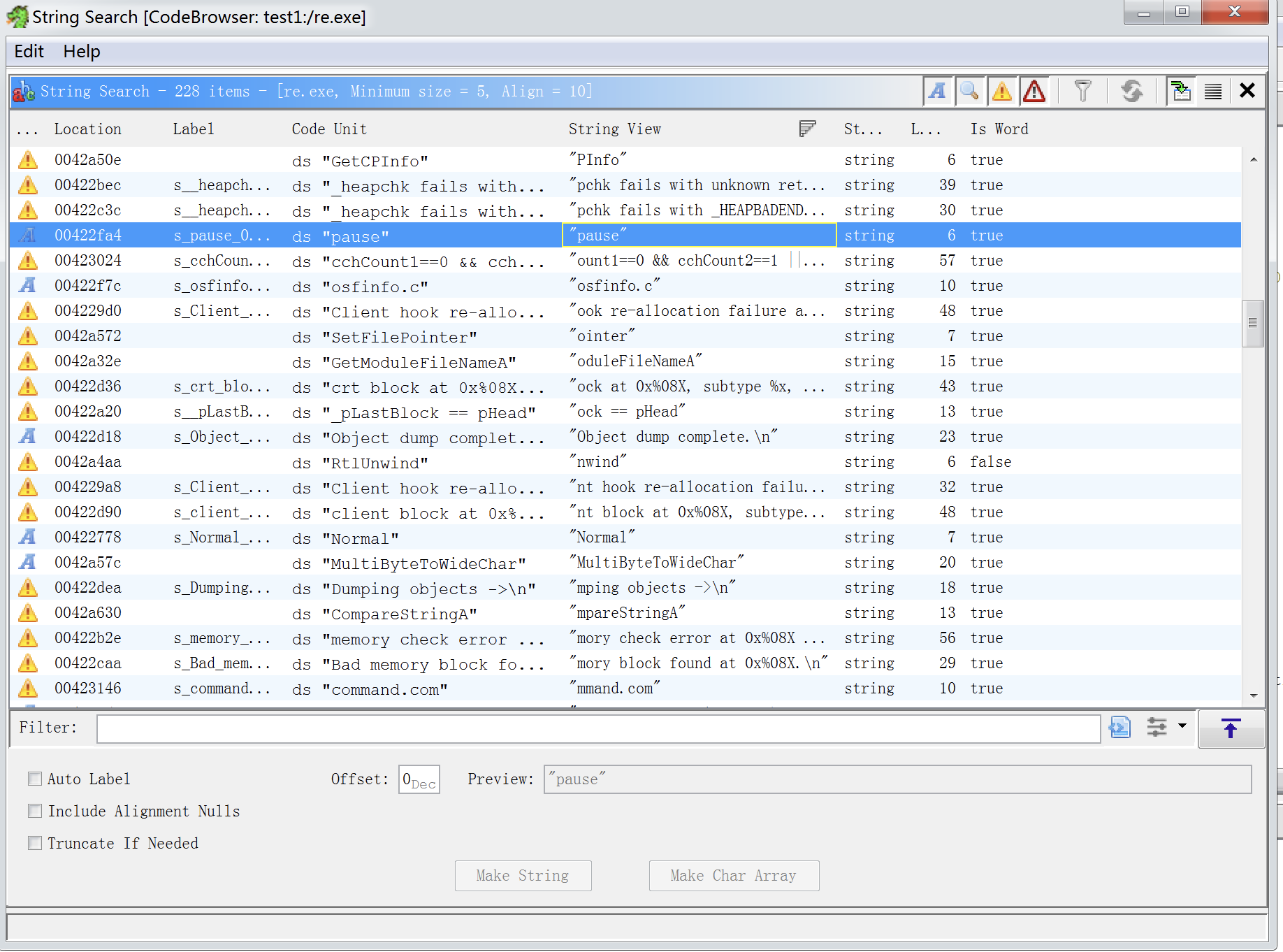
use ghidra!
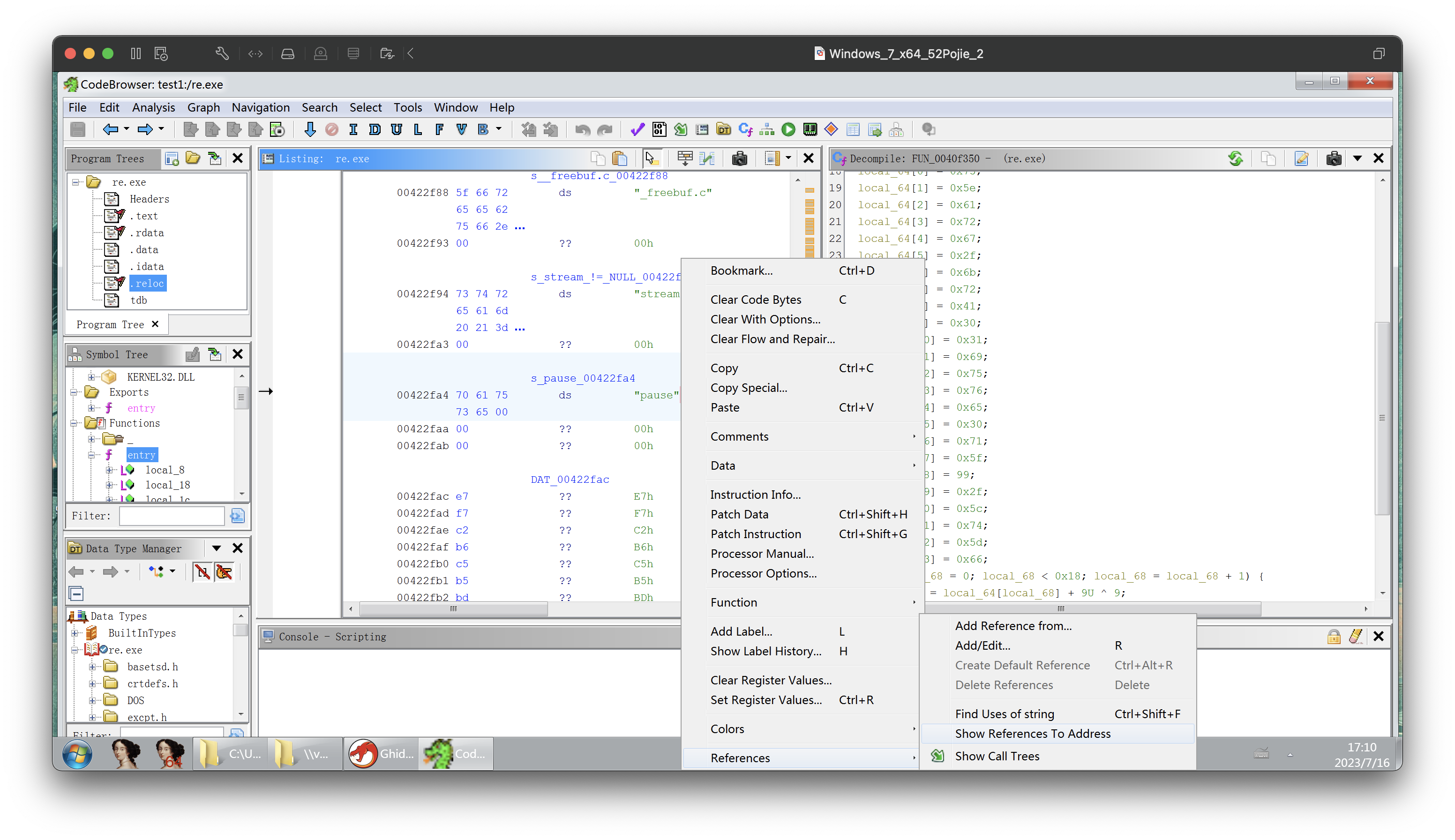
void FUN_0040f350(void)
{
int iVar1;
undefined4 *puVar2;
undefined4 local_b0 [16];
uint local_70;
uint local_6c;
int local_68;
int local_64 [24];
puVar2 = local_b0;
for (iVar1 = 0x2b; iVar1 != 0; iVar1 = iVar1 + -1) {
*puVar2 = 0xcccccccc;
puVar2 = puVar2 + 1;
}
local_64[0] = 0x73;
local_64[1] = 0x5e;
local_64[2] = 0x61;
local_64[3] = 0x72;
local_64[4] = 0x67;
local_64[5] = 0x2f;
local_64[6] = 0x6b;
local_64[7] = 0x72;
local_64[8] = 0x41;
local_64[9] = 0x30;
local_64[10] = 0x31;
local_64[11] = 0x69;
local_64[12] = 0x75;
local_64[13] = 0x76;
local_64[14] = 0x65;
local_64[15] = 0x30;
local_64[16] = 0x71;
local_64[17] = 0x5f;
local_64[18] = 99;
local_64[19] = 0x2f;
local_64[20] = 0x5c;
local_64[21] = 0x74;
local_64[22] = 0x5d;
local_64[23] = 0x66;
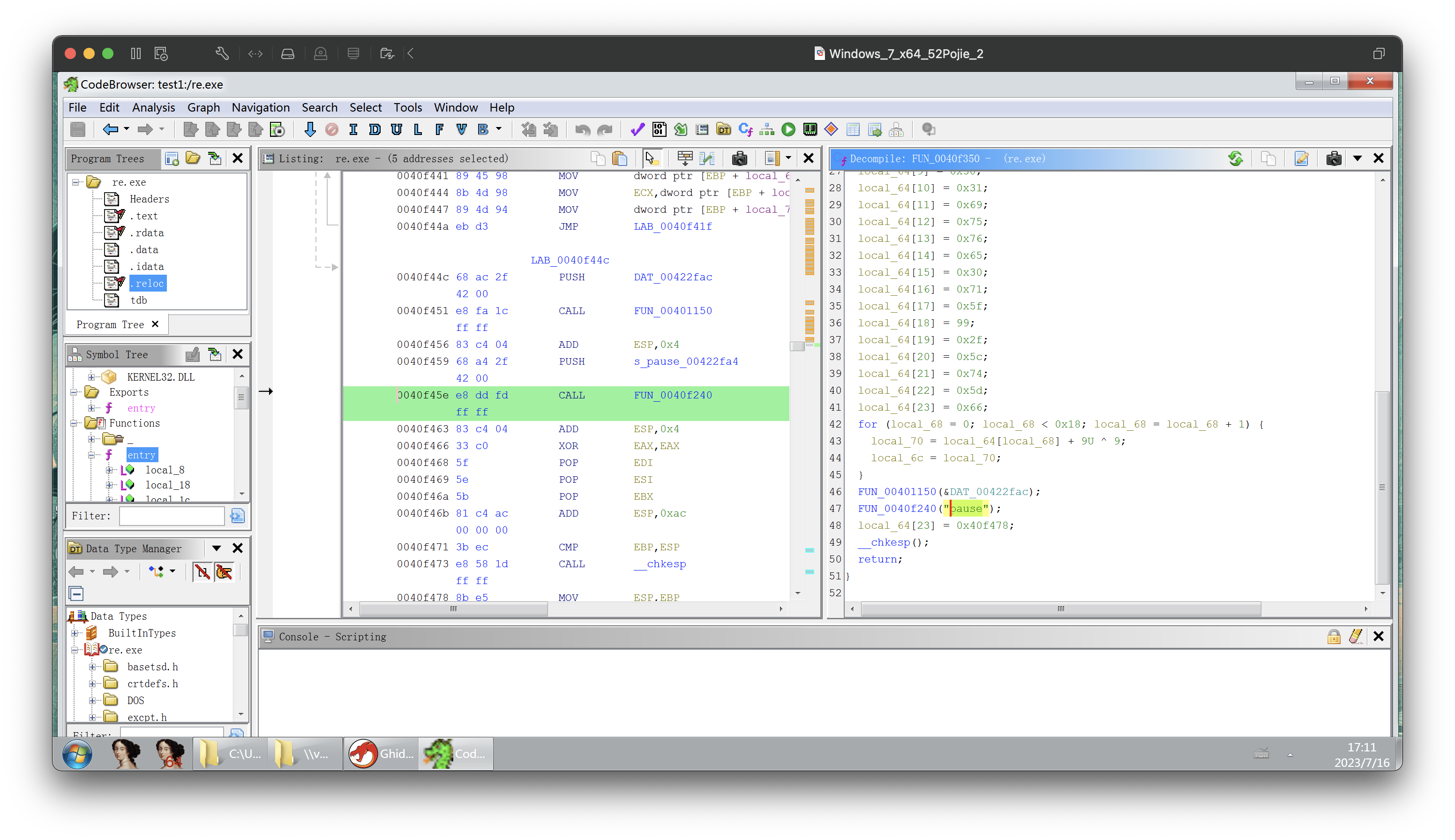
for (local_68 = 0; local_68 < 0x18; local_68 = local_68 + 1) {
local_70 = local_64[local_68] + 9U ^ 9;
local_6c = local_70;
}
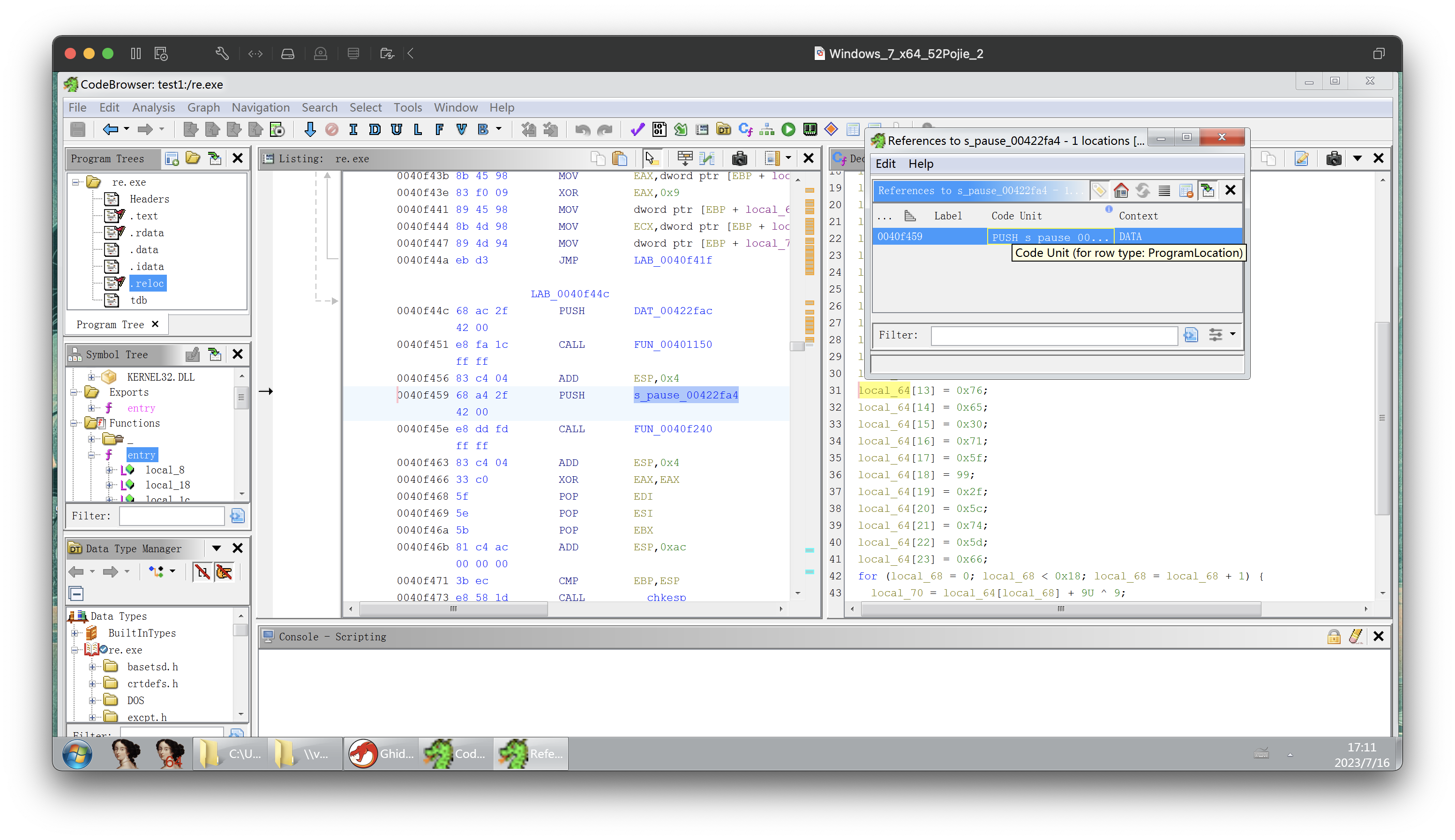
FUN_00401150(&DAT_00422fac);
FUN_0040f240(“pause”);
local_64[23] = 0x40f478;
__chkesp();
return;
}
change the code!
#include<stdio.h>
void FUN_0040f350(void);
int main(void){
FUN_0040f350();
return 0;
}
void FUN_0040f350(void)
{
int local_70;
//int local_6c;
int local_68;
int local_64 [24];
int local_64_2[24];
local_64[0] = 0x73;
local_64[1] = 0x5e;
local_64[2] = 0x61;
local_64[3] = 0x72;
local_64[4] = 0x67;
local_64[5] = 0x2f;
local_64[6] = 0x6b;
local_64[7] = 0x72;
local_64[8] = 0x41;
local_64[9] = 0x30;
local_64[10] = 0x31;
local_64[11] = 0x69;
local_64[12] = 0x75;
local_64[13] = 0x76;
local_64[14] = 0x65;
local_64[15] = 0x30;
local_64[16] = 0x71;
local_64[17] = 0x5f;
local_64[18] = 99;
local_64[19] = 0x2f;
local_64[20] = 0x5c;
local_64[21] = 0x74;
local_64[22] = 0x5d;
local_64[23] = 0x66;
for (local_68 = 0; local_68 < 0x18; local_68 = local_68 + 1) {
local_70 = (local_64[local_68] + 0x9) ^ 0x9;
//local_6c = local_70;
local_64_2[local_68]=local_70;
printf(“%c”,local_70 );
}
//cout>>endl;
printf(“\n”);
for (local_68 = 23; local_68 > -1; local_68 = local_68 - 1) {
//local_70 = (local_64[local_68] + 0x9) ^ 0x9;
//local_6c = local_70;
printf("%c",local_64_2[local_68] );
}
//return 0;
}
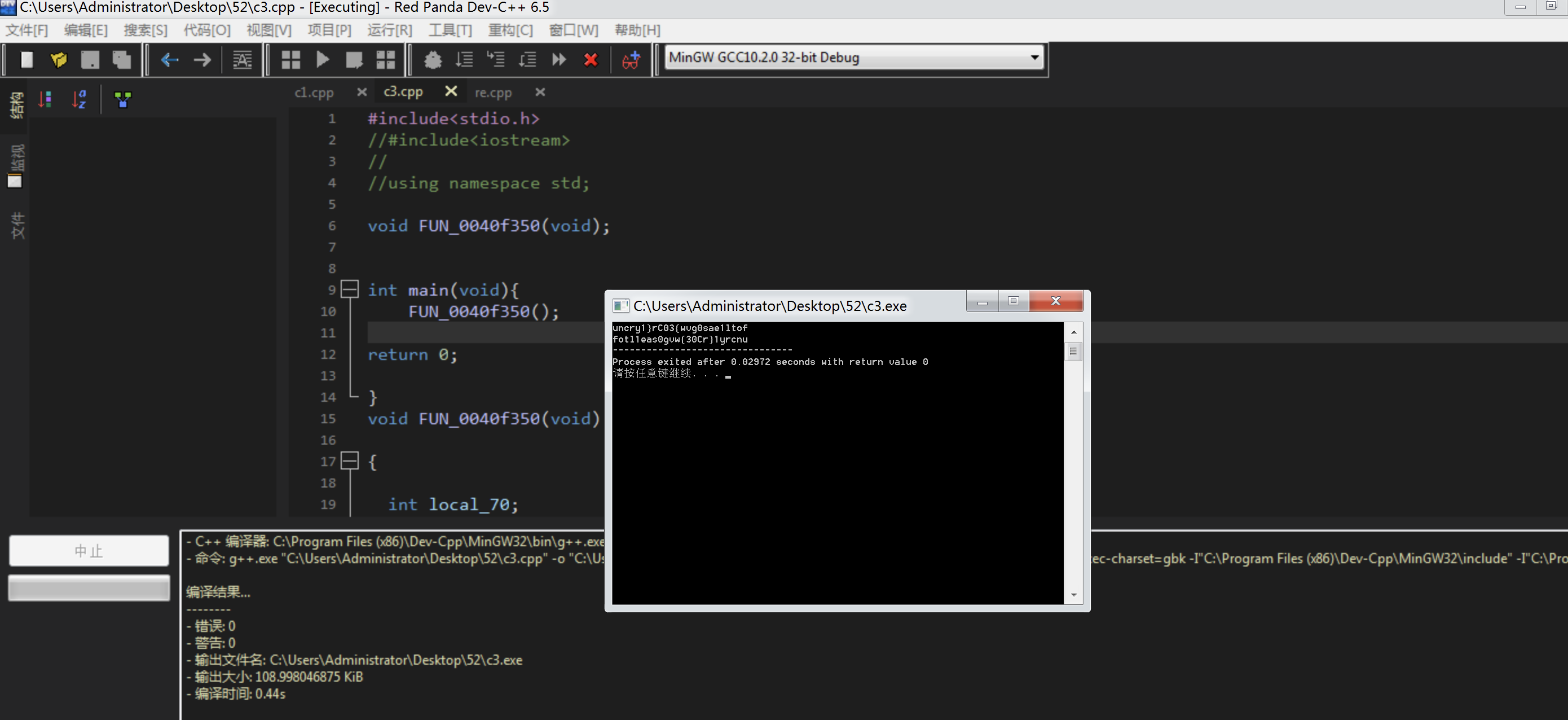
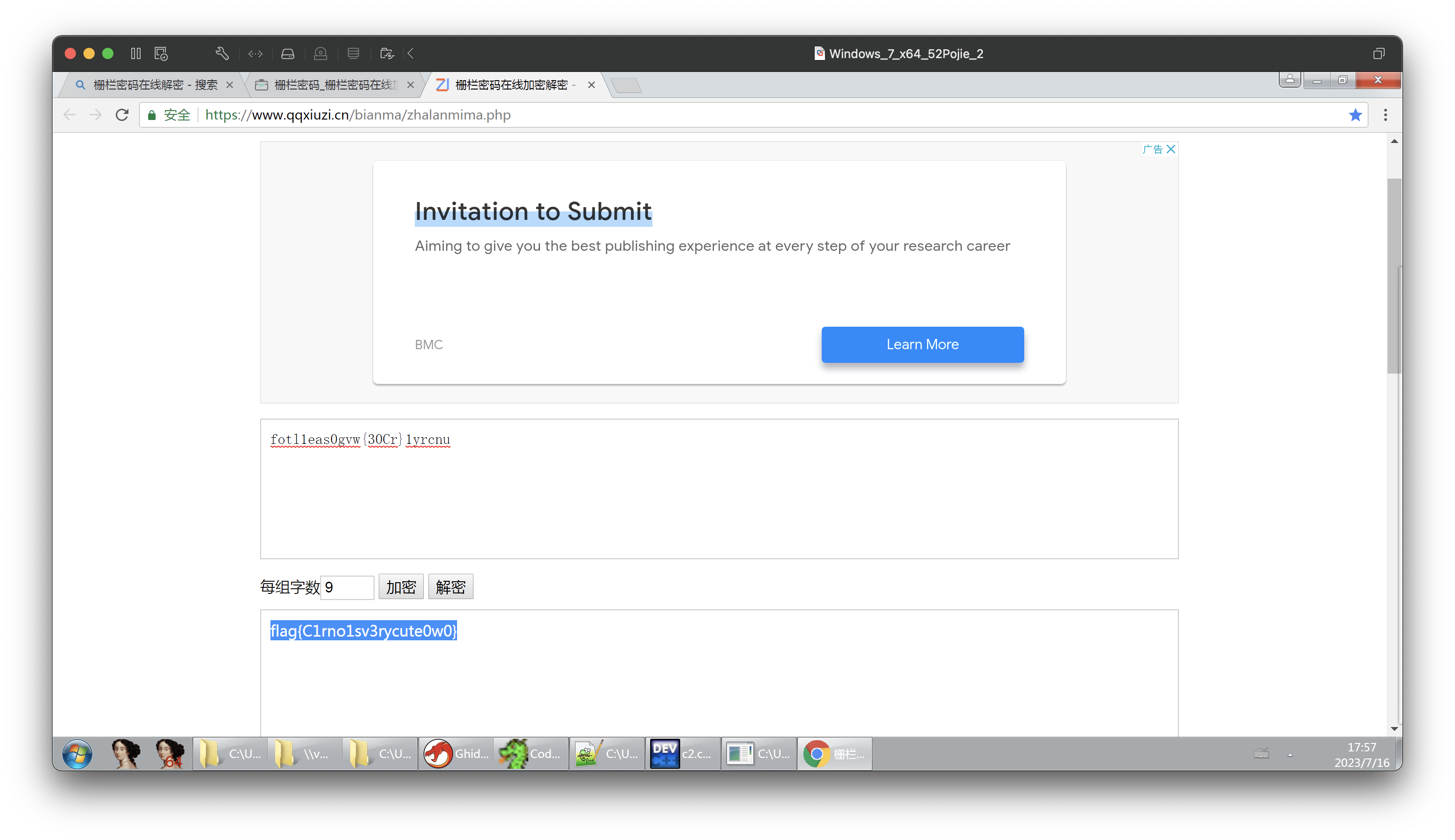
fotl1eas0gvw{30Cr}1yrcnu
flag{C1rno1sv3rycute0w0}
## 最后
**自我介绍一下,小编13年上海交大毕业,曾经在小公司待过,也去过华为、OPPO等大厂,18年进入阿里一直到现在。**
**深知大多数网络安全工程师,想要提升技能,往往是自己摸索成长,但自己不成体系的自学效果低效又漫长,而且极易碰到天花板技术停滞不前!**
**因此收集整理了一份《2024年网络安全全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友。**





**既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,基本涵盖了95%以上网络安全知识点!真正的体系化!**
[**如果你觉得这些内容对你有帮助,需要这份全套学习资料的朋友可以戳我获取!!**](https://bbs.csdn.net/topics/618653875)
**由于文件比较大,这里只是将部分目录截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且会持续更新!**
入学习提升的进阶课程,基本涵盖了95%以上网络安全知识点!真正的体系化!**
[**如果你觉得这些内容对你有帮助,需要这份全套学习资料的朋友可以戳我获取!!**](https://bbs.csdn.net/topics/618653875)
**由于文件比较大,这里只是将部分目录截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且会持续更新!**






















 9886
9886











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








