但需要注意的是不要将此方式用在外部网络环境,以免带来安全问题,因为在外部网络环境下暴露端口是很危险的事,别人随时能攻击甚至窃取你的数据。因此官方也给出了详细警告及处理信息:
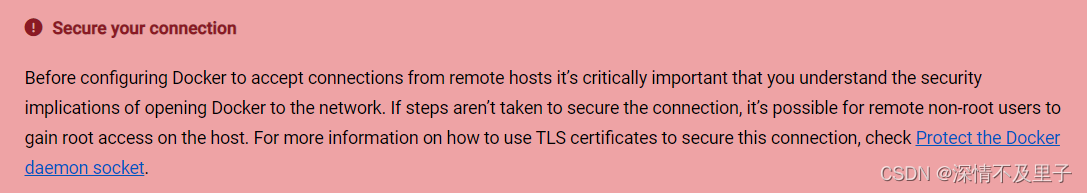 因此我们不能仅仅去配置远程访问就完事了,还要用安全证书进行配置才行。对此官网也给出了相应的解决方式:配置CA证书密钥
因此我们不能仅仅去配置远程访问就完事了,还要用安全证书进行配置才行。对此官网也给出了相应的解决方式:配置CA证书密钥

下面,我们一步一步来~
开启远程访问(不安全)
根据官网方法,进入docker.service文件,编辑并在ExecStart上添加配置 -H tcp://127.0.0.1:2375
Type=notify
# the default is not to use systemd for cgroups because the delegate issues still
# exists and systemd currently does not support the cgroup feature set required
# for containers run by docker
ExecStart=/usr/bin/dockerd -H fd:// --containerd=/run/containerd/containerd.sock -H tcp://0.0.0.0:2375
ExecReload=/bin/kill -s HUP $MAINPID
TimeoutSec=0
RestartSec=2
Restart=always
这里相当于开放了2375端口,因此除了配置文件以外还要在防火墙开放端口,云服务器还需要开放端口策略等等。
[root@VM-12-4-centos ~]# firewall-cmd --query-port=2375/tcp
You're performing an operation over default zone ('public'),
but your connections/interfaces are in zone 'docker' (see --get-active-zones)
You most likely need to use --zone=docker option.
no #没开启
#开启端口号
[root@VM-12-4-centos ~]# firewall-cmd --add-port=2375/tcp --permanent
You're performing an operation over default zone ('public'),
but your connections/interfaces are in zone 'docker' (see --get-active-zones)
You most likely need to use --zone=docker option.
success
#重启防火墙
[root@VM-12-4-centos ~]# firewall-cmd --reload
success
重启服务使得更改后的配置生效,并查看docker启动状态
[root@VM-12-4-centos server]# systemctl daemon-reload
[root@VM-12-4-centos server]# systemctl restart docker
[root@VM-12-4-centos server]# systemctl status docker
● docker.service - Docker Application Container Engine
Loaded: loaded (/usr/lib/systemd/system/docker.service; enabled; vendor preset: disabled)
Active: active (running) since Mon 2023-04-10 09:00:30 CST; 15s ago
Docs: https://docs.docker.com
Main PID: 6425 (dockerd)
Tasks: 51
Memory: 56.1M
CGroup: /system.slice/docker.service
├─6425 /usr/bin/dockerd -H fd:// --containerd=/run/containerd/containerd.sock -H tcp://0.0.0.0:2375
├─6741 /usr/bin/docker-proxy -proto tcp -host-ip 0.0.0.0 -host-port 3303 -container-ip 172.18.1.30 -container-port 3306
├─6747 /usr/bin/docker-proxy -proto tcp -host-ip :: -host-port 3303 -container-ip 172.18.1.30 -container-port 3306
├─6855 /usr/bin/docker-proxy -proto tcp -host-ip 0.0.0.0 -host-port 9000 -container-ip 172.17.0.2 -container-port 9000
├─6861 /usr/bin/docker-proxy -proto tcp -host-ip :: -host-port 9000 -container-ip 172.17.0.2 -container-port 9000
├─6967 /usr/bin/docker-proxy -proto tcp -host-ip 0.0.0.0 -host-port 8848 -container-ip 172.18.1.48 -container-port 8848
└─6983 /usr/bin/docker-proxy -proto tcp -host-ip :: -host-port 8848 -container-ip 172.18.1.48 -container-port 8848
安全访问配置流程
1,在指定文件夹新建一个存放CA密钥的文件夹,笔者这里再docker文件下存放。
[root@VM-12-4-centos server]# cd docker
[root@VM-12-4-centos docker]# ll
total 0
[root@VM-12-4-centos docker]# mkdir ca_key
[root@VM-12-4-centos docker]# ll
total 4
drwxr-xr-x 2 root root 4096 Apr 10 10:27 ca_key
[root@VM-12-4-centos docker]# cd ca_key
2,在Docker主机上通过命令生成CA私钥和公钥
执行命令:openssl genrsa -aes256 -out ca-key.pem 4096
[root@VM-12-4-centos ca_key]# openssl genrsa -aes256 -out ca-key.pem 4096
Generating RSA private key, 4096 bit long modulus
.....................................................................................................................................................................................................................................................++
................................................................................................++
e is 65537 (0x10001)
Enter pass phrase for ca-key.pem:
Verifying - Enter pass phrase for ca-key.pem:
Verify failure
User interface error
139698349328272:error:0906906F:PEM routines:PEM_ASN1_write_bio:read key:pem_lib.c:385:
[root@VM-12-4-centos ca_key]# openssl genrsa -aes256 -out ca-key.pem 4096
Generating RSA private key, 4096 bit long modulus
............++
.............................................................................................................................................................................................................................++
e is 65537 (0x10001)
Enter pass phrase for ca-key.pem:
Verifying - Enter pass phrase for ca-key.pem:
这里需要输入密码并确认,只要两次输入一致就行,否则会像重置密码数据两次新密码一样报验证错误。需要注意的是:Linux上并不会显示输入的密码信息,因此要格外注意别输错了。
如果成功,该文件下就有了pem证书文件生成:
[root@VM-12-4-centos ca_key]# ll
total 4
-rw-r--r-- 1 root root 3326 Apr 10 10:29 ca-key.pem
3,补全CA信息
执行命令:openssl req -new -x509 -days 365 -key ca-key.pem -sha256 -out ca.pem根据要求依次输入访问密码、国家、省、市、组织名称、单位名称、随便一个名字、邮箱等,需要这些信息作为证书申请。
[root@VM-12-4-centos ca_key]# openssl req -new -x509 -days 365 -key ca-key.pem -sha256 -out ca.pem
Enter pass phrase for ca-key.pem:
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN
State or Province Name (full name) []:HUBei
Locality Name (eg, city) [Default City]:WuHan
Organization Name (eg, company) [Default Company Ltd]:ZC
Organizational Unit Name (eg, section) []:QA
Common Name (eg, your name or your server's hostname) []:192.168.98.128(ip地址)
Email Address []:8888888888@qq.com
现在我们有了CA,就可以创建服务器密钥和证书签名请求(CSR)。
Tips:确保“Common Name”与用于连接Docker的主机名匹配,否则后续远程连接会失败!
4,生成service-key.pem
执行命令:openssl genrsa -out server-key.pem 4096
[root@VM-12-4-centos ca_key]# openssl genrsa -out server-key.pem 4096
Generating RSA private key, 4096 bit long modulus
...........................................................................................++
....++
e is 65537 (0x10001)
[root@VM-12-4-centos ca_key]# ll
total 12
-rw-r--r-- 1 root root 3326 Apr 10 10:29 ca-key.pem
-rw-r--r-- 1 root root 2082 Apr 10 10:56 ca.pem
-rw-r--r-- 1 root root 3247 Apr 10 11:45 server-key.pem
5,用CA签署公钥
由于TLS连接可以通过IP地址和DNS名称进行,因此在创建证书时需要指定IP地址或者域名。填写的IP或者域名,都是将来对外开放的地址,也就是用于连接的地址。例如,要允许使用127.0.0.1进行连接:
执行命令:openssl req -subj “/CN=$HOST” -sha256 -new -key server-key.pem -out server.csr
[root@VM-12-4-centos ca_key]# openssl req -subj "/CN=127.0.0.1" -sha256 -new -key server-key.pem -out server.csr
6,匹配白名单
设置允许哪些IP可以远程连接docker。
- 允许指定
IP可以远程连接docker。
echo subjectAltName = DNS:$HOST,IP:XX.XX.XX.XX,IP:XX.XX.XX.XX >> extfile.cnf
$HOST是你的IP或者域名,使用时将$HOST替换为自己的IP或者域名。
如:
# 127.0.0.1 服务器上的 docker,只允许ip地址为225.225.225.0的客户连接
echo subjectAltName = DNS:127.0.0.1,IP:225.225.225.0 >> extfile.cnf
# ideaopen.cn 服务器上的 docker,只允许ip地址为225.225.225.0的客户连接
echo subjectAltName = DNS:ideaopen.cn,IP:225.225.225.0 >> extfile.cnf
- 允许所有
IP连接
设置IP为0.0.0.0即可。
如:
echo subjectAltName = DNS:127.0.0.1,IP:0.0.0.0 >> extfile.cnf
注:只允许永久证书的才可以连接成功
然后需要将Docker守护进程密钥的扩展使用属性设置为仅用于服务器身份验证:
echo extendedKeyUsage = serverAuth >> extfile.cnf
7,生成已签名的证书(signed certificate)
这里执行命令后需要输入之前设置的密码
[root@VM-12-4-centos ca_key]# openssl x509 -req -days 365 -sha256 -in server.csr -CA ca.pem -CAkey ca-key.pem \
> -CAcreateserial -out server-cert.pem -extfile extfile.cnf
Signature ok
subject=/CN=127.0.0.1
Getting CA Private Key
Enter pass phrase for ca-key.pem:
授权插件提供了更细粒度的控制,以补充来自双向TLS的身份验证。除了上述描述的其他信息外,在Docker守护进程上运行的授权插件还接收用于连接Docker客户端的证书信息。
如果第二次申请颁发证书,可能会出现ca.srl: No such file or directory的问题。
此时我们echo “01” > ca.srl 即可,这个文件影响到ca颁发的证书的序号,而证书序号应该是唯一的,所以这点需要控制好。
8,生成客户端key
对于客户端身份验证,我们还需要创建客户端密钥和证书签名请求:
注意:为了简化接下来的几个步骤,我们可以在Docker守护进程的主机上执行此步骤。
[root@VM-12-4-centos ca_key]# openssl genrsa -out key.pem 4096
Generating RSA private key, 4096 bit long modulus
......................................++
.................................++
e is 65537 (0x10001)
[root@VM-12-4-centos ca_key]# openssl req -subj '/CN=client' -new -key key.pem -out client.csr
此外为了使密钥适合客户端身份验证,还需要创建一个新的扩展配置文件:
[root@VM-12-4-centos ca_key]# echo extendedKeyUsage = clientAuth >> extfile.cnf
[root@VM-12-4-centos ca_key]# echo extendedKeyUsage = clientAuth > extfile-client.cnf
然后就可以生成已签名的客户端key了。
[root@VM-12-4-centos ca_key]# openssl x509 -req -days 365 -sha256 -in client.csr -CA ca.pem -CAkey ca-key.pem \
> -CAcreateserial -out cert.pem -extfile extfile-client.cnf
Signature ok
subject=/CN=client
Getting CA Private Key
Enter pass phrase for ca-key.pem:
此时可以看到我们当初创建的ca_key文件里已经有很多文件了。
[root@VM-12-4-centos ca_key]# ll
total 44
-rw-r--r-- 1 root root 3326 Apr 10 10:29 ca-key.pem
-rw-r--r-- 1 root root 2082 Apr 10 10:56 ca.pem
-rw-r--r-- 1 root root 17 Apr 10 13:45 ca.srl
-rw-r--r-- 1 root root 1854 Apr 10 13:45 cert.pem
-rw-r--r-- 1 root root 1582 Apr 10 13:40 client.csr
-rw-r--r-- 1 root root 30 Apr 10 13:43 extfile-client.cnf
-rw-r--r-- 1 root root 102 Apr 10 13:42 extfile.cnf
-rw-r--r-- 1 root root 3243 Apr 10 13:40 key.pem
-rw-r--r-- 1 root root 1895 Apr 10 13:36 server-cert.pem
-rw-r--r-- 1 root root 1586 Apr 10 13:26 server.csr
-rw-r--r-- 1 root root 3247 Apr 10 11:45 server-key.pem
但是有很多多余的配置文件,生成cert.pem,server-cert.pem后,一些签名请求和扩展配置文件可以安全删除了。
#删除多余文件
[root@VM-12-4-centos ca_key]# rm -v client.csr server.csr extfile.cnf extfile-client.cnf
rm: remove regular file ‘client.csr’? y
removed ‘client.csr’
rm: remove regular file ‘server.csr’? y
removed ‘server.csr’
rm: remove regular file ‘extfile.cnf’? y
removed ‘extfile.cnf’
rm: remove regular file ‘extfile-client.cnf’? y
removed ‘extfile-client.cnf’
9,修改权限
为了防止密钥文件被误删或者损坏,我们可以改变一下文件权限,让它只读就可以。
[root@VM-12-4-centos ca_key]# chmod -v 0400 ca-key.pem key.pem server-key.pem
mode of ‘ca-key.pem’ changed from 0644 (rw-r--r--) to 0400 (r--------)
mode of ‘key.pem’ changed from 0644 (rw-r--r--) to 0400 (r--------)
mode of ‘server-key.pem’ changed from 0644 (rw-r--r--) to 0400 (r--------)
为了防止证书损坏,我们也删除它的写入权限。
[root@VM-12-4-centos ca_key]# chmod -v 0444 ca.pem server-cert.pem cert.pem
mode of ‘ca.pem’ changed from 0644 (rw-r--r--) to 0444 (r--r--r--)
mode of ‘server-cert.pem’ changed from 0644 (rw-r--r--) to 0444 (r--r--r--)
mode of ‘cert.pem’ changed from 0644 (rw-r--r--) to 0444 (r--r--r--)
归集服务器证书
将证书存放在docker配置文件夹下
[root@VM-12-4-centos ca_key]# cp server-*.pem /etc/docker/
[root@VM-12-4-centos ca_key]# cp ca.pem /etc/docker/
10,修改Docker配置
























 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








